Auth0 B2C Mappings: Streamline User Management
The digital landscape is constantly evolving, demanding sophisticated solutions for managing user identities. For businesses operating in the B2C (Business-to-Consumer) space, where millions of users interact with services daily, the challenges of identity and access management (IAM) are particularly acute. From ensuring seamless onboarding and personalized experiences to upholding stringent security and compliance standards, the stakes are incredibly high. Traditional, siloed approaches to user management often buckle under this pressure, leading to fragmented user data, increased security vulnerabilities, and a frustrating user journey that ultimately impacts customer loyalty and business growth. This is precisely where modern identity platforms like Auth0 step in, offering a comprehensive, developer-friendly solution designed to address these complex needs head-on.
Auth0, as a leading identity provider, offers a rich array of features that allow businesses to abstract away the intricate details of authentication and authorization. Its strength lies in its ability to centralize identity management, providing a single source of truth for user profiles across various applications and services. Within the B2C context, one of the most powerful, albeit often implicitly understood, aspects of leveraging Auth0 is its capacity for sophisticated "B2C Mappings." While not a single, explicitly named feature, B2C Mappings encapsulate the critical processes of configuring, transforming, and synchronizing user data and identity attributes as they flow through Auth0 and integrate with an organization's broader ecosystem. These mappings are the bedrock upon which streamlined user management, enhanced security postures, and truly exceptional user experiences are built.
This exhaustive guide delves deep into the world of Auth0 B2C Mappings, exploring how they empower businesses to conquer the complexities of consumer identity. We will dissect the architectural components of Auth0 that facilitate these mappings, from its versatile connections and powerful extensibility points like Rules and Hooks, to its robust API-first design. We'll examine practical implementation scenarios, discuss the paramount importance of security and compliance, and share best practices to navigate potential challenges. By mastering Auth0 B2C Mappings, organizations can move beyond merely authenticating users to truly understanding, serving, and protecting their consumer base, thereby unlocking unprecedented levels of operational efficiency and customer satisfaction. The journey ahead will illuminate how Auth0 not only manages identities but also transforms them into a strategic asset, driving value across the entire business lifecycle.
Understanding Auth0 and the Nuances of B2C Identity Management
Before diving into the specifics of mappings, it is crucial to establish a solid understanding of Auth0's fundamental architecture and the unique characteristics that define B2C identity management. Auth0 has positioned itself as an enterprise-grade identity platform that simplifies the complexities of authentication and authorization for developers. It serves as a universal identity layer, enabling applications to support a vast array of login methods – from social logins like Google and Facebook, to enterprise directories like Active Directory, to standard username/password databases – all through a single, consistent interface. This abstraction dramatically reduces the development effort required to implement secure and scalable identity solutions, allowing teams to concentrate on their core product offerings.
At its core, Auth0 provides a centralized identity service that manages user profiles, authentication flows, and authorization decisions. Its "API-first" approach means that virtually every aspect of the platform can be programmatically controlled and extended through a well-documented API. This architectural choice is fundamental to its flexibility and power, making it an ideal candidate for complex B2C scenarios where dynamic integration and customization are frequently required. Developers can use Auth0's various SDKs (Software Development Kits) to easily integrate identity functionality into their web, mobile, and even IoT applications, ensuring a consistent and secure experience across all channels. The platform also offers a "Universal Login" experience, a customizable, Auth0-hosted login page that automatically handles various authentication flows, branding, and language settings, further simplifying development and improving user experience.
The B2C identity landscape presents a distinct set of challenges that differentiate it significantly from B2B (Business-to-Business) or enterprise identity management. Firstly, scale is a dominant factor. B2C applications often cater to millions, if not tens of millions, of users. The identity solution must be capable of handling massive spikes in traffic during promotional events or product launches without degradation in performance. Secondly, diversity of identity sources is paramount. Consumers expect to log in using their preferred method, whether it's their existing social media accounts, email and password, or even device-specific biometric authentication. Supporting this variety seamlessly while maintaining data consistency is a significant undertaking.
Furthermore, security and compliance are non-negotiable. B2C platforms handle vast amounts of personal identifiable information (PII), making them prime targets for cyberattacks. Protecting user data, implementing robust multi-factor authentication (MFA), detecting anomalies, and adhering to global privacy regulations like GDPR and CCPA are critical. A single data breach can devastate a brand's reputation and lead to severe financial penalties. Lastly, personalization and user experience (UX) are key differentiators in the competitive B2C market. Users expect fast, intuitive, and tailored experiences. A clunky login process or inconsistent profile information across different touchpoints can quickly lead to user churn. Auth0's architecture, with its ability to consolidate and standardize user profiles from disparate sources, directly addresses these B2C challenges, laying the groundwork for effective B2C Mappings. Its extensible nature, built upon a robust API framework, allows businesses to adapt and evolve their identity strategy as their user base and regulatory requirements grow.
