Understanding "404 Not Found" Errors in Nginx

The internet, a vast and intricate tapestry of information and services, often presents users with a curious and sometimes frustrating digital roadblock: the "404 Not Found" error. While seemingly a minor inconvenience, for website administrators, developers, and businesses, a proliferation of 404s can signal deeper issues, impacting user experience, search engine optimization (SEO), and even revenue. This is especially true in the complex landscape of modern web architectures, where powerful web servers like Nginx act as the primary gatekeepers for requests, often serving dynamic applications, static assets, and crucially, acting as an api gateway for myriad api services. Understanding the nuances of how Nginx processes requests and, subsequently, how it determines a resource to be "not found" is paramount for maintaining a healthy, performant, and reliable web presence.
Nginx, renowned for its high performance, stability, rich feature set, and low resource consumption, has become the de-facto choice for serving static content, acting as a reverse proxy, load balancer, and HTTP cache. Its architecture allows for incredibly flexible and powerful configuration, but this very flexibility can also be a source of bewilderment when things go awry, particularly when a seemingly simple request culminates in that infamous 404 status code. For systems relying on complex inter-service communication, where an api gateway might funnel requests to various microservices, each presenting its own api endpoints, a 404 can cascade into larger system failures or data inconsistencies. This comprehensive guide will meticulously unravel the intricacies of the 404 Not Found error within an Nginx environment, exploring its fundamental nature, common causes, systematic diagnostic approaches, proactive prevention strategies, and its specific relevance in the context of api management and api gateway operations. Our goal is to equip you with the knowledge to not just troubleshoot, but to build resilient Nginx configurations that minimize these frustrating digital dead ends.
The Anatomy of a 404 Not Found Error: More Than Just a Broken Link
Before delving into the specifics of Nginx, it is crucial to first establish a solid understanding of what a 404 error fundamentally represents within the broader context of the Hypertext Transfer Protocol (HTTP). HTTP status codes are three-digit integers returned by a server in response to a client's request. These codes are categorized into five classes, each indicating a distinct type of response: 1xx (Informational), 2xx (Success), 3xx (Redirection), 4xx (Client Error), and 5xx (Server Error). The 404 error falls squarely into the 4xx client error category, a distinction that carries significant meaning.
A "4xx Client Error" explicitly communicates that the problem lies with the client's request. In the case of a "404 Not Found," the server is explicitly stating that it could not find a resource corresponding to the URL provided by the client. It's not saying the server is down (that would be a 5xx error), nor is it saying the client isn't authorized to view the resource (that would be a 401 or 403 error). Instead, it's a very specific declaration: "I received your request for this specific URL, and I looked for a matching resource on my end, but I simply could not locate it." This clarity is vital for effective troubleshooting. The resource might have been moved, deleted, or perhaps the URL was mistyped or constructed incorrectly in the first place.
The implications of a 404 extend beyond a mere technicality. For the end-user, it represents a broken expectation, a dead end in their navigation. This can lead to frustration, abandonment of the site, and a negative perception of the brand or service. From an SEO perspective, persistent 404s for important pages can harm a website's ranking. Search engine crawlers interpret 404s as signs of poor site maintenance or non-existent content, potentially wasting "crawl budget" on non-existent pages and reducing the site's overall authority. While a single occasional 404 is rarely disastrous, a widespread pattern can significantly degrade a site's health metrics. Therefore, recognizing the precise nature of the 404 – that it is a client-side request issue – is the foundational step in understanding and subsequently resolving these errors within any web server environment, Nginx included.
Nginx Architecture and Request Processing Basics: The Foundation of Resource Location
To truly grasp why Nginx might return a 404, one must first appreciate how it processes incoming HTTP requests and maps them to physical files on a server or proxies them to an upstream service. Nginx's configuration is highly modular, primarily organized around server blocks and location blocks, which dictate how requests are handled based on the requested domain and URI.
At the highest level, an Nginx instance listens on specific ports for incoming connections. When a request arrives, Nginx first identifies the appropriate server block based on the listen directive and the server_name (hostname) in the request header. A single Nginx instance can host multiple websites or applications, each defined within its own server block.
Once a server block is selected, Nginx then evaluates the request URI against the various location blocks defined within that server block. location blocks are powerful tools that allow Nginx to apply different rules based on parts of the URL path. They can be defined using exact matches, prefix matches, or regular expressions, and their order and type of matching are crucial for correct request routing. For instance, a /images/ location block might serve static image files from a specific directory, while an /api/v1/ location block might proxy_pass requests to an internal api gateway or a specific backend api service.
The core directives for serving content and preventing 404s are root and alias. The root directive defines the base directory from which Nginx will search for files relative to the request URI. If root /var/www/html; is set in a server block, and a request comes in for /index.html, Nginx will look for /var/www/html/index.html. If root is specified within a location block, it applies only to that specific location, with the request URI appended to the root path.
The alias directive, on the other hand, is typically used within location blocks and allows a specific path in the URI to be replaced with a different file system path. For example, if you have location /data/ { alias /mnt/datafiles/; } and a request comes in for /data/report.pdf, Nginx will look for /mnt/datafiles/report.pdf, effectively "aliasing" the /data/ part of the URI to /mnt/datafiles/. Misunderstanding the subtle differences between root and alias is a frequent cause of 404 errors.
