FIX: Postgres Docker Container Password Authentication Failed
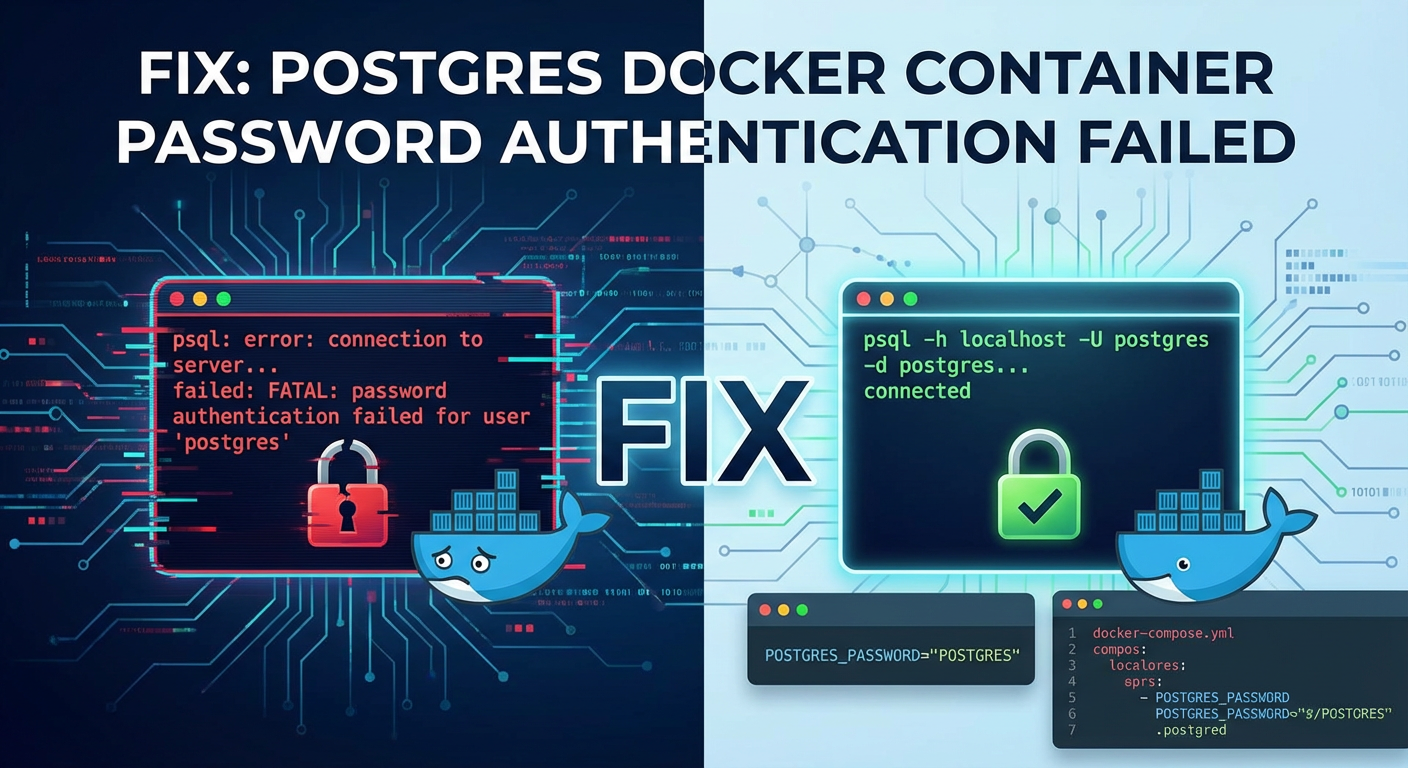
The hum of a well-orchestrated microservices architecture is a symphony of interconnected components, each playing its vital role. At the heart of many such systems, providing the robust persistence layer for critical application data, lies PostgreSQL – a powerful, open-source relational database renowned for its reliability, feature richness, and performance. When coupled with Docker, the promise is one of unparalleled portability, ease of deployment, and consistent environments, making it a cornerstone for modern development and operations. Yet, amidst this harmony, a discordant note frequently arises, often striking fear and frustration into the hearts of developers and system administrators: the dreaded "password authentication failed for user 'postgres'" error when attempting to connect to a Dockerized PostgreSQL instance.
This seemingly innocuous error message, deceptively simple in its phrasing, is a common pitfall that can bring development cycles to a grinding halt and disrupt production environments. It’s a quintessential example of how multiple layers of technology — Docker containers, network configurations, database internal settings, and client-side parameters — must align perfectly for seamless operation. The issue isn't always a straightforward "wrong password" scenario; often, it’s a symptom of deeper misunderstandings or subtle misconfigurations within the complex interplay of these components. Whether you're setting up a local development environment, deploying a new service behind an api gateway, or troubleshooting a critical production issue, encountering this authentication barrier can be a significant roadblock.
This comprehensive guide aims to demystify the "password authentication failed" error within a Dockerized PostgreSQL environment. We will meticulously dissect the underlying causes, ranging from simple credential mismatches to intricate network issues, pg_hba.conf misconfigurations, and even the nuances of database initialization. More importantly, we'll equip you with a systematic, step-by-step troubleshooting methodology, providing the tools and knowledge necessary to diagnose and rectify these issues effectively. By the end of this journey, you'll not only understand how to fix the problem but also how to implement best practices that prevent its recurrence, ensuring your PostgreSQL containers run with robust security and unfailing reliability, ready to serve the most demanding apis and applications.
Deciphering the Dockerized Postgres Ecosystem
Before diving into the myriad ways authentication can fail, it's crucial to establish a solid understanding of how PostgreSQL operates within the Docker ecosystem. Docker, at its core, provides a way to package applications into standardized units called containers. These containers are isolated, lightweight, and include everything an application needs to run: code, runtime, system tools, libraries, and settings.
