Where to Write API Request Headers: The Definitive Guide
In the intricate world of modern web communication and distributed systems, the humble API request header stands as an unsung hero, a silent messenger carrying vital metadata that shapes how requests are processed, authenticated, and understood. From dictating the format of a response to carrying authentication credentials, headers are fundamental to the robustness, security, and interoperability of any API interaction. Understanding where and how to write these headers is not merely a technical detail; it's a critical skill that empowers developers to build more efficient, secure, and resilient applications.
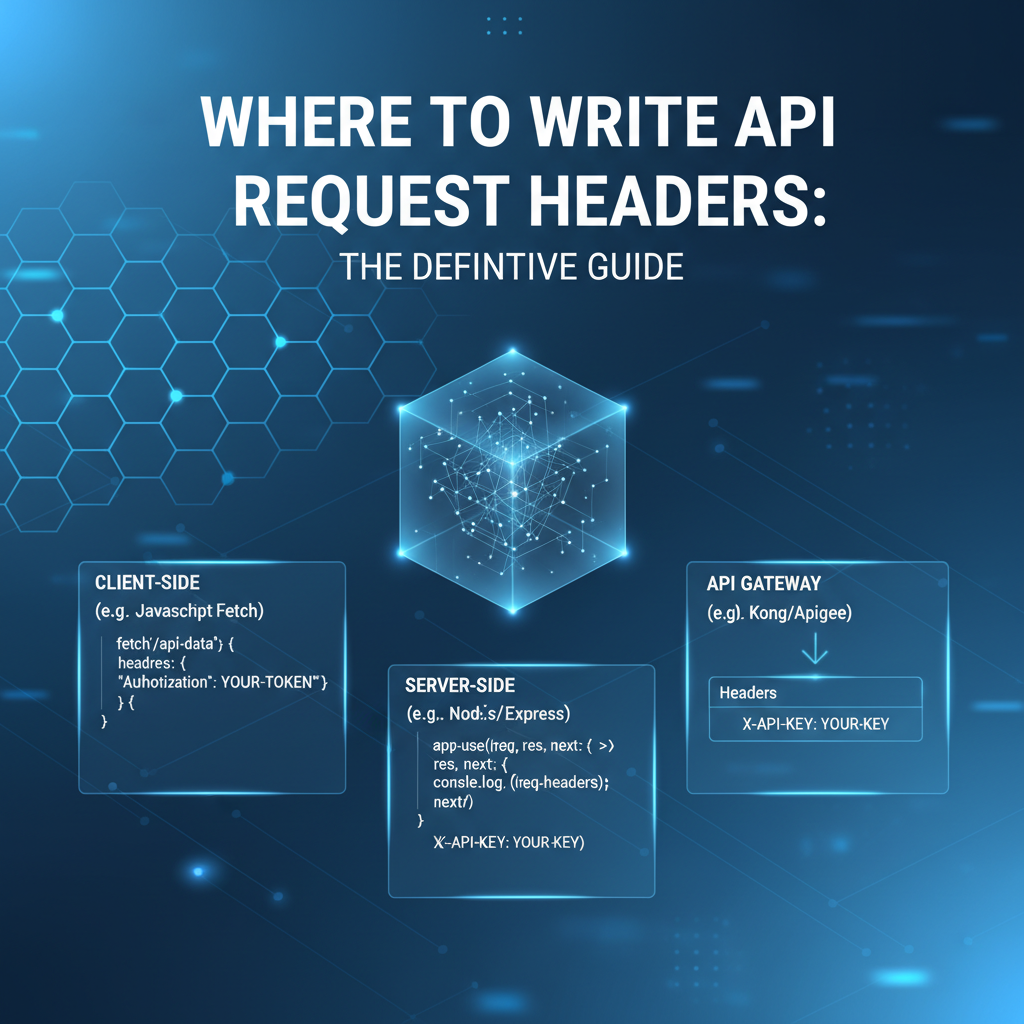
This definitive guide delves deep into the multifaceted landscape of API request headers. We will embark on a comprehensive journey, exploring their foundational principles, dissecting their structure and purpose, and meticulously charting every significant location and context where they can be authored, manipulated, and interpreted. From the client-side developer constructing a request in JavaScript or Python, to the server-side architect configuring an API Gateway or web server, and even to the underlying network infrastructure, headers are a constant, crucial element. By the end of this extensive exploration, you will possess a profound understanding of how to master API request headers, enabling you to design, implement, and troubleshoot API-driven systems with unparalleled confidence and expertise.
1. The Foundational Role of API Request Headers
At its core, an API (Application Programming Interface) provides a set of rules and definitions for how applications can communicate with each other. When an application interacts with an API, it typically sends an HTTP request, and this request is much more than just a URL and a body of data. It's encapsulated within a structured message, and a significant part of that structure is dedicated to headers. These headers are key-value pairs that precede the actual request body, offering metadata about the request itself, the client making it, and the type of response it expects. They are essential for a multitude of reasons, touching upon virtually every aspect of a robust API interaction.
Imagine sending a physical letter: the main content is the request body, but the envelope, the stamps, the return address, and special instructions like "Confidential" or "Urgent" are all analogous to headers. They provide context and directives without being part of the primary message content. Without them, the letter might never reach its destination, or it might be mishandled upon arrival. Similarly, without appropriate API request headers, a server might reject a request outright, respond with an incorrect format, or compromise security by allowing unauthorized access.
1.1. What are API Request Headers?
An API request header is a field that provides information about the request, the client, or the server. Each header consists of a case-insensitive name followed by a colon (:) and then its value. For example, Content-Type: application/json tells the server that the request body contains data formatted as JSON. These headers are part of the HTTP message format, which is the backbone of most web APIs (RESTful APIs predominantly rely on HTTP). While HTTP also defines response headers, our focus here is exclusively on the headers sent from the client to the server.
The HTTP specification defines a set of standard headers for various purposes, but developers also have the flexibility to define custom headers, often prefixed with X- (though this convention is less strictly adhered to in newer designs) or using application-specific prefixes. The primary goal of any header is to convey crucial information that helps the server process the request accurately and securely. This information can range from the client's preferred language to its authentication credentials, or even specifics about how the server should cache the response.
1.2. Why are API Request Headers Important?
The importance of API request headers cannot be overstated. They serve several critical functions that underpin the reliability, security, and efficiency of modern applications:
- Authentication and Authorization: Perhaps one of the most critical roles, headers carry credentials (like API keys, JWTs, or OAuth tokens) that authenticate the client and authorize its access to specific resources. Without these, unauthorized access would be rampant.
