API Gateway Main Concepts: An Essential Guide
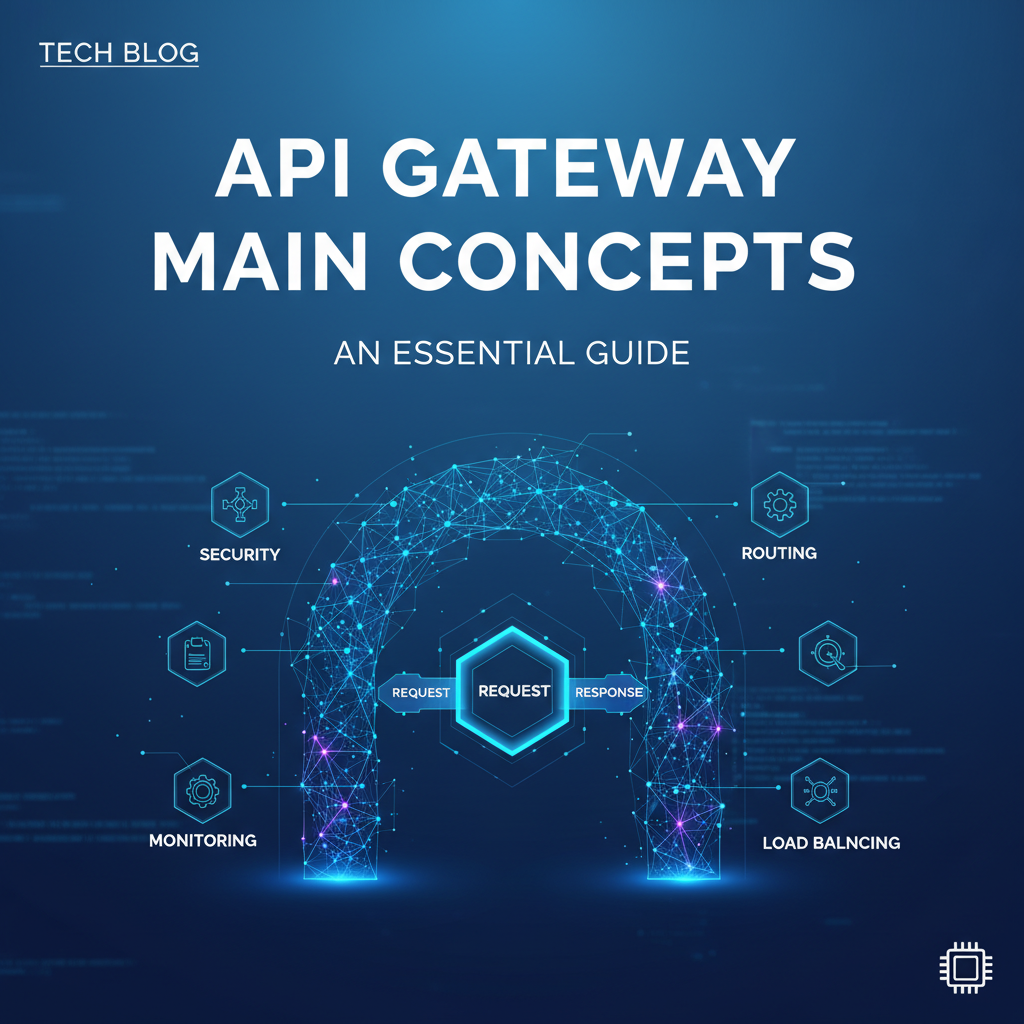
In the intricate tapestry of modern software architecture, where applications are no longer monolithic giants but rather constellations of interconnected, specialized services, the flow of data and communication has become a paramount concern. The rise of microservices, cloud-native deployments, and distributed systems has ushered in an era of unprecedented flexibility and scalability, yet it has simultaneously introduced a new layer of complexity. Managing the myriad interactions between these disparate services, securing their access, and ensuring their efficient operation presents a formidable challenge for developers and architects alike. It is within this demanding landscape that the API Gateway emerges not just as a useful tool, but as an indispensable cornerstone, acting as the intelligent traffic controller and security guard for the entire digital ecosystem.
This comprehensive guide delves deep into the fundamental concepts underpinning the API Gateway, unraveling its multifaceted role, dissecting its core functionalities, and exploring the profound impact it has on the development, deployment, and management of modern applications. We will journey through the architectural philosophies that necessitate its existence, elucidate the myriad problems it elegantly solves, and illuminate the detailed mechanisms through which it empowers organizations to build more resilient, secure, and performant systems. By the end of this exploration, you will possess a master-level understanding of this critical architectural component, equipping you to leverage its full potential in your own distributed environments.
What is an API Gateway? The Digital Front Door
At its heart, an API Gateway is a server that acts as a single entry point for a group of microservices or APIs. Imagine a bustling city with countless specialized shops, offices, and residential buildings. Instead of clients needing to know the exact location and entrance for every single destination, the city implements a grand central station or a reception area that intelligently directs visitors to their correct locations, handles initial security checks, and even offers information or minor services upfront. This analogy perfectly encapsulates the role of an API Gateway. It stands as the vigilant sentinel at the perimeter of your application landscape, intercepting all incoming client requests and routing them to the appropriate backend services.
Prior to the widespread adoption of API Gateways, clients often communicated directly with individual backend services. In a monolithic architecture, this wasn't a significant issue, as there was typically only one large service to interact with. However, with the paradigm shift towards microservices, where an application might comprise dozens or even hundreds of independent services, direct client-to-service communication quickly becomes unwieldy and problematic. Each client would need to manage connections, authentication, and error handling for multiple endpoints, leading to bloated client-side code and a tighter coupling between the client and the ever-evolving backend services. The API Gateway elegantly abstracts this complexity, presenting a unified, simplified interface to the outside world, effectively shielding clients from the intricate, distributed nature of the backend.
The gateway's position in the request-response flow is strategically critical. When a client application (be it a web browser, a mobile app, or another service) needs to interact with your backend, its request first hits the API Gateway. The gateway then performs a series of operations based on predefined rules and policies, which might include authentication, authorization, rate limiting, request transformation, and intelligent routing. Only after passing these checks and modifications does the request proceed to the actual backend service designed to fulfill it. Once the backend service processes the request and generates a response, that response often flows back through the API Gateway, which can then apply further transformations (e.g., aggregating data from multiple services, formatting the output) before sending it back to the client. This centralized control point ensures consistency, security, and efficiency across all external interactions, making the API Gateway far more than just a simple proxy; it is a sophisticated orchestration layer that significantly enhances the entire API ecosystem.