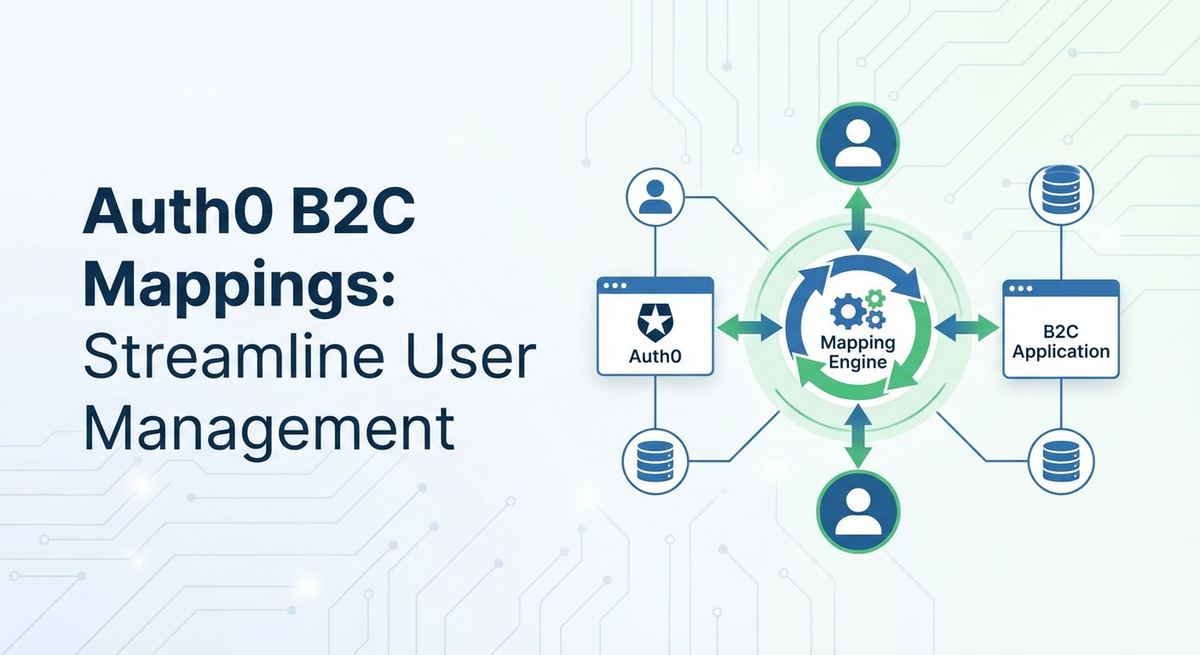
The Concept of B2C Mappings in Auth0: Forging a Unified User Identity
In the context of Auth0 B2C environments, "mappings" refers not to a singular feature but to the comprehensive and intricate process of configuring how user data, attributes, and identity flows are managed, transformed, and synchronized across various identity providers and downstream applications. It's about taking raw identity information from wherever a user authenticates and molding it into a standardized, usable, and consistent user profile within Auth0, which can then be securely transmitted and consumed by your applications. This process is absolutely fundamental to achieving a streamlined user experience, maintaining data integrity, and enforcing granular access controls in a B2C ecosystem.
At its core, Auth0 acts as a universal translator for identities. When a user authenticates through a social provider like Google, a custom database, or an enterprise connection, each provider typically sends back a unique set of user attributes. These attributes might be named differently (e.g., given_name vs. first_name), formatted inconsistently (e.g., full name vs. separate first/last fields), or contain varying levels of detail. The crucial role of B2C Mappings is to normalize this disparate information into a consistent Auth0 user profile. This involves several key aspects:
- User Profile Mappings: This is perhaps the most direct form of mapping. It involves defining how attributes received from various identity providers (e.g.,
email,name,picture,locale) are stored in the canonical Auth0 user profile. Auth0 intelligently handles many standard attributes automatically, but for non-standard attributes or specific data requirements, customization becomes essential. For instance, if a social provider returns apreferred_usernamethat you want to store asusernamein Auth0, or if you need to extract specific pieces of information from a complexaddressfield, this falls under user profile mapping. The goal is to ensure that regardless of how a user signs up, their core profile information is consistently structured and readily accessible within Auth0. - Attribute Transformation and Enrichment: Beyond simple storage, B2C mappings often involve modifying or enhancing user attributes. This might include concatenating first and last names, standardizing phone number formats, or deriving new attributes based on existing ones. For example, a rule might take a user's
emaildomain and use it to assign them to a specific customer segment or even enrich their profile with demographic data fetched from an external API based on their country. This dynamic transformation ensures that your applications receive precisely the data they need, in the format they expect, without requiring complex logic within each application itself. - Role and Permission Mappings: In many B2C applications, users might have different tiers of access (e.g., "basic," "premium," "VIP"). B2C mappings facilitate assigning these roles and permissions based on various criteria. This could be as simple as assigning a "subscriber" role upon successful registration, or as complex as dynamically assigning a "pro_user" role if the user's subscription status, fetched from an external billing system via an API, indicates an active premium plan. Auth0's Role-Based Access Control (RBAC) features rely heavily on these mappings to enforce granular authorization policies.
- External System Integration Mappings: A B2C user's journey rarely ends with authentication. Their data often needs to be synchronized with a multitude of downstream systems: CRM platforms (e.g., Salesforce), marketing automation tools (e.g., HubSpot), analytics platforms, data warehouses, and custom backend services. B2C mappings extend to defining how user lifecycle events (sign-up, login, profile update) trigger data transfers to these external systems, often through their respective APIs. This ensures data consistency across the entire business ecosystem, avoiding data silos and providing a holistic view of the customer.
- Custom Claims Mappings for Tokens: For sophisticated applications, the standard claims in ID tokens and access tokens might not be sufficient. B2C mappings allow developers to inject custom claims into these tokens. For instance, you might want to include a
loyalty_tier, apreferred_currency, or anaccount_IDdirectly in the JWT (JSON Web Token) issued by Auth0. This simplifies authorization logic within your microservices, as they can directly consume these claims from the token without needing to make additional API calls to retrieve user information, enhancing performance and reducing latency.
The importance of these mappings for B2C operations cannot be overstated. Firstly, they ensure data consistency and integrity. By normalizing user profiles, businesses avoid the pitfalls of fragmented data, which can lead to poor user experiences and erroneous business decisions. Secondly, they facilitate personalization at scale. With standardized and enriched user profiles, applications can deliver tailored content, recommendations, and services, driving engagement and customer satisfaction. Thirdly, effective mappings are critical for security and compliance. By controlling exactly what data is stored and how it flows, organizations can better meet privacy regulations (like GDPR's "right to be forgotten" by centralizing data management) and enforce consistent security policies. Lastly, they significantly improve developer velocity. By centralizing mapping logic within Auth0, application developers are freed from implementing complex identity-specific code, allowing them to focus on core product features. The robust API framework of Auth0 underpins all these capabilities, providing the programmatic control necessary for intricate and dynamic B2C mapping strategies.
