Murmur Hash 2 Online Generator: Instant & Accurate

In the vast and ever-expanding universe of digital information, where petabytes of data traverse networks at lightning speed and complex systems operate across myriad servers, the humble hash function plays an unsung yet absolutely critical role. It is the silent workhorse behind numerous fundamental operations, from ensuring data integrity to optimizing system performance. Among the pantheon of hash functions, Murmur Hash 2 stands out as a highly efficient, non-cryptographic algorithm designed for speed and excellent distribution properties. Its utility in modern computing environments, particularly where data volume is immense and processing speed is paramount, cannot be overstated.
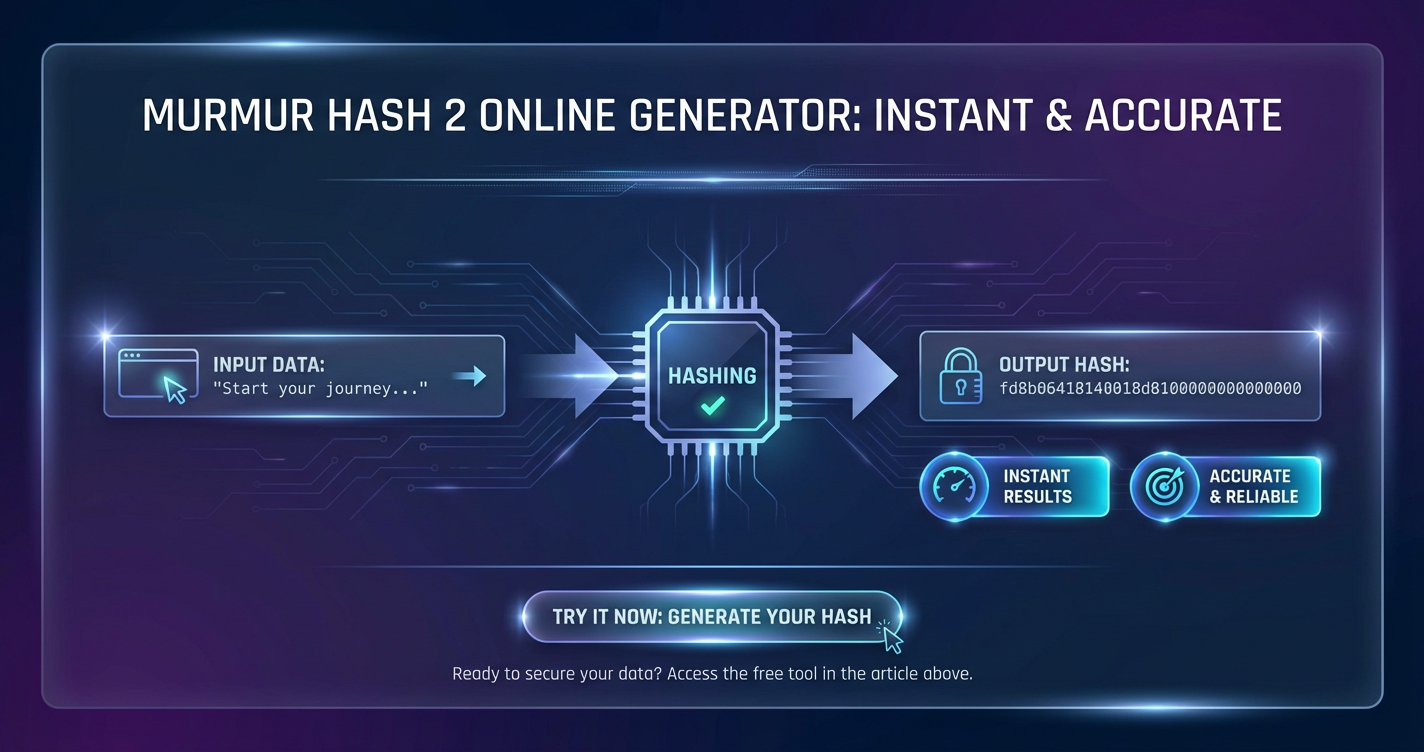
This comprehensive exploration delves into the intricacies of Murmur Hash 2, dissecting its technical underpinnings, myriad applications, and the profound convenience offered by online generators that provide "instant & accurate" results. We will journey through the foundational principles of hashing, understand why Murmur Hash 2 carved out its niche, examine the operational mechanics of web-based tools, and ultimately appreciate how these generators empower developers and data professionals alike. The article will also venture into the broader ecosystem of data management, touching upon the significance of APIs and gateways in orchestrating complex digital services, and how sophisticated platforms like APIPark contribute to this landscape. By the end, readers will possess a profound understanding of Murmur Hash 2's significance and the indispensable value of readily available, precise online tools.
The Essence of Hashing: A Foundational Concept in Digital Data Management
At its core, hashing is a process of transforming any given input data, irrespective of its size or type, into a fixed-size string of characters, typically a number or a hexadecimal value, known as a hash value, hash code, digest, or simply a hash. This transformation is performed by a mathematical algorithm called a hash function. The concept itself might seem abstract, but its applications are ubiquitous, underpinning much of the digital infrastructure we interact with daily. From the seemingly simple act of storing files on a computer to the complex distributed systems that power global networks, hashing is silently at work, ensuring order, efficiency, and integrity.
The fundamental appeal of hash functions lies in several key properties. Firstly, they are deterministic: for a given input, a hash function will always produce the exact same output hash value, every single time. This unwavering consistency is paramount for their reliability. Secondly, hash values are typically fixed in length, regardless of the input data's size. Whether you hash a single character or a multi-gigabyte file, the resulting hash will have a predetermined length, making it incredibly useful for indexing and comparison. Thirdly, an ideal hash function exhibits what is known as the "avalanche effect": even a tiny change in the input data, such as altering a single bit, should result in a drastically different hash value. This property makes hashes highly sensitive to modifications, an essential characteristic for detecting data corruption or tampering. Finally, hash functions are generally designed to be one-way; it should be computationally infeasible to reverse the process and reconstruct the original input data solely from its hash value. This one-way property is particularly crucial in cryptographic hashing but is a desirable trait even in non-cryptographic contexts to prevent trivial reconstruction.
However, no hash function is perfect, and a critical concept in hashing is "collision." A collision occurs when two different input values produce the same hash output. While an ideal hash function would avoid collisions entirely, in reality, they are theoretically unavoidable due to the pigeonhole principle (mapping an infinite number of inputs to a finite number of outputs). The goal, therefore, is to minimize the probability of collisions and ensure that finding collisions is computationally difficult, especially in cryptographic contexts. The acceptable collision rate varies drastically depending on the hash function's purpose.
