IP Allowlisting vs. Whitelisting: What's the Difference?

In the increasingly complex and interconnected digital landscape, safeguarding sensitive data and critical infrastructure has never been more paramount. As organizations migrate their operations to the cloud, embrace microservices architectures, and expose their functionalities through Application Programming Interfaces (APIs), the perimeter of what needs protection expands dramatically. Network security, once a relatively straightforward endeavor focused on physical boundaries, has evolved into a sophisticated discipline centered on access control at various layers. At the heart of many fundamental security strategies lies the principle of restricting access to only known and trusted entities. This article delves into two terms frequently encountered in this context: "IP Whitelisting" and "IP Allowlisting." While seemingly interchangeable at first glance, a deeper examination reveals important distinctions, particularly in contemporary security discourse and best practices. Understanding these nuances is crucial for implementing robust security policies, designing secure network architectures, and effectively managing access to vital resources, including the critical pathways managed by an API gateway.
For decades, the term "whitelisting" has been ubiquitous in cybersecurity. It described a security model where a system or network resource would only permit access from a pre-approved list of entities, explicitly denying all others. This "default deny, explicit permit" philosophy formed the bedrock of many defense-in-depth strategies. However, in recent years, a conscious shift in terminology has led to the emergence and widespread adoption of "allowlisting." This change is not merely semantic; it reflects a broader industry movement towards more inclusive language and clearer, more descriptive terminology in technical domains. As we navigate the intricacies of modern API ecosystems and the powerful role of an API gateway in managing traffic, the precision of language becomes even more significant. This comprehensive exploration will dissect both concepts, compare their historical and modern applications, highlight their functional similarities and subtle contextual differences, and provide insights into their practical implementation as cornerstones of a secure digital environment. We will examine how these principles are applied across various technological layers, from network firewalls to advanced API gateway solutions, ensuring a thorough understanding for security professionals, developers, and system administrators alike.
Understanding IP Whitelisting: The Traditional Approach to Access Control
IP Whitelisting represents a foundational security mechanism, a method deeply rooted in the principle of least privilege. At its core, IP Whitelisting is an access control strategy where a system or service explicitly lists the IP addresses or ranges that are permitted to connect, with all other IP addresses implicitly denied. This model operates on the premise that unless an IP address is on the "white list," it is considered unauthorized and will be blocked. It's an inverse approach to blacklisting, where specific malicious or unwanted IP addresses are blocked, but all others are allowed by default. Whitelisting, by contrast, starts from a position of absolute denial and only grants exceptions.
Historically, IP Whitelisting emerged as a relatively straightforward and effective means of securing network perimeters. In a world where corporate networks were largely confined to physical offices and resources were accessed primarily by internal employees with static IP addresses, whitelisting provided a robust barrier. It was, and in some contexts still is, a simple yet powerful gatekeeping mechanism. Imagine a scenario where a company's internal database server holds highly sensitive customer data. By whitelisting only the IP addresses of specific internal application servers or administrative workstations, the attack surface for that database is drastically reduced. Any attempt to connect from an IP address not on that approved list would be instantly rejected, long before any authentication credentials could even be attempted. This proactive blocking significantly mitigates risks from external attackers, unauthorized users, or even compromised systems outside the defined trusted perimeter.
The mechanism of IP Whitelisting typically involves configuring network devices or software to enforce these rules. This could be a hardware firewall at the network edge, a software firewall running on a server, or even specific configurations within an application itself. When an incoming network request arrives, the device or software intercepts it, examines the source IP address, and compares it against its internal whitelist. If a match is found, the connection is allowed to proceed to its intended destination. If no match exists, the connection is dropped, often without any further interaction, effectively making the protected resource invisible to unauthorized sources. This simplicity in operation contributes to its perceived reliability and ease of understanding.
Typical Use Cases for IP Whitelisting:
- Securing Administrative Interfaces: Perhaps the most common application is restricting access to critical administrative panels for servers, network devices, and management systems. Limiting SSH, RDP, or web-based admin access to a handful of known, secure IP addresses significantly reduces the risk of brute-force attacks or unauthorized configuration changes.
- Protecting Sensitive Databases: Database servers often contain the crown jewels of an organization's data. Whitelisting ensures that only specific application servers or trusted internal systems can initiate connections, creating a vital layer of defense around sensitive information.
- Restricting API Access for Partners: For businesses that expose APIs to trusted third-party partners, whitelisting the partners' public IP addresses ensures that only these authorized entities can consume specific API endpoints. This is a crucial first line of defense, often preceding token-based authentication. An API gateway can be configured to enforce such rules, acting as the primary gatekeeper.
- Enforcing VPN Tunnel Integrity: In scenarios where employees connect to internal resources via a Virtual Private Network (VPN), whitelisting can be used to ensure that only traffic originating from the VPN gateway itself (or specific IP ranges within the VPN's assigned pool) can reach certain systems, preventing direct internet access to these resources even if an employee's personal device is compromised.
- Controlling Access to Cloud Resources: In cloud environments, whitelisting specific IP ranges for access to storage buckets, serverless functions, or virtual machines is a standard practice to limit exposure to the broader internet.
Benefits of IP Whitelisting:
- Enhanced Security: By strictly defining who can access a resource, the attack surface is dramatically reduced. It's a proactive defense that denies access by default, making it much harder for attackers to even begin probing.
- Simplicity of Implementation (for static environments): For small, stable networks with predictable IP addresses, setting up and maintaining a whitelist can be quite straightforward.
