Redis Connection Refused: Common Causes & Solutions
In the intricate world of modern application development, Redis has cemented its position as an indispensable in-memory data store, revered for its lightning-fast performance, versatile data structures, and robust capabilities as a cache, message broker, and real-time analytics engine. From high-traffic web applications to complex microservices architectures, Redis underpins countless critical systems, facilitating swift data access and processing that drives responsive user experiences and efficient backend operations. Its role is so fundamental that any disruption in its availability can ripple through an entire ecosystem, bringing operations to a grinding halt and potentially leading to significant service degradation or outages. Developers and system administrators universally understand the paramount importance of a stable and readily accessible Redis instance.
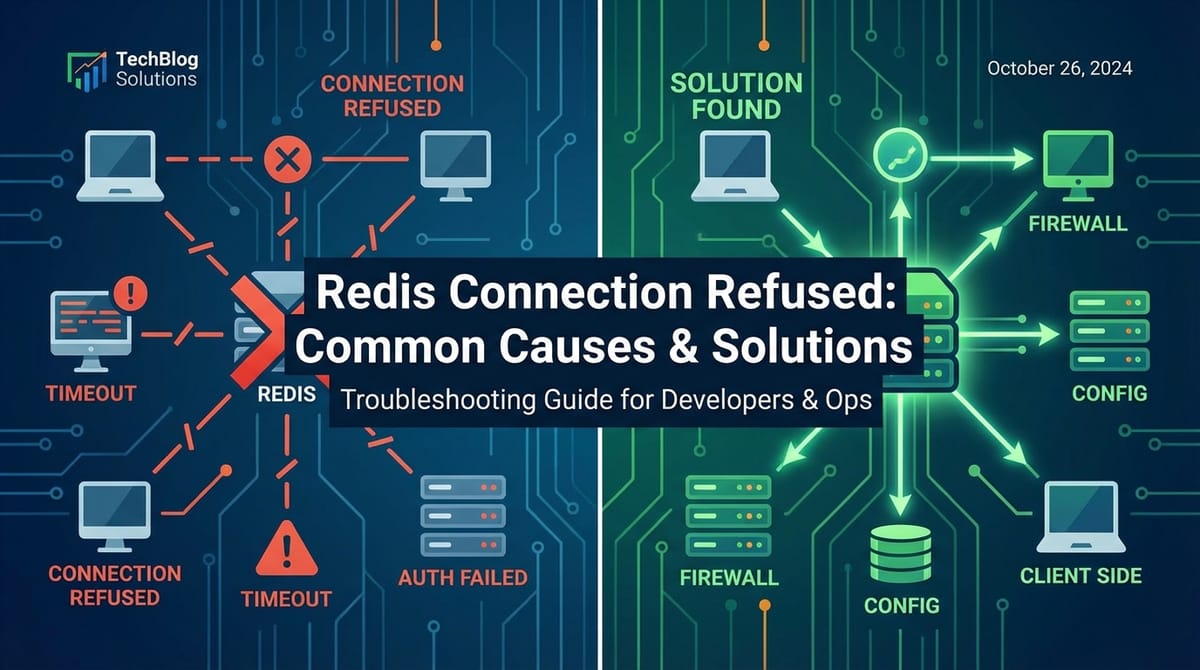
However, despite its inherent reliability and elegant design, encountering the dreaded "Redis Connection Refused" error message is an all too common, profoundly frustrating experience. This seemingly straightforward error, often appearing as Error: connect ECONNREFUSED 127.0.0.1:6379 in a client application or Could not connect to Redis at 127.0.0.1:6379: Connection refused when using the redis-cli tool, signals a complete breakdown in communication between your application or client and the Redis server. It's a digital brick wall, indicating that the operating system on the target machine actively denied the connection attempt, rather than merely timing out or experiencing a network unreachable scenario. The immediate consequence is a critical inability for your application to interact with Redis, leading to data unavailability, feature malfunctions, or even a total application failure. Navigating this error requires a deep understanding of its potential origins, which can span a wide spectrum from simple configuration oversights to complex network topology challenges. This comprehensive guide aims to demystify the "Redis Connection Refused" error, meticulously dissecting its root causes and providing actionable, detailed solutions to help you diagnose, troubleshoot, and ultimately resolve this pervasive issue, restoring the seamless operation of your Redis-dependent systems.
Understanding "Connection Refused": What It Truly Means
When a client application or redis-cli utility attempts to establish a connection to a Redis server and receives a "Connection Refused" error, it's not merely a generic communication failure. This specific error message conveys a precise technical meaning at the operating system and TCP/IP stack level, indicating a distinct phase of the connection establishment process has failed in a very particular way. To fully grasp its implications and guide effective troubleshooting, it's crucial to understand the underlying mechanics.
The TCP/IP connection process, often referred to as the "three-way handshake," begins when a client sends a SYN (synchronize) packet to the server's specified IP address and port. The server, if it's listening on that port and is willing to accept connections, is expected to respond with a SYN-ACK (synchronize-acknowledge) packet. Finally, the client sends an ACK (acknowledge) packet, completing the handshake and establishing the connection.
A "Connection Refused" error occurs when the client sends its initial SYN packet, but the server's operating system responds almost immediately with an RST (reset) packet, rather than a SYN-ACK. This RST packet is a definitive rejection; it’s the server's way of saying, "There's nothing listening on that port," or "I am unwilling to accept your connection at this time." It's a stark contrast to a timeout error, which would typically occur if the SYN packet never received a response, suggesting network black holes or an unresponsive server. The presence of an RST packet confirms that the network path to the server is open, the target IP address exists, and the server's operating system itself is active and processing network requests. The problem, therefore, lies specifically with the server's ability or willingness to accept a connection on the specified port.
The common underlying scenarios that trigger an RST response and subsequently a "Connection Refused" error include:
- No Process Listening on the Port: The most frequent cause. The operating system receives the SYN packet on the specified port but finds no active process (like the Redis server) bound to and listening for incoming connections on that particular port. Without a listening application, the OS has no one to hand the connection over to, so it sends an RST.
- Firewall Actively Denying the Connection: While some firewalls might simply drop packets (leading to timeouts), others are configured to explicitly reject connections on certain ports, sending an RST packet. This is an active denial, signaling that a security rule prevented the connection.
- Server Exceeding Connection Limits: Less common for an immediate "Connection Refused" unless the system is under extreme duress or misconfigured. If the server has a hard limit on the number of simultaneous connections it can accept (e.g.,
maxclientsin Redis, or OS file descriptor limits), and that limit has been reached, the OS or the application itself might be configured to send an RST for new connection attempts rather than queue them or let them time out.
Understanding this technical distinction is crucial for targeted troubleshooting. When you see "Connection Refused," you can immediately rule out many network-level issues like DNS resolution failures or basic IP routing problems, as the initial packet successfully reached the target host. Instead, your focus should narrow down to the server host itself: Is Redis running? Is it configured to listen on the correct network interface and port? Are there any local firewall rules blocking it? Is the server overloaded? By adopting this precise understanding, the troubleshooting process becomes significantly more efficient and less about guesswork.
Common Causes of "Redis Connection Refused" and Their Solutions
Diagnosing a "Redis Connection Refused" error requires a systematic approach, as its root cause can vary widely. Below, we delve into the most common scenarios that lead to this error, offering detailed explanations and practical solutions for each.
1. Redis Server Not Running
Explanation: This is arguably the most straightforward and frequently overlooked cause. For a client to connect to Redis, the Redis server process must be actively running and listening for incoming connections on the specified port. If the Redis server process has crashed, failed to start, or was intentionally stopped, any attempt by a client to connect will be met with a "Connection Refused" error because no application is bound to the Redis port to accept the connection. This can happen due to various reasons, such as system reboots, configuration errors preventing startup, resource exhaustion, or manual intervention.
Detailed Troubleshooting & Solution:
- Verify Process Status:
- Linux/macOS: Use
systemctl status redis(for systemd-based systems like Ubuntu, CentOS 7+) orservice redis status(for older init systems like Debian 8, CentOS 6) to check if Redis is running as a service. If not configured as a service, you might look for the process directly usingps aux | grep redis-server. The output should indicate an "active (running)" state for a service, or show aredis-serverprocess with its associated arguments (e.g., the configuration file path). - Windows: Open the Services manager (search for "Services" in the Start Menu) and look for a service named "Redis" or "Redis Server". Check its status. Alternatively, use
tasklist | findstr redis-server.exein Command Prompt or PowerShell.