Another critical directive is index, which specifies the default files Nginx should look for when a directory is requested (e.g., index.html, index.php). If a request is made for /, and index index.html index.htm; is configured, Nginx will first try to serve /index.html, then /index.htm from the root directory. If none are found, a 404 might ensue unless further directives intervene.
Perhaps the most potent and often misunderstood directive for preventing and handling 404s is try_files. This directive allows Nginx to check for the existence of files or directories in a specified order and, if none are found, to perform an internal redirect to a fallback URI. For example, try_files $uri $uri/ /index.html; first checks if the exact URI exists as a file, then if it exists as a directory (appending a /), and finally, if neither is found, it internally redirects the request to /index.html. This is a cornerstone for single-page applications (SPAs) and frameworks that handle routing internally.
Finally, Nginx's role as a reverse proxy, often for an api gateway or backend api servers, introduces the proxy_pass directive. When Nginx receives a request matching a location block configured with proxy_pass, it doesn't search for local files. Instead, it forwards the request to an upstream server (e.g., proxy_pass http://backend_server;). In this scenario, a 404 originating from Nginx might mean the proxy_pass directive itself is misconfigured, or more commonly, that the upstream api server returned a 404, which Nginx then propagates back to the client. Understanding these fundamental building blocks of Nginx configuration is the bedrock upon which effective 404 troubleshooting is built.
Common Causes of 404 Errors in Nginx: Unraveling the Configuration Labyrinth
Armed with an understanding of Nginx's request processing, we can now meticulously examine the most prevalent culprits behind "404 Not Found" errors. These often stem from subtle misconfigurations that break the delicate chain of how Nginx maps a URI to a resource.
Misconfigured root or alias Directives
This is arguably the most common cause. The root directive specifies the document root for a server or location block. If root /var/www/mywebsite; is set, a request for /css/style.css will lead Nginx to look for /var/www/mywebsite/css/style.css. If /var/www/mywebsite is incorrect, or if the css folder or style.css file isn't where Nginx expects it to be relative to that root, a 404 occurs.
The alias directive, used within location blocks, is trickier. It replaces the matched part of the URI with a specified path. For example:
location /static/ {
alias /usr/share/nginx/html/static_assets/;
}
A request for /static/image.jpg would instruct Nginx to look for /usr/share/nginx/html/static_assets/image.jpg. A common mistake is using alias where root would be more appropriate, or vice-versa, or forgetting the trailing slash on the alias path when the location path has one, leading to incorrect path construction. If the alias path points to a non-existent directory, or the files aren't structured correctly within it, Nginx will report a 404.
Missing Files or Directories
This cause is deceptively simple but frequently overlooked. Sometimes, the Nginx configuration is perfectly valid, but the requested file or directory literally does not exist at the path Nginx is configured to look for. This can happen due to: * Deployment Errors: Files not correctly copied during deployment. * Deletion: Content inadvertently deleted from the server. * Case Sensitivity: Linux file systems are case-sensitive. If a file is named MyFile.html but the request is for /myfile.html, Nginx will not find it, resulting in a 404. Windows and macOS (by default) are often case-insensitive, which can mask this issue during local development, only for it to appear on a Linux-based production server. * Symbolic Link Issues: If Nginx relies on symbolic links, and the target of the link is broken or points to a non-existent path, it will lead to a 404.
Incorrect location Blocks
The logic within location blocks dictates how URIs are matched and processed. Errors here can severely impact routing: * No Matching Location: If a request URI doesn't match any defined location block, Nginx falls back to the server block's default handling (often defined by a root directive, or leading to a 404 if no default catch-all is present). * Overlapping Locations: Complex regular expression locations can overlap in unexpected ways, causing requests to be handled by the wrong block, which might not have the correct root, alias, or proxy_pass directive, leading to a 404. * Incorrect Regex: Errors in regular expressions can cause location blocks to either match too broadly or too narrowly, preventing legitimate requests from being processed correctly. For instance, forgetting to anchor regexes (^ and $) can lead to unintended matches.
try_files Directive Issues
The try_files directive is incredibly powerful but equally prone to misconfiguration: * Incorrect Order: The order of arguments in try_files matters. Nginx tries each argument in sequence. If try_files $uri /index.html; is used, and $uri is a directory, Nginx won't automatically serve index.html from that directory unless $uri/ is also specified. A common pattern is try_files $uri $uri/ /index.html; for single-page applications. * Non-existent Fallback: If the final fallback in try_files (e.g., /index.html or =404) points to a file that doesn't exist, or to a named location that doesn't exist, it will ultimately result in a 404. * Missing root: try_files relies on the root directive of its parent location or server block to resolve paths. If root is missing or incorrect, try_files cannot locate files.
Rewrite Rule Problems
Nginx's rewrite module allows for powerful URL manipulation. However, faulty rewrite rules can easily lead to 404s: * Incorrect Target: A rewrite rule might change the URI to a path that simply doesn't exist on the file system or is not handled by any other location block. * Infinite Loops: Poorly constructed rewrite rules can create redirect loops, which eventually lead to errors (though often not a 404 directly, but potentially browser errors or timeout). * Flags: Understanding flags like last, break, redirect, and permanent is crucial. last stops processing rewrite rules and restarts matching location blocks with the new URI. If the new URI still doesn't match a proper location, a 404 can occur.