Why Do We Need an API Gateway? The Problems It Solves
The transition to distributed architectures, while offering immense benefits in terms of scalability and maintainability, also introduces a fresh set of challenges. Without a centralized control mechanism, these challenges can quickly spiral out of control, leading to a brittle, insecure, and difficult-to-manage system. The API Gateway acts as the crucial antidote to these modern architectural ailments, addressing a spectrum of concerns that range from client-side complexity to robust security enforcement and operational visibility. Understanding these problems and how the gateway mitigates them is key to appreciating its indispensable role.
Complexity Hiding and Client Simplification
One of the most immediate benefits of an API Gateway is its ability to hide the inherent complexity of a microservices architecture from client applications. In a distributed system, a single logical operation from a client's perspective might involve calls to several backend services. For instance, loading a user profile page might require fetching data from a UserService, an OrderService, and a NotificationService. Without a gateway, the client would be responsible for knowing the specific endpoints of these three services, making three separate network calls, aggregating the data, and handling potential failures from each. This not only burdens the client with significant operational logic but also tightly couples the client to the internal structure of the microservices, making future refactoring or service changes a nightmare. The API Gateway consolidates these interactions, allowing the client to make a single, simplified request to the gateway (e.g., GET /user/{id}/profile). The gateway then internally orchestrates the calls to the necessary backend services, aggregates their responses, and presents a single, coherent response back to the client. This dramatically simplifies client-side development, reduces network chattiness, and insulates clients from backend architectural changes.
Reduced Round Trips and Optimized Performance
Direct client-to-microservices communication often results in numerous network round trips, particularly when a client needs to retrieve data from multiple services to render a single view. Each round trip incurs latency, which can degrade the user experience, especially for mobile applications or clients operating over high-latency networks. An API Gateway can aggregate these multiple service calls into a single request, executing them in parallel or sequentially on the backend and returning a consolidated response to the client. This significantly reduces the number of network interactions between the client and the server-side infrastructure, leading to lower latency and improved overall application performance. By moving the burden of orchestration from the client to a dedicated, high-performance gateway, applications can feel snappier and more responsive, directly impacting user satisfaction.
Decoupling Clients from Services for Independent Evolution
In a truly agile microservices environment, individual services should be able to evolve and deploy independently without impacting other services or client applications. However, if clients are directly coupled to service endpoints, any change to a service's interface, location, or protocol could necessitate updates to all consuming clients. This tight coupling undermines the very principle of microservices. The API Gateway acts as an effective decoupling layer. Clients interact solely with the stable, well-defined interface exposed by the gateway. The gateway, in turn, handles the dynamic mapping and routing to the underlying services. This means that backend services can be refactored, new versions deployed, or even entirely new services swapped in, all without requiring any changes to the client applications, as long as the gateway's external API contract remains consistent. This independence accelerates development cycles, reduces integration risks, and allows teams to innovate more freely.
Centralized Security Enhancement
Security is paramount in any application, and in distributed systems, managing security across numerous services can be a daunting task. Each service would ideally need to implement its own authentication, authorization, and perhaps even rate limiting mechanisms. This leads to redundant code, inconsistent security policies, and increased surface area for vulnerabilities. The API Gateway offers a powerful solution by centralizing these cross-cutting security concerns. All client requests must first pass through the gateway, making it the ideal choke point to enforce security policies. It can handle user authentication (e.g., validating JWT tokens, integrating with OAuth2 providers), implement granular authorization rules (determining if a user has permission to access a specific resource), and apply rate limiting to prevent abuse or denial-of-service attacks. This centralization ensures consistent security across all services, simplifies security auditing, and reduces the risk of misconfigurations that could expose sensitive data. Furthermore, by placing a Web Application Firewall (WAF) functionality at the gateway level, common web vulnerabilities like SQL injection and XSS can be mitigated before they even reach the backend services.
Improved Observability and Monitoring
Understanding the health, performance, and usage patterns of a complex distributed system is critical for troubleshooting, capacity planning, and business intelligence. Without a centralized point, collecting meaningful metrics and logs from every individual microservice can be cumbersome and fragmented. The API Gateway provides an invaluable vantage point for comprehensive observability. As all external traffic flows through it, the gateway can collect detailed access logs, record performance metrics (e.g., latency, throughput), and integrate with distributed tracing systems. This consolidated data provides a holistic view of API usage, identifies performance bottlenecks, and helps in quickly diagnosing issues. Centralized logging and monitoring facilitate faster incident response, proactive problem detection, and better insights into how consumers are interacting with the APIs, turning the gateway into a data-rich hub for operational intelligence.
Robust Traffic Management
Beyond simple routing, an API Gateway offers sophisticated traffic management capabilities essential for maintaining the stability and performance of a distributed system. It can intelligently route requests based on various criteria, such as the load on backend services (load balancing), geographical location of the client, or even specific user attributes. The gateway can implement caching to serve frequently requested data without burdening backend services, significantly reducing latency and server load. Throttling mechanisms can be put in place to limit the number of requests a particular client or API endpoint can make within a given timeframe, protecting backend services from being overwhelmed. Furthermore, advanced features like A/B testing or canary deployments can be orchestrated at the gateway level, allowing new versions of services to be gradually rolled out to a subset of users, minimizing risk and facilitating continuous delivery.
Protocol Translation and Legacy System Integration
Modern applications often need to interact with a diverse ecosystem of systems, some of which may use older or non-standard protocols (e.g., SOAP, fixed-width files, proprietary message queues), while newer services prefer REST or gRPC. Client applications, especially mobile ones, typically prefer lightweight RESTful JSON APIs. An API Gateway can act as a protocol translator, exposing a unified, modern interface (e.g., REST over HTTP/2 with JSON payloads) to clients, while internally communicating with backend services using their native protocols. This is particularly useful when integrating with legacy systems, allowing them to remain operational without requiring extensive rewrites, while simultaneously providing a modern API experience to new clients. The gateway bridges the technological gap, making disparate systems appear cohesive and interoperable.
In essence, the API Gateway transforms a collection of independent services into a cohesive, secure, and manageable API product. It addresses the inherent complexities of distributed systems by centralizing cross-cutting concerns, providing a single point of entry and control, and ultimately enhancing the developer experience, operational efficiency, and overall resilience of the entire application landscape.