Docker Fundamentals: Containers, Images, Volumes, and Networks
- Images: A Docker image is a read-only template with instructions for creating a Docker container. For PostgreSQL, the official
postgresimage from Docker Hub is frequently used. This image contains a pre-configured PostgreSQL server, ready to be run. - Containers: A container is a runnable instance of an image. When you run
docker run postgres, Docker creates a container from thepostgresimage. This container has its own isolated filesystem, network interface, and process space. - Volumes: Containers are ephemeral by design; any data written inside a container's filesystem is lost when the container is removed. To persist data, Docker volumes are used. A volume is a designated directory on the host machine that is mounted into the container. For PostgreSQL, the database's data directory (typically
/var/lib/postgresql/data) is almost always mapped to a Docker volume to ensure data persistence across container restarts or removals. - Networks: Docker containers are, by default, connected to a
bridgenetwork. This creates a private network on the host machine, allowing containers to communicate with each other using their container names (if using Docker Compose) or IP addresses. For external access (from the host machine or other machines), specific ports within the container need to be mapped to ports on the host machine using the-pflag (e.g.,-p 5432:5432). This networkgatewayprovides the initial point of contact for external clients.
How PostgreSQL Integrates with Docker
The official PostgreSQL Docker image is designed for ease of use. When you first run a postgres container:
- Initialization: If the data directory (mounted via a volume) is empty, the
postgresentrypoint script performs aninitdboperation. This creates a new PostgreSQL data cluster, sets up default configuration files likepostgresql.confandpg_hba.conf, and initializes thepostgressuperuser with a password. - Environment Variables: The image relies heavily on environment variables to configure the database during initialization. The most critical one for authentication is
POSTGRES_PASSWORD. Setting this variable (e.g.,docker run -e POSTGRES_PASSWORD=mysecretpassword postgres) tells theinitdbprocess to set thepostgressuperuser's password tomysecretpassword. Other variables likePOSTGRES_USERandPOSTGRES_DBallow you to create additional users and databases during the initial setup. - Default
pg_hba.conf: The defaultpg_hba.confwithin the Docker image is often quite permissive to facilitate quick starts, but it still enforces authentication. Typically, it will allow connections from any IP address within the Docker network with password-based authentication.
The Client-Server Authentication Handshake
When a client (e.g., psql, a Node.js application, a Java api service) attempts to connect to a PostgreSQL server, a specific handshake occurs:
- Connection Request: The client sends a connection request to the PostgreSQL server's IP address and port, specifying the username, database, and sometimes the password (or method to obtain it).
- Server Authentication: The PostgreSQL server receives the request. Its first point of reference is the
pg_hba.conffile (Host-Based Authentication). This file dictates which hosts, users, and databases are allowed to connect, and crucially, which authentication method they must use (e.g.,md5,scram-sha-256,trust,peer). - Password Verification: If
pg_hba.confallows the connection with a password-based method, the server requests the password from the client. The client sends the password, which the server then hashes (using the configuredpassword_encryptionmethod) and compares against its stored hash for that user. - Success or Failure: If the hashes match, authentication succeeds, and the client establishes a connection. If they don't, or if
pg_hba.confdenies the connection, the "password authentication failed" error is returned.
Understanding this intricate dance between Docker's isolation, PostgreSQL's internal configuration, and the client's connection attempt is the first step towards effectively troubleshooting any authentication woes. Each layer presents potential points of failure, and a systematic approach is key to pinpointing the exact cause.
Root Causes Unveiled: Why Authentication Fails
The "password authentication failed" error is a catch-all message, meaning the actual root cause can vary significantly. To effectively troubleshoot, we must consider each potential point of failure.
1. The Case of the Mismatched Passwords: POSTGRES_PASSWORD vs. Client Password
This is by far the most common reason for authentication failures, and ironically, often the easiest to overlook. It boils down to a simple mismatch between the password the PostgreSQL container expects and the password the client provides.
Explanation and Common Pitfalls:
The POSTGRES_PASSWORD environment variable plays a critical role during the initialization of a new PostgreSQL data directory. When the postgres container starts for the very first time with an empty data volume, the entrypoint script runs initdb, creating the database cluster and setting the password for the default postgres superuser (or the user specified by POSTGRES_USER) to the value provided in POSTGRES_PASSWORD.
Crucially, if the data directory already exists and contains an initialized database, changing POSTGRES_PASSWORD on subsequent container starts will not change the password of the existing user. The password is set only during the initial initdb process. This is a frequent source of confusion. Developers often stop a container, change the password in their docker-compose.yml or docker run command, and then expect the password to magically update. It won't.
Common pitfalls include:
- Typos: Simple keyboard errors when typing the password on either the server (Docker environment variable) or client side.
- Whitespace: Leading or trailing whitespace in the
POSTGRES_PASSWORDenvironment variable or the client's connection string. These are often invisible but count as characters. - Environment Variable Overrides: If using Docker Compose, an environment variable might be set in multiple places (e.g.,
.envfile,environmentsection indocker-compose.yml), leading to an unexpected value being used. - Shell Escaping: Special characters in passwords (e.g.,
!,$,#) might be misinterpreted by the shell if not properly quoted or escaped. - Database Re-creation without Volume Deletion: If you're experimenting and recreate your container, but don't delete the associated Docker volume, the old initialized database (with its old password) persists. The new
POSTGRES_PASSWORDyou provide will be ignored.
