OpenAPI: Your Guide to Getting JSON from Requests
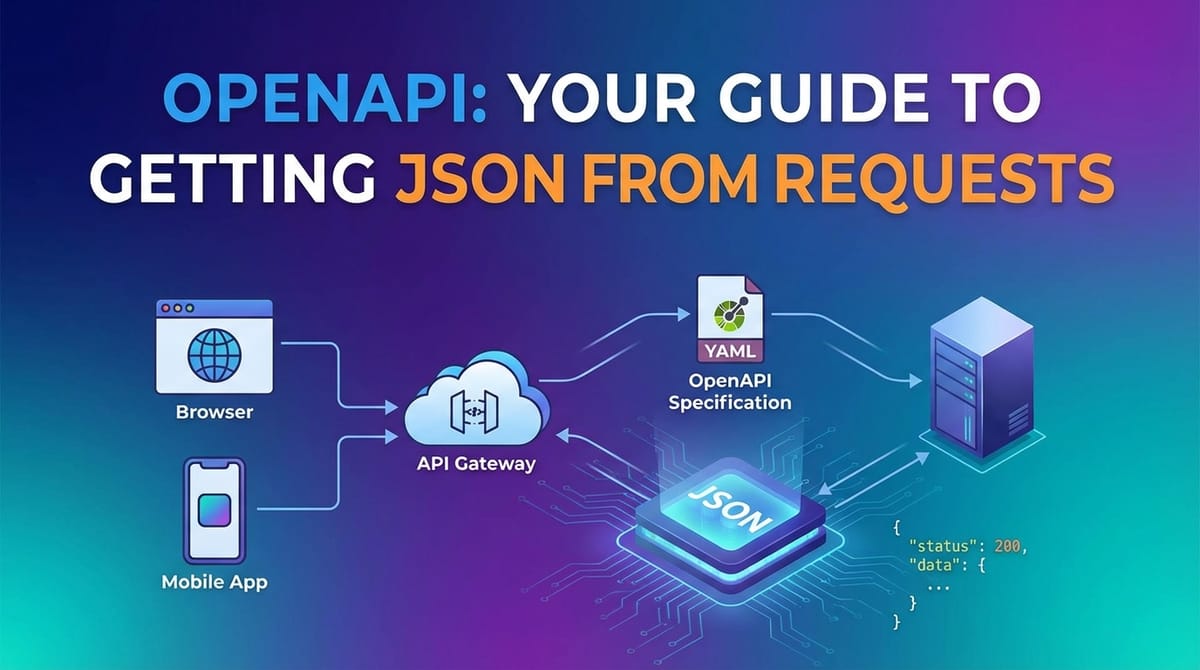
In the intricate tapestry of modern digital ecosystems, data flows relentlessly, connecting applications, services, and users across an ever-expanding network. At the heart of this dynamic interaction lie Application Programming Interfaces (APIs), the unsung heroes that enable disparate software components to communicate and exchange information seamlessly. As the digital world continues to evolve, the ability to effectively interact with these APIs, particularly to retrieve and process data formatted as JSON (JavaScript Object Notation), has become an indispensable skill for developers, data scientists, and system architects alike. This extensive guide will demystify the process, taking you on a journey from understanding the foundational concepts of APIs and their specifications, through the practicalities of making requests, to the nuances of extracting and utilizing JSON data. We will delve into the power of OpenAPI, explore the critical role of an API gateway, and equip you with the knowledge to master API consumption in a truly robust and efficient manner.
The Foundation: Understanding APIs and Their Digital Dialogue
Before we embark on the specifics of OpenAPI and JSON, it's crucial to solidify our understanding of what an API truly is and why it has become the bedrock of contemporary software development. At its core, an api acts as a messenger, facilitating communication between two software applications. It defines the methods and data formats that applications can use to request and exchange information. Think of it like a waiter in a restaurant: you, the client, don't go into the kitchen (the server) to prepare your meal. Instead, you tell the waiter (the API) what you want from the menu (the available operations), and the waiter conveys your order to the kitchen, retrieves your meal, and brings it back to you. The waiter also communicates any issues, like an item being unavailable. This analogy perfectly encapsulates the client-server interaction fundamental to most web APIs.
RESTful Principles: The Architectural Style of Choice
While various architectural styles exist for designing APIs, Representational State Transfer (REST) has emerged as the dominant paradigm, largely due to its simplicity, scalability, and statelessness. A RESTful api adheres to a set of principles that emphasize the use of standard HTTP methods to perform operations on resources, which are typically identified by unique Uniform Resource Locators (URLs). These principles include:
- Client-Server Architecture: A clear separation of concerns between the client and the server. Clients send requests; servers process them and return responses.
- Statelessness: Each request from a client to a server must contain all the information needed to understand the request. The server should not store any client context between requests. This enhances scalability and reliability.
- Cacheability: Responses must explicitly or implicitly define themselves as cacheable or non-cacheable to prevent clients from reusing stale or inappropriate data.
- Uniform Interface: This is the most critical constraint. It simplifies the overall system architecture by ensuring that a single, consistent way of interacting with resources is used. This includes:
- Identification of Resources: Resources are identified by URIs.
- Manipulation of Resources Through Representations: Clients manipulate resources by sending representations (e.g., JSON documents) that contain the desired state.
- Self-Descriptive Messages: Each message includes enough information to describe how to process the message.
- Hypermedia as the Engine of Application State (HATEOAS): This principle, often considered the most difficult to implement, suggests that responses should contain links to related resources, guiding the client on possible next actions.
- Layered System: A client cannot ordinarily tell whether it is connected directly to the end server, or to an intermediary along the way. This allows for intermediate servers like load balancers, proxies, and api gateway solutions to be introduced without affecting the client-server interactions.
- Code on Demand (Optional): Servers can temporarily extend or customize the functionality of a client by transferring executable code. This is the only optional constraint.
Adhering to these principles leads to a robust, scalable, and maintainable API design, making it easier for diverse clients to consume services.