- Content Negotiation: Headers allow clients to specify what type of content they are sending (
Content-Type) and what type of content they prefer to receive (Accept). This enables APIs to support multiple data formats (e.g., JSON, XML) and clients to choose the most suitable one. - Caching Control: Clients can suggest caching directives (
Cache-Control) to proxies and servers, influencing how responses should be cached, which can significantly improve performance by reducing redundant data transfers. - Client Identification and Context: Headers like
User-Agentidentify the client software, whileRefererindicates the previous page, providing valuable context for analytics, logging, and security. - Security Features: Beyond authentication, headers can help mitigate certain types of attacks, although many security-focused headers are typically response headers. However, request headers like
Originplay a crucial role in CORS (Cross-Origin Resource Sharing) mechanisms, preventing unauthorized cross-origin requests. - Request Transformation and Routing: In complex architectures involving API Gateways and load balancers, headers can guide how requests are transformed, routed, and processed across various backend services. They can carry correlation IDs for tracing or flags for specific backend logic.
- API Versioning: Some API designs utilize headers to specify the desired API version, allowing clients to interact with a specific iteration of the API without changing the URL path.
- Conditional Requests: Headers like
If-Modified-SinceorIf-None-Matchallow clients to make requests conditionally, only retrieving new data if the resource has changed, saving bandwidth and processing power.
Without these capabilities, API interactions would be vastly less flexible, less secure, and much harder to manage and scale. Headers are the invisible scaffolding that supports the entire edifice of API communication, making their proper handling and placement a cornerstone of robust software development.
2. Setting Headers on the Client-Side: Initiating the Request
The journey of an API request header begins at the client, the application or script that initiates the communication. Whether it's a web browser, a command-line utility, or a sophisticated application written in a programming language, the client is responsible for packaging the request, including all necessary headers, before sending it across the network. The methods for setting these headers vary significantly depending on the client environment and the tools or libraries being used. Understanding these differences is crucial for any developer interacting with an API.
2.1. Web Browsers (JavaScript Fetch API, XMLHttpRequest)
In the context of modern web applications, JavaScript running in a browser is a primary client for making API requests. The two dominant mechanisms for this are the Fetch API and the older XMLHttpRequest (XHR) object. Both provide straightforward ways to attach headers to outgoing requests, but they operate with certain browser-imposed security restrictions, particularly regarding Cross-Origin Resource Sharing (CORS).
2.1.1. Using the Fetch API
The Fetch API offers a powerful and flexible way to make network requests, built on Promises, making it easier to work with asynchronous operations. Headers are typically provided as part of the init object passed to the fetch() function.
Example with fetch:
const apiUrl = 'https://api.example.com/data';
const authToken = 'your_jwt_token_here';
const requestBody = {
name: 'John Doe',
email: 'john.doe@example.com'
};
fetch(apiUrl, {
method: 'POST',
headers: {
'Content-Type': 'application/json',
'Authorization': `Bearer ${authToken}`,
'Accept-Language': 'en-US,en;q=0.9',
'X-Custom-App-Id': 'my-web-app-v1' // Example custom header
},
body: JSON.stringify(requestBody)
})
.then(response => {
if (!response.ok) {
throw new Error(`HTTP error! status: ${response.status}`);
}
return response.json();
})
.then(data => {
console.log('Success:', data);
})
.catch(error => {
console.error('Error:', error);
});
In this fetch example, headers are passed as a plain JavaScript object within the init configuration. The browser automatically handles certain headers (like Host or Content-Length) and also enforces security policies, notably CORS. If the API is on a different origin than the web page, the browser will send an Origin header and potentially a preflight OPTIONS request with Access-Control-Request-Headers to check if the server permits the custom headers (X-Custom-App-Id in this case) and method.
2.1.2. Using XMLHttpRequest (XHR)
While Fetch is the modern standard, XMLHttpRequest remains widely used, especially in older codebases or when more fine-grained control over the request lifecycle (like progress events) is needed. Headers are set using the setRequestHeader() method after open() but before send().
Example with XMLHttpRequest:
const xhr = new XMLHttpRequest();
const apiUrl = 'https://api.example.com/data';
const authToken = 'another_jwt_token';
const requestBody = {
product: 'Widget A',
quantity: 5
};
xhr.open('PUT', apiUrl, true); // true for asynchronous
xhr.setRequestHeader('Content-Type', 'application/json');
xhr.setRequestHeader('Authorization', `Bearer ${authToken}`);
xhr.setRequestHeader('If-None-Match', '"some-etag-value"'); // Example conditional header
xhr.onload = function() {
if (xhr.status >= 200 && xhr.status < 300) {
console.log('Success:', JSON.parse(xhr.responseText));
} else {
console.error('Error:', xhr.status, xhr.statusText);
}
};
xhr.onerror = function() {
console.error('Network Error');
};
xhr.send(JSON.stringify(requestBody));
Both Fetch and XHR provide similar capabilities for setting headers. The key takeaway for browser-based clients is the inherent security context: browsers automatically add certain headers and restrict others to prevent malicious activities. Developers must be mindful of CORS policies, as custom headers or non-standard methods often trigger preflight requests, and the API server must be configured to allow these specific headers and origins.
2.2. Command-Line Tools (cURL)
For quick tests, debugging, or scripting API interactions without writing a full application, cURL is an indispensable command-line tool. It offers extensive control over every aspect of an HTTP request, including headers. The -H or --header flag is used to specify headers.
Example with cURL:
# Basic GET request with an Authorization header
curl -X GET \
-H "Authorization: Bearer abcdef12345" \
-H "Accept: application/json" \
"https://api.example.com/users/123"
# POST request with Content-Type and a custom header
curl -X POST \
-H "Content-Type: application/json" \
-H "X-Client-ID: my-cli-tool" \
-d '{ "name": "Jane", "job": "Developer" }' \
"https://api.example.com/create-user"
# Request with multiple Accept-Encoding values (for compression)
curl -H "Accept-Encoding: gzip, deflate, br" "https://api.example.com/large-data"
The cURL tool provides a direct and explicit way to specify headers, making it incredibly powerful for testing and understanding how an API responds to different header configurations. Each -H flag defines a single header, and its value should be properly quoted if it contains spaces or special characters. cURL sends exactly what you tell it to, making it an excellent utility for isolating header-related issues.
