IP Allowlisting vs Whitelisting: What's the Real Difference?
In the labyrinthine world of cybersecurity, precision in language is not merely a matter of semantics; it is a cornerstone of robust defense. As digital landscapes expand, encompassing everything from intricate microservices to expansive cloud infrastructures, the methods used to control access become increasingly vital. Among the most fundamental of these methods are IP whitelisting and IP allowlisting – terms often used interchangeably, yet harbouring nuances that, while subtle, speak to a broader evolution in technological communication and security philosophy. This extensive exploration aims to peel back the layers of these seemingly identical concepts, dissecting their origins, mechanisms, advantages, and challenges, to reveal the "real" difference and, more importantly, to illuminate why this distinction matters in the contemporary digital epoch.
The imperative for stringent access control has never been more pressing. Every day, organizations face a barrage of sophisticated cyber threats, from brute-force attacks to advanced persistent threats, all aiming to breach perimeters and exploit vulnerabilities. In this high-stakes environment, the principle of "default deny" reigns supreme. This principle dictates that unless explicitly permitted, all access is denied. IP whitelisting and allowlisting are direct applications of this tenet, acting as digital gatekeepers that scrutinize every incoming connection, granting passage only to those pre-approved entities identified by their unique Internet Protocol (IP) addresses. Whether safeguarding sensitive data within a corporate network, regulating traffic to a critical backend API, or fortifying the entry points of an API gateway, these access control mechanisms are indispensable tools in a security architect's arsenal.
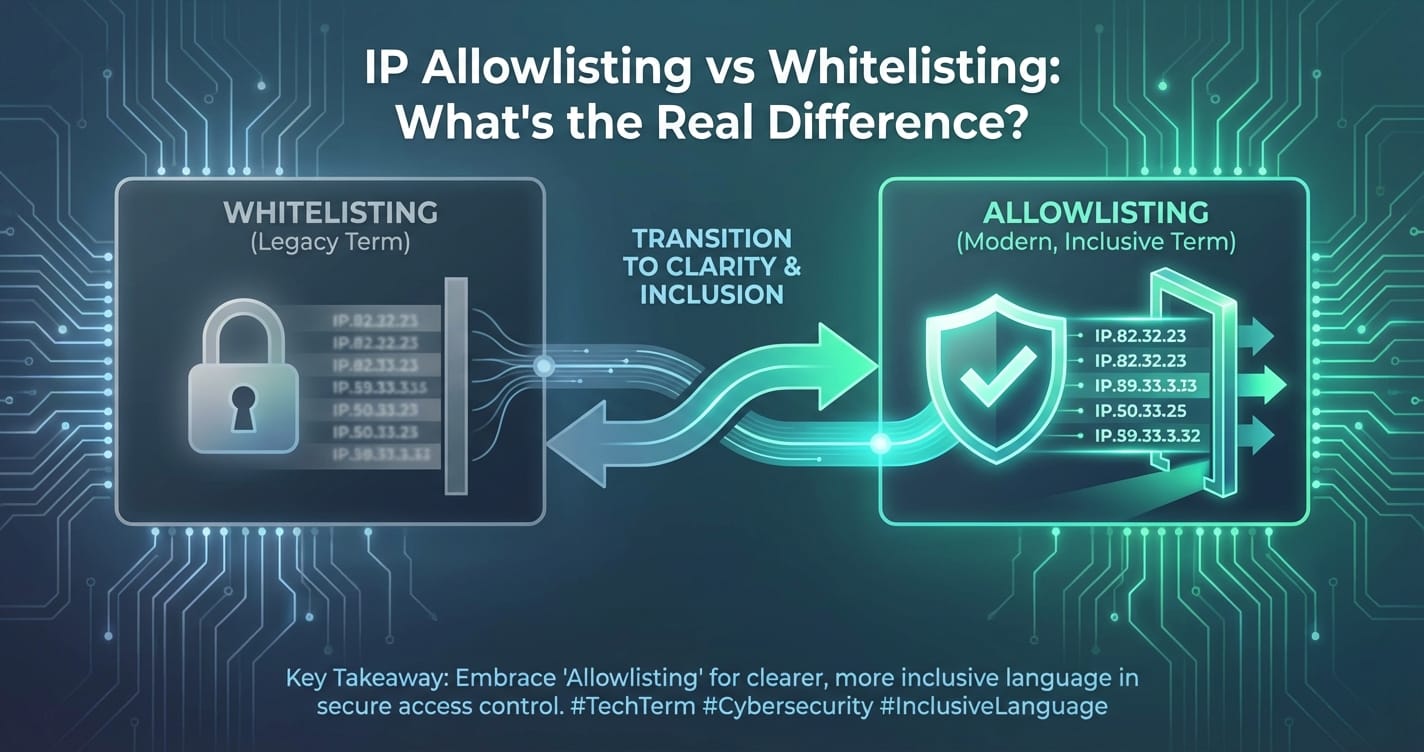
However, the journey from traditional network security to modern cloud-native architectures has brought with it not only technological advancements but also a re-evaluation of terminology. Terms that once seemed innocuous are now being reconsidered for their historical connotations or for their potential to foster miscommunication in an increasingly global and diverse industry. This article will meticulously dissect both "IP whitelisting" and "IP allowlisting," demonstrating that while their functional outcomes are virtually identical – both creating an explicit list of permissible IP addresses – the underlying shift in language represents a deliberate move towards clarity, inclusivity, and a more precise articulation of security policy. By understanding these subtle distinctions, practitioners can not only enhance their technical implementations but also foster clearer communication, ultimately building more resilient and comprehensible security frameworks for the future.