HTTP Methods: The Verbs of API Communication
When a client makes a request to a RESTful API, it uses one of the standard HTTP methods, each conveying a specific intent regarding the resource. Understanding these "verbs" is fundamental to interacting with any api:
| HTTP Method | Purpose | Idempotent? | Safe? | Typical Use Cases |
|---|---|---|---|---|
| GET | Retrieve a resource or a collection of resources. | Yes | Yes | Fetching user profiles, listing products in an e-commerce store, retrieving configuration settings. A GET request should never alter the state of the server. |
| POST | Submit data to be processed to a specified resource. Often results in the creation of a new resource. | No | No | Creating a new user account, submitting a new blog post, placing an order. Multiple identical POST requests may create multiple resources or trigger multiple side effects. |
| PUT | Update an existing resource, or create a new resource if it doesn't exist at the specified URI. | Yes | No | Fully replacing a user's profile with new data, updating an entire document. If a resource exists, PUT replaces it entirely; if not, it creates it. Repeated PUT requests with the same data have the same effect as a single request. |
| DELETE | Remove a specified resource. | Yes | No | Deleting a user account, removing an item from a shopping cart, cancelling an order. Repeated DELETE requests on the same resource will result in the same state (resource no longer exists) as a single request. |
| PATCH | Apply partial modifications to a resource. | No | No | Updating only a specific field of a user's profile (e.g., changing only their email address, not their entire profile). PATCH is used when you want to modify a portion of a resource without sending the complete representation. |
| HEAD | Retrieve the headers that would be returned if the HEAD request's corresponding GET request were to be sent. | Yes | Yes | Checking if a resource exists, inspecting metadata (like Content-Type or Content-Length) without downloading the entire resource body. Useful for performance optimization or pre-flight checks. |
| OPTIONS | Describe the communication options for the target resource. | Yes | Yes | Used by clients to discover the capabilities of a server or a specific resource. Often used in Cross-Origin Resource Sharing (CORS) pre-flight requests to check what methods and headers are allowed by the server from a different origin. |
Idempotent means that making the same request multiple times will have the same effect on the server as making it once. Safe means the request does not alter the state of the server. Understanding these distinctions is crucial for designing and interacting with robust APIs.
HTTP Status Codes: The Server's Response Language
When a server responds to an API request, it includes an HTTP status code, a three-digit number that indicates the outcome of the request. These codes are categorized into five classes, providing vital feedback to the client:
- 1xx (Informational): The request was received and understood.
- 2xx (Success): The request was successfully received, understood, and accepted.
200 OK: The most common success code.201 Created: Resource successfully created (e.g., after a POST request).204 No Content: The server successfully processed the request, but is not returning any content (e.g., after a DELETE request).
- 3xx (Redirection): Further action needs to be taken by the user agent to fulfill the request.
301 Moved Permanently: The resource has been permanently moved to a new URL.302 Found: The resource has been temporarily moved.
- 4xx (Client Error): The request contains bad syntax or cannot be fulfilled.
400 Bad Request: Generic client error, often due to malformed request body or parameters.401 Unauthorized: Authentication is required and has failed or has not yet been provided.403 Forbidden: The server understood the request but refuses to authorize it.404 Not Found: The requested resource could not be found.429 Too Many Requests: The user has sent too many requests in a given amount of time (rate limiting).
- 5xx (Server Error): The server failed to fulfill an apparently valid request.
500 Internal Server Error: Generic server error.503 Service Unavailable: The server is currently unable to handle the request due to temporary overloading or maintenance.
Thoroughly checking status codes in API responses is a critical step for robust error handling and ensuring the reliability of any application consuming API data.
JSON: The Lingua Franca of Web APIs
While various data formats have been used for API communication, including XML, YAML, and Protocol Buffers, JSON (JavaScript Object Notation) has undeniably become the de facto standard for most web APIs. Its popularity stems from several key advantages:
- Lightweight and Human-Readable: JSON's syntax is simple and intuitive, making it easy for both humans to read and machines to parse. It's a text-based format, which also contributes to its lightweight nature, leading to faster data transfer.
- Language Agnostic: Although derived from JavaScript, JSON is entirely language independent. Parsers and generators for JSON exist in virtually every programming language, making it universally compatible across different technology stacks.
- Hierarchical Data Representation: JSON effectively represents complex data structures using two basic constructs:
- Objects: Unordered sets of name/value pairs, enclosed in curly braces
{}. Names are strings, and values can be strings, numbers, booleans, null, objects, or arrays. - Arrays: Ordered lists of values, enclosed in square brackets
[]. Values can be any valid JSON data type.
- Objects: Unordered sets of name/value pairs, enclosed in curly braces
- Ease of Parsing: Most programming languages provide built-in functions or readily available libraries to parse JSON strings into native data structures (e.g., dictionaries/objects, lists/arrays), making data extraction straightforward.
For example, a typical JSON response from an api fetching user data might look like this:
{
"id": "user123",
"username": "johndoe",
"email": "john.doe@example.com",
"isActive": true,
"roles": ["admin", "editor"],
"profile": {
"firstName": "John",
"lastName": "Doe",
"age": 30,
"address": {
"street": "123 Main St",
"city": "Anytown",
"zipCode": "12345"
}
},
"lastLogin": "2023-10-26T10:30:00Z"
}
This structure clearly and efficiently conveys complex information, making it ideal for API payloads.
Diving Deep into OpenAPI: The Blueprint for API Clarity
As APIs proliferate and become more complex, the need for clear, consistent, and machine-readable documentation becomes paramount. This is where OpenAPI Specification (OAS) steps in. OpenAPI is a standard, language-agnostic interface description for RESTful APIs, allowing both humans and computers to discover and understand the capabilities of a service without access to source code, documentation, or network traffic inspection. Born from the Swagger Specification, OpenAPI provides a robust framework for describing APIs in a structured JSON or YAML format.
The Evolution and Purpose of OpenAPI
The OpenAPI Specification was originally known as the Swagger Specification, created by Tony Tam at Wordnik. Its primary goal was to simplify API development and consumption by providing a universal way to describe an API's operations, parameters, authentication methods, and responses. In 2015, SmartBear Software, which maintained Swagger, donated the Swagger Specification to the Linux Foundation to create the OpenAPI Initiative (OAI). This move signaled a commitment to fostering a truly open, vendor-neutral specification, leading to its renaming as the OpenAPI Specification.
The core purpose of OpenAPI is multifaceted:
- Machine-Readability: An OpenAPI document is machine-readable, meaning tools can automatically generate documentation, client SDKs (Software Development Kits), server stubs, and even perform automated testing.
- Human-Readability: Despite being machine-readable, the structure of an OpenAPI document is intuitive enough for developers to understand the API's contract quickly.
- Consistency: It enforces a consistent way of describing APIs, which reduces ambiguity and improves interoperability across different teams and organizations.