Hash functions broadly fall into two main categories: cryptographic hashes and non-cryptographic hashes. Cryptographic hash functions, such as SHA-256 or SHA-3, are designed with strong security guarantees against collision attacks and preimage attacks (reconstructing input from hash). They are vital for applications like digital signatures, password storage, and blockchain technology, where security against malicious adversaries is paramount. These functions are typically slower due to their complexity and robust design.
In contrast, non-cryptographic hash functions, which include algorithms like Murmur Hash 2, FNV, and CRC32, prioritize speed and good distribution over cryptographic security. They are engineered to produce unique-enough hash values rapidly, making them suitable for tasks where the likelihood of malicious input is low or irrelevant, and the primary concern is efficient data organization and retrieval. Their speed allows for quick processing of large datasets, making them invaluable for optimizing performance in various computing scenarios. While they may be more susceptible to collisions than their cryptographic counterparts, they are still designed to distribute keys evenly across a hash table, minimizing clustering and maximizing search efficiency. Understanding this distinction is crucial for selecting the appropriate hash function for any given task, ensuring both efficiency and security where needed.
Murmur Hash 2: A Deep Dive into its Genesis and Design Philosophy
Murmur Hash, a family of non-cryptographic hash functions, was conceived by Austin Appleby with a primary focus on speed and high-quality distribution of hash values. The name "Murmur" itself is derived from "multiply and rotate," reflecting the core operations at the heart of the algorithm. Murmur Hash 2, specifically, emerged as a significant improvement over its predecessor, Murmur Hash 1, offering enhanced performance and better distribution characteristics, particularly for small keys. While Murmur Hash 3 later succeeded it, refining some aspects and introducing new variants, Murmur Hash 2 remains a widely adopted and respected algorithm due to its simplicity, efficiency, and proven track record in various real-world systems.
The design philosophy behind Murmur Hash 2 is rooted in balancing computational efficiency with excellent statistical properties for non-cryptographic use cases. Appleby aimed to create a hash function that was fast enough for high-throughput applications while still generating hashes that were uniformly distributed and exhibited a strong "avalanche effect." The avalanche effect, as mentioned earlier, is the desirable property where a minor change in the input (even a single bit flip) leads to a drastically different output hash. This characteristic is vital for minimizing collisions and ensuring that hash tables perform efficiently. A hash function lacking a good avalanche effect would tend to cluster similar inputs into similar hash values, leading to increased collision rates and degraded performance in hash-based data structures.
Murmur Hash 2 achieves its impressive performance and distribution through a series of carefully chosen bitwise operations: multiplications, XORs (exclusive OR), and rotations. These operations are computationally inexpensive and can be efficiently executed by modern CPUs, leveraging their pipelines and cache architectures. The algorithm typically processes input data in fixed-size blocks (commonly 4 bytes for the 32-bit version, or 8 bytes for the 64-bit variant), mixing them progressively into an accumulating hash value.
Let's break down the conceptual technical walkthrough of the Murmur Hash 2 algorithm (specifically the 32-bit version, often referred to as MurmurHash2_32):
- Initialization (Seed): The process begins with a
seedvalue, which is an arbitrary 32-bit integer. The seed serves as an initial state for the hash calculation. Using different seeds for the same input will produce different hash values. This is incredibly useful for creating multiple, independent hash functions from the same algorithm, which can be beneficial in applications like Bloom filters or distributing data across multiple independent partitions. Theseedis initialized into the main hash variable,h. - Processing in Blocks: The input data is read in blocks of 4 bytes (for the 32-bit version). For each 4-byte block:
- The 4 bytes are interpreted as a 32-bit integer, let's call it
k. kis then multiplied by a fixed constant,m(a large prime number, e.g.,0x5bd1e995). This multiplication helps to spread out the bits and introduce non-linearity.- The result is XORed with the current hash
h.h = h ^ k. This combines the block's influence with the accumulated hash. his then multiplied by the same constantmagain:h = h * m. This second multiplication further scrambles the bits and contributes to the avalanche effect.
- The 4 bytes are interpreted as a 32-bit integer, let's call it
- Handling Remaining Bytes (Tail): After processing all full 4-byte blocks, there might be a "tail" of fewer than 4 bytes remaining if the input data's length is not a multiple of 4. These remaining bytes are processed individually, typically byte by byte, using a sequence of XORs and multiplications to fold them into the
hvalue. The specific order and operations ensure that every bit of the input contributes to the final hash, regardless of its position. For example, a single remaining byteb1might be XORed withh, and thenhis multiplied bym. If two bytes (b1,b2) remain,b1might be XORed, thenb2is XORed after being shifted, and thenhis multiplied bym, and so on. - Finalization Mix: Once all input bytes have been processed, a final mixing step is applied to the accumulated hash
h. This step is crucial for thoroughly spreading the bits throughout the 32-bit hash value, ensuring that any remaining patterns or biases from the block processing are eliminated, and a strong avalanche effect is maintained. The finalization typically involves a series of XORs with right-shifted versions ofh, followed by multiplications:h ^= h >> 13;(XOR with right-shiftedh)h *= m;(Multiplication by the constantm)h ^= h >> 15;(Another XOR with right-shiftedh)
These operations are carefully chosen to ensure that MurmurHash2_32 provides excellent statistical randomness for its output hashes. It avoids common pitfalls of simpler hash functions, such as poor distribution for inputs with many leading zeros or common byte patterns. The algorithm's optimization for modern CPUs, combined with its strong distribution properties, has solidified its position as a go-to choice for non-cryptographic hashing in high-performance applications. The existence of 32-bit and 64-bit variants allows developers to select the appropriate hash size based on their specific needs for collision resistance and performance.
The Indispensable Role of Online Generators
In an era defined by rapid development cycles and the pervasive need for quick, reliable data processing, online generators for algorithms like Murmur Hash 2 have become indispensable tools. These web-based utilities provide immediate access to complex hashing functionality without the overhead of local software installation, compilation, or coding. Their accessibility and convenience have transformed how developers, system administrators, data analysts, and even curious individuals interact with hashing algorithms.