- Compliance: Many regulatory frameworks and security standards recommend or mandate strict access controls, for which IP whitelisting serves as an excellent foundational measure.
- Cost-Effective: Often implemented using existing firewall capabilities, it doesn't always require significant additional investment in security tooling.
Drawbacks and Challenges:
Despite its clear advantages, IP Whitelisting is not without its limitations and complexities, especially in modern, dynamic environments:
- Lack of Flexibility: This is arguably its biggest weakness. In today's highly mobile and distributed workforce, where employees work from home, cafes, or co-working spaces with dynamic IP addresses, maintaining a static whitelist for individual users becomes impractical or impossible. Constantly updating lists can be an administrative nightmare.
- Management Overhead: As the number of authorized IPs grows, or as IPs frequently change (e.g., cloud instances, mobile users), the administrative burden of updating and verifying the whitelist can become substantial. Errors in management can lead to legitimate users being blocked or, worse, unauthorized IPs gaining access.
- Single Point of Failure (Conceptual): If a whitelisted IP address is compromised, an attacker gains immediate and unrestricted access to the protected resource, bypassing the initial IP-based security layer. This highlights the need for multi-layered security.
- Scalability Issues: For large enterprises with thousands of employees, external contractors, and a global presence, creating and managing a monolithic whitelist that covers all legitimate access points is a monumental task that often proves unsustainable.
- Problematic Terminology: Perhaps the most significant contemporary drawback, and the catalyst for the shift to "allowlisting," is the use of the term "whitelist" itself. In an era striving for inclusivity and sensitivity in language, terms like "whitelist" and "blacklist" (and their associated racial connotations) are increasingly being replaced by more neutral and descriptive alternatives. This semantic shift, while not altering the underlying technical function, reflects a growing awareness and commitment to responsible language in technology.
The traditional approach of IP Whitelisting, while robust for specific, static scenarios, therefore faces significant challenges when applied universally to the fluid and dynamic nature of modern IT infrastructures. This realization, coupled with the desire for more inclusive language, paved the way for the adoption of "allowlisting."
The Evolution to IP Allowlisting: A Modern Standard
The transition from "whitelisting" to "allowlisting" is more than just a superficial change in vocabulary; it reflects an industry-wide commitment to fostering inclusive language and adopting clearer, more descriptive terminology in technical domains. While the fundamental technical function remains identical – permitting access only from explicitly approved IP addresses – the shift to "allowlisting" represents a modernization of security communication and policy. This evolution is particularly pertinent in discussions around sophisticated infrastructure components like the API gateway, where precise language is essential for clear policy enforcement.
The primary rationale behind this terminology change stems from the desire to move away from terms that, even inadvertently, carry negative societal connotations. "Whitelist" and "blacklist" have historical associations that are deemed inappropriate in a modern, inclusive professional environment. "Allowlist" and "denylist" are direct, functional replacements that avoid these problematic undertones, making the technical concept clear without any extraneous baggage. This shift aligns with broader efforts across the technology sector to promote diversity, equity, and inclusion in all aspects, including language used in documentation, code, and professional discourse.
Functionally, IP Allowlisting is the exact equivalent of IP Whitelisting. It defines a set of IP addresses or IP ranges that are explicitly permitted to establish a connection or access a specific resource. All other IP addresses, not present on this allowlist, are by default denied access. This "default deny, explicit permit" principle remains the bedrock of this security strategy, emphasizing that access is only granted when specifically sanctioned. It is a proactive security measure designed to minimize the attack surface by ensuring that only known and authorized sources can interact with sensitive systems.
Core Principle: Default Deny, Explicit Permit
This principle is fundamental to robust cybersecurity and is the guiding philosophy behind IP Allowlisting. Instead of trying to identify and block every potential threat (which is an exhaustive and often impossible task, akin to a "denylist"), the "default deny, explicit permit" approach simplifies security by only allowing what is explicitly known and approved. This dramatically reduces the chances of an unknown vulnerability or an unlisted malicious actor gaining access. Any attempt to connect from an IP address not on the allowlist is inherently treated as suspicious and blocked, significantly enhancing the security posture of any system or network. This principle is applied universally across various security layers, from network firewalls to application-level access controls, and is a cornerstone of modern API gateway security configurations.
Implementation Details of IP Allowlisting:
IP Allowlisting is a versatile security control that can be implemented at multiple layers of the IT stack, providing defense-in-depth:
- Network Firewalls: These are often the first line of defense. Hardware or software firewalls can be configured to allow inbound or outbound traffic only from specified IP addresses or networks (using CIDR notation). This operates at the network layer (Layer 3/4 of the OSI model) and is highly effective for broad network segment protection.
- Cloud Security Groups/Network Security Groups (NSGs): In cloud computing environments (like AWS, Azure, Google Cloud), security groups or NSGs provide virtual firewall capabilities for virtual machines, databases, and other cloud resources. Users can define ingress and egress rules to allow traffic based on source IP, port, and protocol. This is an essential tool for securing cloud-native applications and microservices.
- Operating System Firewalls: Server-level firewalls (e.g.,
iptableson Linux, Windows Firewall) offer fine-grained control over network traffic reaching individual machines. They can complement network-level firewalls by adding another layer of defense directly on the host. - Application-Level Configuration: Some applications or services have built-in capabilities to configure IP-based access restrictions. This allows developers to hardcode or configure allowed IPs directly within the application logic, providing a very specific and targeted control.