Deep Dive into IP Whitelisting: A Traditional Bastion of Security
IP whitelisting represents one of the oldest and most trusted methods of network access control, fundamentally rooted in the security principle of "default deny." At its core, IP whitelisting involves creating an explicit, predefined list of IP addresses that are authorized to access a specific network resource, system, or service. Any IP address not found on this list is automatically and unequivocally denied access. This mechanism operates like an exclusive guest list for a private event: only those whose names (IP addresses) are on the list are permitted entry, while all others are turned away at the door without question.
The term "whitelist" itself carries a historical weight, stemming from analogous concepts in physical security and general administrative practices. Historically, a "white list" might refer to a roster of approved personnel, a list of trusted suppliers, or even a catalogue of acceptable books in a library. In the digital realm, this concept was seamlessly translated to network access control in the early days of computing and the internet. As networks became interconnected and threats began to emerge, the need to explicitly designate trusted sources became paramount. Firewalls and early network access control systems naturally adopted this terminology to describe their permit-by-exception rulesets. The widespread adoption of "whitelist" across vendor documentation, industry standards, and security literature solidified its position as a conventional term for explicit permission-based access control for decades.
The mechanism of IP whitelisting is elegantly simple yet profoundly effective. When a network packet arrives at a protected resource (e.g., a server, a database, an API gateway), the access control system first extracts the source IP address from the packet header. This source IP is then compared against the established whitelist. If a match is found, the packet is allowed to proceed to its intended destination. If no match is found, the packet is immediately dropped or rejected, preventing any further interaction with the protected resource. This process occurs at various layers of the network stack, depending on where the whitelist is implemented. For instance, network-level firewalls might perform whitelisting at Layer 3 (IP layer), while application-level API gateways might apply it before routing requests to backend services.
The implementation of IP whitelisting is pervasive across virtually every segment of IT infrastructure. Firewalls, whether hardware or software-based, are perhaps the most common points of application, allowing administrators to restrict incoming connections to specific ports or services from only authorized IP ranges. Routers can employ whitelisting rules to control traffic flow between different network segments. More granularly, operating systems can be configured to whitelist specific IPs for administrative access (e.g., SSH, RDP). Database servers frequently utilize IP whitelisting to ensure that only approved application servers or developer workstations can establish connections, thereby safeguarding sensitive data from unauthorized direct access. In the context of modern application development, an API gateway often serves as a critical enforcement point for IP whitelisting. By configuring the API gateway to only accept requests from known client applications or partner networks, organizations can dramatically reduce the attack surface for their exposed APIs, ensuring that only legitimate consumers can interact with their services. This is particularly crucial for backend APIs that power mobile applications, web portals, or B2B integrations, where an unauthorized request could lead to data breaches or service disruptions.
One of the most significant advantages of IP whitelisting is the robust security posture it enforces. By adhering to the "default deny" principle, it inherently minimizes the attack surface. Instead of trying to identify and block every conceivable malicious IP address (a task akin to finding a needle in an ever-growing haystack), whitelisting focuses on explicitly identifying the known good. This approach significantly reduces the risk of zero-day exploits or novel attack vectors originating from unknown sources, as any unlisted IP is automatically deemed untrusted. For environments with a finite and well-defined set of authorized users or systems, such as internal corporate networks, closed-loop systems, or dedicated partner integrations, whitelisting offers unparalleled control and predictability. It provides a clear, auditable trail of who is allowed to access what, simplifying compliance efforts and security audits. For instance, a financial institution might whitelist only its internal network IP ranges to access its core banking APIs, drastically limiting exposure to external threats.