Permissions Issues
While less common to directly cause a 404 (a 403 Forbidden is more typical), incorrect file or directory permissions can sometimes manifest as a 404. If the Nginx worker process does not have read permissions for a requested file or execute permissions for a directory it needs to traverse, it might report that the file "doesn't exist" rather than "access denied" depending on the underlying operating system call and Nginx's error handling. It's always prudent to check that the Nginx user (e.g., www-data or nginx) has appropriate read access to static files and execute access to directories along the path.
DNS/Proxy Caching
Sometimes, the 404 isn't an active problem but a lingering ghost. Stale DNS records pointing to an old server, or aggressive caching by an intermediate proxy server (like a CDN or even a browser's cache) can serve outdated content or attempt to access resources that have since been moved or deleted. This often requires clearing caches or waiting for DNS propagation.
API Gateway and API Specific Causes
The modern web heavily relies on apis, and Nginx often acts as an api gateway or a reverse proxy for api services. This introduces a unique set of 404 causes: * Incorrect Upstream Configuration: If Nginx is proxying requests to an api gateway or a backend api server (proxy_pass), and the upstream block is misconfigured, points to an incorrect IP/port, or the backend service is down, Nginx might not be able to connect, sometimes resulting in a 5xx error, but it can also manifest as a 404 if the backend service itself returns a 404 for the requested api endpoint. * Missing API Endpoints: The backend api service simply doesn't implement the requested api endpoint. The client might be calling /api/v1/users, but the backend only has /api/v2/customers. * Misrouted API Requests: An api gateway's primary job is to route api requests to the correct backend service. If the routing rules within Nginx (or the api gateway it proxies to) are incorrect, a request for one api might be sent to the wrong service, which then returns a 404 because it doesn't recognize that api path. * API Versioning Issues: Clients requesting an old or non-existent api version (e.g., /api/v1/products when only v2 exists) will receive a 404. * Incorrect Base Paths for API Services: The Nginx location block might be stripping or adding an incorrect path prefix before proxying to the api server, causing the api server to receive an unexpected URL. For instance, Nginx may proxy /api/users to http://backend/users, but if the backend expects http://backend/api/users, it will respond with a 404. * Authentication/Authorization Errors: While usually a 401 or 403, some poorly implemented apis might default to a 404 for unauthenticated or unauthorized access, obscuring the true problem.
Understanding these diverse causes is the first major hurdle. The next step is to systematically diagnose which of these factors is at play when a 404 rears its head.
Diagnosing 404 Errors in Nginx: A Systematic Troubleshooting Approach
When confronted with a 404, a systematic and methodical approach is crucial for efficient diagnosis. Jumping to conclusions or randomly altering configurations often exacerbates the problem. Here's a structured methodology for identifying the root cause of Nginx 404 errors:
1. Check Nginx Configuration Syntax and Logic
The very first step is to ensure your Nginx configuration is syntactically correct and logically sound. * Syntax Validation: Always use nginx -t after making any configuration changes. This command checks the configuration for syntax errors and displays the path to the main configuration file and any included files. If there are errors, Nginx will explicitly point them out. bash sudo nginx -t A successful output will typically state: nginx: the configuration file /etc/nginx/nginx.conf syntax is ok and nginx: configuration file /etc/nginx/nginx.conf test is successful. * Review Configuration Files: Carefully examine nginx.conf, sites-available (or conf.d), and any other included configuration files. Focus on the specific server block and location block that should be handling the problematic URI. * server_name: Does the server_name directive correctly match the domain being requested? * root and alias: Are the root and alias directives pointing to the correct absolute paths on the file system? Pay close attention to trailing slashes and how they interact with the URI. * location Block Matching: Does the request URI actually match the intended location block? If using regular expressions, verify their correctness. Remember that Nginx prioritizes exact matches, then regular expressions (in order of definition), then prefix matches. * try_files: Is the try_files directive configured correctly? Does it account for directories ($uri/)? Is the fallback URI (/index.html or =404) correct and accessible? * rewrite Rules: If rewrite rules are in use, trace their logic. What is the URI after the rewrite? Does that rewritten URI then correctly map to a location block or file? * proxy_pass: If Nginx is acting as a reverse proxy, is the proxy_pass directive pointing to the correct upstream server (IP address/hostname and port)? Is the upstream server itself healthy and responding?
2. Examine Nginx Logs
Nginx logs are an invaluable source of truth. They record what Nginx actually did with each request. * Access Logs (access.log): These logs record every request Nginx receives. Look for entries corresponding to the 404-generating requests. bash tail -f /var/log/nginx/access.log Key information to extract: * Client IP: Where did the request originate? * Request URI: What exact URL path was requested? This is crucial for verifying if the client is sending what you expect. * Status Code: Confirm it's indeed a 404. * Bytes Sent/Referer/User Agent: Additional context that might be useful. By comparing the requested URI in the access log with your configuration, you can see if the location block you expect to handle it is actually being matched. * Error Logs (error.log): This is often where the real diagnostic gold lies. Nginx logs internal errors, warnings, and debugging information here. bash tail -f /var/log/nginx/error.log * [error] messages: Look for explicit "No such file or directory" messages, permission denied errors (even if they result in a 404), or issues related to upstream servers (if proxying to an api gateway or backend api). * [crit] messages: Indicate critical failures. * Log Level: For deeper debugging, temporarily increase the error_log level to info or even debug in your Nginx configuration. Be cautious with debug in production environments as it generates a huge volume of logs. nginx error_log /var/log/nginx/error.log info; # or debug; After changing the log level, remember to sudo nginx -s reload. The error log will then show more detailed steps Nginx takes internally, such as trying various try_files options.