- API Gateways: An API gateway plays a crucial role in modern distributed systems, acting as the single entry point for all API requests. It is an ideal place to implement IP Allowlisting, alongside other authentication and authorization mechanisms. An API gateway can inspect the source IP of incoming API calls and block those not on the allowlist before they even reach the backend services. This offloads security responsibility from individual microservices and centralizes access control, improving consistency and manageability. For instance, a sophisticated platform like APIPark, an open-source AI gateway and API management platform, provides robust capabilities for managing API access permissions. It allows organizations to define granular security policies, ensuring that only approved callers from specified IP ranges can invoke APIs, whether for traditional REST APIs or advanced AI models. This capability is integrated into its end-to-end API lifecycle management, enhancing overall API security and governance.
Key Distinctions (in context) and Advanced Use Cases:
While functionally identical, the adoption of "allowlisting" often coincides with a more modern approach to security, integrating with broader strategies:
- Integration with Automation and Infrastructure as Code (IaC): Modern allowlisting implementations are increasingly automated. Instead of manual updates, IP allowlists are often defined as part of Infrastructure as Code (e.g., Terraform, CloudFormation), ensuring consistency, version control, and rapid deployment of changes.
- Dynamic IP Management: With cloud resources frequently acquiring new IP addresses upon restart or scaling events, allowlisting often needs to integrate with dynamic DNS or cloud provider metadata services. For instance, allowing all instances within a specific cloud VPC or security group, rather than individual IPs.
- Zero Trust Architecture: IP Allowlisting is a foundational component of a Zero Trust security model. While Zero Trust goes further by verifying every request, user, and device regardless of their network location, IP Allowlisting serves as an initial perimeter control, ensuring that only known network segments can even initiate the verification process.
- Microservices Communication: In complex microservices architectures, an API gateway (like APIPark) might use allowlists to restrict which internal services can communicate with each other, adding another layer of "east-west" traffic security. This prevents unauthorized internal lateral movement in case one service is compromised.
- Hybrid Cloud Environments: Organizations operating in hybrid cloud environments can use IP allowlisting to ensure secure communication between on-premises data centers and cloud resources, allowing only specific public IPs from the corporate network to access cloud services.
The shift to "IP Allowlisting" not only addresses linguistic concerns but also signifies a broader evolution in how organizations approach network security. It's often part of a more comprehensive, automated, and context-aware security strategy, reflecting the dynamic demands of modern IT infrastructure and the critical role of platforms like an API gateway in managing and securing access to diverse APIs and services.
Practical Implementation and Configuration of IP Allowlisting
Implementing IP Allowlisting effectively requires careful planning, a clear understanding of network architecture, and continuous management. It's not a set-it-and-forget-it solution, but rather a dynamic security measure that must evolve with the needs of the organization. This section delves into the practical aspects of creating, managing, and optimizing IP allowlists, highlighting tools, challenges, and best practices. Understanding these details is crucial for anyone responsible for securing network perimeters, individual servers, or the entry points managed by an API gateway.
How to Create and Manage an IP Allowlist:
The first step in creating an IP allowlist is to meticulously identify all legitimate IP addresses or ranges that require access to the protected resource. This involves a thorough audit and understanding of your network topology and application dependencies.
- Identifying Legitimate IPs:
- Static IPs: For on-premises servers, workstations, or dedicated VPN endpoints, identifying static public or private IP addresses is straightforward. These are typically stable and require infrequent updates.
- Dynamic IPs: This is where complexity arises.
- Cloud Instances: Virtual machines, containers, or serverless functions in cloud environments often have dynamic public IP addresses. Instead of whitelisting individual IPs, it's more practical to allow traffic from specific cloud security groups, virtual private clouds (VPCs), or entire cloud regions if appropriate.
- Remote Users: Employees working from home often have dynamic IPs assigned by their ISPs. The most common solution here is to require them to connect via a corporate VPN, whose gateway has a static, whitelisted public IP. This aggregates all legitimate remote user traffic through a single, controlled point.
- Third-Party Services: If integrating with external services (e.g., payment gateways, analytics platforms), these services often publish a list of their outbound IP addresses that need to be allowlisted. These lists should be regularly checked for updates.
- Subnetting and CIDR Notation for Efficiency:
- Instead of listing individual IP addresses, utilize Classless Inter-Domain Routing (CIDR) notation (e.g.,
192.168.1.0/24) to specify entire subnets or ranges. This simplifies management, reduces the size of the allowlist, and makes it more scalable. For instance,10.0.0.0/8would allow any IP address within the entire 10.0.0.0-10.255.255.255 range, suitable for internal network segments. Always aim for the smallest practical CIDR block to minimize exposure.
- Instead of listing individual IP addresses, utilize Classless Inter-Domain Routing (CIDR) notation (e.g.,
- Tools and Methods for Implementation:
- Network Firewalls (Hardware/Software):
- Hardware Firewalls: Devices like Cisco ASA, Palo Alto Networks, Fortinet FortiGate, or Juniper SRX sit at the network perimeter. They offer robust features for creating granular IP access control lists (ACLs) based on source IP, destination IP, port, and protocol. This is ideal for protecting entire network segments.