Despite its powerful security benefits, IP whitelisting is not without its challenges and disadvantages. Its primary drawback lies in its inherent rigidity and the associated maintenance overhead, especially in dynamic or large-scale environments. In scenarios where authorized IP addresses change frequently (e.g., remote workers with dynamic IPs, cloud services with auto-scaling IPs), maintaining an accurate and up-to-date whitelist can become a cumbersome and error-prone task. Manual updates can lead to delays in legitimate access or, conversely, create security gaps if outdated entries are not promptly removed. Scaling whitelists to accommodate a large and diverse user base, or a myriad of client applications accessing an API gateway, can become practically unfeasible, necessitating more flexible access control mechanisms like token-based authentication in conjunction with whitelisting for broader access.
Furthermore, whitelisting can lead to "false negatives," where legitimate users or systems are denied access simply because their IP address was not correctly added or updated on the list. This can result in service disruptions, user frustration, and increased support costs. There's also the persistent risk of human error: a single typo in an IP address range or an oversight in removing a no-longer-authorized entry can either open a security loophole or prevent legitimate access. Even more critically, if a whitelisted third-party IP address becomes compromised, it effectively grants the attacker an authorized entry point into the protected system, bypassing the very security mechanism designed to keep them out. This highlights the need for a multi-layered security approach, where IP whitelisting is just one component among many, including robust authentication, authorization, and continuous monitoring.
In practical terms, real-world examples of IP whitelisting abound. Consider a system administrator who wants to restrict SSH access to critical servers. They would configure the server's firewall to whitelist only the IP addresses of their administrative workstations and the corporate VPN gateway. Any SSH connection attempt originating from an IP address not on this specific list would be immediately rejected. Similarly, an organization collaborating with a specific business partner might whitelist the partner's public IP range to allow their applications to securely connect to a dedicated API for data exchange. This ensures that only the intended partner can access the API, preventing unauthorized third parties from probing or exploiting the endpoint. Within an enterprise architecture, an API gateway might use IP whitelisting to control which internal departments or specific microservices are allowed to call certain sensitive backend APIs. This creates a secure internal perimeter, even within a complex, distributed system, ensuring that only approved internal components can communicate with high-value assets.
Deep Dive into IP Allowlisting: The Evolution of Terminology
IP allowlisting, functionally speaking, is the direct contemporary counterpart to IP whitelisting. It describes the exact same technical mechanism: creating an explicit, predefined list of IP addresses that are granted permission to access a specific resource, while all other IP addresses are implicitly denied. The fundamental principle of "default deny" remains absolutely central to allowlisting, just as it is with whitelisting. However, the emergence and increasing adoption of "allowlisting" over "whitelisting" signals a significant, albeit largely semantic, shift in the language of cybersecurity and technology at large. This transition is not merely a rebranding exercise; it reflects a broader movement towards more neutral, precise, and inclusive terminology within the tech industry.
The rationale behind the shift from "whitelist" to "allowlist" is multifaceted and deeply rooted in modern discourse concerning language. Primarily, it addresses concerns about the historical connotations of color-coded terms like "white" and "black" lists. In many cultures and contexts, "white" is associated with purity, permission, and good, while "black" is associated with exclusion, prohibition, and bad. This association, critics argue, can unintentionally perpetuate biases and contribute to exclusionary language. By moving to terms like "allowlist" and "blocklist" (instead of "blacklist"), the industry aims to adopt language that is more neutral, objective, and devoid of potentially problematic social implications. This change promotes a more inclusive environment within global tech teams and aligns with broader efforts to remove biased language from technical documentation and codebases.
Beyond inclusivity, "allowlist" also offers a degree of increased clarity and precision in its description of the action being performed. "Allow" explicitly denotes the granting of permission, making the function immediately understandable. Unlike "white," which is an adjective that implies a category, "allow" is a verb that describes an action. This subtle linguistic difference can contribute to clearer communication, especially in contexts where English might not be the primary language, or when conveying complex security policies to diverse stakeholders. When an administrator says they are "allowlisting" an IP, the intent is unmistakably to grant it permission. This precise verb usage aligns with modern cybersecurity lexicon that prioritizes direct and action-oriented language.