3. File System Verification
After confirming Nginx's configuration and log output, verify the physical presence and accessibility of the files on the server. * Existence: Use ls -l or find to check if the file or directory Nginx is supposed to serve actually exists at the absolute path determined by your root or alias directives. bash ls -l /var/www/mywebsite/css/style.css # Example * Permissions: Confirm that the Nginx worker process (often www-data or nginx user) has read permissions for the file (r) and execute permissions (x) for all directories along the path to the file. bash ls -ld /var/www/mywebsite/ ls -ld /var/www/mywebsite/css/ ls -l /var/www/mywebsite/css/style.css If permissions are incorrect, use chmod and chown to adjust them. For example, sudo chown -R www-data:www-data /var/www/mywebsite and sudo chmod -R 755 /var/www/mywebsite.
4. Browser Developer Tools and curl
Client-side tools can offer insights into the actual HTTP request and response. * Browser Developer Tools: Open your browser's developer console (F12), go to the "Network" tab, and make the problematic request. You can see the exact request URL, HTTP method, response headers, and the precise status code. This helps confirm that the browser is indeed sending the request you expect and that the server is responding with a 404. * curl: Use the curl command-line tool to make requests directly from the Nginx server itself (if possible) or from a different client. This helps isolate network issues, DNS problems, or proxy caches. bash curl -I http://yourdomain.com/non-existent-page.html # -I shows only headers curl -v http://yourdomain.com/non-existent-api-endpoint # -v shows verbose details If curl from the Nginx server itself also gets a 404, it points to a server-side configuration or file system issue. If an external curl gets a 404 but an internal curl gets a 200, it might be a caching or DNS problem.
5. Testing api Endpoints (Specific to API Gateway/API Context)
When Nginx acts as an api gateway or reverse proxy for api services, specialized testing is necessary. * Direct Backend Testing: Bypass Nginx and test the backend api service directly. If the api itself returns a 404 when directly accessed, the problem lies with the api implementation, not Nginx. This could be done with curl to the api server's IP and port, or using tools like Postman/Insomnia. * Inspect proxy_pass URI: Ensure Nginx is correctly modifying (or not modifying) the URI before forwarding it to the backend api. Directives like proxy_set_header Host $host; are common for ensuring the backend receives the correct hostname. A common pitfall is including the URI in proxy_pass (e.g., proxy_pass http://backend/api/;) when the location block already defines the /api/ prefix.
By diligently following these diagnostic steps, you can systematically narrow down the cause of the 404 error, whether it's a misconfigured directive, a missing file, or an issue originating from a proxied api service.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
Preventing 404 Errors and Best Practices: Building Resilient Nginx Configurations
While robust diagnostic skills are invaluable, the ultimate goal is to proactively prevent 404 errors from occurring in the first place. This involves adopting best practices in Nginx configuration, deployment, and monitoring, with particular attention to how these strategies apply to api gateway and api management.
1. Structured and Modular Configuration
A messy, monolithic Nginx configuration is a breeding ground for errors. Adopt a structured approach: * Modularize: Break down your nginx.conf into smaller, manageable files. Use include directives for server blocks (e.g., /etc/nginx/sites-enabled/*) and common settings (e.g., /etc/nginx/conf.d/proxy.conf). * Comments: Liberally comment your configuration files. Explain the purpose of each server block, location block, and complex directive. This vastly improves maintainability and debugging. * Consistency: Maintain consistent naming conventions and indentation.
2. try_files Best Practices
Leverage try_files intelligently to gracefully handle missing files: * Always provide a fallback: Never let try_files end without a fallback. The try_files $uri $uri/ =404; pattern is common for direct file serving, while try_files $uri $uri/ /index.html; is standard for SPAs. * Order Matters: Understand the order of checks. $uri for a file, $uri/ for a directory, and then the final fallback. * Named Locations for Custom Errors: Use error_page directives combined with named location blocks for custom 404 pages instead of just =404. For example: nginx error_page 404 /404.html; location = /404.html { root /usr/share/nginx/html; internal; # Prevents direct access }
3. Consistent and Automated Deployment
Human error is a significant contributor to missing files. Automate your deployment processes: * Version Control: Store all website code, application binaries, and Nginx configuration files in a version control system (e.g., Git). * CI/CD Pipelines: Implement Continuous Integration/Continuous Deployment (CI/CD) pipelines to automate the build, test, and deployment of your applications and associated Nginx configurations. This ensures that all necessary files are deployed to the correct locations and that Nginx is reloaded only after configuration validation (nginx -t). * Atomic Deployments: Use atomic deployment strategies (e.g., deploying to a new directory and then symlinking) to avoid states where files are temporarily missing.