- Collaboration: It serves as a single source of truth for API definitions, facilitating better collaboration between API designers, developers, testers, and consumers.
- API Lifecycle Management: OpenAPI plays a crucial role throughout the API lifecycle, from design and development to testing, deployment, and deprecation.
Key Components of an OpenAPI Document
An OpenAPI document, often named openapi.yaml or openapi.json, meticulously details every aspect of an API. Let's break down its essential top-level components and their significance:
openapi: Specifies the version of the OpenAPI Specification that the document adheres to (e.g.,3.0.0,3.1.0). This is crucial for parser compatibility.info: Provides metadata about the API. This includes:title: The name of the API.version: The version of the API implementation (not the OpenAPI Specification version).description: A detailed description of the API's purpose and functionality.contact: Information about the API provider.license: Licensing information for the API.
servers: An array of objects defining the base URLs for the API. This allows for defining different environments (e.g., development, staging, production) from which the API can be accessed. Each server object can include a URL and an optional description.paths: This is the core of the OpenAPI document, defining the individual endpoints (paths) and the HTTP operations (GET, POST, PUT, DELETE, etc.) available for each path. Each path item object can contain:- Path Parameters: Variables embedded directly in the URL path (e.g.,
/users/{userId}). - Operations: For each HTTP method (e.g.,
get,post), an operation object describes:summaryanddescription: Brief and detailed explanations of what the operation does.operationId: A unique string used to identify the operation.tags: Used for logical grouping of operations in documentation.parameters: An array of objects defining input parameters for the operation. These can be located in the path, query string, headers, or cookies. Each parameter specifies itsname,in(location),requiredstatus, andschemafor its data type.requestBody: Describes the payload required for POST, PUT, and PATCH operations. It specifies thecontenttype (e.g.,application/json) and theschemafor the request body's structure.responses: A map of HTTP status codes to response objects. Each response object describes the expected status code, a description, and thecontent(schema) of the response body, especially important for defining the JSON structure you expect to receive.security: References the security schemes required for this specific operation.
- Path Parameters: Variables embedded directly in the URL path (e.g.,
components: A reusable container for various API elements. This promotes modularity and reduces redundancy in the API definition. Key sub-components include:schemas: Definitions of data models (JSON schemas) used throughout the API for both request bodies and response payloads. This is where you precisely define the structure and data types of the JSON you send and receive.yaml schemas: User: type: object properties: id: type: string format: uuid username: type: string email: type: string format: email isActive: type: boolean required: - id - username - emailresponses: Reusable response definitions.parameters: Reusable parameter definitions.examples: Reusable examples for various parts of the API.requestBodies: Reusable request body definitions.headers: Reusable header definitions.securitySchemes: Defines security schemes like API Keys, OAuth2, or HTTP Basic authentication that can be referenced by operations.
security: Defines global security requirements for the entire API, which can then be overridden at the operation level.tags: Provides a list of tags used by operations, with optional external documentation. This helps in organizing large APIs in generated documentation.
The depth and precision offered by OpenAPI in defining these components ensure that any consuming application knows exactly what to expect when interacting with the API, making the process of getting JSON from requests far more predictable and manageable.
Tools for Working with OpenAPI
The OpenAPI ecosystem boasts a rich collection of tools that leverage the specification's machine-readability:
- Swagger UI: Automatically generates beautiful, interactive API documentation from an OpenAPI definition. It allows developers to visualize and interact with the API's resources without any implementation logic.
- Swagger Editor: A browser-based editor for designing and validating OpenAPI definitions. It provides instant feedback on syntax errors and best practices.
- OpenAPI Generator: A powerful command-line tool and library that generates client SDKs, server stubs, and documentation from an OpenAPI document in various languages (Java, Python, JavaScript, Go, C#, Ruby, etc.). This significantly accelerates development by providing boilerplate code tailored to the API.
- Postman/Insomnia: Popular API development environments that can import OpenAPI specifications to automatically generate collections of requests, making it easy to test and explore APIs.
- Validation Tools: Tools like
spectral(or those integrated into editors) validate OpenAPI documents against the specification and custom style guides, ensuring adherence to quality standards.
By utilizing these tools, the OpenAPI Specification transforms from a mere documentation format into a powerful enabler of API-first development, automation, and seamless integration.
The Art of Making API Requests: Initiating the Data Flow
With a solid understanding of APIs and the OpenAPI blueprint, the next step is to actually make requests to an API and retrieve data. This involves sending structured HTTP messages to a server and then processing its responses.
Anatomy of an HTTP Request
Every HTTP request, regardless of the method or the tool used, consists of several fundamental parts:
- Method: The HTTP verb (GET, POST, PUT, DELETE, etc.) indicating the desired action.
- URL (Uniform Resource Locator): The address of the resource on the server. This includes the scheme (
httporhttps), the domain, and the path to the specific resource.- Path Parameters: Parts of the URL path that identify a specific resource (e.g.,
/users/123where123is the path parameter). - Query Parameters: Key-value pairs appended to the URL after a
?(e.g.,/products?category=electronics&limit=10). Used for filtering, sorting, or pagination.
- Path Parameters: Parts of the URL path that identify a specific resource (e.g.,
- Headers: Key-value pairs that provide metadata about the request or the client. Common headers include:
Content-Type: Specifies the media type of the request body (e.g.,application/json,application/xml).Accept: Specifies the media types the client is willing to accept in the response (e.g.,application/json).Authorization: Contains credentials for authenticating the client (e.g.,Bearer <token>,Basic <base64-encoded-credentials>).User-Agent: Identifies the client software making the request.
- Body (Payload): For methods like POST, PUT, and PATCH, this section contains the data being sent to the server. For most modern APIs, this data is formatted as JSON.
Making Requests with cURL: The Command-Line Powerhouse
cURL is a ubiquitous command-line tool and library for transferring data with URLs. It's an excellent choice for quick API testing, scripting, and understanding the raw HTTP request/response flow.
GET Request Example: To retrieve a list of users from an API endpoint, you might use:
curl -X GET "https://api.example.com/v1/users?limit=5&sort=name" \
-H "Accept: application/json"
-X GET: Specifies the HTTP GET method."https://api.example.com/v1/users?limit=5&sort=name": The target URL, including query parameters.-H "Accept: application/json": Sets theAcceptheader, indicating that the client prefers a JSON response.