From an operational perspective, the mechanism and implementation of IP allowlisting are functionally identical to whitelisting. When an authorized IP address attempts to connect to a protected resource—be it a web server, a database, a microservice, or a sophisticated API gateway—the system consults its allowlist. If the IP address is present on the list, the connection is permitted. If it is not, the connection is rejected. This rigorous enforcement ensures that only explicitly sanctioned entities can interact with critical digital assets. In contemporary cloud environments and SaaS platforms, where resources are dynamically provisioned and accessed by a myriad of internal and external services, allowlisting is a cornerstone of network segmentation and access control. Many cloud providers and modern security tools have transitioned their terminology to "allowlist" in their configuration interfaces and documentation, reflecting this industry-wide shift.
Consider the deployment of microservices behind an API gateway. Each microservice might expose a specific API endpoint, and not all external clients or even internal services should have unrestricted access to every endpoint. An API gateway can implement IP allowlisting to ensure that, for example, a highly sensitive "payment processing" API can only be invoked by the IP addresses of the "order fulfillment" microservice and a specific internal billing application, even if the gateway itself is publicly accessible. This level of granular control, enforced at the gateway layer, is crucial for maintaining the security integrity of a complex distributed system. Similarly, when integrating with third-party vendors or external partners, an organization might allowlist specific IP ranges from those partners to grant them secure access to specific collaboration APIs or data exchange points. This approach minimizes the risk of unauthorized access while facilitating necessary business collaborations.
The advantages of allowlisting largely mirror those of whitelisting, but they are re-framed within the context of contemporary communication and ethical considerations. It still provides a fundamentally strong security posture by adhering to the "default deny" principle, drastically reducing the attack surface. By explicitly defining what is permitted, organizations can maintain a high degree of control over who accesses their resources, enhancing predictability and reducing the likelihood of unexpected intrusions. The primary added benefit, however, is the enhanced clarity and inclusivity it brings to communication. Adopting "allowlist" aligns an organization with modern best practices in language and fosters a more welcoming and respectful environment for diverse teams globally. This seemingly minor linguistic shift contributes to a more professional and forward-thinking image within the technology community.
However, it is crucial to recognize that the term "allowlist" does not magically resolve the inherent operational challenges associated with this access control mechanism. The disadvantages are fundamentally the same as those faced by whitelisting. Allowlisting still suffers from rigidity: managing a dynamic list of IP addresses in a constantly evolving network environment remains a significant administrative burden. If IP addresses change frequently, constant updates are required, which can be time-consuming and prone to human error. Scalability issues persist; for highly dynamic cloud environments or large public-facing services with a vast and unpredictable user base, allowlisting every single potential IP becomes impractical, if not impossible. In such scenarios, other security mechanisms like robust authentication and authorization (e.g., OAuth, API keys, JWTs) become more appropriate, often working in tandem with broad network-level protections.
Moreover, the risk of "false negatives" persists: a legitimate user or service might be inadvertently blocked if their IP address is not correctly entered or updated in the allowlist, leading to service disruption and operational friction. The critical vulnerability associated with a compromised allowed IP also remains. If an IP address on the allowlist is exploited by an attacker, that attacker gains the same level of trust and access as the legitimate entity, effectively bypassing the allowlist mechanism. This underscores the necessity of a multi-layered security strategy, where IP allowlisting is but one defense mechanism among many, complemented by endpoint security, strong authentication, behavioral analytics, and continuous threat monitoring.
Contemporary examples of IP allowlisting are ubiquitous. Cloud service providers (CSPs) often allow users to configure security groups or network access control lists (NACLs) using IP allowlisting rules. For instance, a cloud-hosted database might be configured to allow inbound traffic only from the application servers' IP addresses and the organization's office VPN IP range. Similarly, a modern API management platform like APIPark, an open-source AI gateway and API management platform, offers robust features for managing and securing APIs. Such platforms intrinsically leverage concepts like IP allowlisting to enforce granular access policies. An API gateway powered by APIPark could be configured to allow API calls to specific AI models or custom REST services only from designated client IP addresses, ensuring secure interaction with critical AI capabilities or business logic. This ensures that while APIPark facilitates easy integration of 100+ AI models and prompt encapsulation into REST API, the access to these powerful capabilities remains strictly controlled and secure, protecting against unauthorized use and potential data breaches. These kinds of security measures are essential for protecting the integrity and confidentiality of the services managed by an API gateway, particularly when dealing with sensitive AI models or proprietary business APIs.