How to Verify and Fix:
- Check
POSTGRES_PASSWORDon the Container: You can inspect the environment variables of a running container.bash docker inspect <container_name_or_id> | grep POSTGRES_PASSWORDThis will show the value Docker thinks it passed to the container. However, this doesn't guarantee it's the password actually used by the initialized database if the data directory already existed.A more direct, though less secure, method for debugging (do not do this in production) is to exec into the container and check the environment variable (if still present) or thepg_hba.confwhich reflects authentication settings, but not the actual hashed password.bash docker exec -it <container_name> env | grep POSTGRES_PASSWORDNote: The actual password itself is stored hashed within the database, not in plain text in a config file. - Verify Client Password: Double-check the password string used in your client application's connection string,
PGPASSWORDenvironment variable, or interactive prompt. Ensure it exactly matches what you intended forPOSTGRES_PASSWORD. - Forcing a Password Reset (Development/Testing only): If the data volume already exists and you must change the
postgresuser's password, you'll need to connect to the database first (perhaps temporarily relaxingpg_hba.confif absolutely necessary, or using an existing valid connection) and then alter the password using SQL:sql ALTER USER postgres WITH PASSWORD 'mynewsecretpassword';After this, restart the container, ensuring the client usesmynewsecretpassword.
The "Clean Start" (Most Recommended for Development): When in doubt during development, the most straightforward approach is to completely remove the existing container and its associated volume and then recreate it. This forces initdb to run again with the current POSTGRES_PASSWORD. ```bash # Stop and remove the container docker stopdocker rm
Remove the associated volume (CAUTION: THIS DELETES ALL DATA)
docker volume rm# or use docker-compose down -v
Recreate the container (e.g., with docker-compose up -d)
``` Always backup critical data before removing volumes in a production-like scenario.
2. pg_hba.conf: The Gatekeeper's Strict Rules
The pg_hba.conf file (Host-Based Authentication) is PostgreSQL's primary mechanism for controlling who can connect to the database, from where, to which databases, and using what authentication method. It acts as a strict gateway, filtering connection attempts at the database server level. A misconfiguration here can prevent even correctly authenticated users from connecting.
Explanation and Syntax:
Each line in pg_hba.conf is an authentication rule. The first matching rule for a given connection attempt determines whether it's allowed and how it should be authenticated. The general syntax is:
type database user address method [options]
type:local(for Unix domain socket connections),host(for TCP/IP connections, IPv4 or IPv6),hostssl(for SSL-encrypted TCP/IP),hostnossl(for non-SSL TCP/IP).database: The database(s) the user is trying to connect to (all,sameuser,samerole, specific database name, or a comma-separated list).user: The user(s) trying to connect (all, specific username, or a comma-separated list).address: The client IP address(es) from which the connection is originating. This can be an IP address, an IP range (e.g.,192.168.1.0/24), orall. Forlocalconnections, this field is not used.method: The authentication method to use. Common methods include:trust: Authenticate automatically, no password required (HIGHLY INSECURE, for debugging/local only).reject: Unconditionally reject the connection.md5: Require an MD5-hashed password.scram-sha-256: Require a SCRAM-SHA-256 hashed password (default since Postgres 10+).peer: Use the client's operating system username for authentication (only forlocalconnections).ident: Authenticate with anidentserver on the client.password: Send password in plain text (INSECURE).gssapi,ssi,ldap,radius,cert,pam: More advanced methods.
options: Additional method-specific options (e.g.,map,krb_srvname).
Default Docker pg_hba.conf Behavior:
The official Docker image typically starts with a pg_hba.conf that includes rules like:
# TYPE DATABASE USER ADDRESS METHOD
host all all 0.0.0.0/0 md5
# or scram-sha-256 depending on Postgres version and config
This rule allows TCP/IP connections (host) from any IP address (0.0.0.0/0) for any database (all) by any user (all), requiring md5 (or scram-sha-256) password authentication. This is generally permissive enough for most Docker deployments but can be too broad for production.
Common Misconfigurations:
- Incorrect
address: If your application is on a different Docker network or external IP, andpg_hba.confis too restrictive (e.g., only127.0.0.1/32or specific Docker network IPs), it will reject connections. - Wrong
method: If thepg_hba.confspecifiesmd5but the user was created withscram-sha-256(or vice-versa), authentication will fail. Similarly, ifpeeris specified for ahostconnection, it will fail. - Rule Order: Rules are processed from top to bottom. A less specific
rejectrule at the top can accidentally block valid connections defined later.
How to Inspect and Override pg_hba.conf:
- Inspect Inside the Container:
bash docker exec -it <container_name> cat /var/lib/postgresql/data/pg_hba.confThis allows you to see the activepg_hba.conffile being used by the running PostgreSQL instance.
Override with a Bind Mount (Recommended): For production or more controlled environments, you often want to provide your own pg_hba.conf. You can do this by creating a custom pg_hba.conf file on your host machine and then bind-mounting it into the container.First, create my_pg_hba.conf on your host: ```
my_pg_hba.conf
TYPE DATABASE USER ADDRESS METHOD
host all all 0.0.0.0/0 scram-sha-256
Allow local connections for the 'postgres' user without password for debugging (temporarily!)