One of the most significant advantages of an online Murmur Hash 2 generator is its accessibility. Anyone with an internet connection and a web browser can instantly use the tool. This eliminates the need to set up a specific development environment, install programming languages or libraries, or even possess advanced coding skills. For a developer who just needs to quickly check a hash value, or a system administrator validating data across different systems, this "zero-setup" approach saves precious time and effort. It democratizes access to sophisticated algorithms, making them available to a broader audience beyond seasoned programmers.
Convenience is another cornerstone of their appeal. Imagine a scenario where you're debugging a distributed system that relies on Murmur Hash 2 for load balancing. You might need to quickly generate a hash for a specific key to predict which server it should be routed to, or to verify if a generated hash matches an expected value. An online generator provides a seamless, ad-hoc solution for such tasks. It's a virtual workbench for quick calculations, hash validations, and cross-referencing, allowing users to stay focused on their primary task rather than getting bogged down in tool setup.
Furthermore, these generators offer cross-platform compatibility. Since they operate entirely within a web browser, they are agnostic to the user's operating system. Whether you're on Windows, macOS, Linux, or even a mobile device, the functionality remains consistent. This universal access is particularly beneficial in diverse development teams or environments where standardizing local tooling might be challenging.
Beyond immediate utility, online generators also serve as valuable educational tools. For those learning about hashing algorithms, an interactive online generator provides a tangible way to experiment. Users can input different strings, observe the avalanche effect by changing a single character, or understand the impact of the seed value on the final hash. This hands-on experience demystifies the algorithm and reinforces theoretical knowledge, making complex concepts more approachable and understandable.
In essence, online Murmur Hash 2 generators bridge the gap between complex algorithms and practical, everyday use. They transform a powerful but potentially intimidating piece of code into an approachable, user-friendly service. For quick checks, validations, or even as an aid for understanding, these tools stand as a testament to the power of accessible web-based utilities, streamlining workflows and empowering users to harness the efficiency of hashing without any unnecessary friction. They make it effortless to perform tasks that would otherwise require diving into code or setting up specific environments, thus accelerating development, debugging, and data management processes across the board.
Unpacking "Instant & Accurate": The Dual Promise of Online Generators
The allure of online Murmur Hash 2 generators, particularly for those operating in fast-paced data environments, can be encapsulated by their dual promise: "Instant & Accurate." These aren't just marketing buzzwords; they represent fundamental operational advantages that significantly impact productivity, reliability, and the overall efficiency of digital workflows. Understanding what each of these terms truly signifies reveals the profound value these tools bring to the table.
The "Instant" Advantage: Speed, Efficiency, and Real-time Feedback
"Instant" refers to the remarkable speed with which these generators process input and deliver results. In a world where milliseconds can make a difference in user experience and system performance, immediate feedback is not just a luxury but often a necessity. The instant nature of online Murmur Hash 2 generators stems from several factors:
- Speed of Computation: Murmur Hash 2 itself is designed for speed. When implemented correctly in a web application (whether client-side JavaScript or server-side compiled code), the algorithm executes remarkably fast. Modern web technologies, coupled with highly optimized underlying code, can compute hash values for even moderately sized inputs in fractions of a second. This efficiency is paramount when dealing with potentially thousands of such operations in a distributed system or rapid prototyping environment.
- Elimination of Setup Time: As previously discussed, the biggest time-saver is the complete absence of any setup phase. There's no software to download, no dependencies to install, no code to write or compile. The moment you open the web page, the tool is ready to use. This "instant-on" capability is a game-changer for ad-hoc tasks, preventing context switching and keeping the user focused on the problem at hand.
- Real-time Feedback: Many online generators provide a dynamic user interface where the hash value updates in real-time as you type or paste input. This immediate visual feedback is invaluable for experimentation, debugging, and quickly understanding how changes in input affect the hash. It allows for rapid iteration and validation, fostering a more interactive and efficient workflow.
- Optimized Infrastructure: Reputable online generators are often hosted on robust server infrastructures or leverage efficient client-side JavaScript implementations. This ensures that the computational overhead is minimal and the service remains responsive even under moderate load, delivering that instant response consistently.
The cumulative effect of these factors means that users can obtain the Murmur Hash 2 value for any given input almost instantaneously. This speed is critical for tasks like quickly verifying data integrity after a transfer, cross-referencing hash values generated by different systems, or rapidly testing different keys for a hashing-based load balancer.
The "Accurate" Promise: Reliability, Consistency, and Error Reduction
"Accurate" speaks to the reliability and correctness of the hash values produced by these online tools. Accuracy is non-negotiable when dealing with hashes, as even a single incorrect bit can lead to severe data integrity issues, system failures, or misrouted requests in distributed systems. The accuracy of online Murmur Hash 2 generators is built upon:
- Determinism of the Algorithm: At its heart, Murmur Hash 2 is a deterministic algorithm. For any identical input and seed, it must produce the exact same hash value. An accurate online generator simply provides a faithful implementation of this deterministic algorithm, ensuring that its output is always consistent with the official specification.
- Reliability of Implementation: Trustworthy online generators use thoroughly tested and vetted implementations of Murmur Hash 2. These implementations adhere strictly to the algorithm's specification, often leveraging established libraries or highly optimized code that has been validated against known test vectors. This minimizes the risk of subtle bugs or deviations from the standard.
- Validation and Cross-checking: For developers, an online generator serves as an excellent tool for validation. If a system or application generates a Murmur Hash 2 locally, the online tool can be used to quickly cross-check and ensure that the local implementation is producing correct results. This is particularly useful during development and debugging phases, helping to catch discrepancies early.
- Preventing Human Error: Manually calculating hash values or relying on custom, untested scripts introduces a significant risk of human error. Typos, incorrect algorithm logic, or overlooked details can lead to erroneous hashes. An accurate online generator eliminates these human factors, providing a reliable, automated calculation that reduces the potential for mistakes.
- Impact on Data Integrity and Consistency: In applications where Murmur Hash 2 is used for data integrity checks (for non-sensitive data), caching keys, or load balancing, accuracy is paramount. An inaccurate hash can lead to corrupted data being accepted, cache misses, or requests being directed to the wrong server, causing cascading failures. The accurate output from online tools helps maintain the consistency and integrity of these critical systems.
In conclusion, the combination of "instant" feedback and "accurate" results makes online Murmur Hash 2 generators exceptionally powerful. They are not merely conveniences but essential components in the toolkit of anyone who interacts with data at scale. They streamline validation processes, minimize potential errors, and provide a rapid, reliable means to leverage one of the most efficient non-cryptographic hash functions available, ultimately contributing to more robust and performant digital infrastructures.