The "Real" Difference: Nuance and Perception
Having delved into the intricacies of both IP whitelisting and IP allowlisting, it becomes clear that the "real" difference between the two is not functional but primarily semantic and perceptual. From a purely technical standpoint, they describe the exact same access control mechanism: an explicit list of permitted IP addresses, with all other unlisted addresses being implicitly denied access. The bits and bytes flow, or are blocked, in precisely the same manner, regardless of whether the list is called a "whitelist" or an "allowlist." The core principle of "default deny" remains immutable under both terminologies.
So, if they are functionally identical, why does the distinction matter, and why has the industry seen a gradual, yet significant, shift towards "allowlisting"? The importance of this distinction lies in several key areas:
- Clarity in Communication: In a globalized technology industry, where teams are diverse and often geographically dispersed, precise and unambiguous language is paramount. The term "allowlist" explicitly describes the action being taken – "to allow" – which leaves little room for misinterpretation. Unlike "whitelist," which is a noun/adjective that implies a category, "allowlist" often functions as a verb or a noun derived from an action, making its intent more direct and actionable. This enhances clarity, reduces ambiguity, and minimizes the potential for misunderstandings in technical documentation, security policies, and day-to-day operations. When dealing with complex API gateway configurations or intricate API access rules, clear language can prevent costly errors.
- Avoiding Exclusionary Language: Perhaps the most significant driver behind the shift is the industry's increasing awareness of the need for inclusive language. Terms like "whitelist" and "blacklist" carry historical baggage and problematic connotations related to racial discrimination. While their origins in technology were likely innocuous, tied to the simple concepts of "permitted" and "forbidden" categories, their association with color can be alienating and perpetuate unconscious biases. By adopting neutral terms like "allowlist" and "blocklist," the tech industry demonstrates a commitment to fostering a more inclusive and respectful environment for all professionals, irrespective of their background. This is not just about political correctness; it's about creating a culture where language promotes understanding and belonging.
- Future-Proofing and Modernization: The adoption of "allowlist" signals an organization's embrace of modern cybersecurity lexicon and best practices. It aligns with broader industry efforts to standardize terminology that is not only technically accurate but also socially responsible. For newer systems, cloud-native architectures, and open-source projects, "allowlist" is rapidly becoming the preferred term. This helps in future-proofing documentation, code, and training materials, ensuring they remain relevant and universally understood as the industry evolves. When organizations like Eolink, through their open-source AI gateway and API management platform APIPark, use "allowlist" in their official communications and product features, it reflects this forward-thinking approach.
- Consistency in Documentation and Policy: For large enterprises with extensive IT infrastructure and a multitude of security policies, consistency in terminology is crucial. It ensures that everyone, from network engineers to application developers and security analysts, is speaking the same language when discussing access controls. This consistency reduces confusion, streamlines training, and ensures that security policies are interpreted and implemented uniformly across the organization, whether for a traditional firewall or an advanced API gateway protecting a suite of APIs.
It is vital to reiterate that the "difference" does not introduce any new security vulnerabilities or benefits in terms of how access is technically controlled. The robustness of the security derived from allowlisting (or whitelisting) remains entirely dependent on its diligent implementation and management. An IP address on an "allowlist" that is compromised poses the exact same risk as one on a "whitelist." The shift is about clarity of intent and social responsibility in communication, not about a fundamental change in cryptographic strength or network protocol.
Regardless of whether one uses the traditional "whitelist" or the modern "allowlist," certain best practices are universally applicable and absolutely critical for effective access control:
- Principle of Least Privilege: This is paramount. Only allow the absolute minimum necessary IP addresses to access a resource. Every additional IP on the list represents an expansion of the attack surface. For example, an API gateway should only allow IP addresses from specific, authorized client applications to access a particular API, rather than opening it up to broad corporate network ranges unless absolutely necessary.
- Regular Review and Audit: IP lists are not static artifacts. Network configurations change, applications are deployed, partners come and go, and remote employees change their home networks. These lists must be regularly reviewed, audited, and updated to reflect the current operational landscape. Outdated entries can create security holes or cause legitimate access failures.