- Software Firewalls:
iptablesorfirewalldon Linux systems and Windows Firewall provide host-based protection. They are excellent for ensuring that individual servers only accept connections from specific IPs, even if a broader network firewall is also in place. - Configuration Example (Linux iptables):
bash # Block all incoming traffic by default sudo iptables -P INPUT DROP # Allow established/related connections sudo iptables -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT # Allow SSH from a specific IP (e.g., your admin workstation) sudo iptables -A INPUT -s your_admin_ip -p tcp --dport 22 -j ACCEPT # Allow HTTP/HTTPS from a specific subnet (e.g., your web servers) sudo iptables -A INPUT -s 192.168.1.0/24 -p tcp --dport 80 -j ACCEPT sudo iptables -A INPUT -s 192.168.1.0/24 -p tcp --dport 443 -j ACCEPT # Allow Loopback sudo iptables -A INPUT -i lo -j ACCEPT # Log and drop anything else (optional, for debugging) # sudo iptables -A INPUT -j LOG --log-prefix "Dropped: " # sudo iptables -A INPUT -j DROP # Save rules (distribution-specific) # sudo apt-get install iptables-persistent (for Debian/Ubuntu) # sudo netfilter-persistent save
- Cloud Provider Security Groups:
- AWS Security Groups, Azure Network Security Groups, GCP Firewall Rules: These are critical for cloud deployments. They act as virtual firewalls attached to instances, subnets, or services. Rules are configured to allow ingress/egress traffic based on source/destination IP (or other security groups), ports, and protocols. They are highly dynamic and integrate seamlessly with cloud resource lifecycles. For example, an AWS Security Group rule might allow inbound SSH access from
my_office_public_ip/32.
- AWS Security Groups, Azure Network Security Groups, GCP Firewall Rules: These are critical for cloud deployments. They act as virtual firewalls attached to instances, subnets, or services. Rules are configured to allow ingress/egress traffic based on source/destination IP (or other security groups), ports, and protocols. They are highly dynamic and integrate seamlessly with cloud resource lifecycles. For example, an AWS Security Group rule might allow inbound SSH access from
- API Gateways:
- An API gateway is arguably one of the most strategic points to implement IP Allowlisting for APIs. As the single point of entry for all API traffic, it can enforce these rules globally across all APIs or granularly for specific API endpoints.
- Platforms like APIPark offer sophisticated API management capabilities, including the ability to configure fine-grained access permissions based on IP addresses. This means that even before authentication, the API gateway can filter out requests from unauthorized IP sources. APIPark, as an open-source AI gateway and API management platform, not only centralizes
APItraffic but also provides end-to-endAPIlifecycle management. Its features include resource access requiring approval, ensuring callers must subscribe to anAPIand await administrator approval, preventing unauthorizedAPIcalls. This advanced permission management system often complements IP allowlisting by adding another layer of security, controlling who can even attempt to subscribe or invoke anAPI. Thegateway's performance rivaling Nginx, detailedAPIcall logging, and powerful data analysis tools further enhance the security posture by providing insights into allowed and blocked traffic.
- Application-Level Logic: For highly specific scenarios, an application might enforce IP restrictions directly in its code. While effective, this decentralizes security and should generally be avoided in favor of network or gateway-level controls unless absolutely necessary.
- Network Firewalls (Hardware/Software):
Challenges and Best Practices:
Implementing IP Allowlisting effectively comes with its own set of challenges, requiring careful attention to detail and a proactive approach.
- Keeping the List Updated: This is a perpetual challenge.
- Process Automation: Integrate allowlist updates into automated deployment pipelines (CI/CD) or Infrastructure as Code (IaC) tools.
- Regular Review: Schedule periodic reviews of all allowlists to remove outdated entries and add new legitimate IPs. Assign ownership for specific lists.
- Change Management: Establish a clear change management process for any modifications to an allowlist, including required approvals and documentation.
- Avoiding Overly Broad Ranges: While CIDR notation is efficient, using overly broad ranges (e.g.,
/0for "any") defeats the purpose of allowlisting. Always aim for the narrowest possible range that covers legitimate traffic. A common mistake is allowing0.0.0.0/0(any IP) to a sensitive port or resource, which completely negates the security benefit. - Monitoring and Auditing Allowed Access:
- Log Analysis: Continuously monitor logs from firewalls, API gateways, and application servers for connections originating from allowed IPs. Even an allowed IP can be compromised.
- Alerting: Set up alerts for unusual activity from allowlisted IPs, such as excessive failed login attempts, unusual data transfers, or access at odd hours.
- Regular Audits: Periodically audit the access patterns and compare them against expected behavior.
- Combining with Other Security Measures: IP Allowlisting is a perimeter defense; it's not a silver bullet.
- Authentication and Authorization: Always combine IP allowlisting with robust user/application authentication (e.g., passwords, MFA, API keys, OAuth2, JWTs) and granular authorization (Role-Based Access Control - RBAC). An allowed IP alone should rarely grant full access. An API gateway is excellent for centralizing these authentication and authorization policies.
- Rate Limiting and Throttling: Even legitimate and allowlisted IPs can be used for abuse (e.g., DoS attacks, excessive polling). Implement rate limiting on your API gateway or application to prevent resource exhaustion.
- Intrusion Detection/Prevention Systems (IDS/IPS): These systems can detect and block malicious traffic even from allowlisted IPs if the traffic pattern indicates an attack.
- Web Application Firewalls (WAFs): WAFs protect against application-layer attacks (e.g., SQL injection, XSS) that IP allowlisting cannot prevent.
- Handling Dynamic IPs for Authorized Users:
- VPNs: As mentioned, requiring remote users to connect via a corporate VPN with a static public IP is the most common and secure solution.
- Proxy Servers: In some cases, organizations might use a proxy server with a static IP as an intermediary for specific external access, which can then be allowlisted.
- Reverse Proxies/Load Balancers: For incoming traffic to web services, a reverse proxy or load balancer often sits in front of the application servers. The API gateway itself typically functions as a reverse proxy. The allowlist would then apply to the public-facing IP of the reverse proxy/load balancer, and traffic to backend services would originate from its internal IPs.