- Linux/macOS: Use
- Check Redis Logs: If Redis is not running or failed to start, its logs are your primary source of information for understanding why. The default location for Redis logs is often
/var/log/redis/redis-server.logon Linux, or specified by thelogfiledirective inredis.conf. Examine the most recent entries for error messages, warnings, or indications of startup failures (e.g., "Address already in use," "Can't bind," "Out of memory"). These logs will provide crucial clues about the underlying problem that prevented Redis from starting or caused it to crash. - Attempt to Start Redis:
- As a service:
sudo systemctl start redisorsudo service redis start. After attempting to start, immediately check its status again. - Manually (for testing/development): Navigate to your Redis installation directory and run
redis-server /path/to/redis.conf(replace with your actual config file). If no config file is provided, it will use default settings. Running it this way often prints errors directly to the console, which can be very informative. - Check for Port Conflicts: If the logs indicate "Address already in use," it means another process is already listening on the default Redis port (6379) or the one specified in
redis.conf. Usesudo netstat -tulpn | grep 6379(Linux) orGet-NetTCPConnection | Where-Object {$_.LocalPort -eq 6379} | Select-Object ProcessId, OwningProcess(PowerShell) to identify the conflicting process. You might need to stop the conflicting process, or configure Redis to listen on a different port.
- As a service:
- Ensure Proper Configuration (
redis.conf): Sometimes, a malformed or incorrectredis.conffile can prevent Redis from starting. If you recently modified the configuration, revert the changes or carefully review them for syntax errors. Pay particular attention toport,bind,daemonize, andpidfiledirectives.
By systematically checking the server's status, consulting its logs, and attempting a controlled restart, you can quickly ascertain whether a non-running Redis instance is the culprit and take appropriate corrective actions.
2. Incorrect Host or Port in Client Configuration
Explanation: Even if the Redis server is running perfectly, a "Connection Refused" error will occur if the client application attempts to connect to the wrong IP address (host) or the wrong port number. This is a common oversight, especially in development environments where configurations might change, or when deploying applications across different environments (e.g., local, staging, production) with distinct Redis endpoints. The client sends its SYN packet to an address and port where no Redis server is listening, leading to the OS on the target machine sending an RST.
Detailed Troubleshooting & Solution:
- Verify Client Configuration:
- Code Review: Thoroughly examine your application's source code where the Redis connection is initialized. Look for connection strings, environment variables, or configuration files that define the Redis host (e.g.,
127.0.0.1,localhost,my-redis-host.example.com) and port (e.g.,6379). - Environment Variables: Many modern applications, especially in containerized or cloud environments, rely on environment variables (e.g.,
REDIS_HOST,REDIS_PORT). Double-check that these variables are correctly set in the environment where your application is running. For Docker containers, check thedocker-compose.ymlordocker runcommand for-eflags. For Kubernetes, inspect your Pod definitions forenvfields. - Configuration Files: If your application uses configuration files (e.g.,
.env,application.properties,appsettings.json, YAML files), ensure the Redis connection details within them are accurate and that the correct configuration file is being loaded.
- Code Review: Thoroughly examine your application's source code where the Redis connection is initialized. Look for connection strings, environment variables, or configuration files that define the Redis host (e.g.,
- Check Redis Server's Listening Address and Port:
redis.conf: Open your Redis server'sredis.conffile. Theportdirective specifies the port Redis listens on (default is6379). Thebinddirective specifies the IP addresses Redis should listen on (e.g.,127.0.0.1for local connections only,0.0.0.0for all available interfaces). The client's configured host and port must match these values.redis-cliInfo: If you can connect to Redis from any client (evenredis-clilocally), you can runINFO Serverto see thetcp_portandbind_addressesfields. This confirms what Redis is actively listening on.netstat/ss: On the Redis server, usesudo netstat -tulpn | grep redis-serverorsudo ss -tuln | grep 6379to see which IP addresses and ports the Redis process (redis-server) is currently listening on. The output0.0.0.0:6379means it's listening on all interfaces on port 6379.127.0.0.1:6379means it's only listening for connections from the local machine.
- Ensure Consistency: The host and port specified in the client configuration must precisely match the host and port that the Redis server is actually listening on. A common scenario is when Redis is bound to
127.0.0.1(localhost) but the client tries to connect to the server's public IP address, or vice versa if Redis is bound to0.0.0.0but the client is configured with127.0.0.1and running on a different machine. - DNS Resolution: If your client uses a hostname (e.g.,
my-redis-server.local) instead of an IP address, ensure that the hostname correctly resolves to the Redis server's IP address. Useping my-redis-server.localornslookup my-redis-server.localfrom the client machine to verify DNS resolution. Incorrect DNS entries can lead the client to attempt connection to a non-existent or incorrect host.
By meticulously comparing the client's connection parameters with the Redis server's actual listening configuration, you can often pinpoint this common source of connection refusal.
3. Firewall Issues
Explanation: Firewalls, both on the Redis server host and potentially intermediary network devices, are designed to restrict network traffic. If a firewall is configured to block incoming connections to the Redis port (default 6379) from the client's IP address or subnet, the connection attempt will be actively rejected. The firewall, acting as a gatekeeper, will intercept the client's SYN packet and respond with an RST packet, preventing it from ever reaching the Redis server process. This is a crucial security measure but a frequent cause of "Connection Refused" errors in development and deployment.
Detailed Troubleshooting & Solution:
- Server-Side Firewall (Linux:
ufw,iptables,firewalld):ufw(Uncomplicated Firewall - common on Ubuntu/Debian):- Check status:
sudo ufw status verbose - Look for rules blocking port 6379. If it's enabled and blocking, you'll see a
DENYrule for port 6379 or a generalDENYfor incoming traffic. - Allow the port:
sudo ufw allow 6379/tcp. If your client has a specific IP (e.g.,192.168.1.100), you can allow it from that IP only:sudo ufw allow from 192.168.1.100 to any port 6379. - Reload
ufw:sudo ufw reload.
- Check status:
iptables(low-level firewall - often used directly or byufw/firewalld):- Check rules:
sudo iptables -L -n -v(for IPv4) andsudo ip6tables -L -n -v(for IPv6). - Look for
DROPorREJECTrules targeting TCP port 6379 in theINPUTchain. - To temporarily allow (will be lost on reboot unless saved):
sudo iptables -A INPUT -p tcp --dport 6379 -j ACCEPT. This rule should be placed before any generalREJECT/DROPrules. - To save (system-dependent, e.g.,
sudo netfilter-persistent saveor specificiptables-save/iptables-restorescripts).
- Check rules:
firewalld(common on CentOS/RHEL):- Check status:
sudo firewall-cmd --state - List active zones and services:
sudo firewall-cmd --get-active-zones - List rules for a specific zone (e.g.,
public):sudo firewall-cmd --zone=public --list-all - Allow the port:
sudo firewall-cmd --zone=public --add-port=6379/tcp --permanent(for persistence) - Reload firewall:
sudo firewall-cmd --reload
- Check status:
- Cloud Provider Security Groups/Network ACLs:
- If your Redis server is hosted on a cloud platform (AWS EC2, Google Cloud Compute Engine, Azure Virtual Machines), their network security features are analogous to firewalls.
- AWS: Check the Security Group attached to your EC2 instance. Ensure an inbound rule exists that allows TCP traffic on port 6379 from your client's IP address (or
0.0.0.0/0for public access, though this is less secure for production). Also, check any Network Access Control Lists (NACLs) associated with the subnet. - Google Cloud: Examine Firewall Rules for your VPC network. Create or modify a rule to allow TCP port 6379 ingress from the required source IP ranges.
- Azure: Review Network Security Groups (NSGs) associated with your VM or its subnet. Add an inbound security rule to permit TCP traffic on port 6379.
- Verify that these cloud-level firewalls are not inadvertently blocking your connection attempts. They often sit before the OS-level firewall on the instance.
- Client-Side Firewall: While less common for "Connection Refused" (more likely for client-side connection timeouts), ensure your client machine's firewall isn't preventing outbound connections to the Redis server's IP and port. This is usually not the case unless very strict outbound rules are in place.
- Network Intermediate Firewalls/Routers: In complex corporate networks, there might be hardware firewalls or routers between your client and the Redis server. If you suspect this, you'll need to consult with your network administrators to ensure that TCP port 6379 is open bi-directionally between the client and server subnets.
- Testing Connectivity with
telnetornc:- From the client machine, attempt
telnet <redis-server-ip> 6379ornc -vz <redis-server-ip> 6379. - If
telnethangs orncreportsConnection refused, it strongly points to a firewall orbindissue. Iftelnetimmediately connects and shows a blank screen (orncreports "succeeded"), then the network path is open, and a process is listening, suggesting the problem might be higher up (e.g., authentication, protocol).
- From the client machine, attempt
Firewalls are essential for security, but they are also a leading cause of connection woes. Systematically checking all layers of firewalls—from the cloud provider to the host OS—is a critical step in troubleshooting "Connection Refused" errors.