POST Request Example (with JSON body): To create a new user by sending JSON data:
curl -X POST "https://api.example.com/v1/users" \
-H "Content-Type: application/json" \
-H "Accept: application/json" \
-d '{
"username": "newuser",
"email": "newuser@example.com",
"password": "strongpassword123"
}'
-X POST: Specifies the HTTP POST method.-H "Content-Type: application/json": Crucially tells the server that the request body is JSON.-d '{...}': Provides the request body data. The single quotes ensure the JSON string is passed as a single argument.
API Clients: Postman and Insomnia
For more complex API interactions, especially during development and testing, graphical API clients like Postman and Insomnia are invaluable. These tools provide intuitive user interfaces to construct requests, manage environments, store authentication tokens, organize requests into collections, and inspect responses.
- Ease of Use: They offer dedicated fields for URLs, headers, body, and authentication, making it simple to construct even complex requests without memorizing
cURLsyntax. - Environment Variables: You can define variables for different environments (e.g.,
{{baseUrl}},{{apiKey}}), allowing you to switch between development, staging, and production servers easily. - Testing and Scripting: Both tools allow you to write pre-request scripts (e.g., to generate a dynamic timestamp) and post-response tests (e.g., to assert status codes or JSON payload values).
- Import/Export OpenAPI: They can import OpenAPI definitions to automatically create request collections, providing a pre-configured testing suite aligned with the API specification. This integration streamlines the entire testing workflow.
Making Requests in Programming Languages
The vast majority of real-world applications consume APIs programmatically. Here's how you might make requests and handle JSON responses in popular languages:
Python (requests library)
The requests library is the de facto standard for making HTTP requests in Python, known for its simplicity and elegance.
import requests
import json
base_url = "https://api.example.com/v1"
headers = {
"Accept": "application/json",
"Content-Type": "application/json"
}
# --- GET Request ---
try:
response = requests.get(f"{base_url}/users", headers=headers, params={"limit": 5, "sort": "name"})
response.raise_for_status() # Raises an HTTPError for bad responses (4xx or 5xx)
users_data = response.json() # Automatically parses JSON into a Python dictionary/list
print("GET Response (Users):")
for user in users_data:
print(f" ID: {user.get('id')}, Username: {user.get('username')}")
except requests.exceptions.HTTPError as err:
print(f"HTTP error occurred: {err}")
print(f"Response body: {err.response.text}")
except requests.exceptions.ConnectionError as err:
print(f"Connection error occurred: {err}")
except requests.exceptions.Timeout as err:
print(f"Timeout error occurred: {err}")
except requests.exceptions.RequestException as err:
print(f"An unexpected error occurred: {err}")
# --- POST Request ---
new_user_payload = {
"username": "python_user",
"email": "python@example.com",
"password": "securepassword"
}
try:
response = requests.post(f"{base_url}/users", headers=headers, json=new_user_payload)
response.raise_for_status()
created_user = response.json()
print("\nPOST Response (Created User):")
print(f" ID: {created_user.get('id')}, Username: {created_user.get('username')}")
except requests.exceptions.HTTPError as err:
print(f"HTTP error occurred: {err}")
print(f"Response body: {err.response.text}")
except requests.exceptions.RequestException as err:
print(f"An unexpected error occurred: {err}")
The response.json() method is incredibly convenient; it attempts to parse the response body as JSON and returns a Python dictionary or list. If the response content is not valid JSON, it will raise a ValueError.
JavaScript (fetch API and axios)
In modern JavaScript environments (browsers and Node.js), the fetch API is built-in for making network requests. axios is a popular promise-based HTTP client that simplifies fetch and adds features.
Using fetch (Browser/Node.js):
const baseUrl = "https://api.example.com/v1";
// --- GET Request ---
async function getUsers() {
try {
const response = await fetch(`${baseUrl}/users?limit=5&sort=name`, {
method: 'GET',
headers: {
'Accept': 'application/json'
}
});
if (!response.ok) {
throw new Error(`HTTP error! status: ${response.status} - ${await response.text()}`);
}
const usersData = await response.json(); // Parses JSON response
console.log('GET Response (Users):');
usersData.forEach(user => {
console.log(` ID: ${user.id}, Username: ${user.username}`);
});
} catch (error) {
console.error('Error fetching users:', error);
}
}
// --- POST Request ---
async function createUser() {
const newUserPayload = {
username: "js_user",
email: "js@example.com",
password: "anothersecurepassword"
};
try {
const response = await fetch(`${baseUrl}/users`, {
method: 'POST',
headers: {
'Content-Type': 'application/json',
'Accept': 'application/json'
},
body: JSON.stringify(newUserPayload) // Converts JS object to JSON string
});
if (!response.ok) {
throw new Error(`HTTP error! status: ${response.status} - ${await response.text()}`);
}
const createdUser = await response.json();
console.log('\nPOST Response (Created User):');
console.log(` ID: ${createdUser.id}, Username: ${createdUser.username}`);
} catch (error) {
console.error('Error creating user:', error);
}
}
getUsers();
createUser();
fetch returns a Promise that resolves to a Response object. The response.json() method is also asynchronous and returns a Promise that resolves with the parsed JSON data. JSON.stringify() is used to convert a JavaScript object into a JSON string for the request body.
Using axios (Node.js/Browser):
First, install axios: npm install axios
import axios from 'axios';
const baseUrl = "https://api.example.com/v1";
// --- GET Request ---
async function getUsersAxios() {
try {
const response = await axios.get(`${baseUrl}/users`, {
params: { limit: 5, sort: 'name' },
headers: { 'Accept': 'application/json' }
});
const usersData = response.data; // Axios automatically parses JSON into `response.data`
console.log('GET Response (Users via Axios):');
usersData.forEach(user => {
console.log(` ID: ${user.id}, Username: ${user.username}`);
});
} catch (error) {
if (error.response) {
console.error(`HTTP error! status: ${error.response.status} - ${error.response.data}`);
} else if (error.request) {
console.error('No response received:', error.request);
} else {
console.error('Error setting up request:', error.message);
}
}
}
// --- POST Request ---
async function createUserAxios() {
const newUserPayload = {
username: "axios_user",
email: "axios@example.com",
password: "supersecurepassword"
};
try {
const response = await axios.post(`${baseUrl}/users`, newUserPayload, {
headers: {
'Content-Type': 'application/json',
'Accept': 'application/json'
}
});
const createdUser = response.data;
console.log('\nPOST Response (Created User via Axios):');
console.log(` ID: ${createdUser.id}, Username: ${createdUser.username}`);
} catch (error) {
if (error.response) {
console.error(`HTTP error! status: ${error.response.status} - ${JSON.stringify(error.response.data)}`);
} else {
console.error('Error creating user with Axios:', error.message);
}
}
}
getUsersAxios();
createUserAxios();
Axios simplifies error handling and automatically transforms JSON responses, making them available directly in response.data. For POST requests, you can pass the JavaScript object directly, and Axios will automatically JSON.stringify it and set the Content-Type header.