Core Concepts and Features of an API Gateway
The power of an API Gateway lies in its rich set of functionalities, each designed to address a specific challenge within distributed API architectures. These features work in concert to create a robust, secure, and efficient layer between clients and backend services. Understanding these core concepts is fundamental to effectively designing and implementing an API Gateway strategy.
Request Routing: The Intelligent Traffic Director
The most fundamental function of an API Gateway is request routing. When a request arrives at the gateway, it needs to determine which backend service is responsible for fulfilling that request. This is achieved through a set of predefined rules that map incoming request attributes to specific backend service endpoints.
Details: * Path-Based Routing: This is the most common method. The gateway examines the URL path of the incoming request. For example, a request to /users/{id} might be routed to the UserService, while a request to /products/{id} goes to the ProductService. This allows for a clean, domain-driven organization of APIs. * Host-Based Routing: In multi-tenant or multi-application environments, requests can be routed based on the hostname. For instance, api.example.com might go to one set of services, while dev-api.example.com goes to a development environment. * Header-Based Routing: Routing decisions can also be made based on specific HTTP headers present in the request. This is often used for A/B testing, canary deployments, or internal feature flags, where a subset of users (identified by a header) might be routed to a new version of a service. * Query Parameter-Based Routing: Similar to header-based routing, certain query parameters can dictate the routing logic, although this is less common for primary routing due to its impact on URL readability and cacheability. * Dynamic Routing: Advanced gateways support dynamic routing, where rules can be updated on the fly without restarting the gateway. This is crucial for agile environments where services are frequently deployed and scaled. Some gateways can even integrate with service discovery mechanisms (like Consul or Eureka) to automatically discover and route to healthy service instances, adapting to changes in the service landscape in real-time. This sophisticated routing ensures that requests always reach the correct, available, and optimal backend service.
Authentication and Authorization: The Digital Bouncer
Security is non-negotiable, and the API Gateway serves as the primary enforcement point for access control, acting as the digital bouncer for your entire API ecosystem.
Details: * Authentication: The process of verifying the identity of the client making the request. The gateway can validate various forms of credentials: * API Keys: Simple, secret strings usually passed in headers. The gateway checks if the key is valid and often maps it to a specific client or application for tracking and rate limiting. * JSON Web Tokens (JWTs): A standard for securely transmitting information between parties as a JSON object. The gateway can validate the signature of the JWT, check its expiration, and ensure it contains the expected claims (e.g., user ID, roles). This offloads token validation from individual services. * OAuth2 / OpenID Connect: The gateway can integrate with OAuth2 authorization servers to facilitate token issuance and validation. It can act as a resource server, validating access tokens and perhaps even refreshing them if needed, before forwarding the request with appropriate user context to the backend service. * Authorization: Once authenticated, the gateway determines if the authenticated client or user has the necessary permissions to access the requested resource or perform the requested action. * Role-Based Access Control (RBAC): The gateway can extract user roles from authentication tokens (e.g., "admin," "customer") and enforce policies that grant or deny access based on these roles for specific API endpoints. * Attribute-Based Access Control (ABAC): More granular authorization can be based on various attributes of the user, the resource, or the environment. * By centralizing these mechanisms, the gateway ensures consistent security policies across all APIs, reduces redundant security logic in backend services, and provides a single, audited point for security enforcement, significantly enhancing the overall security posture.
Rate Limiting and Throttling: Preventing Overload and Abuse
To protect backend services from being overwhelmed by a sudden surge of requests, prevent malicious attacks (like DoS), and ensure fair usage among consumers, API Gateways implement rate limiting and throttling.
Details: * Rate Limiting: Defines the maximum number of requests a client can make within a specified time window (e.g., 100 requests per minute). Once the limit is reached, subsequent requests from that client are rejected or queued until the window resets. * Throttling: A more general term, often implying a softer limit where requests might be delayed rather than immediately rejected, or a tiered approach where different clients (e.g., free vs. premium tiers) have different limits. * Strategies: * Fixed Window: A simple approach where a counter resets at fixed intervals. If the counter exceeds the limit within the window, requests are blocked. * Sliding Window: More sophisticated, it tracks requests over a rolling time window, providing a smoother enforcement. * Leaky Bucket / Token Bucket: These algorithms offer more control over request processing rates, smoothing out bursts of traffic. * Granularity: Rate limits can be applied globally, per API endpoint, per client (identified by API key or IP address), or even per authenticated user. The gateway acts as the enforcement point, maintaining counters and applying policies before requests reach the backend. This capability is crucial for maintaining service stability, preventing resource exhaustion, and ensuring that all consumers receive a consistent quality of service without individual bad actors impacting the experience of others.
Load Balancing: Distributing the Workload
When multiple instances of a backend service are running to handle increased demand or provide high availability, the API Gateway intelligently distributes incoming requests across these instances.
Details: * Algorithm Types: * Round-Robin: Requests are distributed sequentially to each server in the pool. * Least Connections: Directs new requests to the server with the fewest active connections, aiming for even distribution of current load. * IP Hash: Routes requests from a particular client (identified by IP address) to the same server, which can be useful for maintaining session state without sticky sessions. * Weighted Load Balancing: Allows administrators to assign different weights to servers based on their capacity or performance, sending more traffic to more powerful servers. * Health Checks: The gateway continuously monitors the health of backend service instances. If an instance becomes unhealthy (e.g., fails to respond to a ping or a specific endpoint check), the gateway temporarily removes it from the load balancing pool, preventing requests from being sent to failing services. This ensures that clients only interact with healthy and responsive services, significantly improving the overall reliability and uptime of the application. Load balancing, combined with service discovery, makes the gateway a dynamic and adaptive component in managing fluctuating service loads.
Caching: Boosting Performance and Reducing Backend Load
Caching involves storing copies of responses to frequently accessed API requests directly within the API Gateway. When a subsequent identical request arrives, the gateway can serve the cached response immediately, without forwarding the request to the backend service.