Key Components of Auth0 for Streamlined B2C Mappings
Auth0 provides a rich ecosystem of features and extensibility points that are instrumental in implementing comprehensive B2C mappings. Understanding how each component contributes to the overall strategy is crucial for designing a robust and scalable identity solution. These components work in concert to capture, transform, and deliver user identity information securely and efficiently.
1. Connections: The Gateway to Identity Sources
Connections are the heart of Auth0's ability to integrate with various identity providers. They define how users can authenticate into your applications. For B2C environments, Auth0 offers several critical connection types, each with its own mapping characteristics:
- Social Connections: These allow users to sign up and log in using existing accounts from popular social identity providers like Google, Facebook, Apple, Twitter, and many others. Auth0 handles the OAuth 2.0 or OpenID Connect (OIDC) dance with these providers and retrieves a set of standardized user attributes (e.g.,
name,email,picture). While Auth0 automatically maps many common attributes to its canonical user profile, developers can also request additional scopes from social providers to retrieve more specific data (e.g.,user_birthday,user_location) which can then be further mapped or transformed using Auth0 Rules. This automatic normalization is a major streamlining factor, reducing the burden on developers to handle diverse social API responses. - Database Connections: For users who prefer a traditional email/password login, or for businesses that require specific onboarding flows, database connections are essential. Auth0 can either manage the user database itself, offering features like password hashing, MFA, and breach detection, or it can connect to an external custom database. When using a custom database, developers provide JavaScript snippets (called "Custom Database Actions") for common operations like
create,login, andverify. These snippets become critical mapping points, as they define how user attributes from your external database are translated into the Auth0 user profile, and vice-versa. This is a powerful API integration point, allowing businesses to leverage existing user stores while gaining Auth0's security and management features. - Enterprise Connections (SAML, OIDC, WS-Fed): While typically associated with B2B scenarios, enterprise connections can sometimes be relevant in B2C if you have specific partner or affiliate programs, or if you acquire another company and need to onboard their existing user base using their corporate identity provider. Here, attribute assertions from the enterprise IdP are mapped to Auth0 user profile fields. Auth0 provides configurable mappings to handle variations in attribute names (e.g.,
urn:oid:2.5.4.42vs.firstName). This ensures that even enterprise-sourced identities can be seamlessly integrated into your B2C user experience.
2. Auth0 Rules and Hooks: The Extensibility Powerhouses
Auth0's true power in B2C mappings comes from its extensibility features: Rules and Hooks. These are JavaScript functions that allow developers to execute custom logic at various stages of the authentication and user lifecycle. They provide the flexibility to transform, enrich, and synchronize user data dynamically.
- Auth0 Rules: Rules are JavaScript functions that execute immediately after a user successfully authenticates, but before the token is issued to the application. They run synchronously within the authentication pipeline, making them ideal for:
- Attribute Transformation: Normalizing data (e.g.,
user.name.toUpperCase()), parsing complex strings, or deriving new attributes from existing ones. - User Profile Enrichment: Calling an external API to fetch additional user data (e.g., loyalty status from a CRM, geographic data from an IP lookup service) and storing it in
user_metadataorapp_metadata. This is a prime example of leveraging an API to enhance user profiles in real-time. - Role Assignment: Dynamically assigning roles or permissions based on user attributes (e.g., email domain, country of origin, subscription level fetched via an API).
- Conditional Logic: Implementing conditional MFA, blocking suspicious users based on IP address or detected anomalies, or redirecting users to complete progressive profiling steps.
- Custom Claims: Adding application-specific claims to the ID Token or Access Token, ensuring downstream services receive all necessary authorization context without extra API calls. Rules are incredibly powerful but must be designed carefully to avoid introducing latency into the login process.
- Attribute Transformation: Normalizing data (e.g.,
- Auth0 Hooks: Hooks are serverless functions that allow you to customize Auth0's behavior at specific points in the user lifecycle beyond just authentication. They offer greater flexibility and can handle asynchronous operations, making them suitable for:
- Pre User Registration: Validating user input before a new user account is created, or enriching the initial profile with default values.
- Post User Registration: Triggering external actions after a new user registers, such as sending a welcome email, creating a record in a CRM system (via its API), or provisioning an account in a downstream application.
- Client Credential Exchange: Customizing the claims in Access Tokens issued via the Client Credentials Grant.
- Post Change Password: Notifying external systems (e.g., a security log or a different user store) that a user's password has been changed. Hooks are particularly valuable for integrating Auth0 with external systems where real-time, asynchronous data synchronization is required, often involving calls to external APIs. They decouple the identity flow from external system updates, improving resilience.
3. User Metadata: Flexible Storage for Custom Attributes
Auth0 provides two distinct types of metadata for storing custom user attributes:
user_metadata: This is mutable data that can be updated by the user through their profile page (if you expose it) or by application logic. It's ideal for storing information likepreferred_language,marketing_opt_ins,shipping_address, or any other user-specific preferences.app_metadata: This is immutable data from the user's perspective, typically updated by administrators or through server-side logic (e.g., Auth0 Rules, Hooks, or the Management API). It's perfect for storing application-specific attributes that define a user's role, permissions, subscription tier, or any other data that should not be directly modifiable by the user. Effectively utilizinguser_metadataandapp_metadatais a cornerstone of B2C mappings, allowing for the flexible storage and retrieval of custom attributes that go beyond the standard profile fields, driving personalization and authorization.