4. Network Connectivity Problems
Explanation: For a "Connection Refused" error, the client's SYN packet must reach the server's operating system. This implies that basic network connectivity exists at least up to the server's network stack. However, while less likely to directly cause a refused connection (timeouts are more common for pure network outages), subtle network issues can sometimes manifest in ways that masquerade as or contribute to connection refusals, especially in complex or misconfigured environments. For instance, if the client is trying to reach a non-existent IP address due to an incorrect DNS resolution, the client might eventually receive an RST from an entirely different, unintended host, or the connection attempt might fail at the routing level before even attempting a connection. Also, if there are multiple network interfaces or virtual network configurations, the traffic might be misrouted within the server itself.
Detailed Troubleshooting & Solution:
- Verify Basic IP Reachability:
ping: From the client machine, runping <redis-server-ip>. A successful response indicates basic IP-level connectivity. Ifpingfails (100% packet loss), then you have a fundamental network issue that needs to be addressed first (e.g., incorrect IP, network cable disconnected, routing problem). Remember that some firewalls block ICMP (ping) requests, so a failed ping doesn't always mean no connectivity, but a successful one is a good sign.- DNS Resolution: If you're connecting via a hostname, ensure it resolves to the correct IP address using
nslookup <hostname>ordig <hostname>. An incorrect DNS entry could point your client to a server where Redis isn't running or isn't supposed to be.
- Trace Network Path (
traceroute/tracert):- From the client, run
traceroute <redis-server-ip>(Linux/macOS) ortracert <redis-server-ip>(Windows). This command shows the path packets take to reach the server. - Look for unexpected hops, high latency, or failures at intermediate routers. While this typically leads to timeouts rather than refusals, it helps confirm the path.
- Ensure that the
traceroutecompletes and reaches the target Redis server's IP.
- From the client, run
- Check Server Network Interfaces:
- On the Redis server, use
ip addr showorifconfigto list all active network interfaces and their assigned IP addresses. - Ensure that the IP address the client is trying to connect to is actually configured and active on one of the server's network interfaces.
- Verify that the interface is
UPand has the correct subnet mask and gateway.
- On the Redis server, use
- Route Tables:
- On both the client and server, examine the routing tables (
ip route showon Linux,route printon Windows) to ensure there's a valid route for packets to traverse between them. - If the client and server are on different subnets, verify that the default gateways are correctly configured and that routers between the subnets have appropriate routes.
- On both the client and server, examine the routing tables (
- Subtle Layer 2 Issues: In virtualized environments (e.g., VMs, containers) or complex networks, even if IP is reachable, lower-level network issues can sometimes cause strange behavior. For example, ARP resolution problems or VLAN misconfigurations can prevent a server from properly receiving or responding to SYN packets, or direct them incorrectly. While these typically lead to timeouts or unreachability, it's worth considering if all other IP-level checks pass but connectivity remains elusive.
- Restart Network Services (if applicable): If network configurations were recently changed, restarting network services (
sudo systemctl restart networkingorsudo service network restarton Linux, or server reboot) might be necessary to apply them correctly.
While direct network outages usually result in timeouts, understanding and verifying network connectivity is a fundamental prerequisite. Ensuring the client can reach the intended Redis server's IP address and that the server's network interfaces are properly configured helps eliminate a range of underlying issues that could indirectly contribute to or mask the "Connection Refused" error.
5. Binding Issues (Redis bind Directive)
Explanation: The bind directive in the redis.conf file is a crucial security and networking setting. It dictates which network interfaces (IP addresses) the Redis server should listen on for incoming connections. If Redis is configured to bind only to 127.0.0.1 (localhost), it will exclusively accept connections originating from the same machine where Redis is running. Any attempt to connect from a different machine, even if the network path is clear and firewalls are open, will result in a "Connection Refused" error because Redis is not listening on the external network interface. Similarly, if it's bound to a specific non-existent IP address, it won't be reachable.
Detailed Troubleshooting & Solution:
- Locate and Inspect
redis.conf:- Find your Redis configuration file, typically named
redis.conf. Its location varies but common paths include/etc/redis/redis.conf,/usr/local/etc/redis.conf, or in the directory where you runredis-server. - Open the file and search for the
binddirective.
- Find your Redis configuration file, typically named
- Understand
bindDirective Values:# bind 127.0.0.1 -::1(default in newer Redis versions): This configuration makes Redis listen only on the local IPv4 loopback interface (127.0.0.1) and the local IPv6 loopback interface (::1). This is the most secure default for development but prevents remote connections.bind 127.0.0.1: This explicitly binds Redis to the IPv4 localhost interface. Remote connections will be refused.bind 0.0.0.0: This configures Redis to listen on all available network interfaces for IPv4 connections. This is necessary for remote clients to connect.bind <specific-ip-address>: You can bind Redis to one or more specific IP addresses (e.g.,bind 192.168.1.100). If your client is connecting to a different IP address of the server, or the specified IP is not the one the client expects, connections will be refused.- Multiple
binddirectives: You can specify multiple IP addresses, likebind 127.0.0.1 192.168.1.100.
- Adjust
bindfor Remote Access:- For public access (use with extreme caution and strong authentication): If you need Redis to be accessible from any network interface (e.g., across a LAN or the internet, though the latter is highly discouraged without robust security), change the
binddirective tobind 0.0.0.0. - For specific IP access (recommended for controlled environments): If Redis should only be accessible from certain internal networks or specific client IPs, bind it to the IP address of the server that faces those networks, e.g.,
bind 192.168.1.100. Ensure this IP address is active on your server. - Remove
binddirective entirely: If thebinddirective is commented out or not present, older Redis versions might bind to all interfaces by default. Newer versions (Redis 6.0+) default tobind 127.0.0.1 -::1, so explicitly settingbind 0.0.0.0or a specific IP is required for remote access. - Security Warning: Exposing Redis to
0.0.0.0without strong authentication (requirepass) and robust firewall rules is a significant security risk. Redis was not designed with strong internal security mechanisms by default and is vulnerable to attacks if left open. Always combinebind 0.0.0.0with firewalls andrequirepass.
- For public access (use with extreme caution and strong authentication): If you need Redis to be accessible from any network interface (e.g., across a LAN or the internet, though the latter is highly discouraged without robust security), change the
- Restart Redis: After modifying
redis.conf, you must restart the Redis server for the changes to take effect.sudo systemctl restart redis(for service)- Or stop
redis-serverand start it again with the updated config file.
- Verify Listening Interfaces: After restarting, use
sudo netstat -tulpn | grep redis-serverorsudo ss -tuln | grep 6379on the Redis server to confirm that Redis is now listening on the expected IP addresses and ports.- You should see
0.0.0.0:6379if it's listening on all interfaces, or the specific IP address you configured. If it still shows127.0.0.1:6379despite your changes, double-check that you edited the correctredis.conffile and that Redis is loading it.
- You should see
Table: Common Redis bind Configurations and Their Implications
bind Directive in redis.conf |
Effect on Redis Server | Accessibility for Clients | Security Considerations |
|---|---|---|---|
# bind 127.0.0.1 -::1 |
(Default in Redis 6.0+) Listens on local IPv4 and IPv6 loopback only. | Local clients only. Clients on the same machine (using 127.0.0.1 or localhost) can connect. Remote clients will be refused. |
Highly secure by default. Prevents unauthorized external access. Ideal for development or when Redis is accessed only by applications on the same host. |
bind 127.0.0.1 |
Listens on local IPv4 loopback interface only. | Local clients only. Same as above. Remote clients will be refused. | Secure. Explicitly restricts access to the local machine. Good for when Redis serves only local applications or is part of a local microservice. |
bind 0.0.0.0 |
Listens on all available IPv4 network interfaces. | Local and Remote clients. Any client that can reach the server's IP address on the network can attempt to connect (subject to firewalls). | Least secure without additional measures. Exposes Redis to all networks. Requires strong firewall rules (to restrict source IPs) and Redis requirepass authentication to prevent unauthorized access and potential data breaches/attacks. |
bind 192.168.1.100 |
Listens only on the specified IP address (e.g., a specific LAN IP). | Clients on the same network that can reach that specific IP. Connections to other IPs of the server will be refused. | More secure than 0.0.0.0. Restricts access to a particular network interface. Still requires firewall rules and requirepass if clients on that network are untrusted or if the network is exposed. Good for multi-homed servers. |
bind 127.0.0.1 192.168.1.100 |
Listens on multiple specified IP addresses. | Clients that can reach either of the specified IP addresses. Allows access from localhost and a specific internal network. | Moderately secure. Provides controlled access. Follows security principles of bind <specific-ip-address>. Useful in scenarios where both local and specific remote access is needed. |
Misconfiguring the bind directive is a very frequent cause of "Connection Refused" when moving Redis deployments or integrating with remote applications. Correcting this often involves a simple but critical change in redis.conf followed by a server restart.