4. Thorough Testing
Testing should cover all aspects of your application and its serving infrastructure: * Unit and Integration Testing for APIs: For api services, comprehensive unit and integration tests are essential to ensure all api endpoints are implemented, functional, and respond with correct status codes. * Nginx Configuration Testing: Beyond nginx -t, consider tools that can simulate requests against your Nginx configuration to verify routing logic. * Regression Testing: After any changes to code or configuration, run regression tests to ensure existing functionality (and URLs) hasn't been broken, leading to new 404s.
5. Canonical URLs and Redirects
To prevent 404s for moved or deprecated content, and to manage SEO: * 301 Redirects: When a page's URL changes permanently, implement a 301 (Moved Permanently) redirect from the old URL to the new one. This tells browsers and search engines that the content has moved and helps preserve SEO link equity. nginx rewrite ^/old-page\.html$ /new-page.html permanent; * Canonical Tags: Use HTML <link rel="canonical"> tags to inform search engines about the preferred version of a page when duplicate content might exist under different URLs.
6. Custom Error Pages
A generic Nginx 404 page is often unhelpful and jarring for users. Create custom, branded 404 pages: * User-Friendly Messaging: Explain clearly that the page wasn't found, suggest possible reasons (typo, moved page), and provide helpful links (homepage, search, contact). * Branding: Maintain your site's branding and navigation elements to keep users on your site and guide them back to useful content.
7. Monitoring and Alerting
Proactive monitoring is key to catching 404s before they become widespread problems: * Log Aggregation: Use log aggregation tools (e.g., ELK Stack - Elasticsearch, Logstash, Kibana; Splunk; Grafana Loki) to centralize and analyze Nginx access and error logs. * Error Rate Monitoring: Set up dashboards to visualize the rate of 4xx errors. A sudden spike in 404s indicates an immediate problem. * Alerting: Configure alerts (email, Slack, PagerDuty) for significant increases in 404 errors. Define thresholds appropriate for your traffic volume. * Broken Link Checkers: Regularly run broken link checkers (both internal and external) against your website.
8. Version Control for Configuration
Treat your Nginx configurations as code. Store them in Git, implement review processes, and track changes. This allows for easy rollbacks if a change introduces errors and provides an audit trail.
9. Leveraging API Gateway for API Management
For organizations managing a multitude of APIs, especially those leveraging AI models, ensuring all api endpoints are correctly routed and accessible is paramount. A comprehensive api gateway and management platform can abstract much of the low-level routing complexity, thereby significantly reducing the chances of api-related 404 errors that stem from misconfigurations in Nginx acting solely as a simple reverse proxy.
Products like APIPark, an open-source AI gateway and API management platform, provide robust features for end-to-end api lifecycle management, including traffic forwarding, load balancing, and versioning. By centralizing api publication and access, APIPark helps teams ensure their api services are discoverable and correctly invoked, minimizing issues that could lead to 404s at the api gateway layer. It standardizes api invocation, encapsulates prompts into REST apis, and allows for quick integration of 100+ AI models, ensuring consistent routing and availability.
Furthermore, beyond Nginx's native logging, dedicated api gateway solutions offer specialized insights. For instance, APIPark provides comprehensive logging capabilities, recording every detail of each api call. This granular logging is invaluable for businesses to quickly trace and troubleshoot issues, including potential 404 scenarios originating from misconfigured api paths or missing resources within the api ecosystem itself, rather than just the Nginx serving layer. This level of detail surpasses basic Nginx access logs by focusing specifically on the api payload, authentication, and backend service responses, giving a clearer picture of where an api-related 404 genuinely originates. APIPark's powerful data analysis features, built on this detailed logging, can even help predict and prevent issues before they occur by identifying long-term trends in api call patterns and error rates.
By implementing these best practices, from diligent Nginx configuration to advanced api gateway management, you can build a highly resilient web infrastructure that proactively minimizes the occurrence and impact of those frustrating 404 Not Found errors.
Advanced Scenarios and Edge Cases: Beyond the Basics
While the core principles of Nginx 404 diagnosis and prevention remain consistent, modern web architectures often introduce complexities that require a deeper understanding of Nginx's capabilities and interactions with other systems.
1. Geo-distributed Deployments and CDN Interactions
In global deployments, websites often leverage Content Delivery Networks (CDNs) to serve static assets closer to users. A 404 in such an environment can be particularly tricky to debug: * CDN Cache Invalidation: If a file is deleted or moved on the origin server but remains cached by the CDN, users will receive a 404 until the CDN cache is invalidated. Ensure proper cache control headers (e.g., Cache-Control: max-age=...) are set in Nginx to inform the CDN, and be prepared to manually purge CDN caches after critical changes. * Origin Shielding: CDNs often use an "origin shield" layer to reduce requests to the primary Nginx server. Misconfigurations here can lead to 404s if the shield can't reach the origin or has stale information. * Geo-specific Content: If Nginx serves different content based on geographical location, ensuring all regional servers have the correct files and configurations is paramount to avoid regional 404s.