Details: * Benefits: * Reduced Latency: Responses are served much faster as they don't incur the overhead of backend processing and network round trips to the service. * Reduced Backend Load: Backend services are shielded from repetitive requests, freeing up their resources to process unique or complex requests. This can lead to significant cost savings and improved scalability for the backend. * Cache Invalidation: A critical aspect of caching is ensuring that cached data remains fresh. Strategies include: * Time-To-Live (TTL): Responses are cached for a specific duration, after which they expire and must be re-fetched from the backend. * Event-Driven Invalidation: The gateway can be notified by backend services when data changes, prompting it to invalidate specific cached entries. * Cache-Control Headers: HTTP Cache-Control headers from backend services can instruct the gateway on caching behavior. * Granularity: Caching can be applied to specific endpoints, methods, or based on query parameters. It's most effective for idempotent GET requests where the data changes infrequently. Judicious use of caching can dramatically improve API performance and scalability.
Request/Response Transformation: Adapting to Diverse Needs
The API Gateway can modify incoming requests before they reach backend services and outgoing responses before they are sent back to clients. This is a powerful feature for adapting APIs to different client requirements or internal service expectations.
Details: * Request Transformation: * Header Manipulation: Adding, removing, or modifying HTTP headers (e.g., adding an X-Request-ID for tracing, injecting authentication tokens, removing sensitive client headers). * Body Transformation: Converting request payloads from one format to another (e.g., XML to JSON, or restructuring a JSON payload to match a service's expected input schema). * Query Parameter Modification: Adding default parameters, removing unnecessary ones, or mapping them to different names. * Response Transformation: * Data Aggregation: Combining data from multiple backend service responses into a single, cohesive response for the client. This is crucial for microservices architectures where a single logical resource might be composed of data from several services. * Payload Modification: Filtering out sensitive fields, flattening complex structures, or enriching the response with additional data before sending it to the client. * Status Code Mapping: Translating internal service error codes into more generalized or client-friendly HTTP status codes. * These transformations allow the gateway to act as an adaptable facade, bridging gaps between diverse client expectations and varied backend service implementations, providing a consistent and optimal API experience without forcing changes on either side.
Logging and Monitoring: The Eye on the Digital Pulse
For any complex system, visibility into its operations is paramount. The API Gateway, as the central point of ingress, is perfectly positioned to collect comprehensive logs and metrics.
Details: * Access Logging: Records every incoming request, including client IP, timestamp, requested path, HTTP method, status code, response size, and latency. This provides an invaluable audit trail and a rich dataset for analysis. * Error Logging: Captures details of any errors encountered by the gateway itself or errors returned by backend services, facilitating quick debugging and issue resolution. * Performance Metrics: Collects key performance indicators (KPIs) such as request rate (RPS), average response time, error rates, and CPU/memory usage of the gateway instance. * Integration with Observability Stacks: These logs and metrics are typically integrated with external logging platforms (like ELK Stack, Splunk, Logstash) and monitoring systems (like Prometheus, Grafana, Datadog). This allows for centralized log aggregation, real-time dashboards, alerting, and deep historical analysis. * Distributed Tracing: The gateway can inject unique trace IDs into incoming requests and propagate them through the backend services. This enables end-to-end visibility of a request's journey across multiple services, which is crucial for diagnosing latency issues or failures in a microservices environment. The rich data collected by the gateway is indispensable for understanding API usage, troubleshooting problems, identifying performance bottlenecks, and ensuring the overall health and stability of the entire system.
Circuit Breaker and Resilience Patterns: Safeguarding Against Cascading Failures
In a distributed system, a failure in one service can rapidly cascade, overwhelming other dependent services and potentially leading to a complete system outage. The API Gateway can implement resilience patterns like the Circuit Breaker to prevent such scenarios.
Details: * Circuit Breaker Pattern: Inspired by electrical circuit breakers, this pattern monitors calls to a particular backend service. If the service starts failing (e.g., a high percentage of requests time out or return errors), the circuit "trips" open. During this open state, the gateway stops sending requests to the failing service and immediately returns a fallback response (e.g., an error message or cached data) to the client. After a predefined time, the circuit enters a "half-open" state, allowing a few test requests to pass through. If these succeed, the circuit closes, and normal traffic resumes; otherwise, it returns to the open state. * Benefits: * Prevents Cascading Failures: A failing service won't bring down the entire system. * Faster Failure Detection: Clients receive immediate feedback instead of waiting for timeouts. * Allows Recovery: Gives the failing service time to recover without being continuously bombarded with requests. * Other Resilience Patterns: * Retry: The gateway can automatically retry failed requests (with backoff) if the error is deemed transient. * Timeout: Enforcing strict timeouts for backend service calls to prevent long-running requests from hogging resources. * By incorporating these patterns, the API Gateway acts as a critical line of defense, making the entire distributed system more robust and fault-tolerant, significantly improving its overall reliability and user experience even in the face of partial service degradation.
API Versioning: Managing Evolution Gracefully
As applications evolve, so too do their APIs. Managing different versions of an API is crucial to avoid breaking existing client applications while allowing for new features and improvements. The API Gateway provides a centralized mechanism for managing API versions.
Details: * Versioning Strategies: * URI Versioning: The version number is embedded directly in the URL path (e.g., /v1/users, /v2/users). This is straightforward but can affect URL readability and caching. * Header Versioning: The version is specified in a custom HTTP header (e.g., X-API-Version: 1). This keeps URLs cleaner but requires clients to manage custom headers. * Query Parameter Versioning: The version is passed as a query parameter (e.g., /users?api-version=1). Simple to implement but can conflict with other parameters and is often discouraged for primary versioning. * Gateway's Role: The API Gateway inspects the incoming request (based on the chosen versioning strategy) and routes it to the appropriate version of the backend service. For instance, requests to /v1/products might go to the ProductServiceV1, while /v2/products goes to ProductServiceV2. This allows different client applications to consume different API versions simultaneously, facilitating a smooth transition period when new versions are deployed. The gateway can also perform transformations to bridge minor differences between versions, allowing older clients to continue using a slightly updated service without immediate changes. This centralized version management is critical for maintaining backward compatibility and enabling continuous evolution of your APIs without disruption.
Protocol Translation: Bridging the Communication Gap
In diverse enterprise environments, backend services might communicate using a variety of protocols (e.g., REST, gRPC, SOAP, message queues). However, client applications, especially web and mobile, often prefer a simpler, unified interface, typically RESTful JSON over HTTP. The API Gateway can act as a protocol translator.