2.3. Programming Languages and Libraries
Beyond web browsers and command-line tools, developers frequently interact with APIs from backend services, desktop applications, or mobile apps written in various programming languages. Each language typically offers its own HTTP client libraries, which abstract away the low-level details of socket communication and HTTP protocol, providing convenient ways to manage requests and headers.
2.3.1. Python (requests library)
Python's requests library is renowned for its simplicity and elegance in making HTTP requests. Headers are passed as a dictionary to the headers parameter of the request methods (get, post, put, etc.).
Example with Python requests:
import requests
import json
api_url = 'https://api.example.com/items'
api_key = 'your_secret_api_key'
payload = {'item_name': 'New Gadget', 'price': 99.99}
# Define headers as a dictionary
headers = {
'Content-Type': 'application/json',
'Accept': 'application/json',
'X-API-Key': api_key, # Common for API key authentication
'User-Agent': 'Python-Requests/MyCoolApp'
}
try:
response = requests.post(api_url, headers=headers, data=json.dumps(payload))
response.raise_for_status() # Raise an exception for HTTP errors (4xx or 5xx)
print("Success:", response.json())
except requests.exceptions.HTTPError as err:
print(f"HTTP error occurred: {err}")
except requests.exceptions.RequestException as err:
print(f"Other request error occurred: {err}")
The requests library makes header management intuitive. The dictionary structure maps directly to header key-value pairs, allowing for clear and organized definition of all necessary metadata. This approach is highly flexible, supporting dynamic header generation based on application logic or user input.
2.3.2. Node.js (axios, built-in http/https modules)
In the Node.js ecosystem, axios is a popular promise-based HTTP client that simplifies API interactions. Alternatively, Node.js provides built-in http and https modules for lower-level control.
Example with Node.js axios:
const axios = require('axios');
const apiUrl = 'https://api.example.com/status';
const sessionId = 'session_token_123';
const headers = {
'Authorization': `Bearer ${sessionId}`,
'Accept': 'text/plain',
'X-Request-ID': 'unique-trace-id-456'
};
axios.get(apiUrl, { headers: headers })
.then(response => {
console.log('Status:', response.data);
})
.catch(error => {
if (error.response) {
console.error('Error response:', error.response.status, error.response.data);
} else if (error.request) {
console.error('No response received:', error.request);
} else {
console.error('Error setting up request:', error.message);
}
});
With axios, headers are passed within an object in the configuration parameter, similar to Python's requests. This consistency across popular libraries makes it easier for developers to transition between languages. The built-in http.request or https.request functions also accept a headers object, offering more granular control for specific use cases, though they are generally more verbose.
2.3.3. Java (HttpClient)
Java's modern HttpClient (introduced in Java 11) provides a fluent API for making HTTP requests. Headers are built using HttpRequest.Builder methods.
Example with Java HttpClient:
import java.net.URI;
import java.net.http.HttpClient;
import java.net.http.HttpRequest;
import java.net.http.HttpResponse;
import java.time.Duration;
public class ApiClient {
public static void main(String[] args) {
HttpClient client = HttpClient.newBuilder()
.version(HttpClient.Version.HTTP_2)
.connectTimeout(Duration.ofSeconds(10))
.build();
String apiKey = "my_java_app_key";
String userId = "user-789";
String requestBody = "{\"message\": \"Hello from Java!\"}";
HttpRequest request = HttpRequest.newBuilder()
.uri(URI.create("https://api.example.com/messages"))
.header("Content-Type", "application/json")
.header("X-API-Key", apiKey)
.header("X-User-Id", userId)
.POST(HttpRequest.BodyPublishers.ofString(requestBody))
.build();
try {
HttpResponse<String> response = client.send(request, HttpResponse.BodyHandlers.ofString());
System.out.println("Status code: " + response.statusCode());
System.out.println("Response body: " + response.body());
} catch (Exception e) {
System.err.println("Request failed: " + e.getMessage());
}
}
}
Java's HttpClient allows for chaining header() calls on the HttpRequest.Builder to add multiple headers, resulting in readable and explicit request construction. This pattern is common in strongly typed languages, ensuring that the request is fully configured before it's built and sent.
2.3.4. Go (net/http)
Go's standard library includes the net/http package, which provides robust capabilities for HTTP client and server implementations. Headers are set on the Header field of an http.Request object.
Example with Go net/http:
package main
import (
"bytes"
"fmt"
"io/ioutil"
"net/http"
)
func main() {
apiUrl := "https://api.example.com/reports"
reportId := "daily-sales-summary"
jwtToken := "eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9..." // example JWT
requestBody := []byte(`{"period": "today", "format": "pdf"}`)
req, err := http.NewRequest("POST", apiUrl, bytes.NewBuffer(requestBody))
if err != nil {
fmt.Printf("Error creating request: %v\n", err)
return
}
// Set headers directly on the Request.Header map
req.Header.Set("Content-Type", "application/json")
req.Header.Set("Authorization", "Bearer "+jwtToken)
req.Header.Set("X-Report-ID", reportId) // Custom header
client := &http.Client{}
resp, err := client.Do(req)
if err != nil {
fmt.Printf("Error sending request: %v\n", err)
return
}
defer resp.Body.Close()
body, err := ioutil.ReadAll(resp.Body)
if err != nil {
fmt.Printf("Error reading response body: %v\n", err)
return
}
fmt.Printf("Response Status: %s\n", resp.Status)
fmt.Printf("Response Body: %s\n", body)
}
Go's net/http package provides a low-level but highly flexible way to construct HTTP requests. By creating an http.Request object, developers gain direct access to its Header field, which is a map[string][]string, allowing for multiple values per header if needed (though typically only one is used for most request headers). The Set method simplifies adding or overwriting a single header value.
2.3.5. Ruby (net/http)
Ruby's standard library also includes net/http for making HTTP requests. Headers are set on the request object (e.g., Net::HTTP::Post, Net::HTTP::Get) as if they were hash keys.