2. Dynamic Content Generation and Framework-Specific Routing
Many modern applications are built using frameworks (e.g., React, Angular, Vue for frontends; Node.js, Python/Django/Flask, PHP/Laravel for backends) that handle their own routing. Nginx's role is typically to direct requests to the application server, not to resolve file paths for dynamic content. * Single-Page Applications (SPAs): For SPAs, Nginx usually serves index.html for all non-static paths, and the client-side JavaScript handles further routing. Misconfigured try_files $uri $uri/ /index.html; (or similar) can prevent the SPA's index.html from loading, leading to a 404 if Nginx tries to find a file matching the dynamic URI. * Backend Framework Routing: When Nginx proxy_passes to a backend application server (e.g., Gunicorn for Django, FPM for PHP), a 404 originating from Nginx itself usually means the proxy_pass configuration is faulty, or Nginx is attempting to serve the request as a static file before passing it to the application. If the backend application returns a 404, Nginx merely proxies that 404 back to the client. Debugging then shifts to the application server's logs and its routing logic. Ensure Nginx passes the full, correct URI to the backend application.
3. Load Balancers and Health Checks
When Nginx is part of a larger system with external load balancers (e.g., AWS ELB/ALB, Google Cloud Load Balancing), these load balancers often perform health checks on the Nginx instances. * Health Check Paths: If a health check path (e.g., /healthz) is misconfigured in Nginx or the application, the load balancer might deem the Nginx instance unhealthy and remove it from the pool. While not directly a 404 for a user, it can lead to degraded service or service unavailability if too many instances are marked unhealthy, potentially contributing to scenarios where users receive errors. * Sticky Sessions: In some cases, sticky sessions (where a user is consistently routed to the same Nginx instance) might inadvertently exacerbate 404s if one specific Nginx instance has a unique configuration error or missing files.
4. Microservices Architecture and Service Discovery
In a microservices world, Nginx often acts as an API Gateway, directing requests to numerous backend services. This is where the concept of an api gateway becomes central. * Service Discovery: When backend services scale dynamically or move, Nginx needs to be aware of their current locations. This can be handled by upstream blocks with multiple servers, or more dynamically through service discovery mechanisms (e.g., Consul, Eureka) integrated with Nginx using custom modules or dynamic configuration reloading. If Nginx loses track of a service, or tries to route to a defunct instance, it can result in a 404 (if the path is not found on the downstream service) or a 5xx (if Nginx cannot connect). * API Versioning and Deprecation: Managing api versions in a microservices environment is complex. An api gateway like Nginx can be configured to route requests for /v1/users to one service version and /v2/users to another. Incorrect location blocks or rewrite rules for api versions can easily lead to 404s for clients requesting deprecated or non-existent versions. * Request Transformation: An api gateway might transform requests before forwarding them (e.g., adding headers, stripping path prefixes). Errors in these transformations can lead to the backend api receiving an unexpected URI and responding with a 404.
These advanced scenarios underscore the need for meticulous configuration, robust monitoring, and a comprehensive understanding of the entire request flow from client to ultimate resource. Each layer, be it a CDN, load balancer, Nginx, an api gateway, or the backend application, contributes to the potential for a 404, and diagnosing them often requires looking beyond just the immediate Nginx configuration.
Impact on SEO and User Experience: The Real-World Consequences
Beyond the technicalities of server configuration, the ubiquitous "404 Not Found" error carries significant real-world implications, impacting both a website's standing in search engine results and the perception and satisfaction of its users. Ignoring or consistently failing to address 404s is detrimental to a healthy online presence.
Crawl Budget Wastage
Search engines like Google have a finite "crawl budget" for each website – the number of pages they are willing to crawl within a given timeframe. When a crawler encounters a 404, it spends part of that budget requesting a non-existent page. If a site has numerous broken links or missing pages, the crawl budget is wasted on these dead ends, meaning legitimate, important pages might be crawled less frequently or even missed entirely. Over time, this can lead to slower indexing of new content and a decline in overall site visibility in search results. Persistent 404s tell search engines that a site is poorly maintained, potentially signaling a lower quality site.
Broken Links and Reputation
From a user's perspective, encountering a 404 is frustrating. It signifies a broken promise – the expectation of content at a specific URL is unmet. * User Frustration: Repeatedly landing on 404 pages leads to a poor user experience, increasing bounce rates and reducing the likelihood of repeat visits. Users might perceive the website as unreliable, unprofessional, or outdated. * Loss of Trust: If a business relies on its website for sales, support, or information dissemination, numerous 404s can erode customer trust and directly impact brand reputation. This is especially critical for api services; if an api endpoint consistently returns 404s, developers using that api will lose trust in its reliability, potentially opting for a competitor's api. * Lost Conversions: For e-commerce sites or lead generation platforms, a 404 on a product page or a contact form directly translates to lost revenue and missed opportunities.
Strategies to Mitigate Negative Impact
While some 404s are inevitable due to user typos or temporary content, a proactive approach can significantly lessen their negative impact:
- Implement Custom 404 Pages: As discussed in prevention, a well-designed, user-friendly 404 page is crucial. It should clearly state the page wasn't found, offer suggestions (e.g., check spelling, use search), and provide easy navigation back to essential parts of the site (homepage, sitemap, contact us). This turns a dead end into an opportunity to retain the user.
- Utilize Sitemaps: An XML sitemap (submitted to Google Search Console and other webmaster tools) lists all the pages you want search engines to crawl. Regularly update your sitemap and ensure it doesn't contain URLs that return 404s. This helps search engines understand your site structure and avoid wasting crawl budget.
