What You Need to Set Up an API: A Complete Guide

In the intricate tapestry of the modern digital landscape, Application Programming Interfaces (APIs) serve as the indispensable threads that weave disparate systems, applications, and services into a cohesive, functional whole. They are the silent architects of connectivity, enabling innovation, fostering collaboration, and propelling businesses into new realms of efficiency and customer engagement. From the simple act of checking the weather on your phone to the complex orchestration of cloud-native microservices, APIs underpin nearly every interaction we have with digital technology.
The journey of setting up an API, however, is far from a trivial undertaking. It demands a meticulous understanding of technical intricacies, a keen eye for design principles, and a strategic foresight into its long-term management and evolution. This comprehensive guide is crafted to demystify the process, offering a deep dive into every critical facet of API setup, from conceptualization and design to development, deployment, and ongoing governance. Whether you are an aspiring developer venturing into the world of web services, an architect tasked with modernizing legacy systems, or a business leader seeking to leverage the power of programmatic access, this guide will equip you with the knowledge and actionable insights necessary to build robust, scalable, and secure APIs that truly drive value. We will explore the fundamental concepts, delve into best practices for design and implementation, discuss the crucial role of API gateway solutions, emphasize the importance of formal specifications like OpenAPI, and ultimately, chart a course for successful API lifecycle management. Prepare to embark on a detailed exploration that transforms the daunting task of API setup into a clear, manageable, and ultimately rewarding endeavor.
Chapter 1: Understanding the Fundamentals of APIs
Before embarking on the practical journey of setting up an api, it is paramount to establish a solid understanding of what an api is, its core components, and the underlying principles that govern its operation. Without this foundational knowledge, the subsequent steps of design, development, and deployment can quickly become mired in confusion and inefficiency. An api, at its heart, is a set of defined rules and protocols that allow different software applications to communicate with each other. It acts as an intermediary, facilitating requests and responses between distinct systems without requiring them to understand each other's internal workings.
What Exactly is an API? A Deeper Dive
To grasp the essence of an api, let's employ a common analogy: imagine you are in a restaurant. You, the customer, represent the "client" application. The kitchen represents the "server" application, holding all the resources (food ingredients) and the logic to prepare them. You don't go into the kitchen yourself, nor do you need to know precisely how the chef prepares your meal. Instead, you interact with a waiter, who takes your order (a request), delivers it to the kitchen, and then brings back your meal (a response). In this scenario, the waiter is the api. They have a specific protocol for taking orders (the api's request format), a defined menu of items you can request (the api's available resources/endpoints), and a way to deliver the finished product back to you (the api's response format).
Technically speaking, an api defines the methods and data formats that applications can use to request and exchange information. It specifies:
- Operations (Methods): What functions can be performed? (e.g., "get user data," "create new order," "update product inventory").
- Inputs (Parameters): What information is needed to perform an operation? (e.g.,
user_id,product_name,quantity). - Outputs (Responses): What information will be returned? (e.g.,
user_profile_json,order_confirmation_id,success_message). - Data Formats: How will the data be structured? (e.g., JSON, XML).
- Protocols: What communication rules must be followed? (e.g., HTTP/S for web APIs).
This structured approach ensures that applications can interact reliably and predictably, irrespective of the underlying technologies or programming languages used to build them.
Key Concepts and Terminology in the API World
Navigating the world of APIs requires familiarity with a specific lexicon. Understanding these terms is fundamental to both designing and consuming APIs effectively.
- Endpoint: An endpoint is a specific URL where an api can be accessed. It's like a specific dish on the menu in our restaurant analogy. For example,
https://api.example.com/usersmight be an endpoint to access user information, andhttps://api.example.com/products/123would be an endpoint for a specific product. - Request: A message sent by the client to the server, asking for a particular action or data. A request typically includes:
- HTTP Method: Indicates the desired action (GET, POST, PUT, DELETE, PATCH).
- URL/Endpoint: Specifies the resource.
- Headers: Metadata about the request (e.g.,
Content-Type,Authorization). - Body: Data to be sent to the server (e.g., JSON payload for creating a new resource).
- Response: The message sent back by the server to the client in reply to a request. A response typically contains:
- HTTP Status Code: A numerical code indicating the outcome of the request (e.g., 200 OK, 404 Not Found, 500 Internal Server Error).
- Headers: Metadata about the response.
- Body: The actual data requested, or an error message.
- HTTP Methods (Verbs): These define the type of action you want to perform on a resource:
- GET: Retrieve data from the server. (Idempotent and safe)
- POST: Send new data to the server to create a resource. (Not idempotent)
- PUT: Update an existing resource with new data, or create it if it doesn't exist. (Idempotent)
- DELETE: Remove a resource from the server. (Idempotent)
- PATCH: Apply partial modifications to a resource. (Not idempotent)
- Authentication: The process of verifying a client's identity. Common methods include:
- API Keys: A simple token provided in the request header or query parameter.
- OAuth 2.0: An authorization framework allowing third-party applications to obtain limited access to user accounts on an HTTP service.
- JWT (JSON Web Tokens): A compact, URL-safe means of representing claims to be transferred between two parties.
- Authorization: The process of determining if an authenticated client has permission to perform a specific action or access a particular resource.
- Data Formats: The structure in which data is exchanged.
- JSON (JavaScript Object Notation): The de facto standard for web APIs due to its lightweight nature, human readability, and ease of parsing in most programming languages.
- XML (Extensible Markup Language): Older but still used in some enterprise systems, particularly with SOAP APIs.
- REST (Representational State Transfer) vs. SOAP (Simple Object Access Protocol):
- REST: An architectural style for designing networked applications. RESTful APIs are stateless, client-server based, and utilize standard HTTP methods. They are typically simpler, more flexible, and widely adopted for web services. Most modern APIs are RESTful.
- SOAP: A protocol for exchanging structured information in the implementation of web services. SOAP APIs are often more complex, relying on XML, and come with a stricter contract (WSDL). They are often found in enterprise environments with stricter security and transaction requirements. This guide will primarily focus on RESTful API setup, given its pervasive use.