- Dynamic IP Management Considerations: For scenarios involving dynamic IP addresses (e.g., remote workers, cloud functions with variable egress IPs), relying solely on static IP allowlisting can be problematic. In such cases, organizations often employ VPNs (Virtual Private Networks) or implement more sophisticated identity-based access control (RBAC, ABAC) mechanisms, sometimes integrated directly into an API gateway, to manage access dynamically. For instance, an employee accessing a sensitive internal API via APIPark might connect through a VPN, whose gateway IP is allowlisted, and then further authenticate using multifactor authentication.
- Layered Security Approach: IP allowlisting is a powerful first line of defense, but it should never be the only line. It must be integrated into a comprehensive, multi-layered security strategy. This includes strong authentication (MFA), authorization, encryption (TLS/SSL), Web Application Firewalls (WAFs), intrusion detection/prevention systems (IDS/IPS), and continuous security monitoring. Even if an attacker gains access through an allowlisted IP, these subsequent layers should prevent them from causing significant damage.
- Comprehensive Documentation: Meticulous documentation of all allowed IP addresses, their justifications, associated systems, and review schedules is essential. This ensures accountability, facilitates troubleshooting, and aids in compliance. Clear documentation helps articulate the security posture enforced by an API gateway or any other controlled access point.
- Monitoring and Alerting: Implement robust monitoring and alerting for any attempts to bypass or probe the allowlist, as well as for suspicious activity originating from allowlisted IPs. Anomalous behavior from a seemingly trusted source could indicate a compromise.
When managing access to a myriad of services, especially those involving AI models or complex REST APIs, the role of an API gateway becomes paramount. Platforms like APIPark, an open-source AI gateway and API management platform, offer robust capabilities for defining precise access policies. These policies often incorporate IP allowlisting to ensure that only authorized applications or environments can interact with critical backend services, integrating seamlessly with features like authentication and comprehensive lifecycle management. With APIPark's ability to quickly integrate 100+ AI models and encapsulate prompts into REST API, the need for stringent access control via IP allowlisting becomes even more critical. Such a gateway ensures that while the power of AI and diverse APIs is harnessed, access remains secure, controlled, and traceable, preventing unauthorized invocation and potential data breaches, a feature APIPark directly supports through its approval processes and detailed logging. This holistic approach, combining a powerful API gateway with well-defined access controls like IP allowlisting, creates a secure and efficient ecosystem for managing modern digital services.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
Comparative Overview: IP Whitelisting vs. IP Allowlisting
To succinctly summarize the discussed points, the following table provides a comparative overview of IP Whitelisting and IP Allowlisting across various attributes. This allows for a quick visual understanding of their similarities and the key areas of divergence.
| Feature / Attribute | IP Whitelisting | IP Allowlisting |
|---|---|---|
| Primary Function | Explicitly permits access for listed IPs, implicitly denies all others. | Explicitly permits access for listed IPs, implicitly denies all others. |
| Core Principle | Default Deny (Permit by Exception) | Default Deny (Permit by Exception) |
| Functional Outcome | Identical: Only specified IPs can access. | Identical: Only specified IPs can access. |
| Terminology Origin | Traditional, historical usage, often associated with physical "lists." | Modern, emerging usage, driven by clarity and inclusivity. |
| Connotation | Can carry problematic historical or social connotations related to "white" as privileged/good. | Neutral, action-oriented, and inclusive, focusing on "allowing" access. |
| Modern Adoption Trend | Still prevalent in legacy systems and older documentation. | Rapidly becoming the preferred and standard terminology in new systems, cloud, and open-source projects. |
| Clarity in Communication | Generally clear, but less precise than "allowlist" in its verb form. | More precise and direct in describing the action (to allow). |
| Social Implication | Can be seen as culturally insensitive or exclusionary by some. | Designed to be neutral, inclusive, and socially responsible. |
| Security Impact | Strong security posture by reducing attack surface. | Strong security posture by reducing attack surface. |
| Maintenance Complexity | High for dynamic environments, prone to human error. | High for dynamic environments, prone to human error. |
| Examples of Use | Firewall rules, network access control lists, server access restrictions, API gateway rules (legacy terminology). | Cloud security groups, modern API management platforms, microservice access policies, API gateway rules (modern terminology). |
This table clearly illustrates that while the underlying technical mechanism and security benefits are identical, the distinction between "whitelisting" and "allowlisting" is predominantly linguistic and reflects a conscious evolution in industry best practices for communication and inclusivity.
Broader Context: Beyond IPs to a Holistic Security View
While the discussion so far has meticulously focused on IP allowlisting versus whitelisting, it's crucial to understand that these concepts are not isolated to network addresses alone. The underlying principle of explicit permission and implicit denial extends far beyond mere IP addresses and forms a foundational cornerstone of robust cybersecurity across numerous domains. This broader application underscores the universality and timeless relevance of the "default deny" posture, emphasizing its indispensable role in building truly resilient digital defenses.