6. Max Clients Exceeded
Explanation: Redis, like any server application, has a finite capacity for handling simultaneous client connections. This capacity is primarily governed by the maxclients directive in redis.conf and, at a lower level, by the operating system's file descriptor limits. If the number of active client connections reaches the maxclients threshold, Redis will actively refuse any new incoming connection attempts. When a new client tries to connect, Redis will send an RST packet because it cannot accept the connection, resulting in a "Connection Refused" error. This scenario typically occurs under heavy load or due to application-level connection leaks.
Detailed Troubleshooting & Solution:
- Check Redis
maxclientsConfiguration:- Locate the
redis.conffile and search for themaxclientsdirective. - The default
maxclientsvalue is usually 10000, which is generally ample for most applications. However, if it has been explicitly set to a lower value, or if your application requires a massive number of concurrent connections, this could be the bottleneck. - If
maxclientsis commented out, it uses the default (usually 10000).
- Locate the
- Check Current Client Connections:
- If you can connect to Redis from
redis-cli(e.g., locally or ifmaxclientshasn't been hit yet), runINFO Clients. - Look at the
connected_clientsfield. This shows the current number of active connections. If it's close to or equal to yourmaxclientslimit, then this is likely the cause. - You can also use
CLIENT LISTto see details of each connected client, which might help identify applications that are holding too many connections.
- If you can connect to Redis from
- Check Operating System File Descriptor Limits:
- Redis itself uses file descriptors for each client connection, as well as for persistence files (RDB/AOF). The
maxclientssetting is typically capped by the OS file descriptor limit. - On Linux, check the system-wide limit:
cat /proc/sys/fs/file-max. - Check the limit for the Redis process itself:
cat /proc/<redis-pid>/limits(replace<redis-pid>with the actual process ID ofredis-server). Look forMax open files. - To increase the system-wide limit, edit
/etc/sysctl.confand add/modifyfs.file-max = <new_limit>. Apply withsudo sysctl -p. - To increase the limit for the Redis service, edit
/etc/systemd/system/redis.service(or/etc/init.d/redis-server) and addLimitNOFILE=<new_limit>under the[Service]section (for systemd). Thensudo systemctl daemon-reloadandsudo systemctl restart redis. Ensure this value is higher than or equal to yourmaxclientssetting.
- Redis itself uses file descriptors for each client connection, as well as for persistence files (RDB/AOF). The
- Solution Strategies:
- Increase
maxclients: If appropriate, increase themaxclientsvalue inredis.confand restart Redis. Only do this if your server has sufficient memory and CPU resources to handle the increased load. - Implement Connection Pooling: This is the most robust and recommended solution at the application level. Instead of each request creating and closing a new Redis connection, a connection pool maintains a fixed set of open connections that can be reused. This significantly reduces the overhead of connection establishment and ensures that the number of active connections to Redis remains within reasonable limits. Most Redis client libraries offer built-in connection pooling mechanisms.
- Identify and Fix Connection Leaks: If your application isn't properly closing Redis connections, it can lead to a gradual accumulation of open connections, eventually hitting
maxclients. Review your application code to ensure all connections are explicitly closed or managed by a connection pool that handles resource release. - Scale Redis: If your application genuinely requires more connections than a single Redis instance can handle, consider scaling strategies such as Redis Cluster (sharding data across multiple instances) or setting up replicas for read scaling.
- Optimize Application Logic: Examine if your application is making unnecessary or excessively frequent connections to Redis. Batching operations or caching data at a higher layer might reduce the connection pressure.
- Increase
When Redis is refusing connections due to maxclients being reached, it's a clear signal that your system is either under extreme load or, more commonly, that your application's connection management needs improvement. Addressing this often involves a combination of configuration tuning and application-side architectural adjustments.
7. Authentication Issues (requirepass Directive)
Explanation: For security reasons, Redis supports password-based authentication. If the requirepass directive is configured in redis.conf with a password, any client attempting to connect must first authenticate with the correct password using the AUTH command. If a client tries to issue commands without authenticating, or with an incorrect password, Redis will typically terminate the connection or actively reject subsequent commands, which can sometimes manifest as a "Connection Refused" error, although more often it's an "Authentication required" or "NOAUTH Authentication required" error. However, a malformed AUTH command or an unexpected authentication flow from a client library could potentially lead to a refusal. More directly, if a client library tries to connect and implicitly sends some command before AUTH when requirepass is enabled, Redis might refuse that initial interaction.
Detailed Troubleshooting & Solution:
- Check
redis.confforrequirepass:- Open your
redis.conffile and search for therequirepassdirective. - If it's uncommented and followed by a password (e.g.,
requirepass your_strong_password), then authentication is enabled, and your client must provide this password. - Note down the configured password carefully.
- Open your
- Verify Client Authentication Configuration:
- Application Code/Config: Inspect your application's Redis client configuration. It should have a field for the password (e.g.,
password,auth_pass,redis_password). Ensure this value precisely matches therequirepassvalue inredis.conf. - Environment Variables: If using environment variables, ensure the password variable is correctly set and passed to the application.
redis-cli: When connecting withredis-cli, you can authenticate in two ways:redis-cli -h <host> -p <port> -a <password>(recommended for one-off use)- Connect first (
redis-cli -h <host> -p <port>), then typeAUTH <password>at the prompt.
- Application Code/Config: Inspect your application's Redis client configuration. It should have a field for the password (e.g.,
- Common Mistakes:
- Mismatched Passwords: A typo in either
redis.confor the client configuration. requirepassenabled on server, but not configured in client: The client attempts to connect without providing any password.requirepassnot enabled on server, but client sends a password: While usually not causing a "Connection Refused" (Redis would simply ignore the password), it's a configuration mismatch.- Special Characters: If the password contains special characters, ensure proper escaping or quoting in both
redis.confand the client's configuration.
- Mismatched Passwords: A typo in either
- Solution Steps:
- If
requirepassis enabled: Ensure your client application is configured to send the exact password specified inredis.conf. - If
requirepassis not intended: If you're encountering authentication-related issues and don't need authentication (e.g., in a secure internal network protected by firewalls), you can comment out or remove therequirepassdirective fromredis.confand restart Redis. This is generally discouraged for production environments without robust network isolation. - Test with
redis-cli: Try connecting from the client machine usingredis-cli -h <redis-server-ip> -p 6379 -a <your-password>. If this works, then the issue lies specifically with your application's client library or configuration. Ifredis-clistill refuses or fails to authenticate, the problem might be with therequirepasssetting itself or a more fundamental connectivity issue.
- If
Authentication failures can be tricky, as Redis might respond with various error types depending on the client library and the exact moment of failure. Always double-check password consistency across server and client configurations.
8. Operating System Resource Limits
Explanation: Beyond Redis's internal maxclients limit, the underlying operating system imposes its own resource limits on processes, which can directly or indirectly lead to connection refusal. The most common and impactful of these is the "maximum number of open file descriptors" (often referred to as ulimit -n). In Unix-like systems, every network connection, file, and pipe is treated as a file descriptor. If the Redis server process or the entire system reaches its allocated limit for open file descriptors, it cannot accept new connections or open new files, resulting in a "Connection Refused" error for new connection attempts. Other resource limits, such as available memory or CPU, can also cause Redis to crash or become unresponsive, indirectly leading to refusal.
Detailed Troubleshooting & Solution:
- Check File Descriptor Limits (Most Common OS Limit):
- Current limits for the Redis process:
- First, find the Process ID (PID) of your Redis server:
ps aux | grep redis-server. - Then, check its limits:
sudo cat /proc/<redis-pid>/limits. Look forMax open files.
- First, find the Process ID (PID) of your Redis server:
- System-wide limits:
cat /proc/sys/fs/file-max. ulimitfor the user running Redis (if started manually):ulimit -n.- Redis itself has a
maxclientssetting, but it cannot exceed thenofile(number of open files) limit set by the OS for the Redis process. Redis logs often warn if themaxclientssetting is higher than the OSnofilelimit, automatically adjustingmaxclientsdown.
- Current limits for the Redis process:
- Increase File Descriptor Limits:
- System-wide: Edit
/etc/sysctl.conf(or create a file like/etc/sysctl.d/99-redis.conf) and add/modifyfs.file-max = 65536(or a higher value). Apply withsudo sysctl -p. - Per-user/Per-service (recommended for Redis):
- For systemd services (e.g., Ubuntu, CentOS 7+): Edit the Redis service unit file, typically
/etc/systemd/system/redis.serviceor/lib/systemd/system/redis-server.service. AddLimitNOFILE=65536(or a suitable value like 100000) under the[Service]section. Then runsudo systemctl daemon-reloadandsudo systemctl restart redis. - For older init systems (
/etc/init.d): You might need to addulimit -n 65536in the Redis startup script itself or in/etc/security/limits.conffor theredisuser. - Important: Ensure the value for
LimitNOFILEis sufficiently higher than yourmaxclientssetting inredis.conf.