4. APIs and SDKs: The Programmable Core
Auth0's entire platform is built on an API-first principle, providing programmatic access to almost every feature. This is critical for advanced B2C mappings and integrations:
- Management API: This API allows you to programmatically manage users, roles, applications, connections, rules, and hooks. It's used by administrators or automated scripts to create users, update profiles, assign roles, and configure identity providers. For instance, an admin dashboard might use the Management API to update
app_metadatafor a user based on a support request. - Authentication API: This API is used by your applications to initiate authentication flows, retrieve user profiles, and obtain tokens. While SDKs abstract most of this away, understanding the underlying API calls is crucial for debugging and highly custom implementations.
- SDKs: Auth0 provides comprehensive SDKs for various programming languages and platforms, simplifying integration with its APIs. These SDKs handle token management, refresh flows, and secure storage, abstracting away much of the complexity of interacting directly with the Auth0 API. The API-first nature of Auth0, with its comprehensive documentation often resembling an OpenAPI specification, empowers developers to build highly customized and automated identity workflows, which are essential for sophisticated B2C mapping strategies.
5. Tenant Settings: Global Controls and Branding
Tenant settings encompass global configurations for your Auth0 tenant, including:
- Universal Login Customization: Branding, language settings, and social connection order on the login page.
- MFA Policies: Defining when and how multi-factor authentication is enforced.
- Token Settings: Configuring JWT expiration times, signing algorithms, and audience/issuer values.
- Email Templates: Customizing emails for password resets, verification, etc. These settings influence the overall user experience and security posture, implicitly playing a role in how user identity is perceived and managed across the board.
By intelligently combining these components—leveraging flexible connections, powerful Rules and Hooks, granular metadata storage, and robust APIs—businesses can construct incredibly sophisticated B2C mapping strategies that streamline user management, enhance security, and deliver truly personalized experiences. The ability to connect various identity sources and then transform and enrich that data dynamically within the Auth0 pipeline is what truly sets it apart for complex consumer identity requirements.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
Implementing Advanced B2C Mappings with Auth0
Moving beyond the foundational elements, let's explore practical scenarios where Auth0's B2C mapping capabilities truly shine, demonstrating how a well-architected identity solution can drive significant business value. These scenarios highlight the flexibility and power of Auth0's extensibility model.
Scenario 1: Progressive Profiling for Enhanced User Data Collection
In the B2C world, a lengthy sign-up form is a major deterrent. Progressive profiling is a strategy to collect minimal information during initial registration and then gradually gather more data from users over time, only when it's contextually relevant or necessary. Auth0 B2C mappings are perfectly suited for this.
Implementation: When a new user signs up (e.g., via social login), you might initially only collect their email and name. An Auth0 Rule can then check for the presence of certain user_metadata fields (e.g., phone_number, date_of_birth). If these fields are missing, the Rule can redirect the user to a specific application page where they are prompted to provide this additional information. Once submitted, your application calls the Auth0 Management API (using an appropriate access token) to update the user's user_metadata with the newly provided data. Subsequent logins would then see these fields present, and the progressive profiling step would be skipped. This ensures a frictionless initial onboarding while still allowing for rich user profiles over time, which can then be used for targeted marketing or personalized services.
Scenario 2: Granular Access Control and Role-Based Permissions
Many B2C applications have different tiers of users (e.g., free, premium, enterprise) or require specific permissions based on user attributes. Auth0's RBAC (Role-Based Access Control) features, combined with Rules and app_metadata, enable sophisticated access control mappings.
Implementation: Upon user registration or login, an Auth0 Rule can inspect user attributes or make an API call to an external billing system to determine the user's subscription tier. Based on this, the Rule would assign a corresponding role (e.g., "basic_subscriber", "premium_member") to the user and store it in their app_metadata or assign it using Auth0's built-in RBAC APIs. This role can then be added as a custom claim to the Access Token. Downstream microservices, protected by an API Gateway, can then validate this Access Token and its claims. For example, a "premium_member" claim in the token would grant access to premium content APIs, while a "basic_subscriber" would be restricted. This approach centralizes authorization logic within Auth0, simplifying application-level authorization checks.
Scenario 3: Integrating with CRMs and Marketing Automation Platforms
Maintaining consistent customer data across identity and marketing platforms is crucial for personalized communication and effective customer relationship management. B2C mappings facilitate this real-time data flow.
Implementation: An Auth0 Hook (specifically, a Post User Registration or Post User Login Hook) can be configured to fire whenever a new user signs up or an existing user logs in. Within this Hook, you can make an API call to your CRM (e.g., Salesforce, HubSpot) or marketing automation platform. The Hook would send relevant user data (email, name, sign-up date, user_metadata) to create a new contact or update an existing one. For example, a Post User Registration Hook could create a new contact in HubSpot, including their user_metadata.preferred_language. A Post User Login Hook could update their "last_login" timestamp in the CRM, helping marketing teams track engagement. This ensures that your marketing efforts are always based on the most up-to-date and comprehensive user data.
Scenario 4: Multi-Tenancy for B2C Solutions
For businesses that offer white-labeled products, manage multiple brands, or support distinct customer segments, multi-tenancy is often a requirement. Auth0 can facilitate this through clever mappings and configuration.
Implementation: While Auth0 supports separate tenants for complete isolation, within a single tenant, you can use app_metadata and Rules to segregate users. Each "tenant" (e.g., a brand or a client application) could be identified by a unique tenant_id stored in the user's app_metadata. When a user logs in, a Rule can check their tenant_id and ensure they are accessing the correct application or domain. Custom database connections can also be configured to point to different user stores based on the incoming client application. Furthermore, the Auth0 Management API can be used to programmatically manage users and their app_metadata.tenant_id, ensuring that administrative operations are scope-bound to specific tenant contexts. This allows for a consolidated identity management platform while maintaining logical separation for different B2C offerings.