local all postgres trust Then, in your `docker-compose.yml`:yaml version: '3.8' services: db: image: postgres:15 environment: POSTGRES_DB: mydatabase POSTGRES_USER: myuser POSTGRES_PASSWORD: mypassword volumes: - postgres_data:/var/lib/postgresql/data - ./my_pg_hba.conf:/etc/postgresql/pg_hba.conf:ro # Mount custom pg_hba.conf ports: - "5432:5432" volumes: postgres_data: `` *Note: When bind-mounting/etc/postgresql/pg_hba.conf, ensure you also specify the correct path within the container for the PostgreSQL version you are using. For recent Postgres versions, it's often located in/var/lib/postgresql/data/pg_hba.confor/etc/postgresql//main/pg_hba.conf. The official Docker image symlinks itspg_hba.conffrom the data directory.* A safer bet might be mounting into/etc/postgresql/and then ensuring PostgreSQL picks it up, or just mounting into/var/lib/postgresql/data/pg_hba.conf. The/etc/postgresql/pg_hba.confexample above assumes the official image is configured to pick up from/etc/postgresql/. Inspecting/etc/postgresql/postgresql.confwithin the container will reveal the actualhba_fileparameter. For Docker's official image, it's usually inside/var/lib/postgresql/data`.Table: Common pg_hba.conf Authentication Methods
| Method | Description | Security | Use Case |
|---|---|---|---|
trust |
No password or authentication required. Any user providing the specified database and user can connect. |
Very Low | Local development, temporary debugging (NEVER production). |
reject |
Unconditionally reject the connection. | N/A | Explicitly block unwanted connections. |
password |
Password transmitted in plain text. | Low | Legacy systems, specific highly secure internal networks (generally avoid). |
md5 |
Password transmitted as MD5 hash. Historically common, but less secure than SCRAM-SHA-256. | Medium | Compatibility with older clients/servers, internal trusted networks. |
scram-sha-256 |
Secure SCRAM-SHA-256 challenge-response authentication. Default for Postgres 10+. | High | Recommended for all new deployments, modern clients. |
peer |
Authenticate using the client's operating system username. Only for local (Unix socket) connections. |
High | Local host access where OS users map to DB users. |
ident |
Authenticate by contacting an ident server on the client host. |
Medium | Legacy UNIX systems, usually for internal trusted environments. |
Post pg_hba.conf Changes:
After modifying pg_hba.conf, PostgreSQL needs to reload its configuration. You can do this by sending a SIGHUP signal to the postgres process (e.g., docker exec -it <container_name> pg_ctl reload) or simply restarting the Docker container (docker restart <container_name>). Restarting is often simpler and safer in a Docker context.
3. Network Labyrinth: Connectivity and Firewall Issues
Even if your password is correct and pg_hba.conf is perfectly configured, the client still needs to reach the PostgreSQL server. Docker's networking, host firewalls, and cloud security groups can all prevent this crucial initial connection. This is where fundamental gateway concepts become vital.
Explanation of Docker Networking:
- Default Bridge Network: When you run containers without specifying a network, they are attached to the default
bridgenetwork. Containers on the same bridge network can communicate with each other by their IP addresses or (if using Docker Compose) by their service names. - Port Mapping (
-p): For a client on the host machine or an external network to connect to a service inside a container, a port needs to be mapped. For example,-p 5432:5432maps port 5432 on the host to port 5432 inside the container. If this mapping is missing or incorrect, external connections will fail. - Docker Compose Networks: Docker Compose automatically creates a dedicated network for all services defined in a
docker-compose.ymlfile. Services on this network can reach each other by their service names. For instance, anapiservice can connect todbif the database service is nameddb.
Common Network & Firewall Issues:
- Missing Port Mapping: The most common mistake. If you don't map
5432:5432, your client on the host can't reach the container's port. - Incorrect IP Address/Hostname: Clients trying to connect to
localhostor127.0.0.1when the container is only reachable via its Docker internal IP, or when usingdocker-composeservice names are not correctly resolved. - Firewall on Host: Your operating system's firewall (e.g.,
ufwon Linux, Windows Defender Firewall) might be blocking incoming connections to the mapped port on the host machine. - Cloud Security Groups/NACLs: If deploying to a cloud environment (AWS, Azure, GCP), network security groups or network access control lists (NACLs) might be blocking traffic on port 5432 to your server instance.
- Wrong Docker Network: If your client application container and your Postgres container are on different Docker networks, they won't be able to communicate unless explicitly linked or connected to a shared network.
- Network
GatewayIssues: In complex setups, the networkgateway(either the Dockerbridgegatewayor an external router) might not be configured to route traffic correctly to the container's internal IP.
Diagnosing Network Issues:
- Verify Port Mapping: Check
docker psoutput to confirm the port mapping.bash docker ps # Look for something like: 0.0.0.0:5432->5432/tcpIf you see5432/tcpwithout a host port, it means the port is exposed inside the container but not mapped to the host. - Test Connectivity from Host: Use
telnetornc(netcat) to test if you can reach the mapped port on the host.bash telnet localhost 5432 # or nc -vz localhost 5432A successful connection will showConnected to localhost.orsucceeded!. If it hangs or gives "Connection refused," the issue is likely network-related before authentication. - Check Firewall Rules:
- Linux (ufw):
sudo ufw status. If enabled, ensure port 5432 is allowed:sudo ufw allow 5432/tcp. - Windows: Search for "Windows Defender Firewall with Advanced Security" and check inbound rules.
- Cloud Providers: Review security group rules (e.g., AWS EC2 Security Groups, Azure Network Security Groups).
- Linux (ufw):
- Verify Docker Network: If using Docker Compose, ensure your services are on the same network. By default, they are. If you've created custom networks, ensure both the Postgres service and your
apiservice (or whatever client it is) are part of that network.bash docker network ls docker network inspect <network_name> # to see connected containers - Ping from Client Container to DB Container (if applicable): If your client is another Docker container, exec into it and try to ping the database container by its service name.
bash docker exec -it <client_container_name> ping <db_service_name>If ping fails, it's a fundamental network communication issue between containers.
4. The Unready Database: Initialization and Startup Race Conditions
A common scenario in multi-service deployments (like those orchestrated by Docker Compose) is a race condition where a client application tries to connect to PostgreSQL before the database server has fully initialized or started accepting connections. This isn't strictly an authentication failure but often manifests with similar "connection refused" or "authentication failed" messages, as the database isn't ready to process the request.
Explanation of Initialization and Readiness:
- Postgres Initialization: The first time a
postgrescontainer runs with an empty data volume, it performs aninitdbprocess. This can take anywhere from a few seconds to a few minutes, depending on the system's performance and the specific image. During this time, the database server is not fully operational and cannot accept client connections. - Startup Sequence: Even after
initdb, PostgreSQL needs to fully start up, load configurations, and open its port for listening. This also takes time. - Race Conditions in Docker Compose: When you run
docker-compose up, all services often start in parallel. Your application service might start much faster than the database, attempting to connect before PostgreSQL is ready. Thedepends_ondirective in Docker Compose only ensures a container is started before its dependencies, not that it's ready.