Extracting and Working with JSON Responses: Unlocking the Data
Once an API request is successfully made and a response is received, the next crucial step is to extract and process the JSON data it contains. This involves parsing the JSON string into native data structures and then navigating these structures to access the specific pieces of information required.
Understanding JSON Structure for Effective Parsing
JSON's simplicity belies its power in representing complex hierarchical data. The two fundamental structures are:
- Objects (
{}): Collections of unordered key-value pairs. Keys are always strings (enclosed in double quotes), and values can be strings, numbers, booleans,null, another object, or an array. In most programming languages, these map directly to dictionaries, hash maps, or objects.json { "name": "Alice", "age": 30, "city": "New York" } - Arrays (
[]): Ordered lists of values. Values can be any valid JSON data type. These map directly to lists or arrays in programming languages.json [ "apple", "banana", "cherry" ]
JSON allows for nesting these structures arbitrarily, enabling the representation of highly complex datasets. For instance, a list of users, where each user has a nested address object and an array of roles, can be perfectly modeled in JSON.
Parsing JSON in Various Programming Languages
As demonstrated in the request examples, most modern languages provide straightforward mechanisms for parsing JSON.
Python
The json module is built-in. When using requests, response.json() handles parsing automatically. If you have a JSON string from another source, you'd use json.loads():
import json
json_string = '''
{
"productName": "Laptop X1",
"price": 1200.50,
"inStock": true,
"features": ["SSD", "16GB RAM", "Full HD Display"],
"dimensions": {
"weightKg": 1.8,
"heightCm": 2,
"widthCm": 35,
"depthCm": 24
},
"reviews": [
{"user": "Alice", "rating": 5, "comment": "Great laptop!"},
{"user": "Bob", "rating": 4, "comment": "Good value."}
]
}
'''
data = json.loads(json_string)
# Accessing values
print(f"Product Name: {data['productName']}")
print(f"Price: ${data['price']}")
print(f"In Stock: {data['inStock']}")
# Accessing array elements
print(f"First Feature: {data['features'][0]}")
# Accessing nested object values
print(f"Weight: {data['dimensions']['weightKg']} kg")
# Iterating through an array of objects
print("Reviews:")
for review in data['reviews']:
print(f" User: {review['user']}, Rating: {review['rating']}, Comment: '{review['comment']}'")
# Safely accessing potentially missing keys
user_email = data.get('email', 'N/A') # 'email' might not exist, provides default 'N/A'
print(f"Email (if present): {user_email}")
Python's dictionary and list access ([] and .get()) make navigating parsed JSON very natural.
JavaScript
The JSON object is global in JavaScript. For strings, use JSON.parse(). For fetch and axios, response.json() or response.data handles it.
const jsonString = `
{
"productName": "Laptop X1",
"price": 1200.50,
"inStock": true,
"features": ["SSD", "16GB RAM", "Full HD Display"],
"dimensions": {
"weightKg": 1.8,
"heightCm": 2,
"widthCm": 35,
"depthCm": 24
},
"reviews": [
{"user": "Alice", "rating": 5, "comment": "Great laptop!"},
{"user": "Bob", "rating": 4, "comment": "Good value."}
]
}
`;
const data = JSON.parse(jsonString);
// Accessing values
console.log(`Product Name: ${data.productName}`);
console.log(`Price: $${data.price}`);
console.log(`In Stock: ${data.inStock}`);
// Accessing array elements
console.log(`First Feature: ${data.features[0]}`);
// Accessing nested object values
console.log(`Weight: ${data.dimensions.weightKg} kg`);
// Iterating through an array of objects
console.log("Reviews:");
data.reviews.forEach(review => {
console.log(` User: ${review.user}, Rating: ${review.rating}, Comment: '${review.comment}'`);
});
// Safely accessing potentially missing keys (ES2020+ Optional Chaining)
const userCity = data.user?.address?.city || 'N/A';
console.log(`User City (if present): ${userCity}`);
JavaScript uses dot notation (.) for object property access and bracket notation ([]) for array elements or when property names are dynamic. Optional chaining (?.) is a modern feature for safely accessing deeply nested properties.
Java (Jackson Library Example)
Java requires external libraries for robust JSON parsing. Jackson and Gson are two popular choices. Here's an example using Jackson:
First, add Jackson dependencies to your pom.xml (Maven) or build.gradle (Gradle):
<!-- Maven -->
<dependency>
<groupId>com.fasterxml.jackson.core</groupId>
<artifactId>jackson-databind</artifactId>
<version>2.13.0</version>
</dependency>
import com.fasterxml.jackson.databind.JsonNode;
import com.fasterxml.jackson.databind.ObjectMapper;
import java.io.IOException;
public class JsonParsingExample {
public static void main(String[] args) {
String jsonString = """
{
"productName": "Laptop X1",
"price": 1200.50,
"inStock": true,
"features": ["SSD", "16GB RAM", "Full HD Display"],
"dimensions": {
"weightKg": 1.8,
"heightCm": 2,
"widthCm": 35,
"depthCm": 24
},
"reviews": [
{"user": "Alice", "rating": 5, "comment": "Great laptop!"},
{"user": "Bob", "rating": 4, "comment": "Good value."}
]
}
""";
ObjectMapper objectMapper = new ObjectMapper();
try {
JsonNode rootNode = objectMapper.readTree(jsonString);
// Accessing values
System.out.println("Product Name: " + rootNode.get("productName").asText());
System.out.println("Price: $" + rootNode.get("price").asDouble());
System.out.println("In Stock: " + rootNode.get("inStock").asBoolean());
// Accessing array elements
JsonNode features = rootNode.get("features");
if (features.isArray() && features.size() > 0) {
System.out.println("First Feature: " + features.get(0).asText());
}
// Accessing nested object values
JsonNode dimensions = rootNode.get("dimensions");
if (dimensions != null) {
System.out.println("Weight: " + dimensions.get("weightKg").asDouble() + " kg");
}
// Iterating through an array of objects
JsonNode reviews = rootNode.get("reviews");
if (reviews.isArray()) {
System.out.println("Reviews:");
for (JsonNode review : reviews) {
System.out.println(" User: " + review.get("user").asText() +
", Rating: " + review.get("rating").asInt() +
", Comment: '" + review.get("comment").asText() + "'");
}
}
// Safely accessing potentially missing keys
JsonNode nonExistent = rootNode.get("nonExistentKey");
if (nonExistent != null) {
System.out.println("This won't print.");
} else {
System.out.println("Non-existent key handled gracefully.");
}
} catch (IOException e) {
e.printStackTrace();
}
}
}
Jackson's JsonNode provides methods like get(), asText(), asInt(), asDouble(), asBoolean() to navigate the JSON tree and extract typed values. It also supports ObjectMapper.readValue() to directly map JSON to Java POJOs (Plain Old Java Objects), which is ideal for complex, well-defined JSON structures.