Behind the Scenes: How a Murmur Hash 2 Online Generator Works
Understanding the operational mechanics of an online Murmur Hash 2 generator reveals the interplay between web technologies and algorithmic computation. While the user experience is often straightforward—input data, get hash—the underlying process involves careful consideration of performance, security, and user interaction.
The core of any online generator is the implementation of the Murmur Hash 2 algorithm itself. This implementation can reside either on the client side (within the user's web browser) or on the server side (on a remote server).
Client-side Processing: Many modern online hash generators leverage JavaScript to perform the hashing directly within the user's browser. * Advantages: * Reduced Server Load: Hashing computations are offloaded to the client's machine, reducing the computational burden on the server. This allows the generator to scale more easily without requiring significant server resources. * Enhanced Privacy: For sensitive (though non-cryptographic) data, processing on the client side means the input string never leaves the user's browser and isn't transmitted over the internet to a third-party server. This can be a significant privacy benefit. * Instantaneous Feedback: Because there's no network latency involved in sending data to a server and waiting for a response, client-side processing can offer genuinely instantaneous hash generation as the user types. * Disadvantages: * Browser Performance Variability: The speed of computation can depend on the user's browser and device capabilities. Older browsers or less powerful devices might experience slower performance. * JavaScript Limitations: While JavaScript implementations are highly optimized, they might not always achieve the absolute raw speed of native C/C++ implementations running on a server. * Complexity for Large Files: Hashing extremely large files entirely in the browser can consume significant memory and processing power, potentially leading to browser slowdowns or crashes.
Server-side Processing: Alternatively, the user's input can be sent to a server, where the hashing computation is performed, and the result is then sent back to the browser. * Advantages: * Consistent Performance: Server-side implementations often use highly optimized languages (like C, C++, Go, Java, Python with native extensions) and run on powerful server hardware, ensuring consistent and often superior performance regardless of the client's device. * Centralized Control and Security: The server owner has full control over the hashing logic, making it easier to maintain, update, and potentially integrate with other backend services. * Handling Large Files: Servers are better equipped to handle very large file uploads for hashing, as they typically have more memory and processing capacity. * Disadvantages: * Network Latency: There's an inherent delay in sending the input to the server and receiving the hash back, which means the process isn't truly "instantaneous" in the same way client-side processing can be. * Increased Server Load: Each request consumes server resources, which can become a bottleneck under high traffic. * Privacy Concerns: The input data must be transmitted to the server, which might raise privacy concerns for some users, even if the data itself is non-sensitive in the context of Murmur Hash 2.
Regardless of where the computation takes place, the input handling is crucial. Most generators provide a simple text area where users can type or paste strings. Some advanced tools might also offer file upload capabilities for hashing entire files. A critical consideration here is character encoding. The hash value for the string "hello" can be different if it's interpreted as UTF-8 versus ASCII, for instance. A robust generator will clearly state its default encoding (UTF-8 is common for web contexts) or provide options for users to select different encodings, ensuring the hash matches expectations.
The seed input is another important feature. As discussed, the Murmur Hash 2 algorithm starts with a seed. While many online generators default to a common seed (e.g., 0 or a fixed constant), providing an input field for the user to specify a custom seed allows for greater flexibility and reproducibility, particularly when mimicking specific system behaviors or using the hash for multi-part distribution schemes.
Finally, the output display must be clear and intuitive. Murmur Hash 2 typically produces a 32-bit or 64-bit integer, which is almost universally displayed in hexadecimal format (e.g., 0x1234ABCD). Some generators might also offer decimal or binary representations. Essential user interface elements include "copy to clipboard" buttons for easy transfer of the hash value and a "clear/reset" button to quickly prepare for a new input.
In summary, an online Murmur Hash 2 generator is more than just an algorithm; it's a carefully crafted web application that optimizes for user experience, performance, and accuracy, balancing client-side and server-side strengths to deliver a seamless and reliable hashing utility.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
Practical Applications of Murmur Hash 2 in the Digital Ecosystem
Murmur Hash 2, with its unique blend of speed and good hash distribution, has found a broad spectrum of practical applications across various facets of the digital ecosystem. Its non-cryptographic nature means it's unsuitable for security-sensitive tasks like password hashing or digital signatures, but where efficiency and even data spread are paramount, it excels. Let's delve into some of its most impactful use cases.
Load Balancing
In distributed systems, load balancing is crucial for efficiently distributing incoming network traffic across a group of backend servers. The goal is to maximize throughput, minimize response time, and avoid overloading any single server. Murmur Hash 2 plays a significant role here, particularly in consistent hashing schemes. By hashing an identifier for a request (e.g., a user ID, a session ID, or a URL) using Murmur Hash 2, and then mapping that hash to a specific server, requests for the same identifier can be consistently routed to the same server. This reduces cache misses and improves efficiency, as session-specific data can reside on a single machine. The excellent distribution of Murmur Hash 2 ensures that requests are spread evenly across the available servers, preventing hot spots and optimizing resource utilization.
Caching Systems
Caching is a fundamental technique to improve the performance of applications by storing frequently accessed data in a faster, more accessible location. In systems like Memcached, Redis, or local application caches, Murmur Hash 2 is frequently used to generate keys for cache entries. When a piece of data needs to be stored or retrieved from the cache, its identifier is hashed to produce a cache key. The speed of Murmur Hash 2 ensures that key generation adds minimal overhead to the caching process, while its good distribution reduces hash collisions within the cache, which could otherwise lead to performance degradation or incorrect data retrieval. For instance, a web page's URL might be hashed to serve as its cache key.
Distributed Hash Tables (DHTs)
DHTs are a class of decentralized distributed systems that provide a lookup service similar to a hash table. They are designed to scale to extremely large numbers of nodes and to handle node arrivals, departures, and failures. Examples include BitTorrent's DHT, Apache Cassandra, and DynamoDB. Murmur Hash 2 (or similar non-cryptographic hashes) is used to map "keys" (data identifiers) to "nodes" (servers or peers) in the network. The hash value determines which node is responsible for storing or retrieving a particular piece of data. Its efficiency and excellent distribution properties are vital for ensuring that data is evenly distributed across the nodes and that lookups are fast and reliable in these massive, dynamic systems.