How to Address Readiness Issues:
- Check Postgres Logs: The most reliable way to know if Postgres is ready is to inspect its logs. Look for a message indicating it's ready to accept connections.
bash docker logs <postgres_container_name> # Look for lines like: "database system is ready to accept connections" - Implement
healthcheckin Docker Compose (Recommended): Docker Compose'shealthcheckallows you to define a command that Docker will periodically run inside the container to check its "health." You can then combine this withdepends_onto ensure an application service only starts after its database dependency is healthy.yaml version: '3.8' services: db: image: postgres:15 environment: POSTGRES_DB: mydatabase POSTGRES_USER: myuser POSTGRES_PASSWORD: mypassword volumes: - postgres_data:/var/lib/postgresql/data ports: - "5432:5432" healthcheck: test: ["CMD-SHELL", "pg_isready -U $$POSTGRES_USER -d $$POSTGRES_DB"] interval: 5s timeout: 5s retries: 5 app: build: . depends_on: db: condition: service_healthy # This is key! # ... other app configurations volumes: postgres_data:pg_isreadyis a utility provided by PostgreSQL client tools that checks the connection status of a PostgreSQL server. The$$is used to escape the$forPOSTGRES_USERandPOSTGRES_DBso they are correctly interpreted by Docker Compose and then by the shell inside the container. - Client-Side Connection Retries: Your application code should ideally implement a retry mechanism for database connections during startup. Instead of failing immediately, it should attempt to connect multiple times with short delays. Many database drivers and ORMs offer this functionality out-of-the-box.
- Wait-for-it Scripts: For simpler setups or when
healthcheckis insufficient, you can use external scripts (likewait-for-it.shordockerize) that wait for a specific port to be open before starting the application service.Examplecommandfor an app service indocker-compose.yml:yaml app: build: . depends_on: - db command: ["./wait-for-it.sh", "db:5432", "--", "npm", "start"] # (Assuming wait-for-it.sh is copied into your app container)
5. Encryption Evolution: MD5 vs. SCRAM-SHA-256
PostgreSQL version 10 introduced scram-sha-256 as the default password encryption method, replacing the older md5. While md5 is still supported, if your PostgreSQL server uses one method and your client library or connection attempt expects another, authentication can fail.
Explanation and Compatibility:
password_encryptionParameter: Thepostgresql.conffile contains thepassword_encryptionparameter, which dictates the default hashing method for new passwords. Since PostgreSQL 10, this defaults toscram-sha-256.- Client Driver Support: Older client drivers or
psqlversions might not supportscram-sha-256and expectmd5. Conversely, a modern client might tryscram-sha-256while the server is configured only formd5. pg_hba.confmethod: Themethodspecified inpg_hba.conf(e.g.,md5orscram-sha-256) must match how the user's password was created and the capabilities of the client.
How to Check and Resolve:
- Check Server's
password_encryption: Exec into the container and inspect thepostgresql.confor query the database.bash docker exec -it <container_name> grep "password_encryption" /var/lib/postgresql/data/postgresql.conf # or (if you can connect somehow, e.g., temporarily using 'trust' for a local rule) psql -U postgres -d postgres -c "SHOW password_encryption;" - Check User's Password Type: You can query
pg_shadoworpg_authidto see the actual password hash type for a user (again, requires a successful connection).sql SELECT usename, passwd FROM pg_shadow WHERE usename = 'myuser'; -- The `passwd` field will start with `md5` or `scram-sha-256` - Adjust
pg_hba.confMethod: Ensure themethodinpg_hba.conf(e.g.,md5orscram-sha-256) matches the password type you expect from your client and how the user's password was initially set. - Change User's Password (to a specific type): If your client must use
md5but the user's password isscram-sha-256, you can change the user's password tomd5:sql ALTER USER myuser WITH PASSWORD 'newpassword'; -- This will use the default `password_encryption` -- To explicitly force MD5 (though generally not recommended for new setups): -- ALTER USER myuser WITH ENCRYPTED PASSWORD 'newpassword'; -- (pre-SCRAM-SHA-256 syntax, still works for MD5) -- Or, more modern approach, modify postgresql.conf's password_encryption and then alter user.Alternatively, upgrade your client driver to one that supportsscram-sha-256. This is the preferred long-term solution. - Temporarily Allow Both (for migration): During a migration, you might temporarily have two
pg_hba.confentries for the sameaddress,database,userbut with differentmethodtypes, ensuring both old and new clients can connect. However, this complicates security and should be a temporary measure.
6. Volume Permissions: The Silent Saboteur
Less common but equally perplexing, incorrect file system permissions on the Docker volume where PostgreSQL stores its data can prevent the database from starting correctly, leading to authentication issues or even container crashes.
Explanation and Common Causes:
PostgreSQL runs inside the container as a specific user, typically postgres, with a particular UID/GID (usually 999). This postgres user needs appropriate read and write permissions to its data directory (/var/lib/postgresql/data).
When you bind-mount a host directory as a Docker volume, the host's file system permissions take precedence. If the host directory is owned by root or another user with restrictive permissions, the postgres user inside the container might not be able to write to it, causing initdb to fail or the database server to not start.
Common causes include:
- Manually Created Host Directory: If you manually create a directory on the host (e.g.,
mkdir ./postgres-data) and then bind-mount it, it will inherit permissions from your current user, which might not be accessible to thepostgresuser (UID 999) inside the container. - Incorrect
chown/chmod: After creating a volume, you might have manually adjusted permissions on the host incorrectly.
How to Check and Resolve:
- Check Container Logs: The first indicator will be in the container logs. Look for error messages related to permissions or inability to write to the data directory.
bash docker logs <postgres_container_name> # Look for errors like: "could not create directory", "could not open file", "permission denied" - Inspect Volume Permissions from Host: Identify the actual path of your Docker volume on the host. For named volumes,
docker volume inspect <volume_name>will show theMountpoint. For bind mounts, it's the host path you specified. Then, check its permissions:bash ls -ld /path/to/your/postgres/data/on/hostYou ideally want this directory to be owned by the userpostgres(UID 999) or have permissions that allow thepostgresuser to write.