Example with Ruby net/http:
require 'net/http'
require 'uri'
require 'json'
uri = URI.parse("https://api.example.com/orders")
api_token = "ruby_api_token_xyz"
order_data = {
item: "Book",
quantity: 2,
customer_id: 123
}
http = Net::HTTP.new(uri.host, uri.port)
http.use_ssl = true # Use SSL for HTTPS
request = Net::HTTP::Post.new(uri.path, 'Content-Type' => 'application/json')
request['Authorization'] = "Token token=#{api_token}" # Another common auth header style
request['X-Ruby-Client'] = 'MyRubyApp/1.0' # Custom client ID
request.body = order_data.to_json
response = http.request(request)
puts "Response Code: #{response.code}"
puts "Response Body: #{response.body}"
In Ruby, headers are assigned directly to the request object using a hash-like syntax. This concise syntax allows for easy definition of headers either during the request object instantiation or by assigning them later, prior to sending the request.
2.4. API Testing Tools (Postman, Insomnia)
Dedicated API testing tools like Postman and Insomnia are designed to simplify API development, testing, and documentation. They provide intuitive graphical user interfaces for constructing requests, including a dedicated section for managing headers.
2.4.1. Postman
Postman is a ubiquitous tool in the API development lifecycle. It features a "Headers" tab where users can add, modify, or remove headers using a simple key-value pair interface.
Key Features for Headers in Postman:
- Key-Value Input: Easily type header names and values.
- Built-in Headers: Postman intelligently suggests common headers (e.g.,
Content-Type,Authorization). - Environment Variables: Headers can leverage environment variables or global variables, allowing dynamic values (e.g., an
Authorizationtoken that changes frequently). This is particularly useful for workflows involving multiple requests where a token obtained from one request needs to be used in subsequent requests. - Pre-request Scripts: For more complex scenarios, JavaScript can be used in "Pre-request Scripts" to programmatically generate and set headers based on logic, calculations, or external data. For instance, generating a signature header or a timestamp.
- Collection/Folder Level Headers: Headers can be defined at the collection or folder level, applying them automatically to all requests within that scope, reducing redundancy.
2.4.2. Insomnia
Insomnia, another popular API client, offers similar robust features for header management, emphasizing a clean and user-friendly interface.
Key Features for Headers in Insomnia:
- Dedicated Headers Tab: A clear interface for adding headers.
- Dynamic Variables: Insomnia's powerful environment and template variables can be used to inject dynamic values into headers, similar to Postman. This is excellent for handling authentication tokens, API keys, or other data that changes across different environments.
- Request Chaining: Headers can be automatically populated from previous responses, streamlining complex workflows.
- Plugins: Insomnia supports plugins that can extend its functionality, including those for generating specific types of headers (e.g., OAuth 1.0 signatures).
Both Postman and Insomnia are invaluable for developers because they allow for rapid iteration and testing of API requests with different header configurations without needing to write or modify code. They make it easy to verify that an API behaves as expected under various conditions, especially concerning authentication, content negotiation, and custom header processing.
3. Modifying and Adding Headers on the Server-Side: Intermediary Layers
Once a request leaves the client, it often doesn't go directly to the ultimate backend service. Instead, it traverses various intermediary layers designed to enhance security, performance, routing, and management. These layers—web servers, load balancers, and most notably, API Gateways—have the capability to inspect, modify, add, or remove headers from the incoming request before forwarding it to the target backend. This server-side header manipulation is critical for implementing cross-cutting concerns that shouldn't be handled by every individual microservice.
3.1. Web Servers (Nginx, Apache HTTP Server)
Common web servers like Nginx and Apache are often deployed as reverse proxies in front of application servers. They can receive client requests, add or modify headers, and then forward those requests to the appropriate backend. This capability is extensively used for tasks like injecting client IP addresses, host information, or security headers.
3.1.1. Nginx
Nginx is a high-performance web server, reverse proxy, and load balancer. Its proxy_set_header directive is the primary tool for manipulating request headers forwarded to an upstream server.
Example with Nginx proxy_set_header:
http {
upstream backend_app {
server 127.0.0.1:8080; # The actual application server
}
server {
listen 80;
server_name api.example.com;
location / {
proxy_pass http://backend_app;
# Forward the original host header
proxy_set_header Host $host;
# Forward the client's real IP address
proxy_set_header X-Real-IP $remote_addr;
# Forward the client's IP, potentially through multiple proxies
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
# Forward the original protocol (HTTP or HTTPS)
proxy_set_header X-Forwarded-Proto $scheme;
# Add a custom header to all requests reaching the backend
proxy_set_header X-Nginx-Processed "true";
# Remove a header if it's not needed by the backend
# proxy_hide_header Authorization; # Example: remove auth if handled by Nginx
}
}
}
In Nginx, proxy_set_header allows for both overriding existing headers (like Host) and adding new ones. Variables like $remote_addr, $host, and $scheme are Nginx's built-in variables that capture information about the client connection and the request itself. This capability is vital for backend applications that need to know the original client's IP, the requested host, or whether the original request was secure (HTTPS).
3.1.2. Apache HTTP Server
Apache, like Nginx, can also function as a reverse proxy. Its mod_proxy and mod_headers modules are used to manipulate request headers.
Example with Apache RequestHeader:
<VirtualHost *:80>
ServerName api.example.com
ProxyRequests Off
ProxyPreserveHost On
<Proxy *>
Order deny,allow
Allow from all
</Proxy>
ProxyPass / http://127.0.0.1:8080/
ProxyPassReverse / http://127.0.0.1:8080/
# Add or modify request headers before forwarding to the backend
RequestHeader set X-Forwarded-Proto "http" env=HTTPS off
RequestHeader set X-Forwarded-Proto "https" env=HTTPS on
RequestHeader set X-Real-IP "%{REMOTE_ADDR}s"
RequestHeader append X-Apache-Processed "true"
# Remove a header (e.g., if you process it at the proxy)
# RequestHeader unset Authorization
</VirtualHost>
Apache's RequestHeader directive offers set, add, append, and unset actions to control headers. It also supports using server variables (like %{REMOTE_ADDR}s) to dynamically generate header values. Similar to Nginx, this allows Apache to inject crucial client and proxy information into the request before it reaches the backend application.
3.2. Load Balancers
Load balancers distribute incoming network traffic across multiple servers to ensure high availability and reliability. Beyond simple traffic distribution, many modern load balancers, whether hardware-based (like F5 BIG-IP) or software-based (like HAProxy, AWS ELB/ALB, Google Cloud Load Balancer), also offer features to manipulate HTTP headers. This is particularly important for propagating client information and managing session stickiness.