By meticulously planning, carefully configuring, and continuously monitoring IP allowlists, organizations can establish a powerful and effective first line of defense for their digital assets, a critical component of any comprehensive cybersecurity strategy, especially when protecting and managing access to diverse APIs through an API gateway.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
Comparing and Contrasting: When to Use Each
In the discussion of IP-based access control, the terms "IP Whitelisting" and "IP Allowlisting" frequently appear, often interchangeably. However, as we've explored, while their functional mechanisms are identical, their contextual implications and preferred usage have diverged significantly. This section aims to clarify their relationship, articulate when each term might be encountered, and ultimately advocate for the adoption of the modern standard.
No Fundamental Functional Difference: A Semantic Shift
It is crucial to re-emphasize that from a purely technical standpoint, there is no functional difference between IP Whitelisting and IP Allowlisting. Both methodologies embody the "default deny, explicit permit" security principle: * A predefined list of IP addresses (or ranges) is established. * Any incoming network traffic originating from an IP address on this list is permitted to proceed. * Any incoming network traffic from an IP address not on this list is automatically blocked or rejected.
The logic applied by a firewall, a server's operating system, a cloud security group, or an API gateway is precisely the same, regardless of whether the configuration option or documentation uses the term "whitelist" or "allowlist." The core purpose—to restrict network access to only known and trusted sources—remains constant. The transformation in terminology is primarily semantic, driven by a desire for more inclusive and unambiguous language within the technology industry.
When "Whitelisting" is Still Encountered:
Despite the industry's shift, the term "whitelisting" has been ingrained in cybersecurity vocabulary for decades, and as such, it will continue to appear in various contexts:
- Legacy Systems and Documentation: Older software, existing network configurations, or historical documentation often use "whitelisting." When working with established infrastructure, you may still find configuration files or user interfaces that explicitly refer to "whitelists." It is important to understand that in these contexts, the term refers to the same underlying functionality as allowlisting.
- Informal Communication: Among practitioners who have been in the field for a long time, "whitelisting" might still be used casually in conversations, even if their formal documentation uses "allowlisting." This is a natural consequence of deeply embedded terminology.
- Proprietary Products: Some vendors, particularly those with long-standing product lines, may continue to use "whitelist" in their product interfaces, manuals, or marketing materials until they undergo a full rebranding or update cycle.
In these instances, while encountering "whitelisting," one should mentally substitute "allowlisting" to maintain alignment with modern best practices and to promote inclusive language where possible.
When "Allowlisting" is Preferred and Recommended:
"IP Allowlisting" is the unequivocally preferred and recommended term for all new implementations, security policy documents, and contemporary discussions. Its adoption reflects a commitment to:
- Inclusive Language: Moving away from terms with potentially problematic connotations, promoting a more welcoming and diverse professional environment.
- Clarity and Descriptiveness: "Allowlist" directly describes the action being taken—allowing specific entities. It is a more transparent and functionally accurate descriptor than "whitelist," which relies on a color metaphor.
- Industry Best Practices: Leading organizations, open-source projects, and standards bodies are actively adopting "allowlist" and "denylist" as standard terminology. Aligning with these practices ensures consistency and clarity across the industry.
- Modern Security Architectures: As organizations embrace cloud-native, microservices, and API gateway architectures, the term "allowlisting" is becoming the default, integrated into cloud provider documentation, modern security frameworks, and API management platforms.
Therefore, when designing new systems, writing security policies, creating network configurations, or discussing access control mechanisms for your APIs managed by an API gateway, "IP Allowlisting" should always be the chosen term.
The Underlying "Default Deny" Principle:
Both "whitelisting" and "allowlisting" are manifestations of the "default deny" security posture. This principle dictates that unless an action, access, or entity is explicitly permitted, it should be denied. This is the strongest possible security stance, as it significantly limits the attack surface and reduces the risk of zero-day exploits or unknown vulnerabilities being exploited. By starting from a position of absolute denial, organizations only create specific, controlled exceptions, ensuring that any unapproved activity is automatically blocked. This principle is fundamental to securing everything from critical infrastructure to individual API endpoints.
Here's a comparison table summarizing the key aspects:
| Feature/Aspect | IP Whitelisting (Traditional Context) | IP Allowlisting (Modern Context) |
|---|---|---|
| Primary Term | Older, widely adopted, potentially problematic terminology | Preferred, inclusive, and descriptive terminology |
| Core Functionality | Explicitly permits traffic from specified IPs, denies all others | Explicitly permits traffic from specified IPs, denies all others |
| Security Principle | Default Deny, Explicit Permit | Default Deny, Explicit Permit |
| Common Tools/Layer | Firewalls (hardware/software), Router ACLs, OS-level controls | Firewalls, Cloud Security Groups, API Gateways, Microservice Meshes, IaC |
| Integration Pattern | Often manual configuration or static lists | More likely integrated with CI/CD, Infrastructure as Code (IaC), IAM systems, and automated security pipelines |
| Best Practice Status | Discouraged in new contexts due to terminology; found in legacy systems | Recommended for all new security policies, implementations, and documentation |
| Context of Use | Can appear in legacy systems, older documentation, informal discussions | Standard in modern cloud-native, API, and gateway architectures, formal security policies, and new product development |
| Linguistic Impact | Carries potential negative connotations | Promotes clarity, inclusivity, and responsible language |
In conclusion, while "IP Whitelisting" and "IP Allowlisting" perform the exact same technical function, the latter term is the modern, preferred standard. Adopting "IP Allowlisting" not only aligns an organization with current industry best practices and inclusive language but also reinforces a clear, functional description of a vital security control, especially within the context of managing access through an API gateway to various APIs and services.