The Role of an API Gateway in this Ecosystem
In a complex microservices architecture, protecting downstream APIs becomes paramount. An API gateway acts as the primary enforcement point, sitting in front of your backend services, validating tokens issued by Auth0 before forwarding requests to the respective services. This is where platforms like APIPark, a robust open-source AI gateway and API management platform, come into play. APIPark can efficiently manage, secure, and monitor all API traffic, including requests authenticated by Auth0, ensuring consistent security policies and high performance across the entire digital landscape.
An API gateway like APIPark can perform several critical functions in conjunction with Auth0: * Token Validation: It validates the JWTs (Access Tokens) issued by Auth0 for every incoming request, ensuring that only authenticated and authorized users can access your services. This offloads authentication and basic authorization from individual microservices. * Rate Limiting and Throttling: It protects your backend APIs from abuse and ensures fair usage by limiting the number of requests a user or application can make within a given timeframe. * Request/Response Transformation: It can modify request headers, body, or response payloads, decoupling your backend services from external client requirements. * Routing and Load Balancing: It intelligently routes requests to the correct backend service instance and distributes traffic to prevent overload. * Centralized Logging and Monitoring: It provides a single point for logging all API traffic, offering insights into performance, errors, and security events. This is also one of APIPark's strong suits, with its detailed API call logging and powerful data analysis features, allowing businesses to trace and troubleshoot issues quickly and predict performance changes.
By deploying an API gateway like APIPark, developers can secure their backend APIs, enforce policies, and manage traffic effectively, complementing Auth0's identity management capabilities. The gateway acts as a crucial layer of defense and control, ensuring that only authenticated users with valid permissions (as defined by Auth0 mappings) can access your sensitive data and functionality. This creates a powerful, end-to-end secure ecosystem.
Here is a table summarizing common B2C mapping use cases and the Auth0 features that facilitate them:
| Use Case | Auth0 Feature(s) | Description |
|---|---|---|
| Standardize Social Login Data | Connections, Rules | Normalize given_name, family_name, picture from various social providers into a consistent format within the Auth0 user profile. Rules can handle more complex transformations or add default values if data is missing. |
| Enrich User Profile | Rules, Hooks, Management API | Fetch additional user data from an external system (e.g., CRM, data enrichment API) based on existing user attributes (like email), and store it in user_metadata or app_metadata for later use. This can happen during login (Rules) or as part of a post-registration process (Hooks). |
| Assign Roles Based on Attributes | Rules, app_metadata, Auth0 RBAC API |
Automatically assign specific roles or permission tiers (e.g., "premium_member", "admin") based on a user's email domain, subscription status (fetched via external API), or other profile attributes. These roles can then be added as custom claims to the Access Token. |
| Sync User Data to External CRM/MAP | Hooks (Post User Registration, Post User Login) | Trigger an event to push new user sign-ups, profile updates, or login events to a CRM system (e.g., Salesforce, HubSpot) or marketing automation platform via their respective REST APIs. Ensures data consistency across all customer-facing systems. |
| Inject Custom ID/Access Token Claims | Rules | Add application-specific claims (e.g., loyalty_tier, account_id, custom_feature_flags) to the ID Token or Access Token. This allows downstream applications and microservices to make authorization decisions without needing to make additional API calls for user context. |
| Progressive Profiling | Rules, user_metadata, Management API, Application Logic |
Prompt users for additional, non-essential information (e.g., phone number, shipping address) at a later, more convenient stage after initial sign-up. Rules can detect missing data and trigger redirections, while the application uses the Management API to update user_metadata. |
| Conditional Multi-Factor Authentication | Rules | Enforce MFA only for users logging in from untrusted geolocations, suspicious IP addresses, or when accessing highly sensitive applications. Rules can evaluate context and trigger MFA prompts dynamically. |
| User Onboarding Workflow Automation | Hooks (Pre User Registration, Post User Registration) | Implement custom logic during user registration, such as verifying eligibility, sending welcome emails via an external API, or provisioning user accounts in multiple downstream applications. |
| Tenant Segregation in Multi-Tenant Apps | app_metadata, Rules, Custom Connections |
Assign a tenant_id to each user in app_metadata and use Rules to ensure users only access resources associated with their assigned tenant. Custom connections can also route users to different authentication backends based on the application they are trying to access. |
| API Protection and Policy Enforcement | API Gateway (e.g., APIPark) | Validate Auth0-issued Access Tokens, enforce rate limits, apply security policies, and route requests to appropriate backend services. Provides a centralized control point for API security and management. |
These examples illustrate the depth and breadth of Auth0's capabilities when it comes to sophisticated B2C identity mappings. By thoughtfully designing and implementing these mappings, organizations can significantly streamline user management, enhance the security posture of their applications, and ultimately deliver a superior user experience that fosters loyalty and engagement. The synergy between Auth0's identity features and an robust API gateway like APIPark provides a complete solution for managing both user identities and the APIs they interact with, creating a resilient and high-performing digital ecosystem.
Security, Compliance, and User Experience Through Effective Mappings
The meticulous implementation of Auth0 B2C mappings extends far beyond mere data transformation; it forms the bedrock for robust security, stringent compliance, and an unparalleled user experience. These three pillars are inextricably linked, and effective identity mappings are the common thread that weaves them into a cohesive and resilient digital strategy.
Enhanced Security: A Fortified Identity Perimeter
Centralizing user identity within Auth0, underpinned by precise mappings, fundamentally enhances security. When user data is fragmented across multiple disparate systems, each with its own security vulnerabilities and management overhead, the attack surface expands exponentially. Auth0 acts as a single, hardened identity perimeter, making it significantly easier to implement and enforce consistent security policies.