Correct Permissions (Caution!): If you find permission issues, you can try to change ownership on the host. bash sudo chown -R 999:999 /path/to/your/postgres/data/on/host # Or, if running the container as a different user: # sudo chown -R <uid>:<gid> /path/to/your/postgres/data/on/host Note: The UID/GID for the postgres user can vary slightly between Docker images or Linux distributions, though 999 is common.A safer approach is to let Docker manage named volumes. Named volumes are usually initialized with the correct permissions by the Docker engine or the container's entrypoint script when the volume is first attached to a container that initializes data there. ```yaml
In docker-compose.yml
volumes: - postgres_data:/var/lib/postgresql/data
...
volumes: postgres_data: # Docker manages this volume, usually with correct permissions `` If you must use bind mounts, ensure the target directory on the host is either empty initially (allowing the container to set up permissions) or pre-configured with the correct ownership/permissions for thepostgres` user.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
The Diagnostic Toolkit: A Step-by-Step Troubleshooting Guide
When faced with the dreaded "password authentication failed," a systematic approach is your best friend. Resist the urge to randomly change settings. Instead, follow this diagnostic checklist.
1. Initial Sanity Checks: Is Everything Even Running?
Before diving deep, ensure the basics are in order. This is the simplest gateway check.
- Is the Docker container running?
bash docker ps -aCheck theSTATUScolumn. If it's "Exited," the container crashed, and you need to checkdocker logs. If it's "Up," proceed. - Is the port mapped correctly? In the
docker psoutput, look at thePORTScolumn. Ensure0.0.0.0:5432->5432/tcp(or your chosen host port) is listed, indicating the container's internal port 5432 is accessible from the host. - Can you reach the port from the host?
bash telnet localhost 5432 # or nc -vz localhost 5432If this fails, it's a network/firewall issue (see Section 3). If it connects, the server is listening, and the issue is likely authentication-specific.
2. The Logs Tell All: Your First and Most Critical Step
Docker logs are an invaluable source of truth. PostgreSQL is verbose, and its logs will often directly point to the problem.
docker logs <postgres_container_name>
What to look for:
- Authentication Errors: The logs will often explicitly state the reason for authentication failure, e.g.,
FATAL: password authentication failed for user "myuser"followed byDETAIL: Password does not match for user "myuser". This confirms a password mismatch (Section 1). pg_hba.confErrors: Ifpg_hba.confis misconfigured, you might see messages likeFATAL: no pg_hba.conf entry for host "172.17.0.1", user "myuser", database "mydatabase", SSL off. This directly points to apg_hba.confissue (Section 2).- Startup Errors: If the container exited or is stuck, look for errors during
initdbor server startup, e.g.,FATAL: data directory "/techblog/en/var/lib/postgresql/data" has wrong ownership(Section 6) orFATAL: could not open configuration file "/techblog/en/var/lib/postgresql/data/postgresql.conf": Permission denied. - "database system is ready to accept connections": This confirms that PostgreSQL has started successfully and is listening. If you don't see this, the database might not be fully initialized or running (Section 4).
3. Environment Variable Verification: What Password Did Docker Promise?
Confirm the POSTGRES_PASSWORD (and POSTGRES_USER/POSTGRES_DB) that Docker passed to the container.
docker inspect <postgres_container_name> | grep POSTGRES_PASSWORD
docker inspect <postgres_container_name> | grep POSTGRES_USER
docker inspect <postgres_container_name> | grep POSTGRES_DB
Cross-reference these values with what your client application is using. Remember, if the volume already had data, changing POSTGRES_PASSWORD after the first initdb won't update the password (Section 1).
4. Deep Dive into pg_hba.conf: The Access Rules
If the logs suggest pg_hba.conf as the culprit, examine the file inside the running container.
docker exec -it <postgres_container_name> cat /var/lib/postgresql/data/pg_hba.conf
- Compare rules to your connection: Does an entry match your client's
type(host),database,user, andaddress? - Check
method: Does themethod(e.g.,md5,scram-sha-256) align with the user's password type and your client's capabilities (Section 5)? - Order matters: Is there a
rejectrule higher up that's inadvertently blocking your connection? 0.0.0.0/0(for host connections) or127.0.0.1/32(if connecting from host to exposed port): Ensure theaddressfield is broad enough for your testing (e.g.,0.0.0.0/0forhostfrom anywhere) or specific to the Docker network or client IP if desired.
5. Network Connectivity Test: Can They Even See Each Other?
If telnet/nc from the host to the Docker-mapped port failed, or if containers can't communicate:
- Review
docker psagain: Is the port mapping correct (-p 5432:5432)? - Check host firewall: Is port 5432 open on your host machine?
- Inside Docker network communication (if client is another container):
bash docker exec -it <client_container_name> ping <postgres_service_name>If this works, trync -vz <postgres_service_name> 5432from the client container. Ifpingfails butncconnects, it's not a basic network connectivity issue but perhaps an application configuration. If both fail, investigate Docker networks more deeply (Section 3).
6. Rebuild and Recreate: A Fresh Start (with Caution)
Sometimes, especially in development, transient issues or unclear states can be resolved by a clean restart.
# For a single container:
docker stop <postgres_container_name>
docker rm <postgres_container_name>
docker run ... # (your original run command)
# For Docker Compose:
docker-compose down # Stops and removes containers, networks. Retains volumes by default.
docker-compose up -d # Recreates and starts.
If you suspect the persistent volume holds stale data or an old password, and you're in a development environment where data loss is acceptable, you can also remove the volume:
docker volume rm <volume_name> # CAUTION: DELETES ALL DATA!