Beyond Simple IP Allowlisting: Advanced Considerations
While IP Allowlisting serves as a fundamental and highly effective first line of defense, its utility often thrives when integrated into a broader, multi-layered security strategy. Relying solely on IP Allowlisting can leave significant vulnerabilities, especially in dynamic environments where identities, devices, and network locations are constantly shifting. Modern cybersecurity demands a holistic approach, where IP Allowlisting is just one component among many, complementing other controls to achieve a robust security posture. This section explores advanced considerations that extend beyond basic IP Allowlisting, focusing on how it integrates with other security measures to create a truly resilient system, particularly for securing APIs and the infrastructure managed by an API gateway.
Dynamic IP Challenges and Solutions:
The most persistent challenge for IP Allowlisting in today's world is the prevalence of dynamic IP addresses. * Mobile and Remote Workforce: Employees connecting from homes, coffee shops, or client sites almost invariably use dynamic IPs assigned by their Internet Service Providers (ISPs). Attempting to allowlist every possible dynamic IP is futile and unmanageable. * Solution: Corporate VPNs: The industry-standard solution is to mandate the use of a corporate Virtual Private Network (VPN). All remote users connect to the VPN gateway, which typically has one or a few static public IP addresses. Only these static VPN gateway IPs are then allowlisted, effectively funneling all legitimate remote traffic through a controlled, identifiable point. This centralizes access control and simplifies allowlist management dramatically. * Cloud Computing and Microservices: Cloud instances, serverless functions, and containers often have dynamic public or private IP addresses that can change upon scaling events, restarts, or redeployments. * Solution: Security Groups and Service Tags: Instead of allowing individual dynamic IPs, cloud providers offer mechanisms like Security Groups (AWS), Network Security Groups (Azure), or Service Tags. You can allow traffic from an entire security group or virtual network, regardless of the individual IPs of instances within it. This leverages the cloud's native networking capabilities for dynamic resource management. * Solution: Private Networking: For communication between microservices, prioritize private networking (e.g., within a VPC) rather than exposing services directly to the internet. IP Allowlisting can then be applied to private IP ranges. * Solution: Internal DNS/Service Mesh: For east-west traffic between internal services, a service mesh or internal DNS can manage service discovery and access, reducing the reliance on direct IP allowlisting for every single internal interaction.
Combining with Authentication and Authorization:
IP Allowlisting acts as a coarse-grained network perimeter defense. It determines who can even knock on the door. It is not a substitute for robust authentication (verifying who you are) and authorization (determining what you are allowed to do). * Multi-Factor Authentication (MFA): Even if an IP is allowlisted, and a user's password is leaked, MFA provides a crucial second layer of verification. Always enforce MFA for administrative access and for any sensitive applications. * Strong User Authentication: Implement strong password policies, account lockout mechanisms, and regularly review user accounts. For APIs, this means using secure API keys, OAuth2 tokens, or JSON Web Tokens (JWTs). An API gateway is the ideal place to enforce these authentication schemes for all incoming API calls. * Role-Based Access Control (RBAC): Once authenticated, users or applications should only be granted the minimum necessary permissions to perform their tasks. RBAC ensures that privileges are aligned with roles. For APIs, this means defining fine-grained permissions for different API endpoints or operations. An API gateway can implement RBAC by validating scopes or claims within tokens. For instance, APIPark allows for the creation of multiple teams (tenants), each with independent applications, data, user configurations, and security policies. This tenant isolation, combined with features like API resource access requiring approval, demonstrates how granular access control works hand-in-hand with perimeter defenses. It allows for detailed API call logging, providing auditable trails for every allowed access.
Rate Limiting and Throttling:
Even an allowlisted IP address belonging to an authorized user or application can be a source of abuse, whether accidental or malicious. * Preventing DoS/DDoS: An authorized user's system could be compromised and used to launch a Distributed Denial of Service (DDoS) attack against your APIs or services. * Resource Exhaustion: Legitimate clients might make excessive requests, leading to server overload, increased costs, or degradation of service for other users. * Scraping: Even from an allowed IP, an attacker could try to scrape data rapidly. * Solution: Implement rate limiting and throttling on your API gateway or application. This limits the number of requests a single client (identified by IP, API key, or user token) can make within a given time frame. An API gateway is perfectly positioned to enforce these policies, protecting your backend services from being overwhelmed.
DDoS Protection (Beyond Basic Allowlisting):
While IP Allowlisting can help mitigate some forms of volumetric DDoS attacks by blocking unknown sources, it is not a comprehensive DDoS solution. Sophisticated DDoS attacks can originate from legitimate-looking or allowlisted IPs if those systems are compromised. * Solution: Dedicated DDoS Mitigation Services: For robust DDoS protection, integrate with specialized DDoS mitigation services (e.g., Cloudflare, Akamai, AWS Shield, Azure DDoS Protection). These services operate at a scale far beyond what typical firewalls or API gateways can handle, absorbing and filtering massive amounts of malicious traffic before it reaches your infrastructure.
Geo-fencing:
In some scenarios, access restrictions might extend beyond specific IP addresses to entire geographic regions. * Compliance and Legal Restrictions: Certain data or services may only be accessible from specific countries due to regulatory requirements (e.g., GDPR, CCPA). * Business Logic: An application might only be intended for users in certain geographical markets. * Threat Mitigation: Blocking entire countries known for high volumes of cyberattacks can reduce overall risk. * Solution: Geo-fencing capabilities are often built into firewalls, WAFs, or API gateways, leveraging IP geolocation databases. This allows administrators to allow or deny access based on the country of origin of the request.