- For systemd services (e.g., Ubuntu, CentOS 7+): Edit the Redis service unit file, typically
- System-wide: Edit
- Other Resource Limits (Less Common for Direct Refusal, but can cause crashes):
- Memory: If Redis runs out of memory (due to
maxmemorysetting or general system RAM exhaustion), it might crash, leading to a "Connection Refused" because the server is no longer running. MonitorINFO memoryinredis-cliand system memory usage (free -h,top). Adjustmaxmemoryinredis.confif necessary, or add more RAM. - CPU: While not directly causing connection refusal, extremely high CPU utilization can make Redis unresponsive, potentially leading to timeouts or, in severe cases, crashes that result in refusal. Monitor CPU usage (
top,htop). - TCP Backlog: The
tcp-backlogdirective inredis.conf(default 511) controls the maximum number of pending connections that Redis can queue before accepting them. If this queue overflows, new connections might be refused. Increasing this value can help during connection spikes, but it's usually not the primary cause unless other resource limits are being hit simultaneously.
- Memory: If Redis runs out of memory (due to
- Check System Logs: Always check
dmesgoutput (dmesg -T) and/var/log/syslog(orjournalctl -xe) for messages related to resource exhaustion, kernel warnings, or OOM (Out Of Memory) killer activations, which might indicate a system-level problem.
Addressing operating system resource limits, particularly file descriptors, is vital for high-concurrency applications like Redis. Ensuring Redis has adequate resources prevents it from hitting these lower-level ceilings and refusing legitimate connection attempts.
9. Incorrect Protocol/SSL/TLS Misconfiguration
Explanation: Redis, by default, communicates using its own plain-text RESP (REdis Serialization Protocol) over standard TCP. It does not natively support SSL/TLS encryption out-of-the-box in the main server process. If a client library is explicitly configured to use SSL/TLS when connecting to a standard, non-SSL Redis server, or if there's a misconfiguration in an SSL proxy (like stunnel or Redis-TLS), the connection will fail. The server will receive encrypted traffic it cannot understand, or the proxy will fail to establish the underlying connection to Redis, leading to a "Connection Refused" error or a protocol error, as the connection handshake cannot complete successfully.
Detailed Troubleshooting & Solution:
- Determine Redis Server's SSL/TLS Status:
- Default Redis: By default, a standard Redis server does not support SSL/TLS directly. If your Redis is a vanilla installation, it expects plain TCP.
stunnel/Redis-TLS: If you're using a proxy likestunnelor a dedicated Redis-TLS build to add SSL/TLS capabilities, then the client should connect to the proxy's SSL port, and the proxy then connects to the unencrypted Redis port.- Cloud Providers: Some managed Redis services (e.g., AWS ElastiCache, Azure Cache for Redis) offer native SSL/TLS support. You must check their specific documentation.
- Verify Client SSL/TLS Configuration:
- Application Client Library: Examine your application's Redis client configuration. Look for settings like
ssl=true,use_tls=true,ssl_ca_certs,ssl_certfile,ssl_keyfile. - If client expects SSL but server is plain TCP:
- The client library will initiate an SSL handshake, which the plain-text Redis server will not understand. This often results in a "Connection Refused" or an immediate protocol error (e.g.,
Error: Protocol error, expected '*' but got 'G'). - Solution: Disable SSL/TLS in your client configuration if the Redis server is not configured for SSL.
- The client library will initiate an SSL handshake, which the plain-text Redis server will not understand. This often results in a "Connection Refused" or an immediate protocol error (e.g.,
- Application Client Library: Examine your application's Redis client configuration. Look for settings like
- Verify SSL/TLS Proxy Configuration (if applicable):
- If you're using
stunnelor similar:- Ensure
stunnelis running and listening on the expected SSL port. - Check
stunnellogs for errors connecting to the backend Redis server. A "Connection Refused" here might meanstunnelitself can't reach Redis (e.g., Redis not running, bind issue, firewall betweenstunneland Redis). - Verify
stunnel's configuration (stunnel.conf) for correctaccept(SSL port for clients) andconnect(plain Redis port for backend) directives. - Ensure all necessary certificates and keys are correctly specified and accessible by
stunnel.
- Ensure
- If you're using
- Mixed Protocol Environments:
- It's possible to have a Redis instance accessible via both SSL (through a proxy) and plain TCP (directly). Ensure your client is connecting to the correct port for the desired protocol. Connecting an SSL-enabled client to the plain-text port will fail.
- Test with
redis-cli:redis-cliby default connects via plain TCP. If your Redis server is plain TCP,redis-cli -h <host> -p 6379should work (subject to other issues).- If your Redis server is configured with SSL/TLS (e.g., managed service),
redis-clioften has an--tlsor--sslflag (e.g.,redis-cli --tls -h <host> -p 6379). Ifredis-cli --tlsworks, but your application doesn't, the issue is likely in your application's SSL/TLS setup.
Protocol mismatches, especially concerning SSL/TLS, are a common source of cryptic connection errors. Always ensure that both the client and server (or any intermediary proxy) are aligned on the expected communication protocol.
10. Network Interface Down/Misconfigured on Server
Explanation: For a Redis server to accept connections from clients, the network interface it's bound to must be active and correctly configured with an IP address reachable by clients. If the physical network interface (e.g., eth0, en0) is down, or if its IP address configuration is incorrect (e.g., wrong subnet mask, missing default gateway, a non-existent IP in the bind directive), then any connection attempt will fail. While a truly "down" interface might result in a "Host Unreachable" or timeout, a misconfigured interface might still allow some lower-level traffic but prevent the full TCP handshake on the expected Redis port, potentially leading to a "Connection Refused" if the OS can't properly route the incoming SYN to the Redis process or if Redis is specifically bound to an unusable IP.
Detailed Troubleshooting & Solution:
- Check Network Interface Status:
- On the Redis server, use
ip addr show(modern Linux) orifconfig(older Linux/macOS) to list all network interfaces. - Look for the interface that carries traffic from your client (e.g.,
eth0,ens33). - Verify that the interface is in an
UPstate. If it'sDOWN, you'll see "state DOWN" or similar. - Solution: Bring the interface up:
sudo ip link set <interface-name> up(e.g.,sudo ip link set eth0 up).
- On the Redis server, use
- Verify IP Address Configuration:
- Ensure the interface has the correct IP address assigned.
- If Redis is bound to a specific IP address using the
binddirective inredis.conf, confirm that this IP address is indeed configured on one of the server's active interfaces. - Check the subnet mask and ensure it's correct for your network topology.
- Solution: Correct any misconfigured IP addresses. This often involves editing network configuration files (e.g.,
/etc/netplan/*.yamlon Ubuntu,/etc/sysconfig/network-scripts/ifcfg-<interface-name>on CentOS/RHEL) and then applying changes (sudo netplan applyorsudo systemctl restart network).
- Check Default Gateway and Routing Table:
- If your client and Redis server are on different subnets, the Redis server needs a correct default gateway to send response packets back to the client.
- On the Redis server, check the routing table:
ip route show. Look for a default route (default via <gateway-ip> dev <interface-name>). - If the default gateway is missing or incorrect, it can lead to asymmetric routing where the client's SYN packet reaches Redis, but Redis's SYN-ACK (or RST) response cannot find its way back, potentially causing the client to eventually timeout, or in some edge cases, misinterpret the situation as a refusal.
- Solution: Configure the correct default gateway in your network configuration.
- DNS Issues on Server (less common for "Refused," but good practice):
- Ensure the Redis server can resolve external hostnames (e.g., for updates, or if Redis itself needs to connect to other services). Check
/etc/resolv.conf.
- Ensure the Redis server can resolve external hostnames (e.g., for updates, or if Redis itself needs to connect to other services). Check
- Virtualization/Container Networking:
- If Redis is running in a VM (Virtual Machine) or Docker container, the networking is abstracted.
- VM: Ensure the VM's virtual network adapter is correctly configured and bridged/NATted to the host's network in a way that allows client traffic.
- Docker: If Redis is in a Docker container, ensure port mapping is correct (e.g.,
-p 6379:6379indocker runorports:indocker-compose.yml) and that the container's network mode allows external access if needed. Thebinddirective inside the container should generally be0.0.0.0or its container IP.
Ensuring robust and correctly configured network interfaces on the Redis server is a foundational step. Even seemingly minor misconfigurations can cascade into connection failures, sometimes presenting as a "Connection Refused" error.
11. Corrupted Redis Data or Configuration
Explanation: While less direct, a corrupted redis.conf file or corrupted persistence files (RDB snapshot or AOF file) can prevent the Redis server from starting up correctly or cause it to crash shortly after starting. If Redis fails to initialize due to these issues, no process will be listening on the designated port, leading to a "Connection Refused" error for any client attempts. A syntax error in redis.conf can be particularly insidious as it often prevents Redis from ever reaching a listening state. Similarly, a severely corrupted AOF file might cause Redis to abort startup during the loading phase.