Error Handling and Validation of JSON Responses
While parsing JSON is often straightforward, robust applications must account for potential issues:
- Non-JSON Responses: The API might return HTML for an error page, plain text, or an empty response. Always check the
Content-Typeheader (if available) and wrap parsing intry-exceptblocks. - Malformed JSON: The JSON string might be syntactically incorrect.
json.loads()(Python),JSON.parse()(JavaScript), orobjectMapper.readTree()(Java) will throw exceptions in such cases. - Missing or Unexpected Fields: The API's response structure might change, or certain fields might be optional. Always access keys/properties defensively (e.g., Python's
.get(), JavaScript's optional chaining?., Java'sif (node != null)checks) and provide default values where appropriate. - Incorrect Data Types: A field expected to be a number might come back as a string. Validate the types of extracted data if strict type adherence is critical for your application logic.
- Empty Data: An array might be empty, or an object might contain no key-value pairs. Handle these edge cases gracefully to avoid errors.
Utilizing the schemas defined in your OpenAPI specification can be a powerful way to validate incoming JSON. Many API client libraries or data validation frameworks (like Pydantic in Python or Joi in JavaScript) can be configured with these schemas to automatically validate responses, ensuring data integrity and adherence to the API contract.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
The Role of API Gateways: Orchestrating the API Ecosystem
As APIs become the central nervous system of modern applications, managing them effectively, securely, and at scale becomes a significant challenge. This is where an api gateway steps in. An api gateway acts as a single entry point for all API calls from clients, routing requests to the appropriate backend services, and handling a multitude of cross-cutting concerns that would otherwise clutter individual microservices. It sits between the client and the collection of backend services.
Why an API Gateway is Essential in Modern Architectures
In a microservices architecture, where an application is decomposed into many small, independent services, directly exposing each service to clients would be unwieldy and introduce significant complexities. An api gateway provides a crucial abstraction layer, offering numerous benefits:
- Centralized Authentication and Authorization: Instead of each backend service implementing its own security logic, the api gateway can handle authentication (verifying client identity) and authorization (checking permissions) for all incoming requests. This simplifies security management, ensures consistent policy enforcement, and offloads backend services.
- Traffic Management and Control:
- Rate Limiting: Prevents abuse and ensures fair usage by limiting the number of requests a client can make within a specific timeframe. This protects backend services from being overwhelmed.
- Throttling: Controls the overall traffic flow to ensure system stability and performance under heavy load.
- Load Balancing: Distributes incoming API requests across multiple instances of backend services to optimize resource utilization and prevent single points of failure.
- Circuit Breaker: Prevents cascading failures in distributed systems by automatically opening the circuit to a failing service, allowing it to recover without overwhelming other services.
- Request Routing and Composition: The api gateway intelligently routes client requests to the correct backend service based on the request path, method, or other criteria. It can also compose responses from multiple backend services, allowing a single client request to retrieve data that spans several microservices.
- Caching: Caches responses from backend services to reduce latency for clients and decrease the load on backend servers, especially for frequently accessed, non-volatile data.
- Monitoring, Logging, and Analytics: Provides a centralized point for collecting logs, metrics, and analytics data on all API traffic. This offers invaluable insights into API usage, performance, errors, and potential security threats.
- Protocol Translation and Transformation: Can translate between different communication protocols (e.g., from HTTP to gRPC) and transform request/response payloads (e.g., converting XML to JSON or vice-versa) to accommodate diverse client and backend requirements.
- Version Management: Facilitates the introduction of new API versions without breaking existing clients by routing requests based on version headers or path segments, allowing for graceful deprecation strategies.
How OpenAPI Integrates with API Gateways
The OpenAPI Specification is a natural fit for api gateway solutions. Gateways can consume OpenAPI definitions to:
- Automatically Configure Routes: Parse the
pathsandserverssections to dynamically configure routing rules to backend services. - Enforce Request Validation: Use the
schemasdefined in OpenAPI to validate incoming client requests (e.g., checking if required fields are present and data types are correct) before forwarding them to backend services, providing early error detection. - Generate Documentation: Many gateways can expose their configuration, informed by OpenAPI, as interactive developer portals.
- Apply Policies: Associate specific policies (e.g., rate limits, security policies) with particular OpenAPI operations or paths.
This integration transforms the OpenAPI document from merely a descriptive artifact into an active configuration component of the API infrastructure, making the entire API lifecycle more automated and robust.
In this landscape of advanced API management, platforms like APIPark emerge as crucial tools. APIPark is an open-source AI gateway and API management platform designed to help developers and enterprises efficiently manage, integrate, and deploy both AI and traditional REST services. It offers a unified approach to API lifecycle management, enabling quick integration of over 100 AI models with standardized invocation formats, which means that changes in AI models or prompts don't necessitate application modifications, significantly reducing maintenance costs. Furthermore, APIPark empowers users to encapsulate custom prompts with AI models into new REST APIs, such as sentiment analysis or translation services, effectively transforming complex AI functionalities into easily consumable services. Its robust capabilities include end-to-end API lifecycle management, traffic forwarding, load balancing, detailed API call logging, and powerful data analysis for proactive maintenance, all while delivering performance comparable to Nginx. This makes APIPark an indispensable asset for organizations seeking to streamline their API operations, particularly those venturing into complex AI integrations, by providing centralized control over security, performance, and accessibility.