Zero Trust Architecture:
IP Allowlisting naturally fits into a Zero Trust security model, but it is just one piece of a much larger puzzle. Zero Trust operates on the principle of "never trust, always verify," meaning every access request, whether from inside or outside the network perimeter, must be authenticated, authorized, and continuously monitored. * How Allowlisting Contributes: IP Allowlisting acts as an initial filter, ensuring that only expected network segments can even initiate the Zero Trust verification process. It reduces the surface area that needs continuous validation. * Beyond Allowlisting: Zero Trust extends verification to user identity, device posture, application context, and data sensitivity. It's about micro-segmentation, least privilege, and continuous monitoring. A sophisticated API gateway supports Zero Trust by centralizing authentication, authorization, policy enforcement, and logging for every API call, verifying requests even from 'allowed' networks before passing them to backend services.
Continuous Monitoring and Auditing:
No security measure is effective without continuous vigilance. * Log Everything: Ensure that all attempted connections, both allowed and denied, are logged by your firewalls, API gateways, and application servers. Detailed API call logging, like that provided by APIPark, is crucial for this. * Alerting on Anomalies: Configure alerts for unusual patterns, such as a sudden surge of denied connections, repeated failed authentication attempts from an allowlisted IP, or abnormal traffic volumes. * Regular Audits: Periodically review logs and security configurations to ensure they remain effective and aligned with evolving threats and organizational needs. This includes auditing the allowlists themselves for accuracy and necessity. APIPark's powerful data analysis features, which analyze historical call data to display long-term trends and performance changes, are invaluable here for preventive maintenance and threat detection.
By moving beyond simple IP Allowlisting and integrating it with these advanced considerations, organizations can build a resilient, multi-layered security architecture capable of defending against the sophisticated threats of the modern digital landscape. This holistic approach, often orchestrated and enforced through a central API gateway, ensures that crucial APIs and services are protected at every possible ingress point.
Conclusion
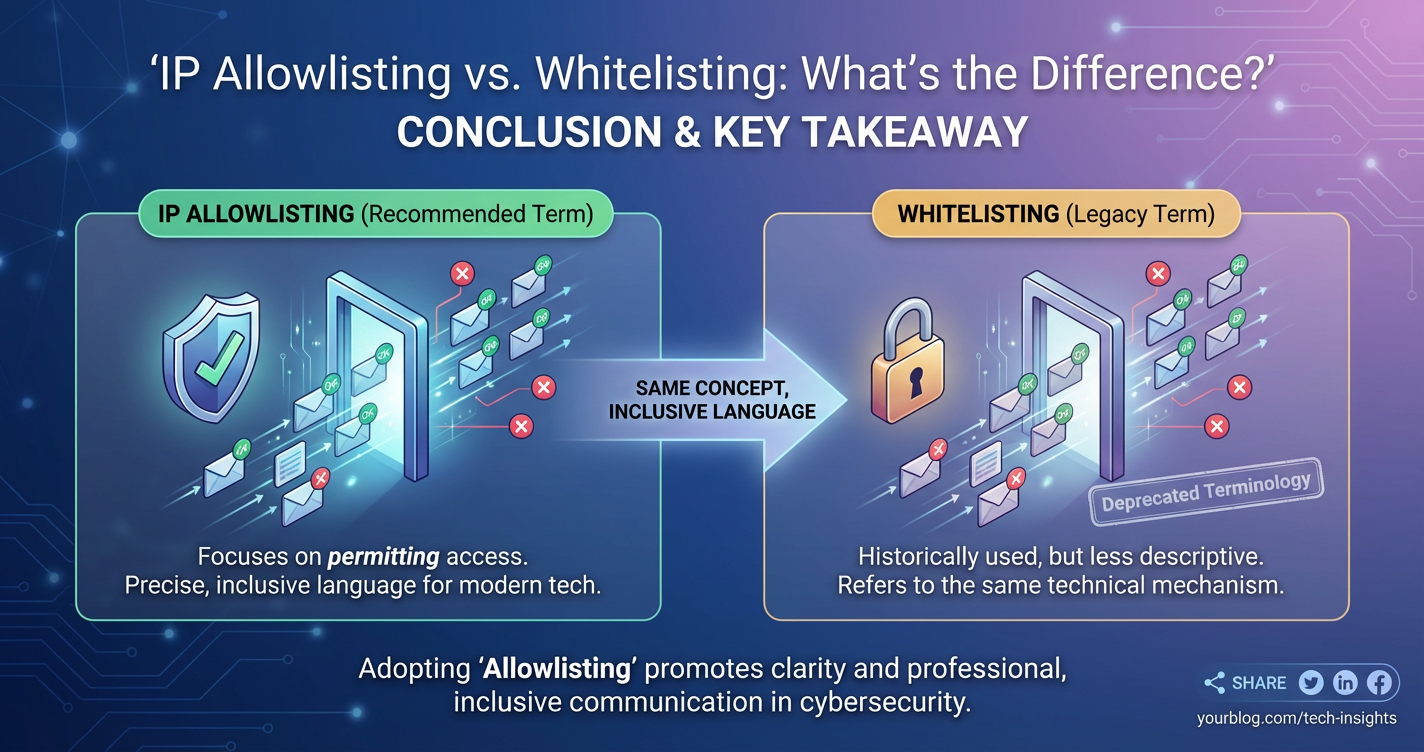
The journey from "IP Whitelisting" to "IP Allowlisting" is a testament to the dynamic nature of cybersecurity, reflecting not only technological advancements but also an evolving awareness of language and its impact. While their underlying technical function remains identical – the explicit permission of traffic from designated IP addresses while denying all others – the modern adoption of "IP Allowlisting" signifies a conscious move towards more inclusive, descriptive, and globally appropriate terminology. This shift is vital for fostering clear communication, aligning with industry best practices, and promoting a more respectful environment within the technology sector.