# or for Docker Compose:
docker-compose down -v # Removes containers, networks, AND volumes.
docker-compose up -d
This forces a fresh initdb with the POSTGRES_PASSWORD currently defined, addressing password mismatch issues rooted in pre-existing data volumes.
7. Temporary Access for Debugging: The trust Method (Use with Extreme Care)
As a last resort for troubleshooting, if you cannot connect to your database at all to make changes, you can temporarily modify pg_hba.conf to use the trust method for your connection. This is highly insecure and should only be done for local debugging, never in production, and reverted immediately after use.
- Create a temporary
pg_hba.conffile on your host:# temp_pg_hba.conf # This grants ALL access without password for debugging. # ONLY USE TEMPORARILY AND LOCALLY. host all all 0.0.0.0/0 trust - Mount this file into your container and restart: In
docker-compose.yml:yaml services: db: # ... volumes: - ./temp_pg_hba.conf:/var/lib/postgresql/data/pg_hba.conf:ro # ...Thendocker-compose up -d. - Connect without a password.
- Fix the actual issue (e.g., set the correct password, adjust
pg_hba.confmethod). - Remove the temporary
pg_hba.confmount and restart your container. Revert to secure settings.
By following these steps, you systematically eliminate potential causes, narrowing down the problem until the true culprit of your Postgres Docker authentication failure is revealed. Patience and logical deduction are key.
Beyond the Fix: Best Practices and Proactive Measures
Once you've successfully navigated the treacherous waters of authentication failures, the next step is to implement practices that prevent future occurrences. Robust systems are built not just on fixes, but on foresight and adherence to best practices.
Docker Compose for Robustness and Clarity
Docker Compose is indispensable for managing multi-service applications, including your api services and database backends. Leveraging its features can significantly reduce authentication-related headaches.
healthcheck: As discussed in Section 4, a well-configuredhealthcheckfor your PostgreSQL service ensures that dependent services (like yourapibackend) only attempt to connect when the database is truly ready. This eliminates common race conditions that manifest as connection or authentication failures.depends_onwithservice_healthy: Usingcondition: service_healthyin conjunction withhealthcheckprovides a robust startup order for your services, far superior to merely checking if a container has started.restartPolicies: Configure appropriaterestartpolicies (e.g.,unless-stopped,always) for your database container. This ensures that if the container crashes for any reason, Docker will attempt to restart it, increasing resilience.
Consistent Environment Variables: Centralize your environment variables (especially POSTGRES_PASSWORD, POSTGRES_USER, POSTGRES_DB) in a .env file or directly in docker-compose.yml. Avoid hardcoding them directly in docker run commands if using Compose, as this can lead to inconsistencies.```yaml
.env file
POSTGRES_USER=myuser POSTGRES_PASSWORD=mysecretpassword POSTGRES_DB=mydb
docker-compose.yml
services: db: image: postgres:15 environment: POSTGRES_USER: ${POSTGRES_USER} POSTGRES_PASSWORD: ${POSTGRES_PASSWORD} POSTGRES_DB: ${POSTGRES_DB} # ... other config ```
Securing Your Postgres Instance
Beyond just getting it to connect, securing your database is paramount, especially when it supports production apis.
- Strong, Unique Passwords: Always use long, complex passwords for database users. Avoid default passwords or easily guessable ones. Store them securely, preferably using Docker Secrets or a secrets management system in production.
- Principle of Least Privilege: Create dedicated database users for each application or service (e.g.,
my_app_userinstead of usingpostgresdirectly). Grant these users only the minimum necessary privileges (e.g.,SELECT,INSERT,UPDATE,DELETEon specific tables), not superuser access. - Restrict
pg_hba.confEntries: Do not use0.0.0.0/0inpg_hba.conffor production environments unless absolutely necessary and coupled with strong external firewalls. Instead, restrictaddressto:- Specific IP addresses or subnets of your application servers.
- The Docker internal network subnet (e.g.,
172.17.0.0/16for default bridge, or a custom subnet for a user-defined network). 127.0.0.1/32for connections originating from the same host, which is only valid if your client is also on the host and connecting to the mapped port.
- Enable SSL/TLS Connections: For connections over untrusted networks (even within a multi-host Docker setup or public cloud), configure PostgreSQL to enforce SSL/TLS encryption. This protects data in transit from eavesdropping. Set
ssl = oninpostgresql.confand ensure yourpg_hba.confspecifieshostsslmethod. - Regular Backups: While not directly an authentication fix, consistent backups are the ultimate safeguard against data loss, which can be catastrophic if authentication issues prevent access to critical data.
The API Gateway Layer: A Unified Front
In a microservices architecture, where numerous services might interact with various data stores like PostgreSQL, ensuring secure and efficient api access is paramount. While the database itself needs foundational security, an api gateway adds a critical layer of authentication, authorization, and traffic management, complementing the foundational security measures you implement directly on your database.
An api gateway acts as a single entry point for all client requests, abstracting the complexity of the backend services. It can perform tasks such as:
- Request Routing: Directing incoming
apirequests to the appropriate backend microservice. - Authentication and Authorization: Validating client credentials (e.g., API keys, OAuth tokens) before forwarding requests to internal services. This means your application
apimight be secured by theapi gateway, reducing the burden on individual backend services to handle external authentication, even though those backend services still need to authenticate with their databases. - Rate Limiting: Protecting backend services from overload by controlling the number of requests clients can make.
- Caching: Improving performance by storing responses to frequently requested data.
- Monitoring and Analytics: Providing a centralized view of
apitraffic and performance.
Platforms such as APIPark streamline the management, integration, and deployment of these apis, including those backed by PostgreSQL. APIPark serves as a comprehensive api gateway and management platform that can significantly enhance the security, performance, and manageability of your services. While APIPark directly manages the api layer, handling client requests before they ever reach your individual services, the underlying database's authentication and security, as we've discussed with PostgreSQL, are foundational to the entire system's integrity. A robust api gateway like APIPark ensures that only authorized api calls reach your application services, which then, in turn, make secure, authenticated connections to your PostgreSQL database. This layered security approach is crucial for enterprise-grade applications.