Data Deduplication
In large storage systems, backups, or content delivery networks, identifying and eliminating duplicate copies of data (deduplication) can save significant storage space and bandwidth. Murmur Hash 2 can be used to generate fingerprints (hash values) for data blocks or entire files. By comparing these hash values, systems can quickly identify identical blocks of data without needing to perform a byte-by-byte comparison, which is computationally expensive. If two blocks have the same Murmur Hash 2 value, they are highly likely to be identical. While a collision could theoretically lead to false negatives (missing a duplicate), the low probability of Murmur Hash 2 collisions for non-adversarial data makes it an effective and fast approach for this purpose.
Bloom Filters
Bloom filters are probabilistic data structures that can quickly test whether an element is a member of a set. They are space-efficient but have a non-zero false positive rate (i.e., they might incorrectly indicate that an element is in the set when it's not, but never a false negative). Murmur Hash 2 is perfectly suited for Bloom filters because they require multiple, independent hash functions to map an element to several positions in a bit array. By using different seeds with Murmur Hash 2, multiple distinct hash values can be generated for the same input, fulfilling this requirement efficiently and ensuring good distribution within the filter's bit array. This is commonly used in databases to check if a row exists before performing a costly disk read, or in web browsers to check if a URL is malicious.
Fingerprinting for Quick Identification
Beyond deduplication, Murmur Hash 2 can serve as a quick "fingerprint" for data blocks, files, or even network packets. This fingerprint allows systems to rapidly identify if a piece of data has changed or if it matches a known pattern without having to analyze the entire content. For instance, in real-time streaming data processing, a Murmur Hash 2 of a data record might be used to detect changes or track unique entities efficiently.
Uniqueness Checks
When dealing with large datasets, it's often necessary to quickly determine if an item is unique or if it has been encountered before. Rather than storing the full item or performing complex lookups, storing and comparing Murmur Hash 2 values can provide a very fast approximation for uniqueness. While collisions mean it's not a perfect guarantee of uniqueness (unless combined with other checks), it's highly effective for probabilistic uniqueness checks where speed is critical.
Checksums (Non-Cryptographic)
For verifying data integrity during transmission or storage, especially for non-sensitive data where malicious tampering is not a primary concern, Murmur Hash 2 can be used as a fast checksum. If a file is transmitted and its Murmur Hash 2 value matches the original, it's highly probable that the data arrived uncorrupted due to accidental errors. It's a faster alternative to cryptographic hashes for this purpose but provides no protection against deliberate manipulation.
To put these applications into perspective, consider the following table which contrasts Murmur Hash 2 with other common hash algorithms and their typical use cases:
| Hash Algorithm | Primary Characteristics | Typical Use Cases |
|---|---|---|
| Murmur Hash 2 | Fast, good distribution, non-cryptographic | Caching (key generation), load balancing (consistent hashing), Bloom filters, data deduplication, distributed hash tables, general-purpose hash table indexing. |
| FNV Hash | Simple, fast, non-cryptographic, good for small keys | Hash table indexing, checksums, generating unique IDs where high collision resistance is not critical, text processing. |
| SipHash | Fast, cryptographically strong against collisions for short messages, keyed, non-cryptographic (designed for non-adversarial but potentially untrusted input) | Protecting hash tables against denial-of-service (DoS) attacks (hash flooding), message authentication codes (MACs) for short messages, network protocols requiring keyed authentication. |
| CRC32 | Very fast, excellent for detecting accidental bit errors, poor for malicious changes | Data integrity check for network protocols (Ethernet, ZIP archives, JPEG files), storage error detection, ensuring data hasn't been corrupted during transmission or storage due to random noise. |
| MD5 | Cryptographic (but broken for security purposes), fast for cryptographic hashes | File integrity verification (legacy, still used where security isn't paramount or historical compatibility is needed), digital forensics (identifying files), unique content IDs. Not recommended for security-sensitive applications due to known collision vulnerabilities. |
| SHA-256 | Cryptographic, strong collision resistance, slower than non-cryptographic hashes | Digital signatures, blockchain technology (mining, transaction verification), password hashing (when combined with salt and stretching), SSL/TLS certificates, software integrity verification. |
This table clearly illustrates why Murmur Hash 2 holds such an important place. It fills the crucial gap for applications demanding speed and good distribution without the overhead of cryptographic strength, making it an efficiency powerhouse in the vast digital landscape.
The "API" and "Gateway" Nexus in Modern Data Processing
In the increasingly interconnected world of digital services, the concepts of an Application Programming Interface (API) and an API Gateway are not merely technical jargon; they are foundational pillars enabling the creation, deployment, and management of complex, scalable, and secure applications. Understanding their interplay is critical to appreciating modern data processing architectures, from microservices to AI-driven platforms.
The Power of APIs: Building Blocks of Interoperability
An API acts as a contract between different software components, defining how they should interact. It specifies the methods, data formats, and protocols that developers can use to communicate with a specific software service or component. In essence, an API is a messenger that takes a request, tells a system what to do, and returns the response.
The power of APIs lies in their ability to facilitate:
- Programmatic Access: APIs allow machines to communicate directly with each other, enabling automation of tasks. For instance, an online Murmur Hash 2 generator, while useful through a web interface, could expose an
apithat allows developers to integrate its hashing functionality directly into their applications. This means an application could send a string to theapi, receive the hash, and use it in its internal logic, all without human intervention. This capability is vital for building complex workflows, data pipelines, and integrating services. - Interoperability and Integration: APIs are the glue that connects disparate systems. They allow different software applications, written in different languages and running on different platforms, to communicate seamlessly. This interoperability is key to modern, modular architectures like microservices, where complex applications are broken down into smaller, independent services that interact via APIs.
- Building Blocks for Complex Applications: Developers can leverage existing APIs to build new, sophisticated applications without having to reinvent the wheel. Instead of building a hashing algorithm from scratch, a developer can simply call a Murmur Hash 2
api. This accelerates development, reduces costs, and allows developers to focus on core business logic rather than auxiliary functionalities. - Innovation and Ecosystems: APIs foster innovation by enabling third-party developers to build new products and services on top of existing platforms. Think of how social media platforms or payment
gateways open their APIs for others to integrate, creating vibrant developer ecosystems.
The Role of Gateways: Orchestrating the Digital Traffic
While APIs define how services interact, an API Gateway acts as a single entry point for all API calls to your services. It sits between the client and a collection of backend services, managing requests and responses, and performing various cross-cutting concerns. Think of it as a sophisticated traffic controller, a bouncer, and a record-keeper all rolled into one for your digital services.