The Indisputable Benefits of Building and Consuming APIs
The widespread adoption of APIs isn't merely a technological trend; it's a fundamental shift driven by tangible business and technical benefits:
- Enhanced Interoperability: APIs break down silos between systems, allowing disparate applications, regardless of their underlying technology, to communicate and share data seamlessly. This is crucial for integrating third-party services, connecting internal microservices, and fostering a cohesive digital ecosystem.
- Increased Automation: By exposing functionalities programmatically, APIs enable automation of workflows. Repetitive tasks, data synchronization, and complex business processes can be orchestrated automatically, reducing manual effort, minimizing errors, and accelerating operational speed.
- Accelerated Innovation: APIs act as building blocks. Developers can leverage existing functionalities exposed by APIs instead of reinventing the wheel, significantly speeding up development cycles and fostering the creation of new products and services. This encourages a culture of rapid experimentation and innovation.
- Improved Efficiency and Productivity: For internal development teams, well-designed APIs can drastically improve productivity. They enforce clear contracts, reduce code duplication, and allow teams to work independently on different parts of an application while ensuring seamless integration.
- Expanded Reach and New Business Models: By exposing their core functionalities through APIs, businesses can open up new channels for growth. They can reach new markets by allowing partners to integrate their services, enable third-party developers to build applications on top of their platform, or even create entirely new data-as-a-service offerings, transforming their data into a valuable asset.
- Data Monetization: APIs can turn valuable data into a revenue stream. Companies with rich datasets can offer programmatic access to this information, charging for usage and creating entirely new business models centered around data provision.
- Better User Experience: By integrating various services through APIs, applications can offer richer, more seamless, and personalized user experiences. Think of an e-commerce site showing real-time shipping updates from a logistics provider api, or a travel app integrating flight data from multiple airlines.
Understanding these fundamentals lays the groundwork for a successful API journey. With a clear picture of "what" an api is and "why" it's essential, we can now proceed to the intricate process of designing one.
Chapter 2: Designing Your API – The Blueprint for Success
The design phase is arguably the most critical step in setting up an api. A well-designed api is intuitive, consistent, scalable, and a pleasure for developers to consume. Conversely, a poorly designed api can lead to frustration, integration headaches, and significant technical debt. This chapter delves into the principles and practices that underpin effective api design, transforming abstract requirements into a concrete, usable specification.
Defining the API's Purpose and Scope: The Foundation
Before writing a single line of code or sketching an endpoint, you must clearly define why your api exists. This involves answering several fundamental questions:
- What problem does this API solve? Is it to expose internal data, enable third-party integrations, or support a new mobile application?
- Who are the target consumers? Are they internal developers, external partners, or the general public? Understanding your audience dictates the level of abstraction, documentation detail, and error handling sophistication.
- What resources will it expose? Identify the core entities that your api will manage (e.g., users, products, orders, documents).
- What operations will be allowed on these resources? Will consumers be able to create, read, update, or delete these resources?
- What are the business requirements? Align the api's capabilities with specific business goals.
- What are the technical constraints? Consider performance requirements, data volume, security mandates, and existing infrastructure limitations.
A clear scope prevents scope creep and ensures the api remains focused on delivering specific value.
Resource Modeling: The Nouns of Your API
In a RESTful api, everything is a resource. Resources are the conceptual entities that your api exposes, and they should typically be represented as nouns. This is a crucial step in design.
- Identify Core Entities: Brainstorm all the significant "things" your system interacts with. For an e-commerce api, these might include
products,orders,customers,reviews,categories. - Define Relationships: How do these entities relate to each other? An
orderhasproductsand belongs to acustomer. Aproducthasreviews. These relationships will inform your URL structure. - Resource Representation: Decide what data attributes constitute each resource. For a
product, this might beid,name,description,price,stock_quantity,image_url.
Endpoint Design (URL Structure): Making Your API Intuitive
The URL structure of your api should be logical, predictable, and easy to understand. RESTful principles guide this process:
- Use Nouns for Resources: Always use plural nouns to represent collections of resources.
- Good:
/products,/users - Bad:
/getProducts,/createUser
- Good:
- Hierarchical Relationships: Reflect relationships in the URL path.
- To get all products for a specific user:
/users/{user_id}/products - To get a specific product from a specific user:
/users/{user_id}/products/{product_id}
- To get all products for a specific user:
- Avoid Verbs in URLs: HTTP methods (GET, POST, PUT, DELETE) already convey the action.
- Good:
GET /users/{id}(to retrieve a user) - Bad:
GET /getUser/{id}
- Good:
- Versioning: Incorporate api versioning into your URLs to manage changes without breaking existing integrations.
/v1/products,/v2/products(path-based versioning is common and clear).- Alternatively, use header-based versioning (e.g.,
Accept: application/vnd.example.v1+json).
- Clear Parameter Naming: Use consistent and descriptive names for query parameters (e.g.,
page,limit,sort_by,search_term).
HTTP Methods: Mapping Actions to Verbs
Each endpoint, combined with an HTTP method, defines a specific action. This table illustrates standard mappings:
| HTTP Method | Action/Purpose | Idempotent | Safe | Description |
|---|---|---|---|---|
| GET | Retrieve resource(s) | Yes | Yes | Requests data from a specified resource. Should not have side effects. Multiple identical GET requests should have the same outcome as a single one. |
| POST | Create a new resource, or submit data | No | No | Sends data to the server to create a new resource or perform a specific action that isn't idempotent (e.g., submitting a form, placing an order). Repeated POST requests can create multiple identical resources. |
| PUT | Update an existing resource, or create if non-existent | Yes | No | Replaces all current representations of the target resource with the request payload. If the resource does not exist, it creates it. Repeated PUT requests for the same resource will yield the same result (idempotent). |
| DELETE | Remove a resource | Yes | No | Deletes the specified resource. Repeated DELETE requests for the same resource will effectively yield the same outcome (the resource remains deleted, subsequent requests might return 404). |
| PATCH | Apply partial modifications to a resource | No | No | Applies partial modifications to a resource. Unlike PUT, it only sends the data that needs to be updated. Repeated PATCH requests might not yield the same result if the operation is state-dependent (e.g., incrementing a counter), hence not strictly idempotent in all cases. |
| HEAD | Retrieve resource headers | Yes | Yes | Similar to GET, but only retrieves the headers, without the response body. Useful for checking resource existence or metadata without downloading the full content. |
| OPTIONS | Describe communication options | Yes | Yes | Requests information about the communication options available for the target resource. Clients can discover what HTTP methods, headers, etc., are supported by an api endpoint. |
Idempotent means that making the same request multiple times will have the same effect as making it once. Safe means the request doesn't change the state of the server.