Best Practices for Robust API Consumption
Consuming APIs effectively goes beyond merely making requests and parsing JSON. It involves adopting a set of best practices that ensure the reliability, security, and maintainability of your application.
Authentication and Authorization: Securing Your Access
Accessing most production APIs requires proper authentication (proving who you are) and authorization (what you're allowed to do). Common methods include:
- API Keys: A simple token, often passed in a request header (
X-API-Key) or as a query parameter. Easy to implement but can be less secure if compromised. - HTTP Basic Authentication: Username and password sent Base64-encoded in the
Authorizationheader (Basic <base64(username:password)>). Simple but sends credentials with every request. Use only over HTTPS. - OAuth 2.0: A robust, industry-standard framework for delegated authorization. It involves obtaining an access token from an authorization server, which is then used to access protected resources on a resource server. This is more complex but offers greater security and flexibility, especially for third-party applications.
- Client Credentials Grant: For machine-to-machine communication where no user interaction is involved.
- Authorization Code Grant: For web applications where a user grants permission for the application to access their resources.
- JSON Web Tokens (JWT): A compact, URL-safe means of representing claims to be transferred between two parties. JWTs are often used as bearer tokens within OAuth 2.0 flows. They are self-contained and digitally signed, allowing the resource server to verify their authenticity and claims without needing to contact the authorization server for every request.
Always store credentials securely (e.g., environment variables, secret management services) and never hardcode them directly into your application's source code.
Rate Limiting and Idempotency: Respecting API Boundaries
- Rate Limiting: APIs often impose limits on how many requests a client can make within a certain timeframe to prevent abuse and ensure service availability for all users.
- Handling
429 Too Many Requests: Your application should be designed to gracefully handle this status code. This typically involves implementing an exponential backoff strategy, where you wait for progressively longer periods before retrying a request. - Checking Rate Limit Headers: Many APIs provide headers like
X-RateLimit-Limit,X-RateLimit-Remaining, andX-RateLimit-Resetto inform clients about their current rate limit status. Use these to proactively manage your request frequency.
- Handling
- Idempotency: An operation is idempotent if executing it multiple times produces the same result as executing it once.
GET,PUT, andDELETErequests are generally designed to be idempotent.POSTrequests are typically not idempotent (e.g., sending the same request twice might create two identical resources).- For operations that are not inherently idempotent but need to be, APIs might provide an "Idempotency-Key" header. This allows clients to retry non-idempotent operations safely; if the same key is sent within a certain timeframe, the server ensures the operation is only executed once.
Versioning APIs: Managing Evolution
APIs evolve. New features are added, old ones are deprecated, and data structures might change. Versioning ensures that changes to an API don't break existing client applications. Common versioning strategies include:
- URL Path Versioning: Incorporating the version number directly into the URL path (e.g.,
api.example.com/v1/users,api.example.com/v2/users). This is the most common and straightforward method. - Header Versioning: Including the version in a custom HTTP header (e.g.,
Accept-Version: v1). - Query Parameter Versioning: Using a query parameter to specify the version (e.g.,
api.example.com/users?version=v1). - Content Negotiation (Accept Header): Using the
Acceptheader to specify the desired media type and version (e.g.,Accept: application/vnd.example.api.v1+json).
Choose a consistent versioning strategy and communicate it clearly in your OpenAPI documentation.
Logging and Monitoring: Gaining Visibility
Effective logging and monitoring are crucial for understanding how your application interacts with APIs and for diagnosing issues quickly.
- Client-Side Logging: Log details of outgoing requests (URL, method, headers, partial body) and incoming responses (status code, headers, partial body, latency). Be cautious not to log sensitive data.
- Centralized Logging: Aggregate logs from all your application instances into a centralized logging system (e.g., ELK Stack, Splunk, Datadog) for easier searching and analysis.
- Performance Monitoring: Track metrics like API call latency, success rates, and error rates. Set up alerts for deviations from normal behavior.
- Tracing: In distributed systems, use distributed tracing tools (e.g., OpenTelemetry, Jaeger) to follow an API request through all the services it touches, providing end-to-end visibility.
Robust Error Handling Strategies: Graceful Degradation
Your application will encounter API errors. How you handle them determines its resilience.
- Check HTTP Status Codes: Always inspect the status code before attempting to parse the response body. Different
4xxand5xxcodes require different handling. - Parse Error Responses: Many APIs return structured JSON error messages (e.g.,
{"errorCode": "INVALID_INPUT", "message": "User ID is missing"}). Parse these to provide specific feedback or take corrective actions. - Retry Mechanisms: For transient errors (e.g.,
503 Service Unavailable, network timeouts), implement retry logic with exponential backoff and jitter to avoid overwhelming the server. - Circuit Breaker Pattern: For persistent service failures, implement a circuit breaker to quickly fail requests to the unhealthy service, preventing further resource waste and allowing the service to recover.
- User-Friendly Messages: Translate cryptic API error messages into understandable language for your end-users.
- Fallback Data: In cases of non-critical API failures, consider providing fallback data or a cached version of the data to maintain a degraded but functional user experience.
By diligently applying these best practices, developers can build applications that not only consume APIs effectively but also operate reliably, securely, and efficiently in dynamic production environments.
Advanced Considerations: Beyond the Basics
As your API consumption needs grow, you might encounter more sophisticated patterns and alternatives that enhance communication and data exchange.
Webhooks: Event-Driven Communication
While traditional API requests follow a pull model (client requests, server responds), webhooks enable a push model. Instead of constantly polling an API for updates, you register a URL with the API provider. When a specific event occurs (e.g., a new order is placed, a file is uploaded), the API server makes an HTTP POST request to your registered URL, notifying your application of the event.
- Benefits: Real-time updates, reduced polling overhead, more efficient resource usage.
- Challenges: Requires your application to expose an endpoint, careful security (verifying webhook signatures), and robust error handling for incoming events.
Webhooks are fundamental to building reactive, event-driven architectures.
GraphQL: A Flexible Alternative to REST
While REST APIs are excellent for resource-oriented interactions, they can sometimes lead to over-fetching (receiving more data than needed) or under-fetching (requiring multiple requests to get all necessary data). GraphQL is a query language for your API, and a runtime for fulfilling those queries with your existing data.
- Key Differences from REST:
- Single Endpoint: Typically, a GraphQL API has a single HTTP endpoint, usually
/graphql, that handles all requests. - Client-Driven Data Fetching: Clients specify exactly what data they need and in what shape, reducing over-fetching.