API Gateways are crucial for:
- Managing API Traffic: A
gatewaycan route requests to the appropriate backend service, perform load balancing to distribute traffic efficiently, and manage caching to reduce backend load. For a highly used Murmur Hash 2 service, agatewaycould ensure that requests are directed to the least busy hashing server, maintaining responsiveness. - Security and Access Control: Gateways are the first line of defense for backend services. They can implement authentication and authorization checks (e.g., API keys, OAuth tokens), rate limiting to prevent abuse, and block malicious traffic. This protects backend services from unauthorized access and Denial of Service (DoS) attacks.
- Monitoring and Analytics: Gateways can log every API call, providing valuable data for monitoring service health, usage patterns, and troubleshooting. This detailed telemetry is essential for performance tuning and understanding how services are being consumed.
- Decoupling Clients from Services: The
gatewayabstracts the complexity of the backend services from the clients. Clients only need to know how to interact with thegateway, which then handles the internal routing and transformation logic to communicate with the actual services. This makes it easier to evolve backend services without impacting client applications. - Protocol Transformation: Gateways can translate between different protocols, allowing clients to interact with services using a consistent interface, even if the backend services use varied communication methods.
APIPark: Empowering Modern API and AI Service Management
For organizations needing robust api management, especially for complex AI and REST services, platforms like APIPark become invaluable. APIPark acts as an open-source AI gateway and api management platform, designed to simplify the management, integration, and deployment of diverse digital services.
Imagine needing to integrate a Murmur Hash 2 generation service into a larger data processing pipeline, alongside various AI models for natural language processing or image recognition. Managing these and other critical services through a robust gateway like APIPark ensures efficiency, security, and scalability.
APIPark offers several key features that address the challenges of modern api and AI service orchestration:
- Quick Integration of 100+ AI Models: It provides a unified management system for authentication and cost tracking across a multitude of AI models, making it easier to leverage advanced AI capabilities.
- Unified API Format for AI Invocation: By standardizing request data formats, APIPark ensures that changes in underlying AI models or prompts do not disrupt consuming applications, simplifying AI usage and reducing maintenance costs.
- Prompt Encapsulation into REST API: Users can combine AI models with custom prompts to quickly create new, specialized APIs (e.g., sentiment analysis, translation), further extending programmatic capabilities.
- End-to-End API Lifecycle Management: From design to publication, invocation, and decommission, APIPark assists in managing the entire lifecycle of APIs, regulating processes, handling traffic forwarding, load balancing, and versioning.
- API Service Sharing within Teams: It centralizes the display of all
apiservices, fostering collaboration and making it easy for different departments to discover and utilize requiredapis. - Independent API and Access Permissions for Each Tenant: For larger enterprises or SaaS providers, APIPark allows for multi-tenancy, enabling independent applications, data, user configurations, and security policies for different teams or clients, while sharing underlying infrastructure.
- API Resource Access Requires Approval: Crucially for security, APIPark can activate subscription approval features, requiring callers to subscribe and await administrator approval before invoking an API, preventing unauthorized access and potential data breaches.
- Performance Rivaling Nginx: With impressive throughput (over 20,000 TPS on modest hardware) and support for cluster deployment, APIPark is built to handle large-scale traffic, ensuring that your services remain highly performant.
- Detailed API Call Logging and Powerful Data Analysis: Comprehensive logging records every
apicall, aiding in troubleshooting and ensuring system stability. Historical data analysis provides long-term trends and performance insights for preventive maintenance.
By offering these capabilities, APIPark transforms the complexities of managing diverse apis and AI services into a streamlined, secure, and scalable operation. It provides the essential gateway functionality that allows organizations to confidently expose and consume services, including foundational utilities like efficient hashing, within a robust, controlled, and performant ecosystem. This integration of apis and gateways is not just a technical enhancement; it is a strategic imperative for any enterprise striving for digital excellence and innovation.
Security and Performance Considerations for Murmur Hash 2
While Murmur Hash 2 is celebrated for its speed and excellent distribution properties, it is imperative to understand its limitations, particularly concerning security and how its performance characteristics translate into real-world applications. Misunderstanding these aspects can lead to critical vulnerabilities or suboptimal system design.
Security: A Non-Cryptographic Hash by Design
The most crucial security consideration for Murmur Hash 2 is that it is explicitly designed as a non-cryptographic hash function. This distinction is not merely academic; it has profound implications for its appropriate use:
- Vulnerability to Collision Attacks: Unlike cryptographic hash functions (e.g., SHA-256), Murmur Hash 2 is not resistant to collision attacks. An attacker can, with relative ease, craft different input messages that produce the same Murmur Hash 2 output. This is a fundamental characteristic of its design, prioritizing speed over cryptographic strength. If an attacker can deliberately cause collisions, they can potentially disrupt systems that rely on the uniqueness of Murmur Hash 2 values.
- No Preimage Resistance: Murmur Hash 2 is also not designed to be preimage resistant. This means it's not infeasible to find an input that hashes to a given output (a "preimage attack"), or to find a different input that produces the same hash as a given input (a "second preimage attack"). These properties are essential for cryptographic security, ensuring that an attacker cannot reverse a hash or create a malicious input that mimics a legitimate one.
When NOT to Use Murmur Hash 2 (for security-sensitive contexts):
- Password Hashing: Never use Murmur Hash 2 for storing or verifying passwords. Its susceptibility to collision and preimage attacks means an attacker could easily generate fake passwords that match legitimate hashes or find a password from its hash. Dedicated, slow, and cryptographically secure hashing functions like bcrypt, scrypt, or Argon2 should always be used for password storage.
- Digital Signatures and Authentication: Murmur Hash 2 cannot be used to create digital signatures or to authenticate the integrity of sensitive data. If an attacker can forge a document with the same hash, they can bypass integrity checks. For this, cryptographic hashes are mandatory.
- Data Integrity for Sensitive Information: While Murmur Hash 2 can detect accidental data corruption, it offers no protection against malicious tampering. If the integrity of sensitive financial records, medical data, or classified information needs to be guaranteed against an adversary, a cryptographic hash must be employed.
- Cryptographic Key Derivation: Never use Murmur Hash 2 as part of any process to derive cryptographic keys.
When Murmur Hash 2 IS Safe and Appropriate:
Murmur Hash 2 is perfectly safe and highly effective in non-adversarial contexts where the primary concerns are speed, good distribution, and detecting accidental data variations, not protection against deliberate attacks. This includes the applications discussed earlier:
- Caching Keys: An attacker generating a collision in a cache key is generally not a security threat, but rather an efficiency issue (cache misses).
- Load Balancing and Distributed Hash Tables: Collisions here might cause minor load imbalances or misrouting, but usually not security breaches.