Request and Response Design: The Contract
The format of your requests and responses forms the explicit contract between your api and its consumers. Consistency and clarity are paramount.
- Input Parameters: Clearly define required vs. optional parameters, their data types, and any constraints (e.g., string length, number range). Use query parameters for filtering, sorting, and pagination, and the request body for complex data submissions (POST, PUT, PATCH).
- Output Data Structure: Design logical and consistent JSON (or XML) structures for your responses.
- Flat vs. Nested: Avoid excessive nesting; keep structures as flat as possible for ease of consumption.
- Consistent Naming: Use
camelCaseorsnake_caseconsistently. - Pagination: Include
total,page,limit,and next/previous linksfor collections. - Metadata: Consider adding metadata to responses (e.g.,
timestamp,version).
- HTTP Status Codes: Use standard HTTP status codes accurately to indicate the outcome of a request.
2xx Success:200 OK,201 Created,204 No Content.3xx Redirection:301 Moved Permanently.4xx Client Error:400 Bad Request,401 Unauthorized,403 Forbidden,404 Not Found,409 Conflict,429 Too Many Requests.5xx Server Error:500 Internal Server Error,503 Service Unavailable.
- Error Handling: Provide detailed, machine-readable error messages. An error response should clearly explain what went wrong and, if possible, how to fix it.
- Structure:
{"error": {"code": "INVALID_INPUT", "message": "The 'name' field is required.", "details": [{"field": "name", "issue": "missing"}]}}
- Structure:
Authentication and Authorization Strategy: Securing Access
Security must be baked into the design from the very beginning.
- Authentication:
- API Keys: Simplest, good for basic usage where granular user access isn't needed. Often passed in headers (
X-API-KEY) or query parameters. - OAuth 2.0: Industry standard for delegated authorization. Ideal when third-party applications need to access user data on behalf of a user without revealing user credentials. Involves grant types (e.g., Authorization Code, Client Credentials).
- JWT (JSON Web Tokens): Commonly used with OAuth 2.0 as access tokens. JWTs are self-contained and digitally signed, allowing stateless authentication.
- API Keys: Simplest, good for basic usage where granular user access isn't needed. Often passed in headers (
- Authorization: After authentication, determine what an authenticated user or application is allowed to do.
- Role-Based Access Control (RBAC): Assign roles to users (e.g.,
admin,editor,viewer), and define permissions for each role. - Attribute-Based Access Control (ABAC): More granular, permissions are based on attributes of the user, resource, and environment.
- Role-Based Access Control (RBAC): Assign roles to users (e.g.,
Versioning: Managing Change Gracefully
APIs evolve. New features are added, old ones are deprecated, and data structures change. Versioning is essential to introduce changes without disrupting existing consumers.
- URL Path Versioning:
/v1/products. This is straightforward and highly visible. - Header Versioning:
Accept: application/vnd.example.v1+json. Less visible but allows the same URL to serve different versions based on theAcceptheader. - Query Parameter Versioning:
GET /products?version=1. Generally less favored as it can make URLs look messy.
Choose a strategy and stick to it. Always provide a clear deprecation policy for older versions.
Documentation First Approach: The Power of OpenAPI Specification
One of the most powerful practices in modern api design is to adopt a "documentation first" or "design first" approach, often leveraging the OpenAPI Specification (formerly known as Swagger).
- What is OpenAPI? OpenAPI is a language-agnostic, human-readable, and machine-readable specification for defining RESTful APIs. It allows you to describe your api's endpoints, operations, input/output parameters, authentication methods, and more in a standardized JSON or YAML format.
- Benefits of OpenAPI:
- Clear Contract: It provides a single source of truth for your api's capabilities, acting as a clear contract between providers and consumers.
- Automatic Documentation: Tools can generate interactive, browsable documentation (like Swagger UI) directly from your OpenAPI definition, eliminating manual documentation effort and ensuring it's always up-to-date with your design.
- Client Code Generation: Developers can use OpenAPI definitions to automatically generate client SDKs in various programming languages, accelerating integration.
- Server Stubs: Generate server-side code stubs, providing a starting point for implementation.
- Automated Testing: OpenAPI definitions can be used to generate test cases, facilitating automated api testing.
- Validation: Tools can validate requests and responses against the OpenAPI schema, catching errors early.
- API Gateway Integration: Many api gateway solutions can ingest OpenAPI definitions to automatically configure routing, validation, and documentation.
By designing with OpenAPI from the outset, you create a robust blueprint that guides development, simplifies communication, and significantly enhances the developer experience. Tools like Stoplight Studio, Swagger Editor, and VS Code extensions make creating and validating OpenAPI definitions much easier.
Effective api design is an art and a science, balancing technical constraints with user-centric intuition. By adhering to these principles, you lay a solid foundation for an api that is not only functional but also future-proof and developer-friendly.
Chapter 3: Developing and Implementing Your API – Bringing the Design to Life
With a robust api design and a detailed OpenAPI specification in hand, the next phase involves translating that blueprint into functional code. This chapter guides you through the practical aspects of developing and implementing your api, covering technology choices, coding best practices, security considerations, and essential testing strategies. This is where the theoretical design becomes a tangible digital service.
Choosing the Right Technology Stack: Tailoring to Your Needs
The choice of programming language, framework, and database significantly impacts an api's performance, scalability, and development speed. There's no one-size-fits-all answer; the best stack depends on your project's specific requirements, your team's expertise, and the existing infrastructure.