Details: * The gateway receives an incoming request in one protocol (e.g., an HTTP GET request for a user). It then translates this request into the native protocol of the backend service (e.g., making an internal gRPC call to a UserService to fetch user details). Once the backend service responds, the gateway translates that response back into the client's expected format (e.g., a JSON payload in an HTTP response). * Use Cases: * Modernizing Legacy Systems: Exposing older SOAP services or proprietary systems as modern RESTful APIs without rewriting the backend. * Interoperability: Allowing services built with different communication technologies to seamlessly interact through a common gateway interface. * Optimizing Internal Communication: While clients use HTTP/REST, the gateway might use more efficient internal protocols like gRPC for communication with microservices, leveraging their benefits without exposing their complexity to external consumers. * This feature makes the API Gateway an invaluable component for integrating heterogeneous systems and providing a consistent, modern API experience to clients, regardless of the underlying backend technology stack.
Developer Portal Integration and API Management: Beyond Just a Proxy
While the functionalities discussed above focus on the technical execution of API requests, an API Gateway is often a fundamental component of a broader API management platform. Such platforms extend beyond mere proxying to encompass the entire API lifecycle, including design, documentation, publication, discovery, and governance.
Details: * Developer Portal: A self-service website where API consumers (internal or external developers) can discover available APIs, browse interactive documentation, subscribe to APIs, generate API keys, and monitor their own usage. The gateway feeds usage data to the portal and enforces the subscription policies defined there. * Lifecycle Management: API management platforms, with the gateway at their core, help manage the entire lifecycle of an API—from its initial design and mocking through development, testing, publication, versioning, and eventually decommissioning. This ensures a structured and controlled process for API evolution. * Monetization: For commercial APIs, the gateway helps enforce billing tiers, track usage, and manage access based on subscription plans, integrated with billing systems. * APIPark Example: Beyond just acting as a sophisticated proxy, many modern API gateways, especially those that are part of comprehensive API management platforms, also facilitate the developer experience and overall API governance. They often integrate with or are a core component of a developer portal, allowing for streamlined API discovery, documentation, and subscription. For instance, platforms like APIPark, an open-source AI gateway and API management platform, not only handle the technical aspects of routing and security but also offer features that simplify the entire API lifecycle. This includes quick integration of over 100 AI models, a unified API format for AI invocation, prompt encapsulation into REST APIs, end-to-end API lifecycle management, and detailed API call logging for powerful data analysis. Such platforms are crucial for effective API governance, enabling teams to share API services, manage access permissions for different tenants, and even require approval for API resource access, ensuring both efficiency and security in a scalable manner, even offering performance rivaling Nginx for high-throughput scenarios.
Security Policies and WAF Capabilities: Advanced Threat Protection
Beyond basic authentication and authorization, an API Gateway can incorporate more advanced security policies and Web Application Firewall (WAF) capabilities to protect against sophisticated attacks.
Details: * Input Validation: The gateway can validate incoming request payloads against predefined schemas (e.g., JSON Schema). This prevents malformed requests or those containing unexpected data types from reaching backend services, mitigating risks like injection attacks. * Threat Protection: Implementing rules to detect and block common web vulnerabilities: * SQL Injection: Detecting and preventing malicious SQL commands in input fields. * Cross-Site Scripting (XSS): Blocking scripts injected into input that could harm other users. * Cross-Site Request Forgery (CSRF): Protecting against unauthorized commands transmitted from a trusted user. * XML External Entities (XXE): Preventing attacks that exploit XML parsers. * IP Whitelisting/Blacklisting: Allowing or blocking requests from specific IP addresses or ranges. * DDoS Mitigation: Working in conjunction with other network layers to absorb or deflect distributed denial-of-service attacks. * These advanced security features at the gateway level provide an additional layer of defense, shielding backend services from a wide array of cyber threats and ensuring that only legitimate and safe requests are processed. This proactive approach significantly reduces the attack surface and fortifies the entire application against malicious intent.
By combining these powerful features, an API Gateway transforms from a simple proxy into a highly intelligent, secure, and resilient orchestration layer. It is the central nervous system for your distributed APIs, ensuring their efficient operation, robust security, and seamless evolution.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
Architecture and Deployment Patterns
The implementation and deployment of an API Gateway can vary significantly depending on the specific architectural needs, scale, and existing infrastructure of an organization. While the core functionalities remain consistent, the way the gateway is integrated into the overall system influences its characteristics and operational considerations.
Centralized API Gateway: The Monolithic Entry Point
The most common and straightforward deployment pattern involves a single, centralized API Gateway instance (or a highly available cluster of instances) that serves as the sole entry point for all external traffic destined for your backend services.
Details: * Concept: All client requests, regardless of which backend service they target, first hit this central gateway. The gateway then applies all the necessary policies (authentication, routing, rate limiting, etc.) and forwards the request to the appropriate internal service. * Advantages: * Simplicity: Easier to manage and configure security and traffic policies in one place. * Consistency: Ensures uniform application of cross-cutting concerns across all APIs. * Clear Boundaries: Provides a distinct separation between external clients and internal services. * Disadvantages: * Single Point of Failure (SPOF): If the central gateway goes down, all APIs become inaccessible. This necessitates robust high availability (HA) and disaster recovery (DR) strategies. * Performance Bottleneck: As all traffic passes through it, the gateway can become a performance bottleneck if not scaled adequately. * Monolithic Gateway: Can become complex to manage as the number of services and policies grows, risking a "monolithic gateway" anti-pattern. * Use Cases: Suitable for organizations starting with microservices, or those with a moderate number of APIs where centralized control is a priority. Often deployed at the edge of the network.
Decentralized/Sidecar Gateway (Service Mesh Context): Distributing the Gateway Logic
As systems grow and complexity increases, the idea of distributing gateway-like functionalities closer to the services themselves has gained traction, particularly with the rise of service meshes.
Details: * Concept: In this pattern, the "gateway" functionality is not a single, external component but rather distributed across individual service instances, often implemented as a "sidecar" proxy alongside each service. This sidecar handles ingress and egress traffic for its specific service, applying policies relevant to that service. An "ingress gateway" (like an Envoy gateway in a service mesh) still exists at the edge, but its role is primarily to route external traffic into the mesh, while fine-grained policy enforcement moves to the sidecars. * Advantages: * Reduced Centralized Bottleneck: Distributes the load and responsibility, improving scalability. * Service-Specific Policies: Each service can define and enforce its own specific security, routing, and resilience policies directly in its sidecar. * Decoupling: Further decouples services from external gateway concerns. * Enhanced Resilience: Failure of one sidecar or service doesn't necessarily impact others. * Disadvantages: * Increased Operational Overhead: Managing sidecars for every service can add complexity to deployment, monitoring, and debugging. * Learning Curve: Requires familiarity with service mesh concepts and tooling (e.g., Istio, Linkerd). * Use Cases: Ideal for large-scale microservices deployments, organizations embracing service mesh architectures, and scenarios requiring extremely granular control and isolation per service.