- Centralized Authentication and Authorization: By routing all authentication requests through Auth0, businesses gain a central point of control. Mappings ensure that critical security attributes, such as
user_rolesorsecurity_clearance, are consistently applied to user profiles. This enables fine-grained authorization policies that can be enforced either within Auth0 (via custom claims in tokens) or by downstream API gateways like APIPark validating these claims. This prevents unauthorized access to sensitive data and functionalities. - Multi-Factor Authentication (MFA): Auth0 offers robust MFA capabilities, and mappings can determine when MFA is enforced. For example, a Rule can check if a user is logging in from an unfamiliar IP address or device, or if they are attempting to access a highly sensitive application (as indicated by
app_metadata), and then conditionally trigger an MFA prompt. This adaptive security layer significantly reduces the risk of credential compromise. - Anomaly Detection and Breach Protection: Auth0 incorporates advanced features for detecting suspicious login attempts, brute-force attacks, and credential stuffing. By centralizing identity, these protections are applied universally across all connected applications. Mappings ensure that user profiles are complete enough to enable features like compromised password detection, where Auth0 can cross-reference user credentials against known breaches and prompt users for a password reset, preventing potential account takeovers.
- Reduced Data Redundancy and Consistency: Effective mappings eliminate redundant copies of user data stored in various formats across different systems. This reduces the number of places where sensitive PII resides, minimizing the potential impact of a data breach. Consistent data also ensures that security policies are applied uniformly, without gaps arising from disparate attribute definitions.
Compliance: Navigating the Regulatory Labyrinth
In an era of increasing data privacy regulations, compliance is a non-negotiable aspect of B2C operations. Auth0 B2C mappings play a crucial role in helping organizations meet their obligations under regulations such as GDPR (General Data Protection Regulation), CCPA (California Consumer Privacy Act), and others.
- Centralized Data Residency and Consent Management: Mappings can be used to capture and manage user consent preferences (e.g., for marketing communications, data sharing with third parties) and store them in
user_metadata. This centralized repository makes it easier to track and enforce user choices. For data residency, while Auth0 operates globally, its architecture allows for tenant segregation that can help in designing solutions where certain PII remains within specific geographical boundaries, though the primary responsibility lies with the overall architecture. - Right to Be Forgotten (Erasure): When a user requests to have their data deleted, Auth0 provides APIs to delete a user and all associated data within the tenant. Effective mappings ensure that all relevant user data is stored within Auth0 or is systematically linked to external systems via APIs. This allows for a more comprehensive and verifiable deletion process across the entire ecosystem, as Auth0 can trigger downstream deletions or notifications to integrated systems via Hooks.
- Data Portability (Access): Regulations often grant users the right to request a copy of their personal data. With a centralized Auth0 user profile, rich with data aggregated through various mappings, fulfilling these requests becomes significantly simpler and more efficient. The Auth0 Management API can be used to export a user's entire profile programmatically.
- Auditability and Logging: Auth0 maintains detailed audit logs of all authentication and authorization events, including changes to user profiles. These logs are invaluable for demonstrating compliance during audits, investigating security incidents, and troubleshooting issues. Mappings ensure that the data within these logs is consistent and meaningful, providing a clear narrative of user activity.
Improved User Experience: Seamless and Personalized Journeys
A well-executed B2C mapping strategy directly translates into a superior user experience, fostering greater engagement and loyalty.
- Single Sign-On (SSO) and Reduced Friction: By consolidating multiple applications under a single Auth0 tenant, users can achieve SSO, logging in once and gaining access to all connected services without re-authenticating. This drastically reduces friction and enhances convenience, a critical factor for B2C retention. Mappings ensure that the user's identity is consistently recognized across these various applications.
- Personalized Experiences at Scale: With a rich, consistent, and up-to-date user profile (thanks to sophisticated mappings that include
user_metadataandapp_metadata), applications can deliver highly personalized experiences. This could range from localized content and currency preferences to tailored product recommendations and proactive customer support, significantly enhancing user satisfaction and driving conversions. - Streamlined Onboarding: Progressive profiling, enabled by clever mappings, allows users to quickly sign up with minimal information. Additional data can be collected later, reducing initial abandonment rates and improving the overall onboarding journey. This "less is more" approach at the start makes users feel valued rather than burdened.
- Consistent Identity Across Channels: Whether a user interacts with your brand via a web application, mobile app, or even an IoT device, effective mappings ensure that their identity and associated attributes remain consistent. This eliminates confusion and creates a cohesive brand experience, reinforcing trust and familiarity.
- Self-Service Capabilities: Auth0 empowers users with self-service features like password resets, profile updates, and MFA management. The clarity and consistency provided by well-defined mappings mean users can manage their identity effectively without constant intervention from support, further improving their autonomy and overall experience.
In essence, investing time and effort into defining robust Auth0 B2C mappings is not merely a technical exercise; it's a strategic imperative. It creates a powerful synergy between security, compliance, and user experience, transforming identity management from a necessary overhead into a competitive advantage. The secure and efficient flow of user data, orchestrated by Auth0's flexible architecture and augmented by the robust API management capabilities of platforms like APIPark, ultimately leads to stronger customer relationships, reduced operational risks, and accelerated business growth.
Challenges and Best Practices in Auth0 B2C Mappings
While Auth0 provides powerful tools for B2C mappings, navigating their implementation effectively requires careful planning and adherence to best practices. Without a thoughtful approach, organizations can encounter challenges that undermine the very benefits they seek to achieve. Understanding these potential pitfalls and adopting proactive strategies is key to success.
Common Challenges in B2C Mappings
- Over-Complicating Rules and Hooks: It's tempting to use Rules and Hooks for every possible logic permutation. However, cramming too much complex business logic, especially external API calls, into Rules can introduce significant latency into the authentication flow. Rules are synchronous; slow external calls directly impact login times. Similarly, overly complex Hooks can be difficult to debug and maintain.