- Programming Languages:
- Python: Excellent for rapid development, data science, and web APIs with frameworks like Django (Django REST Framework) and Flask. Known for its clear syntax and large ecosystem.
- Node.js (JavaScript): Ideal for real-time applications and highly scalable, I/O-bound APIs due to its non-blocking event-driven architecture. Express.js is a popular framework.
- Java: A stalwart for enterprise-grade applications, offering strong typing, robust performance, and a vast ecosystem with frameworks like Spring Boot (very popular for REST APIs) and Quarkus.
- Go (Golang): Gaining popularity for high-performance microservices and APIs due to its concurrency features, efficient compilation, and small binary sizes.
- Ruby: Ruby on Rails provides a convention-over-configuration approach, excellent for rapid prototyping and RESTful API development.
- PHP: With frameworks like Laravel and Symfony, PHP remains a strong contender for web APIs, offering ease of deployment and a massive community.
- Web Frameworks: These libraries provide structure, tools, and helpers to streamline API development, handling routing, request parsing, and response formatting. Popular choices include Django REST Framework (Python), Express.js (Node.js), Spring Boot (Java), Laravel (PHP), and Ruby on Rails (Ruby).
- Databases:
- Relational Databases (SQL): MySQL, PostgreSQL, SQL Server, Oracle. Best for structured data, complex queries, and applications requiring strong transactional consistency (ACID properties).
- NoSQL Databases: MongoDB (document), Cassandra (column-family), Redis (key-value), Neo4j (graph). Excellent for handling unstructured or semi-structured data, high volumes of traffic, and scenarios where schema flexibility and horizontal scalability are priorities. The choice often depends on your data model and access patterns.
Consider factors like developer familiarity, community support, performance requirements, and cloud integration when making your selection.
Coding Best Practices: Building Robust and Maintainable APIs
Writing clean, efficient, and secure code is paramount for the long-term success of your api.
- Modularity and Separation of Concerns: Organize your code logically. Separate concerns like routing, business logic, data access, and validation into distinct modules or layers. This enhances readability, maintainability, and testability.
- Input Validation: Never trust user input. Validate all incoming data thoroughly for type, format, length, and range. This prevents errors, maintains data integrity, and is a critical security measure against injection attacks.
- Error Handling: Implement comprehensive error handling. Catch exceptions gracefully, log internal errors for debugging, and return meaningful, standardized error responses to the client, adhering to your OpenAPI definition for error structures.
- Consistent Code Style: Adhere to a consistent coding style (e.g., PEP 8 for Python, Airbnb style guide for JavaScript). Use linters and formatters (like Black for Python, Prettier for JavaScript) to automate this.
- Sensible Logging: Implement robust logging at various levels (debug, info, warning, error). Log key events, request details, and error messages to aid in monitoring, debugging, and auditing. Be cautious not to log sensitive data.
- Rate Limiting: Implement rate limiting to prevent abuse, protect your backend services from overload, and ensure fair usage among consumers. This can be done at the application level or, more efficiently, at the API Gateway level.
- Caching: Strategically implement caching for frequently accessed, slow-changing data. This can significantly reduce database load and improve response times. Consider client-side caching (ETags,
Cache-Controlheaders) and server-side caching (Redis, Memcached).
Database Integration: Efficient Data Management
Your API's performance is often directly tied to its database interactions.
- ORM (Object-Relational Mapping) vs. Raw Queries:
- ORMs (e.g., SQLAlchemy for Python, Hibernate for Java, Mongoose for Node.js/MongoDB): Abstract away database specifics, allowing you to interact with your database using object-oriented code. They improve development speed and portability but can sometimes lead to less optimized queries.
- Raw SQL Queries: Offer maximum control and optimization, essential for complex reports or high-performance scenarios, but require more manual effort and are less portable.
- Often, a hybrid approach works best: use an ORM for most standard operations and resort to raw queries for specific performance-critical tasks.
- Efficient Querying:
- Indexing: Ensure appropriate indexes are created on frequently queried columns to speed up data retrieval.
- Lazy Loading vs. Eager Loading: Understand when to fetch related data upfront (eager loading) and when to load it only when needed (lazy loading) to avoid N+1 query problems.
- Pagination: Implement server-side pagination for large datasets to prevent overwhelming the server and client with excessive data.
Security Implementation: A Non-Negotiable Imperative
Security is not an afterthought; it's a continuous process throughout development.
- Transport Layer Security (TLS/SSL): Always enforce HTTPS for all api communication. This encrypts data in transit, protecting against eavesdropping and man-in-the-middle attacks.
- Input Validation and Sanitization: As mentioned, validate all inputs to prevent SQL injection, XSS (Cross-Site Scripting), and other common web vulnerabilities. Sanitize any data that will be rendered back to a client.
- Authentication and Authorization: Implement your chosen authentication and authorization mechanisms rigorously.
- Password Hashing: Store user passwords securely using strong, one-way hashing algorithms (e.g., bcrypt) with salts.
- Token Security: Ensure API keys and access tokens are stored securely, transmitted over HTTPS, and have appropriate expiration policies.
- Least Privilege: Grant users and applications only the minimum necessary permissions to perform their tasks.
- CORS (Cross-Origin Resource Sharing): Properly configure CORS headers to control which domains are allowed to make requests to your api from a browser. Restrict
Access-Control-Allow-Originto only trusted domains. - Environment Variables: Never hardcode sensitive information (database credentials, API keys) directly into your code. Use environment variables or a secrets management system.
- Dependency Security: Regularly update your libraries and frameworks to patch known vulnerabilities. Use security scanning tools for dependencies.
- Error Message Disclosure: Avoid exposing sensitive system information (stack traces, database connection strings) in error messages returned to the client.
Testing Your API: Ensuring Quality and Reliability
Thorough testing is crucial to ensure your API functions as expected, handles edge cases gracefully, and remains stable over time.
- Unit Tests: Test individual components (functions, classes) in isolation. These are fast and help pinpoint defects in specific code units.
- Integration Tests: Verify that different parts of your system work together correctly (e.g., your api layer interacting with the database, or multiple microservices communicating).