Edge Gateway vs. Internal Gateway: External and Internal Traffic Control
It's important to differentiate between gateways that handle external client traffic and those that manage internal service-to-service communication.
Details: * Edge Gateway (North-South Traffic): * This is the traditional API Gateway discussed throughout, sitting at the perimeter of the network. * It handles requests from external clients (web, mobile, third-party apps). * Focuses on concerns like client authentication, rate limiting, API versioning, external-facing transformations, and security against external threats. * Often the first point of contact for any inbound request. * Internal Gateway (East-West Traffic) / Service Mesh: * Manages communication between microservices within the internal network. * Can enforce internal authorization policies, facilitate service discovery, apply internal load balancing, and implement resilience patterns like circuit breakers for service-to-service calls. * While an edge gateway might route to an internal service, an internal gateway or service mesh component handles the subsequent hops if that service calls other internal services. * Combined Approach: Many organizations use both. An edge gateway handles external traffic, translating it into internal service calls. Within the cluster, a service mesh or internal gateway then manages the intricate web of inter-service communication. This hybrid approach offers robust control and optimization for both external and internal traffic flows.
Deployment Considerations: Scalability, High Availability, and Performance
Regardless of the chosen pattern, several critical factors must be considered during the deployment phase to ensure the API Gateway itself is robust and reliable.
Details: * Scalability: The gateway must be able to handle anticipated traffic volumes and scale horizontally (by adding more instances) or vertically (by increasing resources for existing instances). Cloud-native gateway solutions often leverage auto-scaling features. * High Availability (HA): To mitigate the SPOF risk, gateway instances should be deployed in redundant configurations across multiple availability zones or data centers. Load balancers are typically placed in front of the gateway cluster to distribute traffic and ensure failover. * Performance: The gateway introduces an additional hop, potentially adding latency. Its performance (throughput, response time) must be optimized. This involves efficient code, minimal overhead for policy enforcement, and judicious use of caching. * Observability: Comprehensive logging, monitoring, and alerting specifically for the gateway instances are crucial. This allows operators to quickly identify and resolve issues with the gateway itself. * Configuration Management: Managing the complex routing rules, policies, and transformations for the gateway requires robust configuration management tools and potentially a GitOps approach for version control and automated deployment of gateway configurations. * Monolithic Gateway vs. Micro-Gateways: In very large systems, a single centralized gateway might become too complex. A strategy of "micro-gateways" can be adopted, where smaller, specialized gateways handle specific domains or sets of APIs (e.g., one gateway for /users related APIs, another for /products). This decentralizes configuration and reduces the blast radius of failures, while still providing a controlled entry point.
Each architectural and deployment pattern offers trade-offs. The choice depends on the organization's scale, team expertise, performance requirements, and desired level of centralized control versus distributed autonomy. A well-designed API Gateway architecture is foundational to the success and resilience of any modern distributed application.
Challenges and Considerations
While the API Gateway offers a wealth of benefits, its implementation is not without potential pitfalls. Architects and developers must be aware of these challenges to design and operate API Gateway solutions effectively, mitigating risks and maximizing their value.
Single Point of Failure (SPOF): The Achilles' Heel
The very strength of the API Gateway—its centrality—can also be its greatest weakness. If the gateway fails, all services behind it become inaccessible, regardless of their individual health.
Details: * Risk: A poorly configured or single-instance API Gateway represents a critical SPOF for the entire application. Downtime of the gateway directly translates to downtime for the entire system, leading to business disruption and user dissatisfaction. * Mitigation: * High Availability (HA) Clustering: Deploy multiple gateway instances across different availability zones or data centers. Use an external load balancer (like AWS ELB, Azure Load Balancer, or NGINX) to distribute traffic among these instances and automatically failover if one instance becomes unhealthy. * Disaster Recovery (DR): Establish robust DR plans, including geographically distributed deployments and rapid recovery procedures, to ensure business continuity in the event of major regional outages. * Monitoring and Alerting: Implement comprehensive monitoring specifically for the gateway's health and performance, with proactive alerts for any signs of degradation or failure, enabling rapid response from operations teams. * Addressing the SPOF is paramount and requires significant investment in infrastructure, redundancy, and operational vigilance.
Increased Latency: The Additional Hop
Introducing an API Gateway into the request path necessarily adds an extra network hop and processing overhead. While often negligible, this can be a concern for highly latency-sensitive applications.
Details: * Impact: Each policy enforcement (authentication, authorization, rate limiting, transformation) takes a small amount of time. Multiplied by hundreds or thousands of requests per second, this cumulative overhead can add perceptible latency, especially if the gateway itself is under-resourced or inefficiently configured. * Mitigation: * Performance Optimization: Use highly performant gateway software. Optimize gateway configuration to minimize unnecessary processing. * Efficient Policy Design: Streamline policies; avoid overly complex transformations or excessive sequential checks. * Caching: Leverage gateway caching extensively for frequently accessed, immutable data to bypass backend services entirely for many requests. * Hardware/Resources: Provision adequate CPU, memory, and network resources for the gateway instances. * Asynchronous Processing: Where possible, non-critical gateway functions (like detailed logging to external systems) can be performed asynchronously. * While an extra hop is unavoidable, its impact can be minimized through careful design, optimization, and resource allocation, ensuring that the benefits of the gateway outweigh this minor latency increase.
Complexity of Configuration: The Management Burden
Configuring an API Gateway can become incredibly complex, especially in systems with many services, diverse clients, and intricate routing and security policies.
Details: * Challenge: Managing hundreds or thousands of routing rules, rate limits, authentication schemes, transformation templates, and access control policies across a large number of APIs can be a monumental task. Manual configuration is error-prone and doesn't scale. * Mitigation: * Configuration as Code (GitOps): Treat gateway configurations as code, storing them in version control (e.g., Git). This enables automated deployment, peer review, and rollback capabilities. * Centralized Management Tools: Utilize API management platforms (which often include a gateway component) that provide intuitive GUIs, dashboards, and programmatic interfaces (e.g., REST APIs) for managing gateway configurations. * Templating and Reusability: Design reusable policy templates (e.g., a standard authentication policy) to apply across multiple APIs, reducing redundancy and ensuring consistency. * Domain-Driven Design: Organize gateway configurations logically based on business domains or service groups to reduce cognitive load. * Automated Testing: Implement automated tests for gateway configurations to catch errors before deployment. * Effective configuration management is crucial to prevent the API Gateway itself from becoming a source of operational complexity and errors, especially as the number of managed APIs grows.