Detailed Troubleshooting & Solution:
- Inspect
redis.conffor Syntax Errors:- If you've recently modified
redis.conf, carefully review your changes for typos, incorrect directives, or missing values. A single misplaced character can prevent Redis from parsing the file correctly. - Test Configuration: You can often test the configuration file syntax without starting the server using
redis-server --test-conf /path/to/redis.conf. This command will parse the configuration file and report any syntax errors or problematic settings, which is invaluable for pre-deployment validation. - Solution: Correct any syntax errors. If unsure, revert to a known good backup of
redis.confor start with a fresh default configuration file and reapply your necessary changes incrementally.
- If you've recently modified
- Check Redis Server Logs for Startup Failures:
- As mentioned earlier, the Redis log file (e.g.,
/var/log/redis/redis-server.log) is critical. - Look for messages specifically related to configuration parsing errors, "Failed to load AOF/RDB file," "Invalid argument," or any other error that occurs immediately after startup. These errors will pinpoint the exact line or issue in the configuration or data files.
- As mentioned earlier, the Redis log file (e.g.,
- Address Corrupted Persistence Files (AOF and RDB):
- AOF Corruption: If Redis fails to start due to a corrupted Append Only File (
appendonly.aof), Redis often logs an error indicating this.- Solution: Redis provides a utility to fix AOF files:
redis-check-aof --fix /path/to/appendonly.aof. Before doing this, always make a backup of your AOF file. This utility attempts to reconstruct a valid AOF by discarding corrupted entries. After fixing, try restarting Redis.
- Solution: Redis provides a utility to fix AOF files:
- RDB Corruption: If Redis fails to load an RDB snapshot (
dump.rdb), similar errors will appear in the logs.- Solution: Redis also has a utility for RDB checks:
redis-check-rdb /path/to/dump.rdb. If it indicates corruption, you might need to recover from an older RDB backup or the AOF (ifappendonlyis enabled and the AOF is intact) or start Redis without persistence enabled (which will lose data).
- Solution: Redis also has a utility for RDB checks:
- Temporary Disable Persistence: For troubleshooting, you can temporarily comment out
appendonly yesandsavedirectives inredis.confand restart Redis. If it starts successfully then, the problem is definitively related to your persistence files. You can then try to troubleshoot the corrupted files more safely. - Delete Corrupted Files (Data Loss Risk!): As a last resort, if you have no recent backups and data loss is acceptable (e.g., development environment, cache data), you can delete the
appendonly.aofanddump.rdbfiles. Redis will then start with an empty dataset. Exercise extreme caution with this step as it WILL lead to data loss if not handled properly.
- AOF Corruption: If Redis fails to start due to a corrupted Append Only File (
- Permissions Issues: Ensure the Redis user has read/write permissions to
redis.conf, the log file, and the directory where RDB/AOF files are stored. Incorrect permissions can prevent Redis from loading configuration or persistence files.
A robust Redis setup involves valid configuration and healthy persistence files. Corruption in either can prevent the server from becoming available, resulting in connection refusal. Regular backups of configuration and persistence files are invaluable for quick recovery.
12. Container/Virtualization Network Issues
Explanation: When Redis is deployed within containerization platforms like Docker or orchestration systems like Kubernetes, the networking stack is abstracted and virtualized. This introduces an additional layer of complexity where "Connection Refused" can arise not from the Redis server itself, but from the interaction between the container's network, the host's network, and the way ports are exposed and services are managed. Common issues include incorrect port mappings, containers running on internal networks inaccessible to the client, or Kubernetes Service misconfigurations.
Detailed Troubleshooting & Solution (Docker, Kubernetes Examples):
- Docker Containers:
- Incorrect Port Mapping:
- Explanation: When running a Docker container, you must explicitly map the container's internal port (where Redis listens, typically 6379) to a port on the host machine. If this mapping is incorrect or missing, clients trying to connect to the host's port will receive "Connection Refused" because the host isn't forwarding that port to the container.
- Verify: Check your
docker runcommand ordocker-compose.ymlfile. Look for the-porports:directive. Example:-p 6379:6379maps host port 6379 to container port 6379. - Solution: Ensure the port mapping is correct (
host_port:container_port). If Redis inside the container is configured to listen on a non-standard port (e.g., 6380), the mapping should reflect that (e.g.,-p 6379:6380).
- Container Not Running/Crashed:
- Explanation: If the Redis container itself has stopped or crashed, Redis is obviously not running, leading to refusal.
- Verify:
docker ps -awill show all containers, including stopped ones.docker logs <container-name-or-id>will show container logs. - Solution: Start the container (
docker start <container-name-or-id>) and check its logs for startup errors.
bindDirective within Container:- Explanation: By default, Redis in a container should bind to
0.0.0.0to be accessible through Docker's network bridge. If it's configured tobind 127.0.0.1inside the container, it will only be accessible from within that same container, and port mappings won't help external access. - Verify: If you're using a custom
redis.confin your container, ensurebind 0.0.0.0(or comment outbinddirective if older Redis defaults to all interfaces) is set. - Solution: Adjust
redis.confused by the container.
- Explanation: By default, Redis in a container should bind to
- Incorrect Port Mapping:
- Kubernetes (K8s) Deployments:
- Service Misconfiguration:
- Explanation: In Kubernetes, you typically access a Redis Pod through a
Service. If theServicedefinition (e.g.,ClusterIP,NodePort,LoadBalancer) is incorrect, or if the selectors don't match the Redis Pods, clients won't be able to reach Redis. - Verify:
- Check
kubectl get svcfor your Redis service. Ensure itsTYPE,CLUSTER-IP, andPORT(S)are as expected. - Check
kubectl describe svc <redis-service-name>for events or errors. - Verify the
selectorin yourServicedefinition matches thelabelson your Redis Pods (kubectl get pods -l app=redis). - Ensure
targetPortin theServicedefinition matches thecontainerPortin the Redis Pod definition.
- Check
- Solution: Correct the Kubernetes
ServiceandDeploymentYAML files, and reapply them.
- Explanation: In Kubernetes, you typically access a Redis Pod through a
- Pod Not Running/Crashing:
- Explanation: If the Redis Pod(s) are not running, failing probes, or constantly restarting, the
Servicewill have no healthy endpoints to route traffic to, leading to "Connection Refused." - Verify:
kubectl get pods,kubectl describe pod <redis-pod-name>,kubectl logs <redis-pod-name>. - Solution: Troubleshoot the underlying Pod issues (e.g., image pull failures, resource limits, Redis server startup errors within the container).
- Explanation: If the Redis Pod(s) are not running, failing probes, or constantly restarting, the
- Network Policies:
- Explanation: Kubernetes Network Policies can restrict traffic between Pods. If a Network Policy is in place that denies ingress to the Redis Pods from your client application's Pods, connections will be refused.
- Verify:
kubectl get networkpoliciesand examine their rules. - Solution: Modify or create a Network Policy to allow traffic to Redis from the necessary sources.
- Ingress/Egress Gateway Issues:
- If accessing Redis from outside the Kubernetes cluster, you might be going through an Ingress, NodePort, or LoadBalancer. Ensure these external access mechanisms are correctly configured and pointing to your Redis service.
- Service Misconfiguration:
In complex distributed systems, especially those leveraging microservices and APIs, ensuring seamless communication between components like Redis and application services is paramount. Platforms like APIPark, an open-source AI gateway and API management platform, help manage and streamline API interactions, which often depend on reliable data backends like Redis. By providing robust API lifecycle management, APIPark helps ensure that the services relying on Redis are properly exposed and managed, contributing to overall system stability and performance in such dynamic containerized environments.
Containerization and virtualization add powerful layers of abstraction but also introduce new potential points of failure for networking. A thorough understanding of Docker networking and Kubernetes Service models is essential for debugging "Connection Refused" errors in these environments.
APIPark is a high-performance AI gateway that allows you to securely access the most comprehensive LLM APIs globally on the APIPark platform, including OpenAI, Anthropic, Mistral, Llama2, Google Gemini, and more.Try APIPark now! 👇👇👇
Systematic Troubleshooting Approach
When faced with a "Redis Connection Refused" error, a structured, methodical troubleshooting approach is far more effective than random attempts. Follow these steps to systematically diagnose and resolve the issue.
Step 1: Verify Redis Server Status (Is it running?)
This is always the first and most fundamental check. If Redis isn't running, nothing else matters.
- Action:
- Linux/macOS:
sudo systemctl status redisorps aux | grep redis-server - Windows: Check Services Manager or
tasklist | findstr redis-server.exe
- Linux/macOS:
- Expected Outcome: Redis server process should be active and running.