Common Headers Added/Modified by Load Balancers:
X-Forwarded-For: This header is perhaps the most commonly added by load balancers. It contains the original IP address of the client that made the request. If multiple proxies or load balancers are in the path, they append their own IP addresses to this header, creating a comma-separated list.X-Forwarded-Proto: Indicates the protocol (HTTP or HTTPS) that the client used to connect to the load balancer. This is crucial for backend services that need to generate absolute URLs or enforce HTTPS redirects, as they might only see HTTP traffic from the load balancer.X-Forwarded-Host: Specifies the original host requested by the client. Useful when the load balancer or proxy handles multiple domain names.Via: This header is added by proxies, indicating the intermediate proxies through which the request has passed. It includes the protocol version and the proxy's hostname.True-Client-IP: Some cloud providers or CDNs (e.g., Cloudflare) might use a custom header likeTrue-Client-IPto provide a single, clean client IP address, especially in cases whereX-Forwarded-Forcan become a long, comma-separated string.
The manipulation of these headers by load balancers is largely automated and configured through their respective platforms. Developers consuming API requests from behind a load balancer must be aware of these headers to correctly identify the original client and its connection context.
3.3. API Gateways
An API Gateway is a central component in modern microservices architectures. It acts as a single entry point for a group of microservices, handling concerns like authentication, authorization, rate limiting, request routing, caching, and request transformation, which includes extensive header manipulation. The API Gateway is arguably the most sophisticated layer for managing API request headers on the server-side, offering granular control over header addition, modification, and removal based on defined policies and routing rules.
Why API Gateways are Crucial for Header Management:
- Centralized Authentication: An API Gateway can validate authentication tokens (like JWTs or API keys) provided in request headers. After successful validation, it can remove the sensitive
Authorizationheader and instead inject internal headers (e.g.,X-User-ID,X-User-Roles) carrying user context to the backend services. This offloads authentication logic from individual microservices. - Request Transformation: Gateways can normalize headers, ensure consistent casing, or translate custom client-specific headers into a standard format expected by backend services. They can add trace IDs (
X-Request-ID,X-Correlation-ID) for distributed tracing across microservices. - Routing and Versioning: Headers can influence how requests are routed to different versions of a service or different backend clusters. For example, a
X-Api-Version: v2header might direct a request to a newer service implementation. - Security Policies: Beyond authentication, gateways can enforce security policies by inspecting headers, blocking requests that contain suspicious headers, or adding headers to prevent certain types of attacks.
- Rate Limiting and Analytics: Client identification headers (e.g.,
X-Client-ID) can be extracted by the gateway to enforce rate limits or gather analytics on API usage per client. - Multi-tenancy: In multi-tenant systems, a gateway can extract tenant identifiers from headers and inject them as internal headers for backend services to filter data or apply tenant-specific logic.
Many API Gateways offer declarative configurations or even scripting capabilities (e.g., Lua in Kong Gateway, policies in Apigee, Ambassador) to define these header manipulation rules. This allows for powerful, centralized control without modifying backend service code.
For instance, an advanced platform like APIPark (Open Source AI Gateway & API Management Platform) exemplifies how an API Gateway can be instrumental in managing headers. APIPark is designed to provide unified management for authentication and request transformation, among other features, specifically for AI and REST services. It standardizes the request data format across various AI models, meaning that a client might send a generic Content-Type header, but APIPark can transform it into the specific Content-Type or add other necessary headers required by a particular AI model's API. When integrating over 100 AI models, APIPark can automatically add, modify, or remove headers to ensure seamless interoperability and consistent authentication practices. For example, it might take a single Authorization header from the client and, based on its internal routing logic, inject a specific vendor's x-api-key header when calling OpenAI, or a different x-subscription-key for an Azure AI service. This greatly simplifies client-side development, as clients only need to conform to APIPark's unified API format, while the gateway handles the complexity of backend-specific header requirements, contributing significantly to simplified AI usage and reduced maintenance costs. Its end-to-end API lifecycle management capabilities ensure that header policies are consistently applied from design to invocation.
3.4. Service Meshes
In a microservices architecture, a service mesh (like Istio, Linkerd, or Consul Connect) provides a dedicated infrastructure layer for handling service-to-service communication. While not directly facing external clients, service meshes operate at a layer below the application code and can perform header manipulation for internal traffic.
Header Manipulation in Service Meshes:
- Distributed Tracing: Service meshes automatically inject and propagate tracing headers (e.g.,
X-B3-TraceId,X-B3-SpanIdfor Zipkin, ortraceparentfor W3C Trace Context) into requests as they flow between services. This allows developers to visualize and debug the path of a request through a complex microservices graph. - Traffic Routing: Headers can be used by the service mesh to direct traffic. For example, an
X-Canary: trueheader might route a request to a canary deployment of a service for A/B testing or gradual rollout. - Authentication/Authorization: While less common for full authentication (which is often handled by an API Gateway), service meshes can enforce authorization policies based on headers, ensuring that only authorized services can communicate.
The header manipulation in a service mesh is often transparent to the application developer, happening at the proxy level (sidecar proxies like Envoy) that intercepts all inbound and outbound traffic for a service. This significantly reduces boilerplate code in microservices and enforces consistency across the entire system.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
4. Common API Request Headers and Their Use Cases
Understanding where to write headers is only half the battle; knowing which headers to write and why is equally important. HTTP defines a vast array of standard headers, and developers frequently extend these with custom ones. Here, we delve into the most common and crucial API request headers, categorizing them by their primary function and illustrating their typical use cases.
4.1. Authentication Headers
These headers carry credentials or tokens that identify the client and prove its authorization to access protected resources. They are paramount for securing APIs.
Authorization: This is the most common header for sending authentication credentials. Its value typically starts with a scheme, followed by the actual token.Authorization: Basic <base64_encoded_username:password>: Used for Basic Authentication, where credentials are Base64 encoded.Authorization: Bearer <token>: The de-facto standard for token-based authentication (e.g., OAuth 2.0 access tokens, JWTs). The<token>is typically an opaque string or a JSON Web Token.Authorization: ApiKey <key>orX-API-Key: <key>: WhileApiKeyis less standard as anAuthorizationscheme, many APIs use a customX-API-Keyheader for simple API key authentication.- Use Cases: Securing endpoints, identifying users or client applications, enforcing access control, validating permissions.
- Where Set: Client-side (web, mobile, backend apps, CLI tools), often managed or transformed by API Gateways.
Cookie: Used to send cookies previously received from the server. Cookies are stateful mechanisms that allow servers to remember client information across multiple requests.- Use Cases: Session management, personalization, tracking.