Over-aggregation and the "Monolithic Gateway" Anti-Pattern: A New Bottleneck
There's a risk that the API Gateway, intended to solve the monolith problem, can inadvertently become a new bottleneck or a "monolithic gateway" itself.
Details: * Risk: If too much business logic, data aggregation, or complex transformations are pushed into the gateway, it can become overly large, difficult to maintain, and slow to deploy. It essentially becomes a new monolith, albeit one that sits in front of other microservices. This defeats the purpose of microservices by reintroducing tight coupling and reducing the independent deployability of teams. * Mitigation: * Keep it Lean: The gateway should focus primarily on cross-cutting concerns (routing, security, rate limiting, basic transformations). Business logic and complex data orchestrations should remain within the specialized backend services. * Micro-Gateways: For very large systems, consider a decentralized approach with multiple, smaller gateways, each responsible for a specific domain or group of APIs. This helps distribute the complexity and responsibility. * Service-Level Aggregation: If complex data aggregation is needed, it might be better handled by a dedicated "backend for frontend" (BFF) service that aggregates data from multiple microservices specifically for a particular client type, rather than burdening the general-purpose API Gateway. * The goal is to find the right balance, using the gateway for its intended purpose as an intelligent traffic director and policy enforcer, without overloading it with application-specific business logic that belongs elsewhere.
Vendor Lock-in and Customization Limitations: Flexibility vs. Features
Choosing an API Gateway solution involves committing to a particular vendor or open-source project, which can have implications for flexibility and future extensibility.
Details: * Challenge: Commercial API Gateway products often provide rich features, enterprise support, and polished UIs but may come with high licensing costs and limits on customization. Open-source solutions offer more flexibility but require internal expertise for setup, maintenance, and feature development. Switching gateway solutions later can be a significant undertaking. * Mitigation: * Careful Evaluation: Thoroughly evaluate different gateway solutions (commercial, open-source, cloud-native) against current and future requirements, considering factors like features, performance, scalability, ease of use, community support, and cost. * Standardization: Where possible, leverage standard protocols (HTTP, OAuth2, OpenID Connect) that are widely supported, making migration easier if needed. * Customization Capabilities: If custom logic is anticipated, select a gateway that offers strong extensibility mechanisms (e.g., plugins, scripting capabilities, serverless functions). * Avoid Over-Customization: Resist the urge to heavily customize an off-the-shelf gateway if that customization ties you too tightly to its internal workings. Prioritize features that are core to the gateway's mission. * Making an informed choice early on, balancing features against flexibility and cost, is crucial to avoid future headaches and ensure the API Gateway remains a valuable asset rather than a limiting factor.
By actively addressing these challenges, organizations can harness the full power of an API Gateway while minimizing its associated risks, ultimately building more robust, secure, and scalable distributed applications.
Popular API Gateway Solutions
The landscape of API Gateway solutions is diverse, offering options from robust commercial platforms to flexible open-source projects and cloud-native services. Each category caters to different needs, scales, and integration preferences.
- Cloud-Native API Gateways:
- AWS API Gateway: A fully managed service that makes it easy for developers to create, publish, maintain, monitor, and secure APIs at any scale. It integrates seamlessly with other AWS services (Lambda, EC2, S3) and provides comprehensive features including authentication, authorization, rate limiting, caching, and versioning. Its serverless nature makes it highly scalable and cost-effective for event-driven architectures.
- Azure API Management: Microsoft's offering for managing external and internal APIs. It provides a developer portal, API publishing, security policies, analytics, and integrations with Azure services. It supports hybrid and multi-cloud environments.
- Google Cloud Apigee API Management (formerly Apigee Edge): A leading enterprise-grade API management platform acquired by Google. It offers advanced analytics, monetization features, security, and a robust developer portal, often favored by large enterprises with complex API ecosystems.
- Google Cloud Endpoints: A distributed API management system that uses the Envoy proxy for APIs running on Google Cloud. It's more lightweight than Apigee and integrates well with Google Kubernetes Engine and App Engine.
- Open-Source API Gateways:
- Kong Gateway: One of the most popular open-source API Gateways, built on NGINX and Lua. It's highly extensible via plugins and offers a wide range of features including authentication, traffic control, analytics, and transformations. Kong also offers an enterprise version with advanced features and commercial support.
- Tyk Open Source API Gateway: Another feature-rich open-source gateway written in Go. It focuses on performance, scalability, and ease of use, offering a powerful policy engine, analytics, and a developer portal. Tyk also has a commercial offering.
- Envoy Proxy: While primarily a high-performance L7 proxy and service mesh component, Envoy can be configured to act as an edge API Gateway. It's highly programmable, performant, and integral to many service mesh implementations (like Istio). It requires more configuration effort but offers unparalleled flexibility.
- Ocelot: A lightweight, open-source API Gateway for .NET Core applications. It's designed for microservices architectures that use .NET and provides routing, request aggregation, authentication, and other gateway features specifically for the .NET ecosystem.
- NGINX (and NGINX Plus): While primarily a web server and reverse proxy, NGINX can be configured to act as a basic API Gateway, handling routing, load balancing, caching, and basic authentication. NGINX Plus is its commercial version, offering advanced features like active health checks, API management dashboards, and more sophisticated load balancing algorithms.
- APIPark: An emerging open-source AI gateway and API management platform. As highlighted earlier, APIPark distinguishes itself with quick integration of 100+ AI models, unified API formats for AI invocation, prompt encapsulation into REST APIs, and end-to-end API lifecycle management, making it an excellent choice for organizations building AI-driven applications or needing robust API governance in their distributed environments. Its focus on AI integration and developer portal capabilities sets it apart.
- Self-Managed/Hybrid Solutions:
- Some organizations build their own custom gateway solutions, often using frameworks like Spring Cloud Gateway (for Java) or leveraging existing reverse proxies with custom scripting. This offers maximum flexibility but comes with the responsibility of maintenance and feature development.