- If not running:
- Attempt to start it:
sudo systemctl start redis. - Immediately check logs:
sudo tail -f /var/log/redis/redis-server.log(or specifiedlogfileinredis.conf) for errors preventing startup. Address any issues found (e.g., config errors, port conflicts, memory issues).
- Attempt to start it:
Step 2: Check Network Reachability (Can the client even see the server?)
Even if the server is up, network blockages prevent communication. While "Refused" suggests network path is open, it's good to confirm the basics.
- Action (from client machine):
ping <redis-server-ip>: Verifies basic IP-level connectivity.telnet <redis-server-ip> <redis-port>ornc -vz <redis-server-ip> <redis-port>: Attempts a raw TCP connection to the specific port.
- Expected Outcome:
pingshould succeed.telnet/ncshould ideally connect immediately (blank screen fortelnet, "succeeded" fornc). Iftelnet/ncimmediately says "Connection refused," proceed to Step 3 and 4, as the network path is open but the OS is refusing. Ifpingfails ortelnet/nctimes out/reports host unreachable, address network issues (routing, client firewall, server-side firewall dropping packets).
Step 3: Inspect Redis Server Configuration (redis.conf)
The server's configuration dictates how it behaves and where it listens.
- Action (on Redis server):
- Open
redis.conf(e.g.,/etc/redis/redis.conf). - Verify
port: Ensure it matches the port the client is trying to connect to. - Verify
binddirective: This is critical.- If the client is remote,
bind 0.0.0.0orbind <server-ip-facing-client>must be set.bind 127.0.0.1will prevent remote connections.
- If the client is remote,
- Verify
requirepass: If enabled, note the password. - Verify
maxclients: Ensure it's a reasonable value and not being hit (checkINFO Clientsif you can connect locally).
- Open
- Expected Outcome:
portandbindsettings should allow the desired client access.requirepassshould be noted. - If changes are made:
- Save
redis.conf. - Restart Redis:
sudo systemctl restart redis. - Verify Redis is listening on correct interfaces/ports:
sudo netstat -tulpn | grep <redis-port>.
- Save
Step 4: Examine Firewall Rules (Server & Cloud)
Firewalls are a leading cause of active connection refusal.
- Action (on Redis server and cloud console):
- OS Firewall:
ufw:sudo ufw status verbose.sudo ufw allow <redis-port>/tcp.firewalld:sudo firewall-cmd --zone=public --list-all.sudo firewall-cmd --zone=public --add-port=<redis-port>/tcp --permanent.sudo firewall-cmd --reload.iptables:sudo iptables -L -n -v. AddACCEPTrule for the port before anyREJECT/DROP.
- Cloud Security Groups/NACLs (if applicable): Check inbound rules for your Redis server instance. Ensure TCP portis allowed from your client's IP range.
- OS Firewall:
- Expected Outcome: Firewall rules should explicitly allow incoming TCP connections on the Redis port from the client's IP address or range.
Step 5: Review Client Configuration
Even if the server is perfect, the client must be configured correctly.
- Action (on client machine/application code):
- Check application's configuration files, environment variables, or code for Redis connection details.
- Verify Host:
IP addressorhostnamemust be correct. - Verify Port: Must match
redis.confportdirective. - Verify Password: If
requirepassis set on the server, the client must provide the exact password. - Verify SSL/TLS: If server is plain TCP, client must not try to use SSL. If server requires SSL, client must be configured for it.
- Expected Outcome: Client connection details precisely match Redis server's listening configuration and security settings.
Step 6: Check Operating System Resource Limits
Overwhelmed systems can refuse new connections.
- Action (on Redis server):
- Check file descriptor limits for Redis process:
sudo cat /proc/<redis-pid>/limits(look forMax open files). - Check system-wide limits:
cat /proc/sys/fs/file-max.
- Check file descriptor limits for Redis process:
- Expected Outcome: File descriptor limits should be sufficiently high (e.g., 65536 or more) and higher than
maxclients. - If limits are too low: Increase
LimitNOFILEin the Redis systemd service file or/etc/sysctl.conf. Restart Redis and possibly the system.
Step 7: Examine Server Logs for Deeper Clues
Logs are often the truth-tellers.
- Action (on Redis server):
- Continuously monitor Redis logs:
sudo tail -f /var/log/redis/redis-server.log. - Check system logs:
sudo journalctl -xeorsudo tail -f /var/log/syslogfor kernel messages, OOM killer, or network-related errors.
- Continuously monitor Redis logs:
- Expected Outcome: No recent errors or warnings indicating crashes, resource exhaustion, or configuration parsing failures.
- If errors found: Research and address specific error messages.
By following this systematic approach, you can methodically eliminate potential causes and pinpoint the exact source of your "Redis Connection Refused" error, leading to a faster and more efficient resolution.
Preventive Measures to Avoid "Redis Connection Refused"
Proactive measures and robust system design can significantly reduce the likelihood of encountering "Redis Connection Refused" errors. By anticipating potential failure points and implementing best practices, you can ensure a more stable and reliable Redis environment for your applications.
1. Implement Robust Monitoring and Alerting
Explanation: The ability to detect anomalies and potential issues before they escalate into full-blown outages is paramount. Comprehensive monitoring of your Redis instances and the underlying infrastructure allows you to catch warning signs early.
Detailed Implementation:
- Redis-Specific Metrics: Monitor key Redis metrics such as:
connected_clients: Alert if this approachesmaxclients.used_memory: Alert if memory usage is close tomaxmemoryor system limits.rdb_last_save_time,aof_last_write_status: Ensure persistence is healthy.keyspacehits/misses: Indicates cache efficiency.uptime_in_seconds: Track Redis restarts.
- System-Level Metrics: Monitor the Redis server's host for:
- CPU utilization, memory usage, disk I/O, network I/O.
- Number of open file descriptors (
/proc/<pid>/fd). - Available disk space (especially crucial for AOF and RDB persistence).
- Connection Status Checks: Implement external health checks that periodically attempt to connect to Redis. Many monitoring tools offer Redis integration (e.g., Prometheus with Redis Exporter, Grafana, Datadog, New Relic).
- Alerting Thresholds: Configure alerts for critical thresholds (e.g., Redis not reachable,
connected_clients> 80% ofmaxclients, high memory usage, server down). Alerts should be routed to appropriate personnel via email, SMS, or Slack. - Log Aggregation: Centralize Redis logs (and system logs) using tools like ELK Stack (Elasticsearch, Logstash, Kibana) or Splunk. This makes it easier to search for error messages and correlate events across multiple systems, providing a historical context for troubleshooting.
2. Practice Proper Configuration Management
Explanation: Inconsistent or unmanaged configurations are a common source of errors. Having a controlled process for managing redis.conf and client connection parameters ensures consistency and reduces manual errors.
Detailed Implementation:
- Version Control
redis.conf: Store yourredis.confin a version control system (e.g., Git). This allows you to track changes, revert to previous versions if issues arise, and ensure consistency across environments. - Automated Deployment: Use configuration management tools (Ansible, Puppet, Chef, SaltStack) or infrastructure-as-code (Terraform) to deploy and manage
redis.confacross all your Redis instances. This eliminates manual configuration errors. - Parameterized Configuration: For client applications, use environment variables, dedicated configuration files (e.g.,
.env,application.properties), or a centralized configuration service (e.g., HashiCorp Consul, Spring Cloud Config) to manage Redis connection details (host, port, password). Avoid hardcoding these values in application code. - Review and Test: Before deploying new
redis.confchanges, useredis-server --test-conf /path/to/redis.confto check for syntax errors. Thoroughly test client connectivity in a staging environment. maxclientsandLimitNOFILEAlignment: Ensure that themaxclientsvalue inredis.confis always less than or equal to theLimitNOFILEsetting for the Redis service at the OS level. Configure these system limits viasystemdunit files orulimitsettings in a managed way.
3. Implement Connection Pooling in Applications
Explanation: Connection pooling is a fundamental best practice for any application interacting with a database or data store like Redis. It mitigates the overhead of repeatedly establishing and tearing down connections and prevents resource exhaustion on the Redis server.
Detailed Implementation:
- Reduce Overhead: Creating a new TCP connection for every Redis command is inefficient. A pool maintains a set of open, reusable connections.
- Prevent
maxclientsIssues: By controlling the maximum number of active connections in the pool, you ensure that your application doesn't overwhelm Redis by opening too many simultaneous connections, thereby preventingmaxclientserrors. - Configure Pool Size: Carefully configure the minimum and maximum pool sizes based on your application's load, Redis's capacity, and available resources. A pool that's too small can cause bottlenecks; one that's too large can still exhaust Redis.