Version Control for Configurations
Treat your Dockerfiles, docker-compose.yml files, custom pg_hba.conf files, and any other configuration artifacts as code.
- Store them in Git: This allows you to track changes, revert to previous versions, and collaborate effectively.
- Automate Deployment: Use CI/CD pipelines to build and deploy your Docker images and configurations. This ensures consistency and reduces manual errors.
Automated Testing
Integrate database connectivity tests into your CI/CD pipelines. These tests can verify:
- That the database container starts correctly.
- That applications can connect to the database using the correct credentials.
- That basic CRUD operations work.
This proactive approach catches authentication issues early in the development cycle, long before they impact production or become frustrating roadblocks. By embracing these best practices, you can establish a resilient and secure PostgreSQL Docker environment, serving as a stable foundation for all your applications and apis, and allowing you to focus on developing features rather than troubleshooting recurrent authentication nightmares.
Conclusion: Mastering Postgres Docker Authentication
The journey through the intricate layers of a "password authentication failed" error in a Dockerized PostgreSQL environment can be a daunting one. What initially appears as a simple credential mismatch quickly reveals itself as a complex interplay of Docker's isolation mechanisms, network configurations, PostgreSQL's host-based authentication rules, and even the subtle nuances of database initialization and password encryption. Yet, by approaching the problem with a systematic and logical mindset, armed with the knowledge and diagnostic tools discussed in this extensive guide, you can confidently unravel these challenges.
We've explored the most prevalent culprits: from the classic POSTGRES_PASSWORD and client password disparities, often exacerbated by the stateful nature of Docker volumes, to the meticulous rule-sets of pg_hba.conf that act as the database's primary security gateway. Network connectivity, firewall rules, and the crucial timing of database readiness in multi-container setups were also dissected, alongside the evolutionary shifts in password encryption like SCRAM-SHA-256 and the often-overlooked permissions on data volumes. Each potential failure point offers a distinct path to diagnosis, predominantly illuminated by the invaluable insights contained within the Docker container's logs.
The true mastery, however, lies not just in fixing the immediate problem but in proactively preventing its recurrence. Embracing best practices such as robust Docker Compose configurations with healthcheck and service_healthy conditions, adhering to the principle of least privilege for database users, and meticulously controlling access through pg_hba.conf are paramount. Furthermore, recognizing the role of an api gateway like APIPark in securing and managing the application layer that interacts with your database provides an additional, essential layer of defense and operational efficiency for modern microservices architectures. While APIPark secures the api endpoints for external consumers, the underlying database's robust authentication, as we've discussed, remains the bedrock of the entire system's data integrity and security.
Ultimately, understanding the Dockerized PostgreSQL ecosystem, coupled with a systematic troubleshooting methodology and a commitment to proactive security and operational best practices, transforms a frustrating authentication error into a valuable learning opportunity. It empowers you to build, deploy, and manage highly reliable and secure database backends, ensuring that your applications and apis run smoothly, efficiently, and without the unwelcome interruption of a failed password authentication.
Frequently Asked Questions (FAQs)
1. What is the most common reason for "password authentication failed" in a Postgres Docker container?
The most common reason is a mismatch between the POSTGRES_PASSWORD environment variable provided to the Docker container and the password used by the client application. A critical point to remember is that POSTGRES_PASSWORD only sets the postgres user's password during the initial creation of the database cluster. If you restart the container with an existing data volume and change POSTGRES_PASSWORD, the password will not be updated. You would need to either reset the password via SQL after connecting (if you can) or delete the data volume to force a re-initialization with the new password (caution: this deletes all data).
2. How can I inspect the pg_hba.conf file inside my running Postgres Docker container?
You can use the docker exec command to run a shell command inside your container. To view the pg_hba.conf file, use:
docker exec -it <container_name_or_id> cat /var/lib/postgresql/data/pg_hba.conf
Replace <container_name_or_id> with the actual name or ID of your PostgreSQL container. This will display the exact rules that PostgreSQL is using for host-based authentication.
3. My client application connects to localhost:5432, but the Postgres Docker container is not reachable. What should I check?
First, verify that you have correctly mapped the container's port to your host machine's port. This is done with the -p flag in docker run or the ports section in docker-compose.yml (e.g., -p 5432:5432). Then, ensure no host firewall (like ufw on Linux or Windows Defender Firewall) is blocking incoming connections to port 5432 on your host. Use telnet localhost 5432 or nc -vz localhost 5432 from your host machine to confirm network connectivity before troubleshooting password issues.
4. What is the difference between md5 and scram-sha-256 methods in pg_hba.conf, and why does it matter?
md5 and scram-sha-256 are password authentication methods. scram-sha-256 is a more secure, modern challenge-response authentication protocol introduced as the default in PostgreSQL 10+, replacing the older md5. It matters because both your PostgreSQL server's password_encryption setting (determining how user passwords are stored) and the method specified in pg_hba.conf (how the server expects clients to authenticate) must be compatible with your client application's capabilities. If there's a mismatch (e.g., server expects scram-sha-256 but client only supports md5), authentication will fail. The best practice is to use scram-sha-256 and ensure your client drivers are up to date.
5. My application container tries to connect to the database container but gets "connection refused" or authentication errors immediately after docker-compose up. How can I ensure the database is ready?
This is often a race condition where your application starts before PostgreSQL has fully initialized and begun accepting connections. To resolve this, use Docker Compose healthcheck in your database service definition and depends_on with condition: service_healthy for your application service. This tells Docker Compose to only start your application service once the database container reports itself as healthy (i.e., ready to accept connections). Alternatively, implement client-side connection retry logic in your application.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.