- Leverage Google Search Console (or Bing Webmaster Tools): These tools provide invaluable insights into how search engines perceive your site. Specifically, the "Crawl Errors" report will highlight all the 404s (or "Not found" errors) that Googlebot has encountered. Regularly review this report to identify and fix broken links. You can also mark fixed errors to help Google re-crawl.
- Implement 301 Redirects for Moved Content: This is the most effective SEO strategy for content that has permanently moved. A 301 redirect passes almost all of the "link equity" (PageRank) from the old URL to the new one, preventing loss of SEO value and ensuring users land on the correct page. Nginx's
rewriteorreturn 301directives are perfect for this. - Monitor Backlinks: Regularly audit your website's backlinks to identify any incoming links pointing to non-existent pages (resulting in 404s). If possible, contact the linking website to update the URL.
- Periodic Broken Link Checks: Tools exist (both online and as browser extensions) to scan your website for broken internal and external links. Integrating these into your routine maintenance schedule can catch issues before search engines or users do.
By treating 404s not just as technical glitches but as critical indicators of user dissatisfaction and potential SEO damage, businesses can adopt a holistic strategy that ensures a more robust, user-friendly, and search engine-optimized online presence. The careful management of Nginx configurations, especially when acting as an api gateway for an array of api services, forms the foundational layer for preventing these issues and safeguarding the overall health of a website or application.
Conclusion: The Path to a 404-Free Nginx Environment
The "404 Not Found" error, while a seemingly simple message, encapsulates a complex interplay of server configuration, file system integrity, request routing logic, and, increasingly, the intricacies of api gateway management and api service health. For Nginx administrators, understanding the precise mechanisms by which Nginx processes requests and determines the absence of a resource is not merely a technical skill but a critical component of maintaining a high-performing, secure, and user-friendly web presence.
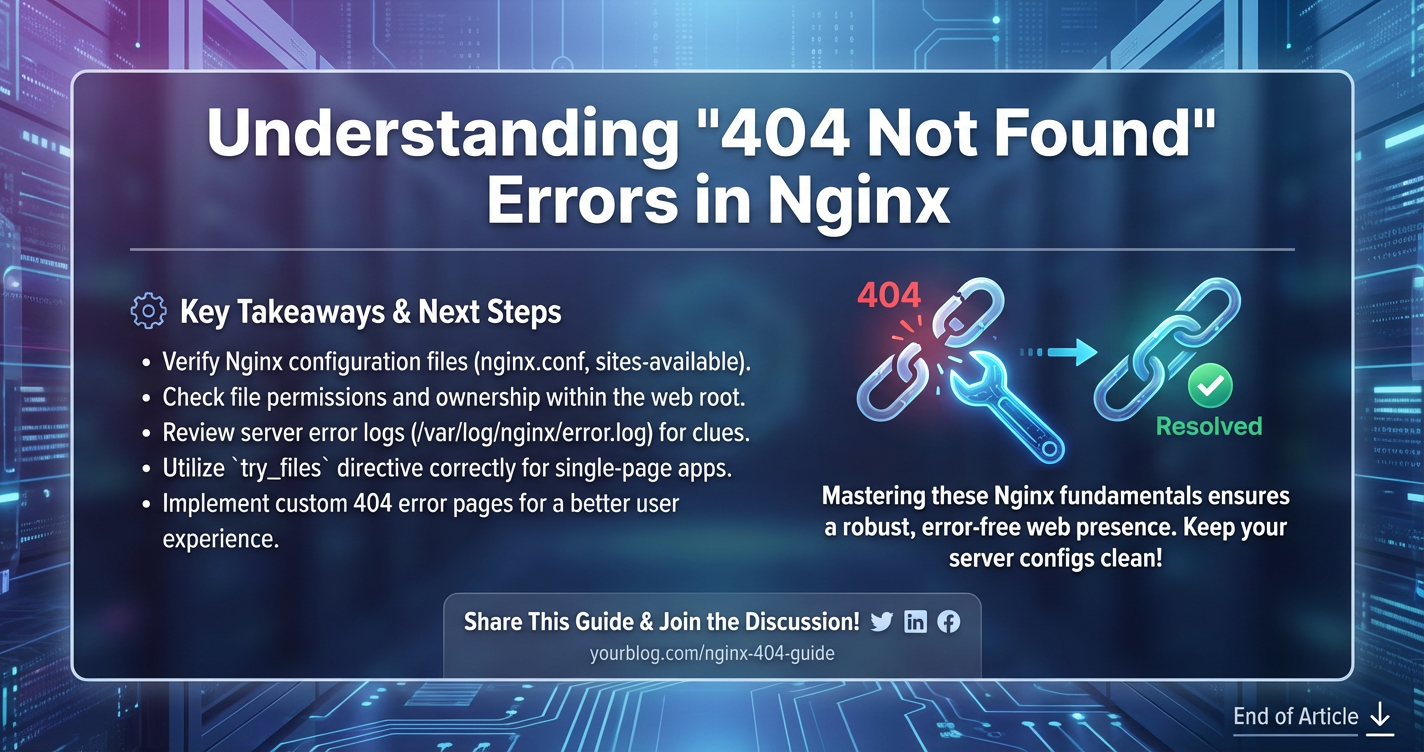
We have journeyed through the fundamental definition of a 404, demystifying its HTTP status class and its implications beyond a mere broken link. We've dissected the Nginx architecture, exploring the pivotal roles of server and location blocks, root and alias directives, and the all-important try_files and proxy_pass commands. Our deep dive into common causes revealed that from simple typos in file paths to sophisticated api gateway routing failures, the sources of 404s are diverse but ultimately traceable.