- Managing Attribute Conflicts and Inconsistencies: When integrating multiple identity providers (social, custom database, enterprise), attribute names and formats can clash. Without clear mapping strategies, this leads to inconsistent user profiles, which can break downstream applications or lead to incorrect authorization decisions. For example,
namefrom Google might beJohn Doe, whilenamefrom a custom database isDoe, John. - Performance Implications of External API Calls: Relying heavily on external API calls within Rules or Hooks for data enrichment or synchronization can introduce performance bottlenecks and external dependencies. If an external service is slow or unavailable, it can directly impact the user login experience or prevent user registration.
- Testing Complex Mapping Logic: Debugging and testing intricate Rule and Hook logic, especially when it involves multiple external API calls or conditional branches, can be challenging. Simulating all possible scenarios and ensuring idempotency for external integrations requires a robust testing strategy.
- Securing API Keys and Secrets: Rules and Hooks often need to call external APIs, requiring API keys or secrets. Storing and managing these credentials securely within Auth0 and ensuring they are not accidentally exposed in client-side code is critical.
- Versioning and Deployment: Managing changes to Rules and Hooks across different environments (development, staging, production) can be cumbersome without proper version control and deployment pipelines. Accidental changes to production rules can have immediate and widespread impact.
- Data Synchronization with External Systems: Ensuring that user data remains consistent between Auth0 and all integrated downstream systems (CRMs, marketing platforms, custom backends) can be complex. Bidirectional sync, conflict resolution, and handling data schema evolution require careful design.
Best Practices for Effective B2C Mappings
- Start Simple and Iterate: Begin with the most essential mappings. Avoid over-engineering from the outset. Implement basic attribute normalization and then gradually add more complex logic, like progressive profiling or advanced role assignments, as your requirements evolve. This iterative approach makes testing and debugging more manageable.
- Document Everything (especially APIs): Comprehensive documentation of your Auth0 configuration, including all Rules, Hooks, connection settings, and custom attribute mappings, is vital. For any custom APIs that you create or integrate with, consider using OpenAPI specifications to describe their functionality, expected inputs, and outputs. This provides a clear contract for developers and facilitates future maintenance. Auth0's own Management API is well-documented, setting a good example for how to approach your custom integrations.
- Prioritize Performance:
- Keep Rules Lean: If an external API call is not absolutely critical for the immediate authentication decision, consider moving it to an asynchronous Hook (
Post User RegistrationorPost User Login) or triggering it from your application post-authentication. - Cache External Data: If external data is static or changes infrequently, consider caching it within your application or a dedicated service rather than fetching it in every Rule execution.
- Optimize External API Calls: Ensure any external APIs called by Rules or Hooks are highly performant and reliable. Implement proper error handling, timeouts, and retries.
- Keep Rules Lean: If an external API call is not absolutely critical for the immediate authentication decision, consider moving it to an asynchronous Hook (
- Test Thoroughly and Continuously:
- Unit Tests for Rules/Hooks: Write unit tests for your JavaScript Rules and Hooks to verify their logic.
- Integration Tests: Test the entire authentication flow, including all mappings and integrations with downstream systems. Use dedicated testing environments.
- Scenario-Based Testing: Test various user types (new user, existing user, social login, database login), edge cases (missing attributes), and error conditions.
- Idempotency: Ensure that external API calls made by Hooks are idempotent, meaning repeated calls produce the same result and do not create duplicate records or unintended side effects.
- Secure API Keys and Secrets:
- Auth0 Dashboard Secrets: Store sensitive
APIkeys and secrets as environment variables within the Auth0 dashboard for Rules and Hooks. Never hardcode them. - Least Privilege: Grant API access tokens the minimum necessary permissions for their intended function.
- Rotate Credentials: Regularly rotate API keys and secrets to mitigate the risk of compromise.
- Auth0 Dashboard Secrets: Store sensitive
- Leverage Auth0's Built-in Features Before Custom Code: Auth0 offers a wide array of features out-of-the-box (e.g., standard social connections, database connections, RBAC). Always explore if a built-in feature can achieve your mapping goal before resorting to custom Rule or Hook code, as built-in features are typically more performant, secure, and easier to maintain.
- Implement Robust Error Handling and Logging:
- Graceful Degradation: Design Rules and Hooks to fail gracefully if an external dependency is unavailable. Consider fallback logic or default values.
- Comprehensive Logging: Utilize Auth0's extensibility features to log relevant information from Rules and Hooks, making it easier to troubleshoot issues. Integrate Auth0 logs with your central logging and monitoring system.
- Use Version Control for Rules and Hooks: Treat Rules and Hooks like any other piece of application code. Store them in a version control system (e.g., Git) and integrate them into your CI/CD (Continuous Integration/Continuous Deployment) pipeline for automated deployment and rollback capabilities. Auth0's Deploy CLI tool can facilitate this.
- Consider an API Gateway: For protecting your backend services that consume Auth0-issued tokens, implement an API gateway like APIPark. This centralizes security policies, rate limiting, and traffic management, complementing Auth0's identity features and providing robust protection for your APIs. APIPark's comprehensive logging and data analysis also aid in identifying issues related to API interactions.
By proactively addressing these challenges and adhering to these best practices, organizations can fully harness the power of Auth0 B2C mappings. This strategic approach ensures that identity management becomes a seamless, secure, and scalable component of their overall digital ecosystem, driving innovation and delivering exceptional value to their consumer base. The synergy between a well-configured Auth0 environment and a powerful API gateway solidifies the foundation for future growth and resilience.
Conclusion: Orchestrating Identity for the Modern Consumer Landscape
The intricate dance of managing consumer identities in today's digital world demands more than just basic authentication. It requires a sophisticated, adaptable, and secure approach that prioritizes both operational efficiency and an exceptional user experience. As we have thoroughly explored, Auth0 B2C Mappings, while not a single explicit feature, represent the strategic orchestration of Auth0's powerful capabilities to achieve precisely this. They are the invisible threads that weave together disparate identity sources, transform raw data into meaningful insights, and synchronize user profiles across a vast ecosystem of applications and services.