One of the most common applications of this principle outside of IP addresses is application allowlisting (often referred to as application whitelisting). Instead of allowing access based on IP, this mechanism controls which software applications or executables are permitted to run on an endpoint, server, or entire network. For example, a corporate workstation might be configured to only allow a specific list of approved productivity software (e.g., Microsoft Office, Google Chrome, internal business applications). Any attempt to execute an unlisted program, whether it's malware, unauthorized software, or a malicious script, is automatically blocked. This is an incredibly powerful defense against malware, ransomware, and insider threats, as it inherently prevents the execution of unknown or malicious code, effectively stopping many attacks at the earliest possible stage. Similarly, in server environments, only approved system utilities and application binaries would be allowlisted, drastically reducing the attack surface.
Another widely adopted application is email allowlisting. This is a common feature in spam filters and email security gateways. Users or administrators can define a list of trusted email senders or domains. Emails originating from these allowlisted sources are then permitted to bypass certain spam checks or are immediately delivered to the inbox, while emails from unlisted sources are subjected to more rigorous scrutiny, quarantined, or outright rejected. This helps ensure that critical communications from known contacts are never inadvertently blocked by aggressive spam filters. However, it also highlights a potential weakness: if an allowlisted sender's account is compromised, malicious emails from that source could easily bypass defenses.
URL allowlisting (or web content allowlisting) is frequently employed in web browsers, network proxies, and content filters. In educational institutions or corporate environments, administrators might configure web proxies to only allow access to a predefined list of approved websites or domains. All other websites are then blocked. This serves both security purposes (preventing access to malicious sites) and productivity purposes (restricting access to non-work-related content). Similarly, in an application's internal configuration, it might only be allowed to make outbound connections to specific, allowlisted external API endpoints or cloud services, preventing it from exfiltrating data to unauthorized destinations.
The principle is consistently applied: in each case, a specific set of entities (IPs, applications, email addresses, URLs) is explicitly granted permission, and everything else is implicitly denied. This proactive, permission-based approach is inherently more secure than a reactive, denial-based approach (where one tries to block every known bad entity). The sheer volume of constantly evolving threats makes the latter an unsustainable strategy.
In the context of modern infrastructure, these diverse allowlisting mechanisms converge to form a holistic security posture. An organization might have IP allowlisting at its network perimeter firewall, application allowlisting on its servers, email allowlisting in its mail gateway, and URL allowlisting in its web proxies. Moreover, within its application architecture, specifically around API management, the same principles are applied. A robust API management system, sitting behind a powerful API gateway, orchestrates many such controls, ensuring consistent policy enforcement across all exposed APIs.
Consider a scenario where a corporate client application needs to access a set of sensitive APIs hosted on a cloud platform. The security layers might look like this: 1. Network Perimeter: The cloud environment's network security groups or firewalls utilize IP allowlisting to permit incoming connections only from the corporate VPN gateway IP addresses. 2. API Gateway: The API gateway (e.g., APIPark) further refines this access. It might employ IP allowlisting to ensure that only client applications originating from specific development environments or partner networks can even attempt to authenticate. Beyond IP, it would then enforce strong authentication (e.g., OAuth, API keys) and authorization (RBAC/ABAC) to control access to specific API endpoints based on the authenticated user's or application's identity. 3. Application Servers: The backend application servers hosting the APIs might have application allowlisting enabled to ensure only approved server-side processes and dependencies are running. 4. Database Servers: The database connected to the APIs might have its own IP allowlisting, only accepting connections from the API application servers.
This multi-layered, synergistic approach dramatically reduces the overall attack surface and provides defense-in-depth. If one layer of defense is bypassed or compromised, subsequent layers are still in place to prevent a full breach. The common thread throughout all these layers is the explicit permission model inherent in allowlisting. By understanding and consistently applying this principle across all facets of IT and cybersecurity, organizations can build far more resilient and secure environments, effectively protecting their valuable digital assets, whether they are sensitive data, critical business logic, or the innovative APIs that drive modern applications.