At its core, IP Allowlisting embodies the fundamental cybersecurity principle of "default deny, explicit permit." This robust approach dramatically shrinks the attack surface by ensuring that only known and authorized entities can even attempt to access critical systems. Whether implemented at the network perimeter via firewalls, within cloud environments through security groups, or at the application layer by an API gateway, allowlisting serves as an indispensable first line of defense. It acts as a digital bouncer, filtering out the vast majority of unsolicited and potentially malicious traffic before it can even reach sensitive data or services. For an API gateway, this capability is particularly potent, allowing it to act as a central gatekeeper, enforcing IP-based access controls across an entire suite of APIs, from traditional REST interfaces to cutting-edge AI services. Platforms like APIPark exemplify this modern approach, offering advanced API management functionalities that integrate seamless access control, robust logging, and powerful analytics, all while managing the entire API lifecycle.
However, the efficacy of IP Allowlisting is amplified when it is viewed not as a standalone solution, but as a foundational component within a comprehensive, multi-layered security strategy. In an era of dynamic IP addresses, mobile workforces, and sophisticated cyber threats, it must be complemented by other crucial controls. Robust authentication and authorization mechanisms (such as MFA, OAuth2, and RBAC) ensure that even allowlisted users or applications are thoroughly verified for who they are and what they are permitted to do. Rate limiting and throttling protect against abuse from authorized sources, while dedicated DDoS mitigation services safeguard against large-scale volumetric attacks. Furthermore, the integration of allowlisting into a broader Zero Trust architecture ensures continuous verification, regardless of network location. The necessity of continuous monitoring, detailed logging, and regular auditing cannot be overstated, as vigilance is key to detecting and responding to evolving threats, even from seemingly trusted sources.
In conclusion, "IP Allowlisting" is more than just a preferred term; it represents a commitment to clear, secure, and inclusive practices in the digital realm. By understanding its foundational role, recognizing its powerful benefits, and diligently integrating it with a diverse arsenal of complementary security measures, organizations can build truly resilient defenses. For any entity leveraging APIs, the strategic deployment of an API gateway with sophisticated allowlisting and access management capabilities is not merely an advantage, but an absolute necessity in safeguarding their digital assets against an ever-present and evolving threat landscape. The ongoing evolution of cybersecurity demands a continuous commitment to best practices, with IP allowlisting standing firm as a cornerstone of this enduring effort.
Frequently Asked Questions (FAQs)
1. What is the fundamental difference between IP Whitelisting and IP Allowlisting? Functionally, there is no difference. Both "IP Whitelisting" and "IP Allowlisting" refer to the same security mechanism: explicitly defining a list of IP addresses or ranges that are permitted to access a resource, while all others are denied by default. The change to "Allowlisting" is primarily semantic, driven by an industry-wide effort to adopt more inclusive, descriptive, and unambiguous terminology, moving away from terms like "whitelist" and "blacklist" that carry potentially problematic connotations.
2. Why should I use IP Allowlisting instead of relying solely on usernames and passwords? IP Allowlisting provides a crucial first layer of defense by restricting who can even attempt to access a system or API. It significantly reduces the attack surface by blocking unauthorized network traffic upfront. While usernames and passwords (or API keys/tokens) are essential for authentication (verifying who you are), IP Allowlisting acts as a perimeter control. Combining both creates a multi-layered security approach: first, only known IP sources can connect, and then, only authenticated and authorized users/applications from those sources can proceed. An API gateway is excellent for enforcing both layers.
3. What are the main challenges when implementing IP Allowlisting in modern environments? The primary challenges include managing dynamic IP addresses (common for remote workers or cloud resources), keeping the allowlist updated, avoiding overly broad IP ranges, and ensuring it's integrated with other security measures. For remote users, a corporate VPN with a static IP is often the solution. In cloud environments, using cloud-native security groups that can allow traffic from other defined groups or services helps manage dynamism. Continuous review and automation through Infrastructure as Code (IaC) are crucial for maintaining an effective allowlist.
4. Can an API gateway help with IP Allowlisting? Absolutely. An API gateway is a strategic component for implementing IP Allowlisting for your APIs. As the single entry point for all API traffic, it can be configured to inspect the source IP address of incoming requests and deny access if the IP is not on the approved allowlist. This centralizes API access control, offloads security from backend services, and can integrate IP-based restrictions with other API security policies like authentication, authorization, and rate limiting. Platforms like APIPark are specifically designed to manage such access controls for APIs.
5. Is IP Allowlisting enough to protect against all cyber threats? No, IP Allowlisting is a foundational security measure but not a complete solution. It's best used as part of a comprehensive, multi-layered security strategy. While it effectively reduces the attack surface, it doesn't protect against attacks originating from an allowlisted (but compromised) IP, application-layer vulnerabilities (like SQL injection), or sophisticated phishing attacks that bypass perimeter controls. Therefore, it must be combined with strong authentication (e.g., MFA), robust authorization (e.g., RBAC), rate limiting, intrusion detection systems, Web Application Firewalls (WAFs), and continuous monitoring for truly robust protection.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.