- Bloom Filters: The probabilistic nature of Bloom filters already accounts for false positives, making Murmur Hash 2 suitable.
- Data Deduplication: While a collision could theoretically lead to misidentifying unique data as duplicate, this is an integrity risk, not typically a security vulnerability against a malicious actor crafting data.
- General Hash Table Indexing: The occasional collision is handled by the hash table's collision resolution strategy and doesn't expose sensitive information.
For online generators specifically, browser security (HTTPS for encrypted communication) and input sanitization (to prevent injection attacks) are general web security practices that should be adhered to, regardless of the hashing algorithm used. The choice of Murmur Hash 2 does not inherently make an online generator less secure if used for its intended purpose.
Performance: Optimized for Speed and Efficiency
Performance is Murmur Hash 2's raison d'être. It was designed from the ground up to be one of the fastest non-cryptographic hash functions available, offering significant speed advantages over cryptographic alternatives while maintaining excellent statistical properties for hash distribution.
- Benchmarking and Comparison: In benchmarks, Murmur Hash 2 consistently outperforms cryptographic hashes like SHA-256 by orders of magnitude (e.g., 10x to 100x faster), and even often surpasses other non-cryptographic hashes like FNV or CRC32 in terms of combined speed and distribution quality for a wide range of input sizes. This makes it ideal for high-throughput scenarios where millions or billions of hash computations are required.
- Factors Affecting Speed:
- CPU Architecture: Murmur Hash 2 leverages basic bitwise operations, multiplications, and rotations that are highly optimized in modern CPU instruction sets. It's designed to minimize pipeline stalls and maximize parallelism within the CPU.
- Data Alignment: The algorithm performs best when operating on naturally aligned data blocks (e.g., 4-byte or 8-byte boundaries). Unaligned access can incur performance penalties, though modern CPUs often handle this efficiently.
- Cache Performance: The algorithm's sequential processing of input data and its use of small, fixed-size constants allow it to exhibit good cache locality, minimizing costly memory access delays.
- Implementation Language: While the algorithm itself is fast, the efficiency of its implementation (e.g., native C/C++ versus a purely JavaScript implementation) can also impact real-world performance. Highly optimized libraries or client-side JavaScript JIT compilers can achieve impressive speeds.
- Efficiency Gains: The raw speed of Murmur Hash 2 translates into tangible efficiency gains across various systems. Faster hashing means:
- Lower Latency: Quicker lookups in hash tables, faster key generation for caches.
- Higher Throughput: More data can be processed per unit of time in distributed systems, load balancers, and deduplication pipelines.
- Reduced Resource Consumption: Less CPU time spent on hashing means more resources available for core application logic, leading to lower operational costs.
When using an optimized online Murmur Hash 2 generator, users benefit from an implementation that has likely been fine-tuned for performance. This contrasts sharply with a naive, unoptimized custom implementation that might miss subtle architectural efficiencies, highlighting the value of using a well-engineered tool.
In essence, while Murmur Hash 2 sacrifices cryptographic security for speed, it does so with purpose. Its performance makes it an indispensable tool for non-security-critical applications demanding rapid, well-distributed hashing. Understanding this security-performance trade-off is paramount for making informed architectural decisions in any data-intensive application.
Advanced Features and Future Trends in Hashing
As digital infrastructure continues to evolve, the demands on hashing tools also grow. While a basic online Murmur Hash 2 generator provides fundamental utility, more advanced features are emerging to cater to complex workflows, and the future of hashing itself is a dynamic field of research and development.
Advanced Features in Online Hashing Tools
Beyond the simple input-output mechanism, sophisticated online generators or integrated development environments (IDEs) are incorporating features that enhance usability and power:
- Batch Processing Capabilities: For users needing to hash multiple strings or large lists of data points, a feature to process them in batches is invaluable. This could involve uploading a file (e.g., CSV, TXT) with one input per line and receiving a corresponding list of hash values. This dramatically improves efficiency compared to individual input entries.
- File Hashing Directly in the Browser: As modern browsers become more powerful, some advanced generators allow users to select a local file, and the hashing calculation occurs entirely client-side. This avoids the need to upload potentially large or sensitive files to a server, combining convenience with privacy. The hash is computed from the file's binary content, providing a quick integrity check.
- Integration with Development Environments (IDEs) or CLI Tools: While not strictly "online generators" in the browser sense, the concept extends to command-line interface (CLI) tools or IDE extensions that provide instant Murmur Hash 2 generation. These tools offer the same "instant & accurate" promise but within a developer's preferred coding environment, often supporting programmatic access for automation.
- Support for Multiple Hash Algorithms: A comprehensive online tool might not just offer Murmur Hash 2 but also other algorithms like FNV, CRC32, MD5, SHA-256, etc. This allows users to quickly compare hash outputs across different algorithms for the same input, aiding in algorithm selection or cross-platform compatibility checks.
- Configurable Output Formats: Beyond hexadecimal, options to output in decimal, binary, or base64 format can be useful for specific integration needs.
- API Endpoints for Programmatic Use: As discussed in the context of APIs and gateways, the most advanced "online generators" are not just web pages but also expose their functionality through a RESTful API. This allows other applications, scripts, or services to programmatically invoke the hashing function, making it a reusable microservice component. This is where a platform like APIPark would be instrumental in managing access, traffic, and security for such a hashing
api.
Future Trends in Hashing
The field of hashing is continuously evolving, driven by new computing paradigms, increased data volumes, and emerging security threats:
- New Algorithms for Specific Needs: While Murmur Hash 2 remains relevant, research continues into new non-cryptographic hash functions tailored for specific workloads. For example, some hashes are optimized for very short keys, others for specific CPU architectures (e.g., SIMD instructions), and others, like SipHash, offer stronger protection against hash flooding DoS attacks while remaining fast.
- Hardware-Accelerated Hashing: Modern CPUs are increasingly incorporating hardware instructions to accelerate cryptographic hash functions (e.g., SHA extensions on x86 CPUs). This trend may extend to non-cryptographic hashes, further boosting their performance and making them even more efficient at the chip level.
- Hashing in Serverless and Edge Computing: The rise of serverless functions (e.g., AWS Lambda, Azure Functions) and edge computing environments means that hashing needs to be performed efficiently and rapidly in highly distributed, ephemeral contexts. Optimized, lightweight hashing implementations will be crucial for these architectures.