Conclusion: Clarifying the Path to Secure Access
In the intricate tapestry of modern cybersecurity, where every connection point and access request represents a potential vulnerability, understanding the nuances of access control mechanisms is paramount. Our extensive journey through IP whitelisting and IP allowlisting has revealed a fundamental truth: technically and functionally, they are two sides of the same coin. Both mechanisms steadfastly adhere to the "default deny" principle, creating an explicit list of permissible IP addresses while implicitly rejecting all others. The security outcome – a fortified perimeter that only allows known, trusted entities – is identical, irrespective of the term used.
However, the "real" difference, subtle yet significant, lies in the evolution of language within the technology industry. The shift from "whitelisting" to "allowlisting" is not a mere rebranding effort; it is a conscious and deliberate move towards greater clarity, precision, and inclusivity in our technical lexicon. "Allowlisting" offers a more action-oriented, neutral term that avoids potentially problematic historical connotations, fostering a more respectful and universally understood communication environment for global teams. This linguistic evolution is part of a broader industry trend to refine terminology, ensuring that our language not only accurately describes technical processes but also aligns with contemporary social values.
Ultimately, whether an organization chooses to employ the traditional "whitelist" or the increasingly preferred "allowlist," the underlying security principle and the best practices for its implementation remain unchanged. The efficacy of either mechanism hinges entirely on its diligent and meticulous management. Adherence to the principle of least privilege, regular auditing and updates, consideration for dynamic IP environments, robust documentation, and a commitment to a layered security approach are universally critical for creating a truly resilient defense. IP access control is a powerful initial barrier, but it must always be integrated within a comprehensive security framework that includes strong authentication, authorization, and continuous monitoring.
In today's complex digital ecosystems, where vast numbers of APIs power everything from mobile apps to AI services, the role of an API gateway as a central enforcement point for these access controls cannot be overstated. Platforms like APIPark, an open-source AI gateway and API management platform, exemplify how modern infrastructure effectively implements these policies. By providing robust features for managing API lifecycle, integrating diverse AI models, and securing API invocation, APIPark helps organizations apply IP allowlisting and other security measures consistently across their entire API portfolio. Such a powerful gateway ensures that while innovation flourishes through accessible APIs, access remains strictly governed, predictable, and protected.
In conclusion, while the debate between IP whitelisting and IP allowlisting may appear semantic, it underscores a crucial evolution in how we communicate about and implement cybersecurity. By embracing clearer, more inclusive language while steadfastly upholding the rigorous application of access controls, organizations can build not only more secure digital assets but also foster a more coherent and responsible technological future. The path to secure access is paved not just with advanced technology, but also with precise language and unwavering commitment to best practices.
Frequently Asked Questions (FAQs)
1. What is the primary functional difference between IP whitelisting and IP allowlisting? There is no functional difference. Both IP whitelisting and IP allowlisting refer to the exact same technical mechanism: creating an explicit list of IP addresses that are permitted to access a specific resource, while all other IP addresses not on that list are implicitly denied access. The core principle of "default deny" applies equally to both.
2. Why did the terminology shift from "whitelisting" to "allowlisting"? The shift in terminology is primarily driven by a desire for more inclusive and neutral language within the tech industry. Terms like "whitelist" and "blacklist" can carry problematic historical and social connotations related to race. "Allowlist" is seen as a more objective, action-oriented, and less biased term that explicitly describes the function of permitting access, fostering clearer communication and a more respectful professional environment.
3. Is IP allowlisting a more secure method than IP whitelisting? No, from a security standpoint, one is not inherently more secure than the other. Their functional security implementation is identical. The strength of the security provided depends entirely on how rigorously the list is maintained, the principle of least privilege is applied, and how it is integrated into a multi-layered security strategy, rather than the term used to describe it.
4. What are the main challenges in managing an IP allowlist? The main challenges include rigidity, maintenance overhead, and scalability issues. In dynamic environments (e.g., cloud deployments, remote workforces with changing IPs), keeping the allowlist accurate and up-to-date can be time-consuming and prone to human error. There's also the risk of "false negatives" (blocking legitimate access) or, conversely, a security breach if an allowlisted IP becomes compromised.
5. How does an API gateway utilize IP allowlisting? An API gateway acts as a crucial enforcement point for IP allowlisting. It can be configured to only accept requests for specific APIs or services from a predefined list of trusted client IP addresses or networks. This ensures that only authorized applications, partners, or internal systems can even attempt to access the APIs managed by the gateway, significantly reducing the attack surface and enhancing overall API security before requests are routed to backend services. Platforms like APIPark, an open-source AI gateway and API management platform, often provide robust features for implementing such granular IP access controls.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.