- End-to-End (E2E) Tests: Simulate real user scenarios, testing the entire flow from the client application through the api to the backend services.
- Performance Tests: Evaluate your API's responsiveness, stability, and scalability under various load conditions (load testing, stress testing, soak testing).
- Security Tests: Conduct penetration testing, vulnerability scanning, and fuzz testing to identify security flaws.
- Tools for API Testing:
- Postman/Insomnia: Excellent for manual testing, creating test collections, and basic automation.
- Automated Testing Frameworks:
pytest(Python),Jest(Node.js),JUnit(Java) can be used with libraries likerequests(Python) orsupertest(Node.js) to write automated API tests. - OpenAPI-based testing tools: Tools that can generate tests directly from your OpenAPI specification, ensuring compliance with your defined contract.
Automate as much of your testing as possible and integrate it into your CI/CD pipeline to catch regressions early. By meticulously following these development and implementation guidelines, you can build an api that is not only functional but also secure, scalable, and maintainable, ready for the next phase of deployment and management.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
Chapter 4: Deploying and Managing Your API – From Code to Production
Building a functional api is only half the battle; the true challenge lies in deploying it reliably and managing its lifecycle effectively in a production environment. This chapter covers the critical aspects of taking your api live, ensuring its performance, security, and long-term stability through robust deployment strategies, monitoring, and the strategic utilization of an API Gateway.
Deployment Environment: Where Your API Lives
Choosing the right infrastructure for your api is a fundamental decision that impacts scalability, cost, and operational complexity.
- Cloud Providers (IaaS/PaaS):
- AWS, Azure, Google Cloud Platform (GCP): Offer a vast array of services (compute, database, networking, serverless functions) that provide unparalleled scalability, reliability, and global reach. You pay for what you use, allowing for flexible scaling.
- Infrastructure as a Service (IaaS): You provision virtual machines (EC2, Azure VMs, Compute Engine) and manage the operating system, runtime, and application. Offers high control.
- Platform as a Service (PaaS): You deploy your code, and the cloud provider manages the underlying infrastructure (e.g., AWS Elastic Beanstalk, Azure App Service, Google App Engine). Simplifies deployment and scaling, but offers less control.
- Serverless (FaaS): Services like AWS Lambda, Azure Functions, Google Cloud Functions allow you to run code without provisioning or managing servers. You only pay when your code executes. Ideal for event-driven, short-lived api functions.
- Containers (Docker) and Orchestration (Kubernetes):
- Docker: Packages your api and all its dependencies into a portable, consistent unit called a container. This ensures that your api runs the same way in development, testing, and production environments, eliminating "it works on my machine" issues.
- Kubernetes (K8s): An open-source system for automating deployment, scaling, and management of containerized applications. It provides self-healing, load balancing, and rolling updates, making it the de facto standard for managing microservices at scale. Deploying your api within Kubernetes (on-premise or managed cloud services like EKS, AKS, GKE) offers immense power and flexibility.
- On-Premise Servers: For organizations with strict data sovereignty requirements or existing infrastructure investments, deploying on private servers remains an option. However, it incurs significant operational overhead for maintenance, scaling, and security.
The trend for modern api deployment heavily favors cloud-native solutions, leveraging containers and serverless architectures for their agility, scalability, and cost-effectiveness.
Scalability and Performance: Handling Growth
As your api gains traction, it must be able to handle increasing loads without degradation in performance.
- Load Balancing: Distributes incoming api traffic across multiple instances of your api service. This improves availability, prevents any single instance from becoming a bottleneck, and enables horizontal scaling.
- Auto-Scaling: Automatically adjusts the number of api service instances based on demand (e.g., CPU utilization, request queue length). This ensures optimal resource usage and consistent performance during traffic spikes and dips.
- Caching Strategies:
- Reverse Proxy/CDN (Content Delivery Network): Caches static assets and responses from public endpoints closer to the user, reducing latency.
- Application-Level Caching: Caches frequently requested data in memory or a dedicated caching layer (e.g., Redis, Memcached) to reduce database hits and accelerate response times.
- Database Optimization: Beyond indexing (as discussed in Chapter 3), consider database replication (read replicas), sharding (distributing data across multiple databases), and connection pooling to enhance database performance under heavy load.
Monitoring and Analytics: Keeping an Eye on Your API
Once deployed, continuous monitoring is non-negotiable for understanding your api's health, performance, and usage patterns.
- Performance Metrics: Track key metrics like:
- Latency/Response Time: How quickly does your api respond to requests?
- Error Rates: Percentage of requests resulting in 4xx or 5xx errors.
- Throughput: Number of requests per second (RPS).
- CPU/Memory Utilization: Resource consumption of your api instances.
- Logging: Centralize all api logs (access logs, error logs, application logs) into a single system (e.g., ELK stack - Elasticsearch, Logstash, Kibana; Grafana Loki, Splunk). This enables easy searching, filtering, and analysis of issues.
- Alerting: Set up automated alerts for critical events (e.g., high error rates, prolonged latency, service downtime). These alerts should notify the relevant teams via email, SMS, or incident management tools.
- Distributed Tracing: For microservices architectures, distributed tracing tools (e.g., Jaeger, Zipkin, OpenTelemetry) help visualize the flow of a single request across multiple services, making it easier to identify performance bottlenecks or failures.
- API Analytics: Gain insights into api consumption patterns, top users, most popular endpoints, and geographical usage. This data is invaluable for business decisions, capacity planning, and identifying potential abuse.
API Gateway: The Front Door to Your API Ecosystem
A crucial component in managing and securing APIs, particularly in microservices architectures or when dealing with numerous APIs, is the API Gateway. An API Gateway acts as a single entry point for all client requests, abstracting the complexity of your backend services and providing a centralized point of control. It sits between the clients and your backend APIs, handling a myriad of cross-cutting concerns that would otherwise need to be implemented in each individual api service.
- What is an API Gateway? Imagine a highly organized concierge for a large, sprawling hotel. Instead of guests trying to find their specific room or service directly, they interact with the concierge, who knows how to route requests, verify identities, and handle common inquiries. An API Gateway serves this role for your APIs. It's a reverse proxy that accepts incoming requests, applies various policies, and routes them to the appropriate backend service.