- Post-Quantum Hashing (Cryptographic Context): While not directly impacting Murmur Hash 2, the broader field of hashing, particularly cryptographic hashing, is grappling with the advent of quantum computing. Researchers are developing "post-quantum" cryptographic hashes designed to resist attacks from quantum computers. This will influence the entire cryptographic landscape, potentially leading to new best practices and algorithm recommendations, even if Murmur Hash 2's role remains unchanged for non-cryptographic tasks.
- Machine Learning for Hash Function Design (Research Area): There's nascent research into using machine learning techniques to design or optimize hash functions. While still highly experimental, this could lead to new algorithms that are exceptionally well-suited for specific data distributions or performance targets.
In conclusion, the journey of hashing from theoretical concept to indispensable tool continues. Online Murmur Hash 2 generators, in their current form, offer remarkable utility, but the future promises even more sophisticated tools and algorithms, driven by the relentless march of technological innovation and the ever-increasing demands of the digital world. The core principles of speed, good distribution, and accuracy will, however, remain central to their enduring value.
Conclusion
In the intricate tapestry of digital infrastructure, Murmur Hash 2 stands as a testament to the power of elegantly designed algorithms that prioritize efficiency and distribution. This deep dive has explored its foundational role, tracing its genesis as a fast, non-cryptographic hash and dissecting the mechanics that enable its widespread adoption. From generating unique keys in caching systems to orchestrating load balancing in distributed architectures, Murmur Hash 2 is a quiet workhorse, ensuring data integrity for non-sensitive data and optimizing performance across countless applications.
The advent of online Murmur Hash 2 generators has democratized access to this powerful algorithm, embodying the dual promise of "instant & accurate" results. These web-based tools eliminate barriers to entry, offering unparalleled convenience for developers, system administrators, and data professionals who require quick validations, ad-hoc calculations, or educational insights. By abstracting away the complexities of implementation, they empower users to leverage advanced hashing capabilities with minimal effort, saving invaluable time and reducing the potential for human error. Whether processing input on the client-side for privacy or on robust servers for consistent performance, these generators are critical components in today's rapid development cycles.
Furthermore, we've contextualized Murmur Hash 2 within the broader framework of modern data processing, highlighting the indispensable roles of APIs and gateways. APIs serve as the language of interoperability, enabling systems to communicate programmatically and forming the building blocks of complex applications. API gateways, in turn, act as intelligent traffic controllers, orchestrating api requests, enforcing security, and providing crucial monitoring capabilities. In this intricate ecosystem, platforms like APIPark emerge as vital solutions, offering an open-source AI gateway and api management platform that simplifies the integration, deployment, and secure management of diverse AI and REST services. Such a platform ensures that even fundamental tools like Murmur Hash 2, when exposed as a service, can be managed with enterprise-grade efficiency, security, and scalability within a comprehensive digital strategy.
While acknowledging Murmur Hash 2's non-cryptographic nature and its unsuitability for security-sensitive applications, its performance advantages for speed-critical tasks remain unparalleled. This careful balance of trade-offs defines its utility and ensures its continued relevance. As digital landscapes evolve, with new trends in batch processing, API-driven architectures, and advanced security considerations, the foundational principles that Murmur Hash 2 embodies — efficiency, reliability, and good data distribution — will continue to underpin the development of future hashing innovations. In a world awash with data, the ability to instantly and accurately process it with tools like Murmur Hash 2 online generators remains an indispensable asset, driving efficiency and robustness in every corner of the digital realm.
Frequently Asked Questions (FAQ)
1. What is Murmur Hash 2 and how is it different from other hash functions? Murmur Hash 2 is a fast, non-cryptographic hash function designed for excellent distribution of hash values and high performance. It was created to generate hash codes quickly and efficiently, making it ideal for tasks where speed is more critical than cryptographic security. Unlike cryptographic hashes (e.g., SHA-256), Murmur Hash 2 is not resistant to malicious collision attacks and should not be used for security-sensitive applications like password storage or digital signatures. Its unique design uses a series of multiplications, XORs, and rotations to achieve a strong avalanche effect and uniform distribution, ensuring minimal collisions in non-adversarial contexts.
2. Why should I use an online Murmur Hash 2 generator instead of writing my own code? Online Murmur Hash 2 generators offer unparalleled convenience and speed. They eliminate the need for software installation, coding, or environment setup, allowing you to get an "instant & accurate" hash value with just a web browser. This is ideal for quick validations, ad-hoc checks, debugging, or learning about the algorithm without any overhead. While writing your own code offers ultimate control, an online generator provides immediate, reliable results without consuming development time, leveraging pre-optimized and thoroughly tested implementations.
3. What are the common use cases for Murmur Hash 2? Murmur Hash 2 is widely used in applications where speed and good data distribution are paramount, and cryptographic security is not a primary concern. Common use cases include: * Caching systems: Generating keys for cache entries (e.g., Memcached, Redis). * Load balancing: Distributing requests evenly across servers in distributed systems. * Distributed Hash Tables (DHTs): Mapping data to nodes in large-scale decentralized systems. * Data deduplication: Identifying duplicate data blocks quickly. * Bloom filters: As a component for probabilistic membership testing. * Non-cryptographic checksums: Verifying data integrity against accidental corruption.
4. Can Murmur Hash 2 be used for security purposes like password hashing? Absolutely NOT. Murmur Hash 2 is a non-cryptographic hash function and is fundamentally unsuitable for security-sensitive applications like password hashing, digital signatures, or protecting sensitive data from malicious tampering. It is vulnerable to collision attacks, meaning an attacker can easily find different inputs that produce the same hash, or even reconstruct inputs from hashes. For security-critical tasks, always use robust cryptographic hash functions specifically designed for those purposes, such as bcrypt, scrypt, Argon2 (for passwords), or SHA-256/SHA-3 (for integrity/signatures).
5. How does an API gateway like APIPark relate to hashing tools or general data processing? An API gateway, such as APIPark, plays a crucial role in modern data processing by acting as a single entry point for all API traffic, managing and securing the communication between client applications and backend services. If an organization develops a robust Murmur Hash 2 service that needs to be exposed as an api for internal or external applications, APIPark can manage this service. It would handle api authentication, rate limiting, traffic routing (e.g., to multiple hashing servers), load balancing, and detailed logging of api calls. This ensures that even fundamental utilities like hashing are delivered efficiently, securely, and scalably within a comprehensive api management framework, especially when integrated into broader AI or data processing pipelines. APIPark centralizes the entire API lifecycle, from development to operations, making it easier to integrate and manage a diverse set of services.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.