Through Auth0's versatile Connections, which seamlessly integrate social logins, custom databases, and enterprise directories, businesses can cast a wide net for user acquisition. The true magic unfolds with Auth0 Rules and Hooks, which act as the intelligent control points, allowing for dynamic attribute transformation, real-time profile enrichment, and conditional policy enforcement. These extensibility features, built upon an API-first architecture, empower developers to tailor every aspect of the identity journey, from progressive profiling to granular access control, ensuring that user data is always consistent, relevant, and secure. The careful utilization of user_metadata and app_metadata provides the necessary flexibility to store and manage a wealth of custom attributes, further personalizing the user experience at scale.
The benefits of mastering Auth0 B2C Mappings are profound and far-reaching. From a security perspective, centralizing identity and enforcing consistent policies, combined with advanced features like MFA and anomaly detection, significantly fortifies the digital perimeter against ever-evolving threats. For compliance, streamlined mappings provide the clarity and control necessary to navigate complex data privacy regulations, facilitating aspects like consent management, data portability, and the right to be forgotten. Critically, these efforts coalesce to deliver an unparalleled user experience: frictionless onboarding, seamless Single Sign-On, and deeply personalized interactions that foster loyalty and engagement, ultimately driving business growth.
However, realizing these benefits is not without its challenges. Over-complicating logic, neglecting performance, and inadequate testing can undermine even the most well-intentioned mapping strategies. Therefore, adhering to best practices—starting simple, documenting thoroughly, prioritizing performance, rigorous testing, and securing credentials—is paramount. The journey towards streamlined user management is a continuous one, demanding vigilance and adaptability.
In this complex landscape, where every interaction can be an API call, the role of robust API gateway solutions becomes undeniably crucial. By deploying a platform like APIPark, an open-source AI gateway and API management platform, organizations can extend the security and management paradigm beyond identity to encompass all their backend APIs. APIPark's capabilities in token validation, rate limiting, and centralized monitoring perfectly complement Auth0's identity services, creating a holistic and formidable defense layer for the entire digital infrastructure. It's the powerful synergy between a state-of-the-art identity provider and a high-performance API gateway that truly empowers businesses to manage, secure, and optimize their entire digital ecosystem.
Auth0 B2C Mappings represent more than just technical configurations; they embody a strategic approach to identity that empowers businesses to thrive in the competitive B2C market. By embracing these principles, organizations can transform identity from a complex challenge into a core strategic asset, allowing them to focus on innovation while providing their consumers with a secure, seamless, and personalized digital journey.
Frequently Asked Questions (FAQs)
1. What exactly are "Auth0 B2C Mappings" and why are they important? "Auth0 B2C Mappings" refers to the comprehensive process of configuring, transforming, and synchronizing user data and identity attributes as they flow through Auth0 and integrate with various applications and external systems in a Business-to-Consumer (B2C) context. It's not a single Auth0 feature but an umbrella term for how you manage user profiles, attributes, roles, and data synchronization. They are crucial because they ensure data consistency, enable personalized user experiences, enforce security policies, and help meet compliance requirements across diverse identity sources and downstream applications, ultimately streamlining user management at scale.
2. How do Auth0 Rules and Hooks contribute to B2C Mappings? Auth0 Rules and Hooks are powerful extensibility points that allow developers to execute custom JavaScript logic at specific stages of the authentication and user lifecycle. Rules run synchronously post-authentication, ideal for attribute transformation, role assignment, and adding custom claims to tokens. Hooks, on the other hand, are serverless functions that can be triggered at various lifecycle events (e.g., post-registration) and are excellent for asynchronous tasks like synchronizing user data with external CRM or marketing platforms via their APIs. Both are fundamental for dynamic and custom mapping strategies, allowing businesses to adapt Auth0's behavior to their unique B2C needs.
3. Can Auth0 B2C Mappings help with compliance regulations like GDPR and CCPA? Absolutely. Effective Auth0 B2C Mappings are instrumental in achieving compliance. By centralizing user data and consent preferences (e.g., in user_metadata), you gain better control over personal identifiable information (PII). Mappings facilitate responding to "right to be forgotten" requests by providing a single source of truth for user data that can then trigger downstream deletion events via APIs or Hooks. They also simplify data portability requests by ensuring user profiles are consistent and accessible. Auth0's comprehensive audit logs further assist in demonstrating compliance during regulatory reviews.
4. How does an API gateway like APIPark fit into an Auth0 B2C environment? An API gateway like APIPark serves as a critical layer for protecting your backend APIs that interact with authenticated users. After Auth0 authenticates a user and issues an Access Token, the API gateway sits in front of your microservices. It validates these Auth0-issued tokens, enforces security policies (like rate limiting), and routes requests to the correct services. APIPark, as a robust API management platform, can secure, manage, and monitor all your API traffic, ensuring that only authenticated and authorized requests (based on Auth0's identity decisions) reach your sensitive backend resources, thereby enhancing the overall security and performance of your B2C application ecosystem.
5. What are some best practices for managing multiple identity sources (e.g., social, email/password) within Auth0 B2C Mappings? When managing multiple identity sources, several best practices are key: * Normalize Attributes: Use Auth0 Rules to standardize attribute names and formats from different sources into a consistent user profile (e.g., ensuring first_name is always given_name). * Link Accounts: Implement account linking to allow users to associate multiple identity providers (e.g., Google and email/password) with a single Auth0 user profile, providing a seamless experience and preventing duplicate accounts. * Progressive Profiling: Start with minimal information at sign-up via any source and progressively collect more data over time, using Auth0 Rules to detect missing information and prompt users. * Clear Connection Strategy: Clearly define which connection types are available for which applications and ensure a consistent user experience across them, possibly using Universal Login branding. * Robust Error Handling: Implement error handling in Rules and Hooks that gracefully manages failures when dealing with diverse input data from various sources.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.