- Strongly Typed Schema: GraphQL APIs are defined by a strong type system, which ensures that clients only request data that exists and in the correct format.
- Hierarchical Queries: Allows fetching nested resources in a single request.
- Single Endpoint: Typically, a GraphQL API has a single HTTP endpoint, usually
- Benefits: More efficient data fetching, reduced network requests, flexible for evolving client needs.
- Drawbacks: Steeper learning curve, requires different tooling, and can be more complex to cache than traditional REST.
For complex front-end applications with varied data requirements, GraphQL can offer significant advantages.
Event-Driven APIs and Message Queues
Beyond synchronous HTTP requests, many modern distributed systems rely on asynchronous, event-driven communication. This often involves message queues (e.g., Kafka, RabbitMQ, Amazon SQS) where services publish events, and other services subscribe to those events.
- Benefits: Decoupling of services, improved scalability, resilience to individual service failures, better handling of spikes in traffic.
- Use Cases: Processing background jobs, distributing tasks, real-time data streaming, integrating heterogeneous systems.
While not directly about getting JSON from HTTP requests, understanding event-driven architectures is crucial for interacting with microservices that might expose an API for initial setup but then communicate primarily through events. The JSON data format remains a common payload for these events.
Conclusion: Mastering the Interconnected Digital Landscape
The journey through the realms of OpenAPI, API requests, and JSON data extraction reveals a sophisticated yet highly structured world that underpins nearly all modern digital services. We began by establishing the fundamental role of an api as the communicative bridge between software components, emphasizing the architectural elegance of RESTful design and the universal utility of JSON as its data format. We then delved into the profound importance of OpenAPI as a robust, machine-readable blueprint that standardizes API descriptions, fostering clarity, automation, and seamless integration across diverse development ecosystems.
The practical aspects of making requests were explored in detail, from the raw power of cURL to the intuitive interfaces of API clients like Postman and the programmatic flexibility offered by various programming languages. The process of retrieving and parsing JSON data was dissected, highlighting the techniques for navigating complex data structures and the critical need for comprehensive error handling to build resilient applications.
Furthermore, we examined the pivotal role of an api gateway as the central nervous system for managing, securing, and optimizing API traffic in complex microservices environments. Solutions like APIPark exemplify how these gateways not only streamline API lifecycle management but also bring advanced capabilities like AI model integration and high-performance traffic handling to the forefront, making them indispensable for enterprises navigating the challenges of modern API consumption and deployment.
Finally, we covered a spectrum of best practices, from robust authentication and vigilant rate limit handling to strategic API versioning and proactive monitoring, all designed to ensure that your API interactions are not just functional but also secure, scalable, and maintainable. The brief foray into advanced topics like webhooks and GraphQL underscored the ever-evolving landscape of API communication patterns.
In essence, mastering the art of getting JSON from API requests, guided by the clarity of OpenAPI and orchestrated through intelligent api gateway solutions, is more than just a technical skill; it is a fundamental competency for thriving in an increasingly interconnected digital world. By embracing these principles and tools, developers are empowered to build applications that are not only powerful and efficient but also adaptable, reliable, and poised for future innovation. The digital conversation continues, and with this guide, you are now well-equipped to be a fluent participant.
Frequently Asked Questions (FAQs)
1. What is the primary benefit of using OpenAPI Specification?
The primary benefit of using the OpenAPI Specification (OAS) is that it provides a standardized, language-agnostic, and machine-readable way to describe RESTful APIs. This enables several crucial advantages: it automatically generates interactive API documentation (e.g., Swagger UI), facilitates the generation of client SDKs and server stubs in various programming languages, allows for automated testing, and provides a single source of truth for API contracts. This consistency and automation significantly reduce development time, minimize errors, and improve collaboration between API producers and consumers.
2. How does an API Gateway enhance API security and performance?
An api gateway enhances API security and performance by acting as a centralized entry point for all API traffic. For security, it enforces authentication and authorization policies, validates requests against predefined schemas, and can detect and mitigate threats like SQL injection or DDoS attacks before they reach backend services. For performance, it optimizes traffic through features like rate limiting, throttling, load balancing across multiple service instances, and caching frequently accessed data. It also allows for efficient routing and potentially composing responses from multiple services, reducing the number of requests a client needs to make.
3. Why is JSON the preferred data format for most REST APIs?
JSON (JavaScript Object Notation) is the preferred data format for most REST APIs due to its lightweight nature, human-readability, and universal compatibility. Its simple, hierarchical structure of objects and arrays makes it easy for both developers to understand and machines to parse. Furthermore, parsers and generators for JSON are readily available in virtually every modern programming language, making it language-agnostic and seamlessly integrable across diverse technology stacks, leading to efficient data exchange and reduced development overhead.
4. What are the key differences between GET and POST requests?
The key differences between GET and POST requests lie in their purpose, idempotency, and how they handle data. A GET request is used to retrieve data from the server and should not have any side effects on the server's state; it is idempotent (multiple identical requests have the same effect as one) and safe (it doesn't change server state). Data for GET requests is typically sent via URL query parameters. A POST request is used to send data to the server, often resulting in the creation of a new resource or an update to an existing one; it is generally not idempotent (multiple identical requests might create multiple resources or trigger multiple actions) and not safe. Data for POST requests is sent in the request body, typically as JSON.
5. How can I handle errors effectively when consuming APIs?
Effective error handling when consuming APIs involves several strategies: 1. Check HTTP Status Codes: Always inspect the HTTP status code (e.g., 2xx for success, 4xx for client errors, 5xx for server errors) before attempting to process the response body. 2. Parse Error Responses: Many APIs return structured JSON error messages for 4xx and 5xx codes. Parse these to get specific error details (errorCode, message) to provide meaningful feedback or take corrective actions. 3. Implement Retry Logic: For transient errors (like 503 Service Unavailable or network timeouts), implement retry mechanisms with exponential backoff and jitter to avoid overwhelming the server. 4. Defensive Data Access: Access parsed JSON data using methods that gracefully handle missing keys or properties (e.g., Python's .get(), JavaScript's optional chaining ?.). 5. Circuit Breaker Pattern: For persistent service failures, employ a circuit breaker to quickly fail requests to the unhealthy service, preventing cascading failures and allowing the service time to recover. 6. Comprehensive Logging and Monitoring: Log all API requests and responses, especially errors, to facilitate debugging and identify recurring issues.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.