- Where Set: Automatically by web browsers, can be manually set by non-browser clients.
4.2. Content Negotiation Headers
These headers allow the client and server to agree on the format, language, and encoding of the request body and the desired response.
Content-Type: Specifies the media type of the request body (e.g.,application/json,application/xml,text/plain,application/x-www-form-urlencoded). This is critical for the server to correctly parse the incoming data.- Use Cases: Telling the server how to interpret the request payload, mandatory for POST/PUT requests with a body.
- Where Set: Client-side (where the request body is created).
Accept: Informs the server about the media types that the client is willing to accept in the response. The server should then choose one of the offered types and respond with it.- Example:
Accept: application/json, application/xml;q=0.9(client prefers JSON, but XML is acceptable with lower quality factor). - Use Cases: Requesting data in a specific format, API versioning (e.g.,
application/vnd.myapi.v1+json). - Where Set: Client-side.
- Example:
Accept-Encoding: Indicates the content encoding algorithms the client understands (e.g.,gzip,deflate,brfor Brotli). The server might compress the response body using one of these algorithms to reduce bandwidth.- Use Cases: Enabling compression for faster data transfer, reducing network latency.
- Where Set: Automatically by web browsers and many HTTP client libraries, can be manually specified.
Accept-Language: Communicates the human languages the client prefers for the response.- Example:
Accept-Language: en-US,en;q=0.9,fr;q=0.8(prefers US English, then general English, then French). - Use Cases: Internationalization (i18n), returning localized content.
- Where Set: Automatically by web browsers, can be manually specified by applications.
- Example:
4.3. Caching and Conditional Request Headers
These headers are used to optimize network communication by leveraging caching mechanisms and allowing for conditional requests, reducing redundant data transfers.
Cache-Control: Though primarily a response header, it can also be a request header to specify caching directives from the client. For example,Cache-Control: no-cachecan tell proxies or the server to re-validate a cached response, orCache-Control: max-age=0can force a fresh request.- Use Cases: Controlling how proxies and the server handle caching of the response.
- Where Set: Client-side, sometimes via JavaScript or HTTP client libraries.
If-Modified-Since: Makes the request conditional. The server should only respond with the resource if it has been modified since the date provided in this header. If not modified, the server responds with a304 Not Modified.- Use Cases: Efficiently retrieving updated data, reducing bandwidth.
- Where Set: Client-side, often automatically by browsers for cached resources.
If-None-Match: Similar toIf-Modified-Since, but uses anETag(Entity Tag) value. The server only responds if the currentETagof the resource doesn't match the one provided by the client.- Use Cases: Preventing redundant data transfer, ensuring data integrity when performing updates (e.g., optimistic concurrency).
- Where Set: Client-side, often used in conjunction with
ETagresponse header.
4.4. Client Information and Context Headers
These headers provide metadata about the client making the request, which can be useful for logging, analytics, security, or debugging.
User-Agent: Identifies the client software originating the request (e.g.,Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 Chrome/100.0.4896.75 Safari/537.36, orPython-Requests/2.27.1).- Use Cases: Logging client types, analytics, identifying bots, tailoring responses for specific browsers.
- Where Set: Automatically by browsers and most HTTP client libraries, can be manually overridden.
Referer: Contains the URL of the page that linked to the resource being requested.- Use Cases: Analytics, logging where traffic is coming from, basic security checks.
- Where Set: Automatically by web browsers, but typically omitted or stripped for security reasons by default in modern browsers when crossing origins.
Origin: Indicates the origin (scheme, host, and port) of the resource that initiated the request. Crucial for CORS.- Use Cases: CORS preflight requests, security checks to prevent cross-site request forgery (CSRF).
- Where Set: Automatically by web browsers for cross-origin requests.
4.5. Proxy and Forwarding Headers
These headers are typically added or modified by proxies, load balancers, or API Gateways to convey information about the original client or the path the request took.
X-Forwarded-For: Contains the original IP address of the client that made the request.- Use Cases: Backend services needing the true client IP for logging, security, or geolocation.
- Where Set: Load balancers, reverse proxies, API Gateways.
X-Forwarded-Proto: Indicates the protocol (HTTP or HTTPS) that the client used to connect to the proxy/load balancer.- Use Cases: Backend services to generate correct absolute URLs or enforce HTTPS.
- Where Set: Load balancers, reverse proxies, API Gateways.
X-Forwarded-Host: Specifies the original host requested by the client.- Use Cases: Backend services behind a proxy that handles multiple domain names.
- Where Set: Load balancers, reverse proxies, API Gateways.
4.6. Custom and Application-Specific Headers
Developers often define custom headers for application-specific metadata that doesn't fit into standard HTTP headers. These headers usually start with X- (e.g., X-Request-ID), although modern practice sometimes omits the X- prefix if the header is clearly application-specific and not intended to become a standard.
X-Request-ID/X-Correlation-ID: A unique identifier assigned to a request at its entry point, propagated through all downstream services.- Use Cases: Distributed tracing, debugging, correlating logs across microservices.
- Where Set: Client-side, API Gateways, service meshes.
Idempotency-Key: A unique key provided by the client for requests that should be idempotent (i.e., multiple identical requests have the same effect as a single request).- Use Cases: Preventing duplicate processing of payment requests, order submissions, etc., after network retries.
- Where Set: Client-side for specific idempotent operations.
X-API-Version: Used for header-based API versioning, allowing clients to specify which version of an API they wish to use.- Use Cases: Managing backward compatibility, phased rollouts of new API versions.
- Where Set: Client-side, often consumed by API Gateways for routing.
This overview illustrates the breadth of information that headers convey. Each header serves a distinct purpose, and their correct usage is vital for building functional, secure, and performant API interactions.