The systematic diagnostic approach outlined—from validating Nginx syntax and scrutinizing access and error logs to verifying file system permissions and utilizing client-side tools like curl and browser developer consoles—provides a clear roadmap for troubleshooting. More importantly, we emphasized the proactive prevention strategies: structured configurations, automated deployments, rigorous testing, smart use of try_files, canonical URLs, custom error pages, and comprehensive monitoring.
In the modern landscape, where Nginx frequently acts as the first point of contact for an api gateway facilitating countless api calls, the stakes are even higher. A 404 in an api context can disrupt critical business processes, compromise data integrity, and erode developer trust. This is where specialized solutions like APIPark emerge as indispensable tools. By centralizing api lifecycle management, offering unified api formats, integrating diverse AI models, and providing detailed logging and data analysis, platforms like APIPark move beyond basic Nginx proxying to offer a robust framework that significantly mitigates api-related 404s and ensures the discoverability and reliability of api services.
Ultimately, mastering 404 errors in Nginx is about more than just fixing isolated incidents; it's about adopting a philosophy of vigilance, precision, and continuous improvement in your web infrastructure. By combining meticulous Nginx configuration with intelligent api management, robust monitoring, and a user-centric perspective, you can pave the way for a more resilient, performant, and virtually 404-free online experience.
Frequently Asked Questions (FAQs)
Q1: What is the fundamental difference between a 404 Not Found and a 403 Forbidden error in Nginx?
A 404 Not Found error indicates that Nginx could not locate a resource at the requested URL. The server successfully processed the request but found no matching file, directory, or location block to handle it. Conversely, a 403 Forbidden error means Nginx found the resource but explicitly denied access to the client. This typically occurs due to incorrect file/directory permissions for the Nginx worker process, IP address restrictions, or other access control rules. In essence, 404 means "it's not here," while 403 means "it's here, but you can't have it."
Q2: How can try_files help prevent 404 errors in Nginx, especially for single-page applications (SPAs)?
The try_files directive instructs Nginx to check for the existence of files or directories in a specified order, and if none are found, to perform an internal redirect to a fallback URI. For SPAs, where client-side JavaScript handles routing, the common pattern try_files $uri $uri/ /index.html; is crucial. It tells Nginx to first try to serve the exact requested URI as a file ($uri), then as a directory ($uri/), and if neither exists, to internally redirect to /index.html. This ensures that for any non-static path, the SPA's index.html (which loads the JavaScript router) is served instead of a 404, allowing the client-side application to handle the routing.
Q3: What role does an api gateway play in preventing 404s, particularly when Nginx is used as a reverse proxy for apis?
When Nginx acts as a simple reverse proxy for api services, it primarily forwards requests based on configured proxy_pass directives. While effective, managing numerous apis, versions, and backends can become complex. An api gateway, such as APIPark, centralizes api management, routing, and lifecycle governance. It provides a single entry point for all api calls, abstracting backend service locations and versions. By defining explicit api routes, handling api versioning, and offering features like traffic forwarding and load balancing, an api gateway ensures that api requests are correctly routed to the appropriate, available backend service. This significantly reduces the likelihood of Nginx propagating a 404 that originated from a misconfigured or non-existent api endpoint, leading to more reliable api consumption.
Q4: How do Nginx access and error logs assist in diagnosing 404 errors?
Nginx logs are the primary diagnostic tools. The access.log records every client request, including the requested URI, the HTTP status code returned by Nginx, and the client's IP. By analyzing the access.log, you can confirm that a 404 was indeed returned for a specific URI and verify the exact path the client requested. The error.log is even more critical; it logs internal Nginx messages, warnings, and errors. For 404s, the error.log might contain explicit "No such file or directory" messages, permission denied errors, or details about upstream connection failures (if proxying). Temporarily increasing the error_log level to info or debug can provide granular insights into Nginx's internal decision-making process when it fails to find a resource, making it an invaluable tool for pinpointing the exact configuration issue.
Q5: What are the SEO implications of widespread 404 errors, and how can they be mitigated?
Widespread 404 errors negatively impact SEO by wasting "crawl budget," as search engine crawlers spend time trying to access non-existent pages instead of valuable content. This can lead to slower indexing and reduced visibility. Additionally, persistent 404s can signal a poorly maintained website to search engines, potentially affecting rankings. To mitigate this: 1. Implement 301 Redirects: For permanently moved content, use 301 (Moved Permanently) redirects to pass link equity from old URLs to new ones. 2. Custom 404 Pages: Provide user-friendly, branded 404 pages with navigation links to keep users on your site. 3. Monitor Search Console: Regularly check Google Search Console's "Crawl Errors" report to identify and fix 404s. 4. Update Sitemaps: Ensure your XML sitemap is current and does not list any URLs that return 404s. 5. Fix Broken Internal Links: Periodically scan your website for broken internal links and repair them.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.