- Key Functions of an API Gateway:
- Authentication and Authorization: The gateway can handle initial client authentication (API keys, OAuth tokens) and ensure that requests are authorized before forwarding them to backend services. This offloads security concerns from individual APIs.
- Rate Limiting and Throttling: Prevent API abuse and protect backend services from overload by enforcing limits on the number of requests a client can make within a certain timeframe.
- Routing and Load Balancing: Directs requests to the correct backend api service based on defined rules and distributes traffic evenly across multiple instances of a service.
- Request/Response Transformation: Modifies request or response headers and bodies, allowing for different client expectations (e.g., translating older api versions to newer ones, or adapting data formats).
- Caching: Caches responses from backend services to reduce load and improve response times for frequently accessed data.
- Monitoring and Logging: Centralizes logging and metrics collection for all api traffic, providing a comprehensive view of api usage and performance.
- Security: Provides an additional layer of defense against common web attacks, injects security headers, and can integrate with WAFs (Web Application Firewalls).
- Developer Portal: Often integrated with a developer portal to provide documentation, SDKs, and a self-service experience for api consumers.
The strategic deployment of an API Gateway enhances security, improves performance, simplifies api management, and provides a better developer experience. It centralizes concerns, allowing individual api services to focus purely on their core business logic.
For instance, robust platforms like APIPark provide an open-source AI gateway and API management solution, streamlining these critical functions and offering advanced features tailored for modern needs. APIPark stands out by not only handling traditional API Gateway responsibilities but also by providing seamless integration with over 100 AI models, unifying their invocation formats. This means developers can encapsulate prompts into REST APIs, creating new AI-powered services like sentiment analysis or translation APIs with ease, all while benefiting from end-to-end api lifecycle management. From design and publication to invocation and decommission, APIPark helps regulate processes, manage traffic forwarding, load balancing, and versioning, ensuring a consistent and efficient api ecosystem. It supports sharing api services within teams, enabling multi-tenancy with independent access permissions, and even requires approval for resource access, enhancing security. Furthermore, APIPark boasts impressive performance, rivaling Nginx with over 20,000 TPS on modest hardware, and offers detailed api call logging and powerful data analysis tools to proactively identify trends and prevent issues. Its rapid 5-minute deployment capability further underscores its commitment to developer efficiency.
Documentation and Developer Portal: Empowering Consumers
No matter how well-designed your api is, it's useless if developers can't understand how to use it. Comprehensive, up-to-date documentation is paramount.
- Developer Portal: A dedicated website where api consumers can discover, learn about, register for, and manage access to your APIs. It's often the first touchpoint for potential integrators.
- Interactive Documentation: As discussed in Chapter 2, leveraging OpenAPI (Swagger UI) generates dynamic and interactive documentation directly from your API's specification. This allows developers to explore endpoints, parameters, and responses, and even make test calls directly from the browser.
- Getting Started Guides: Provide clear, concise guides for quickly integrating with your api.
- Code Samples and SDKs: Offer example code in popular programming languages and provide pre-built client SDKs to reduce the integration effort for consumers.
- Use Cases and Tutorials: Illustrate common scenarios and walk developers through practical implementations.
- Support Channels: Provide clear channels for developers to ask questions, report bugs, and get support.
API Versioning Strategy in Practice: Graceful Evolution
Managing versions requires a clear strategy and careful communication.
- Communicate Changes: Announce upcoming changes and new versions well in advance.
- Deprecation Policy: Establish a clear policy for deprecating older api versions (e.g., support
v1for 12 months afterv2is released). - Backward Compatibility: Strive to maintain backward compatibility as much as possible for minor updates within a version. Breaking changes should warrant a new major version.
- Feature Flags: Use feature flags to roll out new api features incrementally to a subset of users, allowing for testing and quick rollbacks if issues arise.
Security Best Practices in Production: Continuous Vigilance
Production security is an ongoing commitment.
- Regular Security Audits and Penetration Testing: Periodically engage external security experts to conduct audits and penetration tests to identify vulnerabilities.
- Vulnerability Scanning: Use automated tools to continuously scan your api and its underlying infrastructure for known vulnerabilities.
- Web Application Firewall (WAF): Deploy a WAF in front of your api to detect and block common web attacks (e.g., SQL injection, XSS). Often integrated with API Gateway solutions.
- Data Encryption at Rest and in Transit: Ensure all sensitive data is encrypted both when stored in databases (at rest) and when transmitted over networks (in transit) using TLS.
- Principle of Least Privilege: Apply this principle not just to users but also to your api services themselves. Grant them only the permissions necessary to perform their functions.
- Incident Response Plan: Have a well-defined plan for how to detect, respond to, and recover from security incidents.
By meticulously implementing these deployment and management strategies, leveraging powerful tools like API Gateway solutions (including specialized ones like APIPark), and maintaining a relentless focus on security and documentation, you can ensure your api operates as a robust, scalable, and trusted service within your digital ecosystem.
Chapter 5: Evolving Your API and Advanced Best Practices
The journey of an api doesn't end with deployment. In today's dynamic digital landscape, an api must continuously evolve, adapt, and improve to remain relevant and valuable. This final chapter explores strategies for continuous improvement, advanced governance, further security considerations, and glimpses into the future of api development.
Continuous Improvement: Iterating for Excellence
An api is a living product that benefits from ongoing refinement based on feedback and performance data.
- Gathering Feedback: Actively solicit feedback from your api consumers through developer forums, surveys, and direct communication. Understand their pain points, feature requests, and use cases. This feedback loop is invaluable for prioritizing future development.
- Monitoring and Analytics Review: Regularly review the performance metrics, logs, and analytics data collected in Chapter 4. Identify performance bottlenecks, frequently used (or unused) endpoints, common error patterns, and areas where the api experience could be smoother.
- Iterative Development: Embrace an agile approach to api development. Release small, incremental updates frequently rather than large, infrequent ones. This allows for faster iteration, quicker feedback cycles, and reduced risk.