Table: Summary of Common API Request Headers and Their Typical Origins
| Header Name | Purpose | Typical Originator(s) | Example Value |
|---|---|---|---|
Authorization |
Client authentication and authorization credentials. | Client (browser, app, script) | Bearer eyJhbGci..., Basic dXNlcm5hbWU6cGFzc3dvcmQ= |
Content-Type |
Media type of the request body. | Client | application/json, application/x-www-form-urlencoded |
Accept |
Media types acceptable for the response. | Client | application/json, application/xml;q=0.9 |
Accept-Encoding |
Content encoding algorithms understood by the client. | Client (often auto-added by browser/lib) | gzip, deflate, br |
User-Agent |
Information about the client software. | Client (often auto-added by browser/lib) | Mozilla/5.0...Chrome/100, Python-Requests/2.27.1 |
X-Forwarded-For |
Original IP address of the client (when behind a proxy/load balancer). | Load Balancer, Reverse Proxy, API Gateway | 203.0.113.45, 192.168.1.1 |
X-Forwarded-Proto |
Original protocol (HTTP/HTTPS) of the client request. | Load Balancer, Reverse Proxy, API Gateway | https |
X-Request-ID |
Unique ID for request tracing across services. | Client, API Gateway, Service Mesh | a1b2c3d4e5f6g7h8 |
If-None-Match |
Conditional request: only fetch if ETag does not match. | Client (for caching/optimistic concurrency) | "686897696a7c876b7e" |
Idempotency-Key |
Unique key to ensure idempotent request processing. | Client (for specific API operations) | uuid-v4-generated-key |
Origin |
Origin of the request, used for CORS. | Client (browser, for cross-origin requests) | https://www.example.com |
Host |
The domain name of the server (automatically added). | Client (automatically added by HTTP client library), Reverse Proxy (proxy_set_header) |
api.example.com |
Connection |
Specifies connection control options (e.g., keep-alive). | Client (often auto-added/managed) | keep-alive |
Content-Length |
Size of the request body in bytes. | Client (automatically added when body is present) | 128 |
5. Best Practices and Considerations for API Request Headers
Mastering API request headers extends beyond merely knowing where and how to write them; it encompasses a set of best practices and critical considerations that ensure security, performance, interoperability, and maintainability. Ignoring these can lead to vulnerabilities, inefficient communication, or frustrating debugging sessions.
5.1. Security Considerations
Headers often carry sensitive information or are pivotal in security mechanisms. Their handling requires utmost care.
- Always Use HTTPS/TLS: This is the golden rule. All API requests, especially those containing
Authorizationheaders,X-API-Key, or any sensitive custom data, must be sent over HTTPS. TLS encrypts the entire HTTP message, including headers, preventing eavesdropping and man-in-the-middle attacks. Sending credentials over plain HTTP is akin to shouting your password in a crowded room. - Protect Authentication Tokens and API Keys:
- Never Hardcode: Authentication tokens and API keys should never be hardcoded directly into client-side JavaScript or source code that might be publicly exposed.
- Environment Variables: For server-side applications, use environment variables.
- Secure Storage: For client-side (e.g., mobile apps), use secure storage mechanisms provided by the OS. In web browsers, consider
HttpOnlycookies for session tokens (though these are response headers, they relate to how request headers are sent) or robust OAuth flows. - Short Lifespans: Use short-lived access tokens where possible, requiring periodic refreshing.
- Be Mindful of CORS and
OriginHeader: WhileOriginis automatically set by browsers, developers must correctly configure their API servers (or API Gateways) with appropriateAccess-Control-Allow-Originresponse headers. Misconfigurations can lead to either overly permissive policies (security risk) or overly restrictive ones (blocking legitimate clients). - Header Injection Prevention: Be cautious when constructing headers dynamically from user input. Malicious input could inject extra headers or modify existing ones. Always sanitize and validate any input used to build header values.
- Sensitive Data in Custom Headers: Avoid putting truly sensitive, unencrypted data (like full passwords or PII) directly into custom request headers. If such data must be transmitted, it belongs in the encrypted request body or via secure channels that guarantee end-to-end encryption.
- Logging Security: When logging API requests for debugging or auditing, be extremely careful not to log sensitive headers (like
Authorization) in plaintext. Mask or redact such information before writing to logs.
5.2. Performance Optimizations
Headers, while small individually, can impact performance at scale.
- Keep Headers Concise: Avoid sending unnecessary or overly verbose headers. Every byte counts, especially in high-volume APIs. While HTTP/2 introduces header compression (HPACK), minimizing header size remains a good practice.
- Leverage Caching Headers: Properly utilize
If-Modified-SinceandIf-None-Match(withETagresponse headers) to enable conditional requests. This reduces bandwidth by allowing the server to respond with a304 Not Modifiedif the client's cached version is still valid, preventing the re-transmission of the entire response body. - Use
Accept-Encoding: Ensure clients sendAccept-Encodingheaders (e.g.,gzip, deflate, br) and that servers are configured to respond with compressed content. This significantly reduces payload size. - HTTP/2 and HTTP/3 Benefits: These newer HTTP versions inherently offer performance benefits related to headers, including:
- Header Compression: HPACK (HTTP/2) and QPACK (HTTP/3) reduce redundant header data by using dynamic and static tables, significantly cutting down on bandwidth used by headers, especially for repeated requests.
- Multiplexing: Allows multiple requests and responses to share a single connection, reducing connection overhead.
5.3. Interoperability and Standards Adherence
For APIs to be widely adopted and easily consumed, they must be interoperable, meaning different clients and servers can communicate effectively.
- Adhere to HTTP Standards (RFCs): Whenever possible, use standard HTTP headers for their intended purpose. Reinventing the wheel with custom headers for functionalities already covered by existing standards can lead to confusion and integration challenges. Refer to the official RFCs for guidance.
- Case-Insensitivity (Mostly): HTTP header field names are case-insensitive by standard. However, consistency is a virtue. Stick to a common casing convention (e.g.,
Camel-CaselikeContent-Type) for clarity and to avoid potential issues with less forgiving implementations. - Avoid Non-Standard Custom Headers Where Standard Ones Exist: Before inventing
X-My-Auth-Token, consider ifAuthorization: BearerorX-API-Keyis more appropriate. Custom headers should be reserved for truly application-specific metadata. - Document Custom Headers: If custom headers are unavoidable, meticulously document their purpose, expected values, and any constraints in your API documentation. This is crucial for developers consuming your API.
5.4. Debugging and Troubleshooting
Headers are often the first place to look when an API request behaves unexpectedly.
- Inspect Headers with Tools: Use browser developer tools (Network tab),
cURLwith verbose output (-v), Postman/Insomnia, or network sniffers (like Wireshark) to inspect both request and response headers. This can quickly reveal missing, incorrect, or unexpected header values. - Logging: Implement comprehensive, but secure, logging of headers on the server-side, especially at entry points like API Gateways. This provides a trail of breadcrumbs for debugging authentication issues, content negotiation problems, or unexpected client behavior. Remember to redact sensitive information.