The choice of an API Gateway depends on factors such as existing technology stack, budget, desired feature set, scale of operations, internal expertise, and the level of control versus managed services required. A thorough evaluation against specific architectural and business requirements is essential to select the most appropriate solution.
Conclusion
The evolution of software architecture, driven by the principles of microservices and cloud-native development, has irrevocably altered the way we design, build, and deploy applications. In this intricate and dynamic landscape, the API Gateway has emerged as an indispensable architectural component, serving as the intelligent nexus that orchestrates the flow of data, enforces security, and simplifies the complex interactions between clients and a distributed backend. Far from being a mere proxy, it stands as a sophisticated layer that addresses a myriad of challenges inherent in modern distributed systems.
Throughout this comprehensive guide, we have explored the foundational concepts that define an API Gateway, dissecting its critical role as the digital front door to your application ecosystem. We delved into the compelling reasons for its necessity, from abstracting backend complexity and reducing network chattiness to centralizing security, enhancing observability, and providing robust traffic management capabilities. Each core feature, whether it be intelligent routing, stringent authentication, judicious rate limiting, efficient caching, or resilient circuit breaking, contributes to the gateway's profound ability to transform a collection of disparate services into a cohesive, secure, and highly performant API product. We also examined various deployment patterns and acknowledged the challenges, such as the inherent risk of a single point of failure and the potential for increased latency or configuration complexity, alongside strategies to mitigate these concerns.
In essence, the API Gateway is more than just a piece of infrastructure; it is a strategic asset that empowers organizations to build more resilient, scalable, and manageable APIs. It liberates client developers from the burden of navigating complex backend architectures, safeguards valuable backend services from abuse and overloads, and provides architects with a centralized control point for enforcing governance and operational policies. As the digital transformation continues to accelerate, with increasing reliance on APIs for everything from mobile applications to AI-driven services and IoT devices, the role of the API Gateway will only continue to grow in prominence and sophistication. Understanding its main concepts is no longer optional; it is an essential competency for anyone navigating the complexities of modern software development. It stands as a testament to the continuous innovation required to harness the full potential of distributed systems, ensuring that our digital future is both accessible and secure.
Frequently Asked Questions (FAQs)
1. What is the fundamental difference between an API Gateway and a Load Balancer?
While both an API Gateway and a Load Balancer distribute traffic, their primary roles and functionalities differ significantly. A Load Balancer operates at lower network layers (L4 or L7) and is primarily concerned with distributing incoming network requests across multiple healthy server instances to optimize resource utilization, maximize throughput, and ensure high availability. Its main goal is efficient traffic distribution. An API Gateway, on the other hand, operates at the application layer (L7) and focuses on higher-level concerns related to API management. It acts as a single entry point for a collection of services, performing intelligent routing, authentication, authorization, rate limiting, request/response transformation, caching, and API versioning, in addition to basic load balancing. Essentially, a Load Balancer is about efficiently distributing network connections, while an API Gateway is about managing and securing the APIs themselves, providing a façade for complex microservices. Often, a Load Balancer will sit in front of an API Gateway cluster for high availability.
2. Can an API Gateway become a performance bottleneck?
Yes, an API Gateway can indeed become a performance bottleneck if not properly designed, configured, and scaled. As all incoming client requests pass through it, the gateway introduces an additional network hop and processing overhead for each request. The more complex the policies enforced (e.g., intricate request transformations, multiple authentication checks, extensive logging), the more CPU, memory, and network resources the gateway will consume, potentially adding latency. To mitigate this, it's crucial to optimize gateway configurations, provision adequate hardware or cloud resources, leverage caching aggressively for frequently accessed data, and choose a highly performant gateway solution. For very high-throughput or latency-sensitive scenarios, consider distributing gateway functionality (e.g., using micro-gateways or a service mesh for internal traffic) to avoid creating a new monolithic bottleneck.
3. What is the "monolithic gateway" anti-pattern?
The "monolithic gateway" anti-pattern occurs when an API Gateway becomes overly complex, accumulating too much business logic, extensive data aggregation, or intricate orchestration responsibilities that should ideally reside within dedicated backend services. While the API Gateway is designed to abstract backend complexity, pushing application-specific business logic into it can transform it into a new bottleneck or a "smart pipe, dumb endpoint" scenario. This reintroduces tight coupling, slows down deployments, and makes the gateway itself difficult to maintain and scale, essentially recreating a monolith at the edge of the system. To avoid this, the API Gateway should remain lean, focusing primarily on cross-cutting concerns (routing, security, rate limiting, basic transformations), while business logic and complex data composition are handled by specialized microservices or dedicated Backend-for-Frontend (BFF) layers.
4. How does an API Gateway help with API security?
An API Gateway significantly enhances API security by centralizing and enforcing critical security policies at a single entry point. It acts as the primary defense line, performing: 1. Authentication: Validating client identities using API keys, JWTs, or OAuth2 tokens before any request reaches backend services. 2. Authorization: Enforcing access control rules (e.g., RBAC) to ensure clients only access resources they are permitted to. 3. Rate Limiting and Throttling: Protecting backend services from abuse, brute-force attacks, and DoS attempts by restricting the number of requests a client can make. 4. Input Validation: Validating request payloads against schemas to prevent malformed requests and injection attacks. 5. Threat Protection: Incorporating Web Application Firewall (WAF) capabilities to detect and block common web vulnerabilities like SQL injection, XSS, and CSRF. 6. IP Filtering: Allowing or blocking requests from specific IP addresses. By centralizing these mechanisms, the API Gateway ensures consistent security policies across all APIs, reduces redundant security code in microservices, simplifies security auditing, and provides a robust barrier against external threats.
5. Is an API Gateway necessary for all microservices architectures?
While not strictly mandatory for every single microservices architecture, an API Gateway becomes increasingly necessary and beneficial as the number of microservices grows and the complexity of client interactions increases. For very small systems with only a handful of microservices and simple client requirements, direct client-to-service communication might initially suffice. However, as the system evolves, an API Gateway offers crucial advantages in managing complexity, enhancing security, improving performance, and enabling independent service evolution. Without it, developers risk scattering cross-cutting concerns (like authentication, rate limiting, logging) across all services and client applications, leading to duplicated effort, inconsistencies, security vulnerabilities, and a tightly coupled system. Therefore, while not strictly required from day one, an API Gateway quickly becomes an indispensable component for building robust, scalable, and maintainable microservices-based applications.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.