- A/B Testing for API Changes: For non-breaking changes or new features, consider A/B testing different versions of an api endpoint or logic to see which performs better or is preferred by consumers. This can be complex but provides data-driven insights.
API Governance: Ensuring Consistency and Quality Across the Board
As the number of APIs in an organization grows, maintaining consistency, quality, and security becomes a significant challenge. API governance establishes the rules, processes, and tools to manage this complexity.
- Standardization: Define and enforce consistent design principles, naming conventions, error handling, authentication schemes, and data formats across all your APIs. This reduces cognitive load for developers and streamlines integration.
- API Design Review Process: Implement a formal review process for new API designs and significant changes. This ensures adherence to standards, security best practices, and alignment with business objectives before development begins. An OpenAPI specification can be the central artifact for this review.
- Centralized API Catalog/Registry: Maintain a central repository or developer portal (as discussed in Chapter 4) where all APIs are documented, discoverable, and categorized. This prevents duplication and promotes reuse.
- Security Policies: Establish comprehensive security policies for API development and operations, including data privacy, access control, vulnerability management, and incident response.
- Performance Benchmarks: Define performance benchmarks and Service Level Objectives (SLOs) for your APIs, and actively monitor against these targets.
Effective governance ensures that your API ecosystem remains cohesive, secure, and performant, preventing the sprawl of inconsistent or insecure APIs.
API Security Beyond the Gateway: A Multi-Layered Approach
While an API Gateway provides a crucial first line of defense, api security is a multi-layered responsibility that extends throughout your entire infrastructure.
- Data Encryption (at Rest and in Transit): Reiterate the importance of encrypting all sensitive data not just during transmission (TLS/HTTPS) but also when it's stored in databases, file systems, or backups (at rest). Use strong encryption algorithms and secure key management practices.
- DDoS Protection: Implement distributed denial-of-service (DDoS) protection measures. This can involve cloud provider services, specialized DDoS mitigation tools, or configurations within your API Gateway to absorb or filter malicious traffic before it reaches your backend services.
- OWASP API Security Top 10: Familiarize your development and security teams with the OWASP API Security Top 10, a list of the most critical security risks to web APIs. Regularly audit your APIs against these vulnerabilities, which include:
- Broken Object Level Authorization
- Broken User Authentication
- Excessive Data Exposure
- Lack of Resources & Rate Limiting
- Broken Function Level Authorization
- Mass Assignment
- Security Misconfiguration
- Injection
- Improper Assets Management
- Insufficient Logging & Monitoring
- Runtime API Security: Consider specialized API security platforms that offer real-time threat detection, anomaly detection, and behavior analysis to identify and block attacks that bypass traditional WAFs or are unknown vulnerabilities (zero-day exploits).
- Secrets Management: Use dedicated secrets management solutions (e.g., HashiCorp Vault, AWS Secrets Manager, Azure Key Vault) to securely store and access API keys, database credentials, and other sensitive configurations.
The Future of APIs: Trends and Evolution
The api landscape is constantly evolving, driven by new technologies and changing architectural paradigms.
- Event-Driven APIs (Webhooks, AsyncAPI): Beyond traditional request/response models, event-driven APIs allow systems to react to events as they happen.
- Webhooks: Enable real-time notifications, where an api sends data to a pre-registered URL when a specific event occurs (e.g., "new order placed").
- AsyncAPI: A specification for describing event-driven architectures, similar to OpenAPI for REST APIs. It defines messages, channels, and protocols for asynchronous communication.
- GraphQL vs. REST: While REST remains dominant, GraphQL offers an alternative query language for APIs.
- GraphQL: Allows clients to request precisely the data they need, avoiding over-fetching or under-fetching. It consolidates multiple endpoints into a single endpoint, reducing network calls. It's often favored for mobile applications or complex frontends.
- REST: Still excellent for resource-oriented APIs, simpler use cases, and when caching and standardized HTTP methods are critical.
- AI-Powered API Gateways and Management: The integration of Artificial Intelligence and Machine Learning into API Gateway and management platforms is a growing trend. This enables:
- Intelligent Traffic Management: AI can optimize routing, load balancing, and auto-scaling based on predicted traffic patterns.
- Enhanced Security: AI can detect anomalous behavior, identify sophisticated threats, and adapt security policies in real-time.
- Automated API Generation and Discovery: AI could potentially assist in generating OpenAPI specifications or even suggesting new api designs based on data patterns.
- Personalized API Consumption: Tailoring API responses or access based on user behavior and preferences.
- Platforms like APIPark are at the forefront of this trend, integrating AI model invocation directly into their gateway capabilities, showcasing the convergence of AI and api gateway technology.
- API Mesh: An emerging architectural pattern for managing and connecting APIs in complex, distributed environments, particularly within large enterprises or across multiple clouds. It creates a unified fabric for API consumption and governance.
By staying abreast of these emerging trends, organizations can position their api strategy for future growth and innovation.