- Client Library Support: Most modern Redis client libraries (Jedis for Java,
redis-pyfor Python,node-redisfor Node.js,go-redisfor Go) offer robust connection pooling built-in. Utilize these features. - Graceful Handling: Configure connection pools to handle stale or broken connections gracefully, automatically replacing them.
4. Regularly Update and Patch Redis and OS
Explanation: Software bugs, security vulnerabilities, and performance issues are continuously discovered and fixed. Running outdated versions of Redis or the underlying operating system exposes you to known problems that could lead to instability, crashes, or security breaches, all of which can manifest as connection issues.
Detailed Implementation:
- Redis Updates: Stay informed about new Redis releases. Regularly plan and execute upgrades to stable, actively maintained versions. New versions often include performance improvements, bug fixes, and enhanced stability. Always review release notes for breaking changes.
- Operating System Patches: Keep the host operating system updated with the latest security patches and bug fixes. This addresses vulnerabilities in the kernel, network stack, and other system components that Redis relies on.
- Client Library Updates: Ensure your application's Redis client libraries are also kept up-to-date. Newer versions often fix bugs, improve connection handling, and support new Redis features.
- Staging Environment Testing: Always test updates in a non-production (staging) environment first to catch any regressions or compatibility issues before deploying to production.
5. Plan for Redundancy and High Availability
Explanation: Even with the best preventive measures, hardware failures, unexpected software bugs, or network outages can occur. Implementing redundancy ensures that your Redis service remains available even if a single instance fails.
Detailed Implementation:
- Redis Sentinel: For high availability, deploy Redis Sentinel. Sentinel is a distributed system that monitors Redis master and replica instances, performs automatic failover if a master fails, and provides service discovery for clients. Clients connect to Sentinel, which then provides the current master's address.
- Redis Cluster: For horizontal scaling and partitioning data across multiple Redis instances, use Redis Cluster. It provides automatic sharding, replication, and failover capabilities. This not only improves availability but also allows you to scale beyond the limits of a single Redis server.
- Backup and Restore Strategy: Implement a robust strategy for backing up your Redis data (RDB snapshots, AOF files) and regularly test the restore process. While not directly preventing connection refused errors, it's crucial for quick recovery if data corruption or loss occurs after an incident.
- Geographic Redundancy: For disaster recovery, consider deploying Redis instances in multiple geographic regions or availability zones.
By integrating these preventive measures into your development and operations workflows, you create a resilient Redis infrastructure that is less prone to "Connection Refused" errors and can recover more gracefully from unforeseen issues, ensuring continuous availability for your applications.
Conclusion
The "Redis Connection Refused" error, while a common and often bewildering stumbling block for developers and system administrators, is fundamentally a signal that the operating system on the target machine has actively rejected a connection attempt. It indicates a failure at a critical juncture in the TCP handshake, pointing directly to issues on the server host itself rather than mere network unreachability. As we have meticulously explored, the culprits behind this rejection can be numerous and diverse, ranging from the straightforward (a Redis server simply not running) to the more nuanced (intricate firewall rules, misconfigured bind directives, resource exhaustion, or subtle networking glitches within virtualized environments).
Successfully navigating and resolving this error hinges upon a systematic and thorough diagnostic approach. Beginning with basic checks like verifying the Redis process status and network reachability, and then progressively delving into server configuration, firewall settings, client-side parameters, and system resource limits, allows for the methodical elimination of potential causes. Each step, armed with the appropriate command-line tools and an understanding of the underlying mechanisms, brings you closer to pinpointing the exact source of the problem.
Beyond immediate troubleshooting, adopting a proactive stance is crucial for long-term stability. Implementing robust monitoring, adhering to disciplined configuration management, leveraging connection pooling in client applications, maintaining up-to-date software versions, and designing for high availability with solutions like Redis Sentinel or Redis Cluster are not merely optional enhancements but essential practices. These preventive measures serve to minimize the occurrence of connection refusals, enhance resilience against failures, and ensure the continuous, high-performance operation of your Redis-backed applications. By embracing the insights and actionable strategies presented in this comprehensive guide, you can demystify the "Redis Connection Refused" error, transform it from a source of frustration into an opportunity for deeper system understanding, and ultimately build more robust and reliable data infrastructures.
Frequently Asked Questions (FAQs)
Q1: What is the most common reason for a "Redis Connection Refused" error?
A1: The absolute most common reason for a "Redis Connection Refused" error is that the Redis server process is simply not running on the target machine or port. If there is no application listening on the specific port that the client is trying to connect to, the operating system will immediately send an RST (reset) packet, which the client interprets as a "Connection Refused" error. Always check the Redis server's status (systemctl status redis on Linux or Windows Services) and its logs (/var/log/redis/redis-server.log) first. Other frequent causes include incorrect bind directive in redis.conf and firewall blocks.
Q2: How is "Connection Refused" different from a "Connection Timeout" when connecting to Redis?
A2: The distinction is crucial for troubleshooting. * "Connection Refused" means your client's initial SYN packet reached the target server's operating system, but the OS actively rejected the connection by sending an RST packet. This typically indicates no process is listening on the specified port, or a firewall explicitly denied the connection. The network path is generally open. * "Connection Timeout" means your client's SYN packet did not receive a response within a specified period. This often points to network-level issues where the packet never reached the server (e.g., routing problems, server offline, firewall dropping packets silently), or the server was too overloaded to respond in time.
Q3: I'm getting "Connection Refused" when trying to connect to Redis from a remote machine, but it works locally with redis-cli. What should I check?
A3: This scenario almost always points to either the Redis bind directive or firewall rules. 1. Redis bind directive: Check your redis.conf for the bind setting. If it's bind 127.0.0.1 (the default in newer versions), Redis will only accept local connections. To allow remote connections, you need to change it to bind 0.0.0.0 (for all interfaces) or bind <server-external-ip> (for a specific external interface). Remember to restart Redis after changing redis.conf. 2. Firewall: Check both the server's operating system firewall (e.g., ufw, firewalld, iptables) and any cloud provider security groups (e.g., AWS Security Groups, Azure NSGs). Ensure that TCP port 6379 (or your custom Redis port) is explicitly allowed for inbound connections from the IP address of your remote client.
Q4: My application uses connection pooling, but I'm still getting "Redis Connection Refused" errors. What could be happening?
A4: Even with connection pooling, "Connection Refused" errors can occur, especially if the underlying cause is persistent or external to the pool's lifecycle: 1. Initial Connection Failure: The pool itself might be failing to establish its initial set of connections to Redis due to a fundamental server issue (Redis not running, firewall, bind directive). 2. Redis Server Crash/Restart: If the Redis server crashes or restarts, all existing connections in the pool become stale. When the pool tries to reuse them or create new ones, it will encounter "Connection Refused" until Redis is fully back online and reconnected. 3. maxclients Exceeded: While pooling helps manage connections, if the pool size itself is too large for the Redis server's maxclients limit, or if other applications are consuming all available connections, new connections requested by the pool might be refused. 4. Network Glitches: Temporary network instability might cause the pool to repeatedly fail connection attempts, although this might also manifest as timeouts. Monitor Redis logs and system logs for crashes or resource exhaustion, and verify redis.conf settings like bind and maxclients.
Q5: How can APIPark help manage services that rely on Redis, reducing connection issues?
A5: While APIPark doesn't directly troubleshoot Redis "Connection Refused" errors, it plays a vital role in the broader ecosystem of applications that depend on Redis, particularly in microservices and API-driven architectures. * API Lifecycle Management: APIPark is an open-source AI gateway and API management platform that helps manage the entire lifecycle of APIs. Many backend services exposed via APIs interact with data stores like Redis for caching, session management, or real-time data. By ensuring these API-driven services are robustly managed and monitored, APIPark indirectly contributes to the stability of their underlying dependencies, including Redis. * Centralized Control: In complex environments where multiple services might connect to Redis, APIPark provides a centralized platform for managing all API services. This can help enforce best practices for how services access data, and if a service is malfunctioning and causing Redis connection issues (e.g., connection leaks), the overall system visibility provided by APIPark can help identify the problematic service more quickly. * System Resiliency: By facilitating robust API design, traffic management, and potentially health checks for dependent services, APIPark helps build a more resilient system where issues with a data store like Redis can be isolated and addressed more effectively, preventing cascading failures across interconnected services. For more details on APIPark's capabilities, visit the official website: ApiPark.
🚀You can securely and efficiently call the OpenAI API on APIPark in just two steps:
Step 1: Deploy the APIPark AI gateway in 5 minutes.
APIPark is developed based on Golang, offering strong product performance and low development and maintenance costs. You can deploy APIPark with a single command line.
curl -sSO https://download.apipark.com/install/quick-start.sh; bash quick-start.sh

In my experience, you can see the successful deployment interface within 5 to 10 minutes. Then, you can log in to APIPark using your account.

Step 2: Call the OpenAI API.