- Error Messages: Design API error messages to be informative about header-related issues. For example, a
401 Unauthorizedwith aWWW-Authenticateresponse header, or a406 Not Acceptableif theAcceptheader could not be fulfilled.
5.5. API Versioning with Headers
While URL path (/v1/users) or query parameters (?api-version=v1) are common for API versioning, headers offer an alternative approach.
AcceptHeader (Media Type Versioning): TheAcceptheader can include a custom media type that embeds the API version.Accept: application/vnd.myapi.v1+json- This approach is often considered RESTful, as it treats different versions as different representations of the same resource.
- Custom Versioning Header: A dedicated custom header can also be used.
X-API-Version: 1X-Api-Major-Version: 1- This is simpler to implement for some, but less aligned with pure REST principles.
Regardless of the method, versioning through headers allows clients to explicitly request a specific API version without altering the URI structure, which can be advantageous for maintaining clean URLs.
5.6. Idempotency
For operations that can be retried (e.g., payment processing), ensuring idempotency is crucial to prevent unintended duplicate actions.
Idempotency-KeyHeader: Clients can send a unique, client-generatedIdempotency-Keyheader with requests that should be idempotent (e.g., POST requests for creating resources that should only be created once). The server should store this key and ensure that if a request with the same key is received again within a certain timeframe, the original result is returned without re-processing the operation.- Use Cases: Payment gateways, order submissions, creating unique resources.
- Where Set: Client-side, managed and enforced by the API server (often at the API Gateway layer for pre-processing).
By rigorously applying these best practices and considerations, developers can move beyond simply writing headers to mastering them, transforming a technical necessity into a strategic advantage for building secure, efficient, and user-friendly API ecosystems. The careful construction and processing of headers are a hallmark of well-engineered API interactions, ensuring smooth communication across the entire distributed system landscape.
6. Conclusion
The journey through the landscape of API request headers reveals them not as mere technical footnotes, but as fundamental pillars supporting the entire edifice of modern API communication. From the client's initial spark of a request to the server's nuanced processing and the intricate dance of intermediary layers like load balancers and sophisticated API Gateways, headers are the silent, yet profoundly impactful, carriers of context, security, and directives.
We've seen how developers, regardless of their chosen programming language or platform, are empowered to imbue their requests with critical metadata—be it for authentication through Authorization tokens, content negotiation via Content-Type and Accept, or enhancing performance with caching directives like If-None-Match. Each header plays a specific, vital role, ensuring that APIs are not just callable, but truly understandable and responsive to the myriad needs of diverse client applications.
The importance of intermediary components, particularly the API Gateway, has been highlighted as a pivotal point for header management. Platforms like APIPark exemplify how these gateways centralize and simplify the complex task of transforming, securing, and enriching request headers, especially in an era of rapidly integrating AI and REST services. By abstracting away backend-specific header requirements and enforcing consistent policies, API Gateways enable developers to focus on application logic while ensuring robust, scalable, and secure API interactions.
Finally, the emphasis on best practices—ranging from stringent security measures like using HTTPS and protecting credentials, to performance optimizations through header compression and caching, and adherence to established HTTP standards for interoperability—underscores that mastering headers is an ongoing commitment. It's about building not just functional APIs, but resilient, maintainable, and secure API ecosystems that can evolve with confidence.
In essence, understanding where to write API request headers, which headers to employ, and how to manage them effectively across the entire API lifecycle is an indispensable skill for every developer and architect in today's interconnected world. By embracing this knowledge, we pave the way for more seamless, efficient, and trustworthy digital interactions, driving innovation and collaboration across the global software landscape.
Frequently Asked Questions (FAQ)
1. What is the primary purpose of an API request header? The primary purpose of an API request header is to provide metadata about the request itself, the client making it, or the desired response. This metadata is crucial for the server to understand how to process the request, authenticate the client, negotiate content formats, handle caching, and apply various security or routing policies. Essentially, headers provide context and instructions that complement the main request body.
2. Is there a difference in how headers are set in client-side JavaScript (e.g., fetch) versus backend programming languages (e.g., Python requests)? While the conceptual goal is the same (attaching key-value pairs), the syntax and underlying mechanisms differ. Client-side JavaScript in browsers is subject to browser security models like CORS, which automatically adds Origin headers and might trigger preflight OPTIONS requests for certain custom headers or methods. Backend languages typically offer more direct control and are not subject to the same cross-origin restrictions, allowing headers to be set via dictionaries, objects, or dedicated methods provided by their HTTP client libraries.
3. Why would an API Gateway modify request headers, and what are common examples? An API Gateway modifies request headers for several reasons, primarily to centralize cross-cutting concerns and simplify backend service logic. Common examples include: * Authentication: Validating a client's Authorization header, then removing it and adding internal headers like X-User-ID or X-User-Roles for backend services. * Tracing: Injecting X-Request-ID or X-Correlation-ID for distributed tracing across microservices. * Routing: Using headers like X-API-Version to route requests to different service versions. * Security: Adding headers to enforce specific security policies or removing potentially harmful ones. * Transformation: Normalizing client-specific headers to a consistent format expected by backend services (e.g., as exemplified by APIPark for AI model integration).
4. What are the security implications of handling API request headers incorrectly? Incorrect header handling can lead to significant security vulnerabilities. Sending sensitive data (like API keys or authentication tokens) over unencrypted HTTP (without HTTPS/TLS) makes them vulnerable to eavesdropping. Improper validation of Origin headers can expose an API to Cross-Origin Resource Sharing (CORS) attacks. Poor management of Authorization headers can lead to unauthorized access. Additionally, failing to sanitize dynamic header values can make an application vulnerable to header injection attacks.
5. What is the role of X-Forwarded-For and X-Forwarded-Proto headers, and where are they typically added? X-Forwarded-For and X-Forwarded-Proto are crucial headers for identifying the original client's connection details when requests pass through one or more proxies, load balancers, or API Gateways. * X-Forwarded-For: Contains the original IP address of the client that initiated the request. If multiple proxies are involved, it can be a comma-separated list of IPs. * X-Forwarded-Proto: Indicates the original protocol (HTTP or HTTPS) used by the client to connect to the first proxy in the chain. These headers are typically added by intermediary components such as load balancers (e.g., AWS ELB/ALB), reverse proxies (e.g., Nginx, Apache), and API Gateways, ensuring that backend services receive accurate information about the client, even if they only see traffic from the proxy.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.