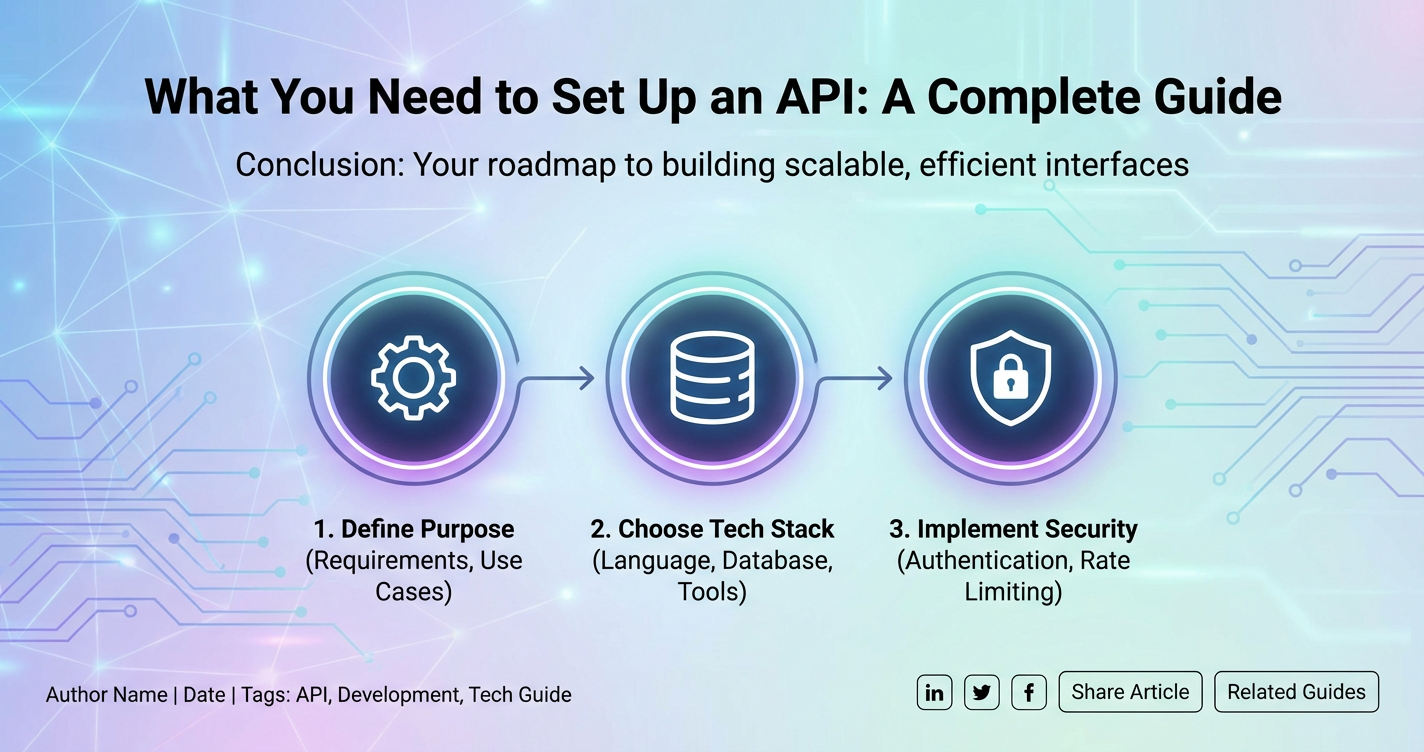
Conclusion: The Enduring Value of Well-Crafted APIs
Setting up an api is a multi-faceted endeavor that spans conceptualization, meticulous design, rigorous development, strategic deployment, and continuous management. It is a journey that requires careful planning, adherence to best practices, and a commitment to security and user experience at every stage. We have traversed the landscape from understanding the fundamental role of an api as the connective tissue of the digital world to the intricacies of designing a coherent OpenAPI specification, implementing robust code, and finally, deploying and governing your api with the aid of powerful tools like an API gateway.
The emphasis on a design-first approach, leveraging specifications like OpenAPI, ensures that your api is not just functional but also intuitive, well-documented, and consumable. The choice of technology stack, adherence to coding best practices, and a vigilant focus on security—from transport layer encryption to input validation and the advanced capabilities of an API Gateway—are all critical ingredients for long-term success. Furthermore, the strategic use of an API Gateway, such as the innovative APIPark solution, stands out as a pivotal element in centralizing control, enhancing security, optimizing performance, and simplifying the management of your api ecosystem, especially in the era of AI integration.
Ultimately, a well-crafted api transcends its technical components; it becomes a catalyst for innovation, a driver of business value, and a foundation for seamless digital experiences. It empowers developers, fosters partnerships, and unlocks new avenues for growth. The work doesn't stop once the api is live; continuous monitoring, feedback loops, and an adaptive approach to evolution are essential to ensure its enduring relevance and sustained success. By embracing the principles and practices outlined in this comprehensive guide, you are not merely setting up an api; you are building a vital artery in the pulsating heart of the digital economy, ready to connect, communicate, and create value for years to come.
Frequently Asked Questions (FAQs)
1. What is the most critical first step when starting to set up an API? The most critical first step is to clearly define the API's purpose and scope. This involves identifying the problem it solves, its target audience, the resources it will expose, and the operations it will support. Without a clear understanding of these foundational elements, the design and implementation phases can become unfocused and lead to an API that doesn't meet its intended goals or is difficult for consumers to understand and use.
2. Why is using OpenAPI Specification so important for API setup? The OpenAPI Specification (formerly Swagger) is crucial because it provides a standardized, machine-readable format to describe your API's capabilities. This "documentation-first" approach acts as a clear contract between API providers and consumers. Its benefits include automatic generation of interactive documentation (like Swagger UI), client SDKs, server stubs, and test cases, all of which accelerate development, improve consistency, reduce errors, and enhance the overall developer experience significantly.
3. What is an API Gateway, and why do I need one? An API Gateway is a single entry point for all client requests to your backend APIs. It sits between the client and your services, handling common cross-cutting concerns like authentication, authorization, rate limiting, routing, caching, and monitoring. You need an API Gateway to centralize these functions, offloading them from individual APIs, which enhances security, improves performance, simplifies API management, and provides better overall control and visibility, especially for complex microservices architectures or a large number of APIs.
4. How can I ensure my API is secure from the outset? Ensuring API security requires a multi-layered approach from the design phase. Key steps include always enforcing HTTPS (TLS/SSL) for all communication, rigorously validating and sanitizing all input data to prevent injection attacks, implementing robust authentication (e.g., OAuth 2.0, JWT) and authorization (e.g., RBAC) mechanisms, properly configuring CORS, storing sensitive data securely (encrypted at rest and in transit), and keeping all dependencies updated. Regular security audits and following guidelines like the OWASP API Security Top 10 are also vital.
5. How do I handle changes to my API without breaking existing integrations? Handling changes to your API gracefully is managed through API versioning. The most common method is URL path versioning (e.g., /v1/products, /v2/products). When introducing breaking changes, a new major version should be released. For non-breaking additions or minor fixes, you can often update within the current version. It's crucial to have a clear deprecation policy for older versions, communicate changes well in advance to consumers, and provide comprehensive documentation for all versions to ensure a smooth transition.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.